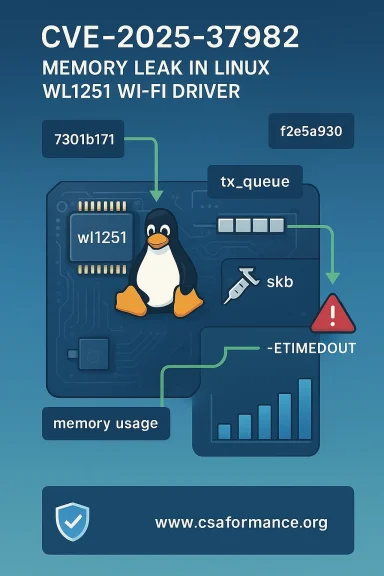
A recently assigned Linux-kernel CVE — CVE-2025-37982 — tracks a memory‑leak bug in the Texas Instruments wl1251 Wi‑Fi driver (the kernel file drivers/net/wireless/ti/wl1251/tx.c). The defect causes a socket buffer (skb) dequeued from the driver's transmit queue to be lost when the driver's power‑save wakeup path (wl1251_ps_elp_wakeup) times out; the upstream fix requeues the skb rather than discarding it. The fix was merged into the stable trees and the Linux CVE team published the advisory (CVE-2025-37982) on May 20, 2025.
The wl1251 driver supports a family of Texas Instruments Wi‑Fi chipsets. It has long been part of the upstream Linux kernel wireless tree and is compiled into kernels used by a variety of distributions and embedded images. The specific problem fixed by CVE‑2025‑37982 is not a classic remote code‑execution primitive — it’s a resource‑management bug that can cause a local memory leak when a particular wakeup path returns -ETIMEDOUT and the driver fails to requeue the skb it removed from tx_queue. Left unpatched, that leak can accumulate and, over time, degrade service or cause denial‑of‑service for systems that use the wl1251 driver heavily. The upstream Linux CVE announcement explains the cause, lists affected files and the commits that remedied the issue, and recommends updating to a kernel that includes the merged fix.
Key technical points to remember up front:
To be explicit:
Operationally:
Plausible Microsoft carriers of the wl1251‑impacted code:
Examples of vendor tracking:
Microsoft’s public statement that “Azure Linux includes this open‑source library and is therefore potentially affected” is authoritative for Azure Linux images and should drive immediate remediation for any Azure Linux hosts. However, it is not an exclusive declaration that no other Microsoft product contains the vulnerable kernel code; defenders must inventory other Microsoft artifacts (WSL2 kernels, Marketplace images, AKS node images and any Microsoft‑shipped appliance kernels) to determine exposure. Microsoft’s phased VEX/CSAF rollout will progressively reduce this uncertainty as the company publishes more attestations. (msrc.microsoft.com)
Action items for defenders:
Conclusion: Azure Linux is the Microsoft product Microsoft has publicly confirmed is potentially affected by CVE‑2025‑37982 — that confirmation matters and should be acted on immediately — but it is not a proof that no other Microsoft product contains the vulnerable upstream kernel code. Verify, patch, and automate the process so the next time a product‑scoped attestation is published you can respond with confidence and speed. (msrc.microsoft.com)
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
The wl1251 driver supports a family of Texas Instruments Wi‑Fi chipsets. It has long been part of the upstream Linux kernel wireless tree and is compiled into kernels used by a variety of distributions and embedded images. The specific problem fixed by CVE‑2025‑37982 is not a classic remote code‑execution primitive — it’s a resource‑management bug that can cause a local memory leak when a particular wakeup path returns -ETIMEDOUT and the driver fails to requeue the skb it removed from tx_queue. Left unpatched, that leak can accumulate and, over time, degrade service or cause denial‑of‑service for systems that use the wl1251 driver heavily. The upstream Linux CVE announcement explains the cause, lists affected files and the commits that remedied the issue, and recommends updating to a kernel that includes the merged fix.Key technical points to remember up front:
- The vulnerable code lives at drivers/net/wireless/ti/wl1251/tx.c and the problematic routine is wl1251_tx_work.
- The symptom is a lost skb when wl1251_ps_elp_wakeup fails with -ETIMEDOUT; the remedy is to requeue the skb back to tx_queue.
- The Linux kernel CVE team and multiple distro tracking systems (Debian, Oracle, NVD, vendor advisories) published entries that reference the same upstream commits and the same technical description.
