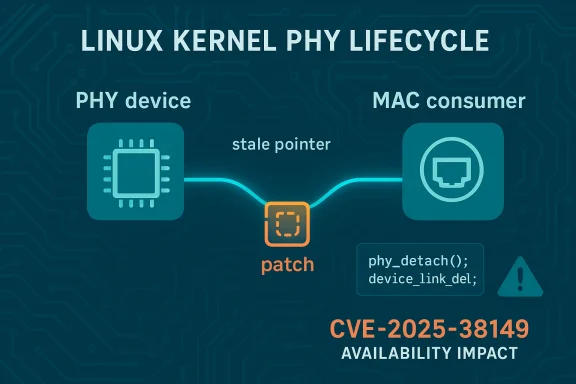
A subtle lifecycle bug in the Linux kernel’s PHY subsystem — tracked as CVE-2025-38149 — can cause a kernel crash when a network port is disabled and later re-enabled, and operators should treat the issue as an availability-first vulnerability that demands prompt, targeted patching and careful verification across distributions and images.
In plain terms, the defect stems from a missing reset of an internal pointer used to track a device‑link between a PHY and its MAC consumer. When a network port is disabled the kernel removes the device link, but it did not clear the
Why this approach is correct:
High‑priority environments include:
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
In plain terms, the defect stems from a missing reset of an internal pointer used to track a device‑link between a PHY and its MAC consumer. When a network port is disabled the kernel removes the device link, but it did not clear the phydev->devlink pointer. If the port is later re‑enabled and the re‑attach code fails early, the cleanup path can call device_link_del() with a stale pointer and trigger a NULL dereference that can crash the kernel. This classifies as a denial‑of‑service / availability issue at the kernel level rather than a remote code execution or data‑exfiltration bug. Upstream maintainers addressed the problem by making the teardown explicit: clear phydev->devlink when the link is deleted so later error paths never see a stale pointer. This change is small and surgical, but operationally important because it touches low‑level attach/detach sequencing used by many NICs and platform drivers. Evidence for the upstream fix and discussion is visible in kernel patch threads and distribution advisories.What exactly goes wrong — technical anatomy
The failing sequence (simplified)
- A MAC/PHY pairing is represented by a device‑link object; during attach the kernel assigns it to
phydev->devlink. - When the port is disabled,
phy_detach()callsdevice_link_del()to remove that link. - The code omitted setting
phydev->devlink = NULLafter removing the link, leaving a stale pointer inphydev. - Later, when re‑enabling the port,
phy_attach_direct()may fail early (for example, becausephy_init_hw()returns an error), which causes the flow to jump to the existing error cleanup — callingphy_detach()again. phy_detach()then callsdevice_link_del()using the stalephydev->devlinkvalue, causing a NULL pointer dereference and a kernel crash.
device_link_put_kref, device_link_del, phy_detach, and phy_attach_direct. Upstream contributors and reviewers agreed the right fix is to clear the pointer when deleting the link rather than accepting the crash as “expected” behavior.Why this is an availability problem
This is not a privilege escalation or remote‑execution primitive by itself. Instead, it is a classic lifetime management fault that can cause a host kernel to panic, hang, or otherwise become unavailable — outcomes that are critical for production networking gear, cloud images, or any host that experiences hot‑plug or frequent interface state changes. Because the trigger is local (it requires attach/detach activity and error paths), the attacker model tends to be:- an untrusted tenant or process that can manipulate network interfaces (e.g., NET_ADMIN-capable containers), or
- a local administrator or script running during orchestrated reconfiguration, or
- operations that cause hardware hotplug sequences (SFP modules, mobile PHYs) to run.
What the patch does (and why it’s low‑risk)
The upstream change is intentionally small: after the code callsdevice_link_del(...) it now explicitly sets phydev->devlink = NULL (and related defensive checks). That eliminates the stale pointer path on error cleanup while preserving the normal attach/detach lifecycle semantics.Why this approach is correct:
- It addresses the root cause (a dangling pointer between cycles) rather than masking the error elsewhere.
- The change is local to the PHY attach/detach code paths and does not alter higher‑level netdev semantics or timing characteristics.
- Small, targeted fixes are easier for downstream maintainers to backport into stable kernel trees and are less likely to introduce regressions.
Who’s affected — scope and distribution coverage
Affected code: the upstream Linux kernel’s PHY device lifecycle code (introduced in a commit identified as the origin of the device‑link addition). OSV / upstream trackers map the vulnerable range (introduced at a particular commit hash) and list the stable commits that fix it. Multiple distributions packaged or backported the fix into kernel updates for affected release series; vendors publishing advisories include SUSE, Ubuntu, Amazon Linux and others. OSV and distribution trackers list the exact fixes and the Git commit IDs that close the issue in stable trees.High‑priority environments include:
- Network appliances, routers and edge boxes that do frequent interface reconfigurations or host hot‑pluggable PHYs.
- Cloud or virtual images that permit tenant‑level network device operations (NET_ADMIN or user namespaces that allow device creation/manipulation).
- CI/CD runners, build machines and developer workstations where testers repeatedly reconfigure interfaces.
Lower priority: hardened single‑tenant servers that never change interface state from unprivileged contexts. Even so, kernel panic on a single‑tenant host can still be severe for critical services and should not be ignored.
Evidence of vendor action and timelines
- SUSE and other distributors produced advisories listing CVE‑2025‑38149 and published patched kernel packages; SUSE lists CVSS and gives remediation guidance.
- Amazon Linux (ALAS) and other enterprise distributions mapped the upstream fixes to ALAS errata and kernel package releases where applicable. Amazon’s advisory data lists the patched kernel packages for Amazon Linux 2023 images.
- Upstream discussion and the patch thread (netdev / kernel mailing lists) show the proposal and review process for the change and include commentary about edge cases; those threads are the authoritative technical record of the change and show reviewers accepted the small pointer‑clear fix.
- Public vulnerability databases (OSV, Snyk, PT Security entries) aggregate the CVE, provide affected ranges and map to fix commits. These records capture the commit IDs used by stable trees to fix the problem and show that the fix entered multiple kernel stable branches.
Exploitability, evidence in the wild, and practical risk
- Exploitability: local-only vector (AV:L). The attacker needs to trigger the attach/detach failure path (or cause the driver lifecycle to run through the faulty sequence). That generally requires local capabilities or control over image provisioning that can manipulate the PHY/MAC lifecycle. Public trackers and EPSS estimates put the exploitation probability low at disclosure time; no widespread worm or remote exploit campaign was reported.
- In‑the‑wild reports: at the time the upstream fix and vendor advisories were published, analysts did not report active exploitation campaigns leveraging CVE‑2025‑38149. That does not mean the vulnerability is harmless; it means the practical attack path is constrained and real threat depends on local access patterns and exposure models (e.g., tenant capabilities in multi‑tenant clouds). Treat the absence of observed exploitation as a reason to patch proactively, not to delay.
- Consequences: the realistic impact is denial of availability for the host or its networking functions. For clusters or appliances, a single node panic can cascade into service disruption; for multi‑tenant hosts, a malicious tenant with sufficient capabilities could intentionally provoke repeated reconfigure cycles to cause persistent outages.
Detection, forensics, and indicators of compromise
Symptoms you can search for:- Kernel oops / tracebacks referencing
device_link_del,phy_detach,phy_attach_direct, or related phylink functions indmesg/journal. These traces are the immediate artifact of the NULL dereference path the CVE describes. - Unexplained host panics, hung CPUs during interface reconfiguration, or repeated kernel restarts on hosts that perform frequent netdev operations.
- Audit logs or container orchestration events that show repeated NET_ADMIN operations or privileged interface reconfigurations coming from unexpected tenants.
- Search kernel logs:
journalctl -kordmesgand filter for the function names above. - Correlate management plane activity (orchestration logs, CI jobs, user sessions) with host kernel events to see if interface operations preceded the crash.
- For suspected exploitation, preserve the full kernel logs and the machine’s state; reproduce only in safe staging environments, never on production live systems.
How to verify patch presence (practical steps)
- Inventory critical hosts and record their kernel version: run
uname -rand capture package metadata (distribution kernel package and changelog). - Map your kernel package to vendor advisories for CVE‑2025‑38149 — vendors publish the package versions and errata IDs that contain the stable backports. For example, SUSE and Amazon Linux published advisory mappings and package release data.