What the assigned CVE actually means (and doesn’t)
Not an immediate remote exploit chain
This CVE describes a local memory‑leak condition in a device driver. It is not a remotely exploitable packet‑processing overflow that immediately yields arbitrary code execution. The practical risk profile is availability/resource exhaustion on hosts that load the wl1251 driver and exercise the specific wakeup path repeatedly under the right failure condition. Multiple vulnerability trackers score the issue as impactful but local in its attack vector.Fixes are available and are small, surgical upstream commits
Upstream maintainers merged small, directed fixes; the official linux‑cve announcement points to the stable commit(s) that carry the change and lists the canonically affected kernel lines. Operators who maintain their own kernels can apply the upstream commits; distributions have already begun shipping or scheduling fixes into their stable trees. The linux‑cve announcement includes the fix commits and guidance to update to a patched kernel.Is Azure Linux the only Microsoft product that includes this library and is therefore potentially affected?
Short answer: No — not necessarily. Azure Linux is the only Microsoft product that Microsoft has publicly attested (via its MSRC/VEX/CSAF outputs) to include the implicated upstream component for this CVE at the time of Microsoft’s advisory, but that product‑scoped attestation is not the same as a categorical statement that no other Microsoft product or artifact could contain the same vulnerable code. Microsoft has explicitly framed the language of such advisories as an inventory statement for the named product and has committed to expand the machine‑readable attestations (VEX/CSAF) as it inspects more artifacts. (msrc.microsoft.com)To be explicit:
- Microsoft’s public CVE entry language — “Azure Linux includes this open‑source library and is therefore potentially affected” — is an authoritative, product‑level inventory statement for Azure Linux images that have been examined. Treat that as a high‑confidence signal to prioritize remediation for Azure Linux hosts. (msrc.microsoft.com)
- That same phrasing does not guarantee exclusivity. Other Microsoft artifacts (for example, WSL2 kernels, Azure Marketplace images, AKS node images, custom Microsoft‑built kernel images) could also contain the vulnerable upstream commit range depending on which upstream kernel commit was used and how the kernel was configured and built. Microsoft’s published attestations are being rolled out in phases; until Microsoft publishes a VEX that explicitly includes or excludes other products, absence from the attestation is “not yet confirmed”, not “not affected.”
How Microsoft’s VEX/CSAF attestation program changes the operational calculus
Microsoft announced a phased rollout of machine‑readable VEX/CSAF attestations starting in October 2025, beginning with Azure Linux. The intent is to publish per‑product, machine‑readable signals that say whether an upstream CVE maps to the product and what the remediation/mitigation state is. That’s a major step toward automating triage: security teams can ingest Microsoft’s VEX output and treat a “confirmed” Azure Linux attestation as an authoritative in‑scope signal. Microsoft also said it will update the per‑CVE mapping if further products are identified as carriers.Operationally:
- If your estate includes Azure Linux images, treat Microsoft’s attestation as a high‑priority action item: patch Azure Linux hosts immediately using Microsoft’s guidance or the Azure Linux package updates. (msrc.microsoft.com)
- For all other Microsoft artifacts, do not assume they’re safe simply because they are not named in the Azure Linux attestation. Inventory and verify. The VEX rollout is ongoing and product coverage will expand over time.
Which Microsoft artifacts are plausible carriers and how to verify them
It’s important to understand the difference between a distribution and an artifact. The same upstream kernel source can be built into many different Microsoft products or images, depending on the release timeline and build choices.Plausible Microsoft carriers of the wl1251‑impacted code:
- Azure Linux (formerly CBL‑Mariner) — Microsoft has published attestations for this distribution and explicitly maps many upstream CVEs to it. If you run Azure Linux images, they are in scope as declared. (msrc.microsoft.com)
- WSL2 kernels shipped by Microsoft — Microsoft maintains a WSL kernel source tree and publishes prebuilt kernel images for WSL2; those kernels can include wireless drivers for host or VM‑specific scenarios and therefore deserve verification.
- Azure Marketplace images and custom VM images that include a Linux kernel built from upstream commits in the vulnerable range — these are per‑image questions and must be inventoried.
- Any Microsoft device or service that ships a Linux‑based appliance (for example, certain Azure edge services or appliances that use Azure Linux as a base image) — again, per‑artifact verification is required.
- Inspect the kernel version and commit range: run uname -a and, where possible, check the upstream commit IDs baked into the image. The linux‑cve announcement lists the commit where the issue was fixed and the earliest introduction commit; comparing those IDs to your kernel build identifies whether the commit range includes the vulnerable code.
- Check for the wl1251 module, or the driver object, on running hosts: modinfo wl1251 or grep -R "wl1251" /lib/modules/$(uname -r) will show whether the driver is present as a module. If it’s built in to the kernel, inspecting /proc/config.gz or the kernel config records can reveal CONFIG_WL1251 settings.
- For images you cannot run locally (Marketplace images, container hosts), extract the kernel RPM/DEB and search the packaged kernel/extract for the driver source or for module binaries matching wl1251. For container‑host images, compare package lists and kernel package versions against upstream fix commits.
- Consult Microsoft’s published VEX/CSAF files and MSRC advisories for product‑level statements; treat those as authoritative for the named product but incomplete for the wider Microsoft artifact set until expanded.
Patching and mitigation guidance
Practical steps every operator should take now:- Identify in‑scope systems
- Inventory all hosts that run a Linux kernel (physical hosts, VMs, container hosts, appliances), and specifically check for the presence of the wl1251 driver. Use automated inventory tools where possible.
- Treat any Microsoft‑supplied Azure Linux images as in‑scope immediately, because Microsoft has attested that Azure Linux carries the implicated upstream component. (msrc.microsoft.com)
- Update to a kernel that contains the upstream fix
- The Linux CVE announcement and multiple distro advisories point to the upstream commits that fix the issue; the privileged and recommended path is to update the entire kernel to a vendor‑published package that includes the fix rather than cherry‑picking single commits.
- If you maintain custom kernels and cannot upgrade to a newer full kernel release immediately, identify and cherry‑pick the specific upstream commits listed by the linux‑cve announcement into your tree, rebuild, and test before deployment. The CVE posting lists stable commit IDs for the fix.
- Monitor vendor advisories
- Watch distribution advisories (Debian, Red Hat, Oracle, Amazon Linux) and Microsoft’s MSRC/VEX feeds for product mapping updates. Many distributions have already published tracking entries that reference the same upstream commits.
- Compensating controls (if immediate patching is impossible)
- Isolate hosts that rely on wl1251 hardware from untrusted networks when practical. The threat is local, but isolation reduces the number of ways an attacker could cause repeated power‑save wakeup failures that trigger the leak.
- Limit unprivileged local user access to affected systems; because the exploit vector requires local access, reducing the local‑user attack surface helps mitigate immediate risk.
- Monitor memory usage and kernel logs on hosts with wl1251 loaded to detect sustained, anomalous resource consumption that could indicate leak accumulation.
- Detection and telemetry
- Add rules to your host‑based monitoring to alert on repeated wl1251 wakeup timeouts in kernel logs or on sustained growth of kernel memory allocations attributable to the network stack. Logging frameworks and EDRs that capture dmesg and kernel messages are useful here.
- If you operate in a cloud environment, enrich your image‑inventory pipeline to search published kernel packages for the commit IDs referenced by the linux‑cve and distro advisories.
Distros and vendor tracking: what’s already been published
The CVE was published upstream on May 20, 2025; NVD, linux‑cve‑announce, and a range of distribution trackers (Debian, Oracle, Amazon Linux advisories and others) added entries that reference the same description and the upstream fix commits. This cross‑vendor triangulation means the fix is recognized upstream and by downstream vendors; operators can rely on vendor kernels that include the backported patches or upstream stable kernels that contain the merges.Examples of vendor tracking:
- Debian and Oracle Linux published CVE tracker entries referencing the fix and offering upgrade guidance.
- Amazon Linux (ALAS) and other cloud vendors have listed CVE‑2025‑37982 in their advisories and shown whether their particular image families are affected; the Amazon ALAS entry assigns a CVSS 3.x score and flags the issue for customers running specific kernel branches.
Risk analysis for Microsoft customers and for defenders at large
Why Microsoft’s Azure Linux attestation matters- When Microsoft says “Azure Linux includes this open‑source library and is therefore potentially affected,” that is an actionable admission that a named Microsoft product family contains the upstream component and therefore needs vendor remediation. If your environment runs Azure Linux in any form (AKS node images, container hosts, Marketplace images built from Azure Linux), you must prioritize patching those images. (msrc.microsoft.com)
- Microsoft’s attestation is useful and transparent — but it is a scoped inventory result, not a forensic guarantee that other Microsoft‑supplied kernels do not include the same upstream code. Other Microsoft images that embed the kernel—WSL2 kernels, older Azure host images, Marketplace images or appliances—are plausible carriers depending on the kernel commit used when they were built. Security teams must verify those images directly rather than rely on the absence of a Microsoft attestation to declare them safe. This nuance is repeatedly emphasized in community analyses and in Microsoft’s communications about the VEX rollout.