- If you maintain a custom kernel, confirm the presence of the upstream commit(s) that fix the issue in your tree. Public trackers list the commit IDs used to fix the bug in stable trees; verify those commit hashes appear in your build. (Upstream stable commit references were recorded in OSV and other trackers.)
- Test in staging: in a controlled test lab, perform an attach/detach reconfiguration scenario that previously exposed the error path (do not run untrusted PoCs in production) and confirm the kernel does not crash and that the kernel logs now show the corrected behavior (link removal followed by a cleared pointer, not a NULL deref).
Short‑term mitigations (when patching is delayed)
- Reduce ability of untrusted workloads to manipulate interfaces: drop NET_ADMIN and related capabilities from containers and untrusted processes. This reduces the local attack surface that can trigger attach/detach flows.
- Limit hotplug: avoid plugging/unplugging SFP modules or performing rapid interface reconfiguration on critical hosts until patched, if feasible in your environment.
- For appliances with vendor firmwares or embedded kernels: contact the vendor for timeline and plan maintenance windows — many embedded images require vendor firmware updates rather than distro kernel upgrades.
Operational checklist (recommended immediate actions)
- Inventory:
- Identify hosts running kernels in the affected ranges (consult OSV or your distro’s CVE mapping).
- Find hosts that expose MDIO, NET_ADMIN, or other network management capabilities to non‑trusted workloads.
- Prioritize:
- High: multi‑tenant hosts, network appliances, gateway hosts, build/CICD runners.
- Medium: edge devices with hot‑plug PHYs, developer machines.
- Low: single‑tenant hardened servers with strict privilege separation.
- Patch:
- Apply vendor kernel updates that include the stable backport for CVE‑2025‑38149 and schedule reboots as required.
- For cloud images (Marketplace images, curated node pools), upgrade node images or roll new node pools built from patched images.
- Verify:
- Confirm the upstream commit IDs or distribution changelogs are present in the installed kernel packages.
- Run the controlled attach/detach test in staging to validate the fix.
- Harden:
- Remove NET_ADMIN from untrusted containers and processes; lock down orchestration flows that permit dynamic interface changes.
- Monitor:
- Add log alerts for kernel oops traces and unexpected interface manipulation events; correlate with orchestration and tenant activity.
Critical analysis — strengths, risks, and the operational reality
Strengths of the response- The upstream fix is small, localized, and low‑risk, which made it straightforward to accept into stable kernel trees and for vendors to backport. That lowers the chance of regressions and shortens the window where operators face hard choices.
- The vulnerability is well‑documented in mailing‑list discussions and vendor advisories, so operators have authoritative pages and commit identifiers to map to packages.
- The operational risk is not the size of the patch but the deployment effort: kernel updates require reboots and well‑planned testing, especially for appliances, telecom systems, and time‑sensitive networks. Uncoordinated module blacklisting or driver removal can create equally disruptive availability problems.
- The long tail of embedded appliances, vendor‑pinned kernels and marketplace images can remain vulnerable for much longer than servers managed by mainstream distros. For those, patching depends on vendor notification and firmware image updates.
- Vendor attestations (for example, when a vendor maps the CVE to a specific product) are useful but limited in scope; absence of a vendor mapping is not proof of absence. Operators must still inventory kernel packages across the estate to be sure.
- At disclosure, there was no widely published proof‑of‑concept showing remote exploitation; the risk remains local. If your environment exposes local-like primitives to untrusted tenants (privileged containers or device passthrough), treat exposure as high until patched. Public exploit campaigns were not observed at the time of vendor announcements.
Final recommendations (what to do now)
- Treat CVE‑2025‑38149 as a patch‑priority for all hosts that may experience frequent interface attach/detach cycles or that expose interface management capabilities to untrusted workloads.
- Apply vendor kernel updates and verify the upstream commit is present in your installed kernel package before declaring a host remediated. Use your distro’s CVE advisory to map package releases.
- If immediate patching is impossible, reduce the local attack surface (drop NET_ADMIN for containers, avoid interface reconfiguration on critical hosts) and consider temporary firewalling or hardening of orchestration pipelines.
- For embedded appliances and vendor images, follow the vendor’s update guidance and plan maintenance windows; don’t disable drivers lightly without testing fallback behavior.
- Add kernel log detection for the function names implicated by the CVE and correlate those events with orchestration or tenant activity for faster triage.
Source: MSRC Security Update Guide - Microsoft Security Response Center