- Likelihood: The vulnerability is local in nature; an attacker requires local access or must be able to run code on an affected host to trigger the leak repeatedly. That reduces immediate remote exploitation likelihood but does not eliminate risk in multi‑tenant or shared‑host environments.
- Impact: Unpatched systems may encounter memory growth and eventual availability degradation on hosts where wl1251 is loaded and exercised under error conditions. For embedded or resource‑constrained devices that depend on wl1251 hardware, the operational impact can be significant.
Practical checklist for administrators (quick reference)
- Inventory: Identify all systems running kernels that could include wl1251 (modinfo wl1251; grep module names in /lib/modules).
- Prioritize: Treat Azure Linux images as in‑scope immediately — Microsoft has attested they include the implicated component. (msrc.microsoft.com)
- Patch: Apply vendor kernel updates (Debian/Oracle/Red Hat/Azure Linux patches) or upgrade to stable kernels that include the upstream merges from the linux‑cve announcement.
- Verify: For each Microsoft artifact (WSL2 kernels, Marketplace images, AKS node images), check kernel versions or module presence; do not assume absence from Microsoft’s Azure Linux attestation equals absence of risk.
- Monitor: Add alerts for kernel logs referencing wl1251 wakeup timeouts and for unusual kernel memory growth.
- Document: Record all affected images and remediation dates in your vulnerability management system; integrate Microsoft’s VEX/CSAF feed to automate future mapping updates.
What to watch for next (and a caution about assumptions)
- Microsoft’s published VEX/CSAF feed will expand over time. If Microsoft identifies additional products that include the same upstream component, MSRC will update the CVE entry and VEX attestations accordingly. Security teams should pull VEX/CSAF feeds automatically and re‑triage when Microsoft updates the product mappings.
- Don’t assume that a Microsoft product not named in today’s attestation is safe; absence of a product in a VEX file means Microsoft has not yet published the inventory result for that artifact — it is not proof of absence. Community analyses and WindowsForum coverage repeatedly emphasize this operational distinction.
Final assessment and recommendations
CVE‑2025‑37982 is a real, upstream‑confirmed memory‑leak bug in the wl1251 Wi‑Fi driver that has been fixed upstream and is being tracked by major vulnerability databases and distributors. The vulnerability is not a remotely exploitable panic‑button for arbitrary code execution, but it can produce availability problems on affected hosts. The upstream fix is small and available as committed patches; distribution vendors and maintainers are rolling those fixes into kernel packages and advisories.Microsoft’s public statement that “Azure Linux includes this open‑source library and is therefore potentially affected” is authoritative for Azure Linux images and should drive immediate remediation for any Azure Linux hosts. However, it is not an exclusive declaration that no other Microsoft product contains the vulnerable kernel code; defenders must inventory other Microsoft artifacts (WSL2 kernels, Marketplace images, AKS node images and any Microsoft‑shipped appliance kernels) to determine exposure. Microsoft’s phased VEX/CSAF rollout will progressively reduce this uncertainty as the company publishes more attestations. (msrc.microsoft.com)
Action items for defenders:
- Immediately confirm and patch any Azure Linux hosts. (msrc.microsoft.com)
- Inventory and verify other Microsoft images and kernels — don’t assume absence from a VEX file equals not affected.
- Apply vendor kernels or upstream fixes; monitor kernel logs and memory behavior on hosts that load wl1251.
- Subscribe to Microsoft’s VEX/CSAF feeds and distro security advisories to automate future determinations.
Conclusion: Azure Linux is the Microsoft product Microsoft has publicly confirmed is potentially affected by CVE‑2025‑37982 — that confirmation matters and should be acted on immediately — but it is not a proof that no other Microsoft product contains the vulnerable upstream kernel code. Verify, patch, and automate the process so the next time a product‑scoped attestation is published you can respond with confidence and speed. (msrc.microsoft.com)
Source: MSRC Security Update Guide - Microsoft Security Response Center