Microsoft’s short MSRC attestation that “Azure Linux includes this open‑source library and is therefore potentially affected” is accurate for CVE‑2025‑38193 — but it is a product‑scoped inventory statement, not a technical guarantee that no other Microsoft product or published image could include the same vulnerable kernel code.
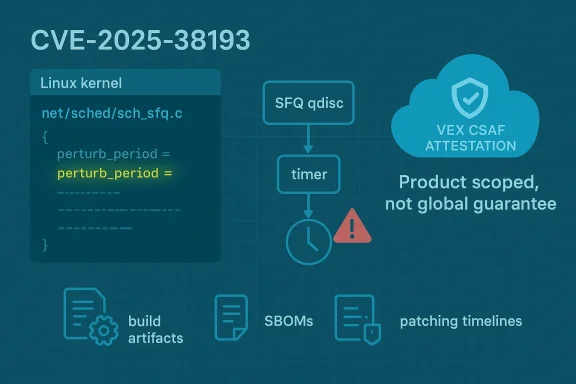
CVE‑2025‑38193 was assigned to a Linux kernel defect filed as “net_sched: sch_sfq: reject invalid perturb period.” The bug arises because the SFQ (Stochastic Fair Queuing) qdisc accepted a perturb_period value without validating its range or ensuring ctl->perturb_period * HZ cannot overflow, creating conditions that can trigger a race fixed by follow‑on patches. The issue was publicly announced by upstream maintainers and included in standard CVE feeds.
Multiple distro and vulnerability trackers cross‑reference the upstream announcement and list fixed kernel snapshots and backports. Distributors such as Ubuntu, Debian, Amazon Linux, and stable‑kernel maintenance channels have recorded affected and fixed kernel versions and provided guidance to their users. These independent listings corroborate the technical facts of the bug and the location in the tree (net/sched/sch_sfq.c).
At the same time Microsoft’s Security Response Center (MSRC) published a succinct product mapping line commonly used for recent Linux CVEs: “Azure Linux includes this open‑source library and is therefore potentially affected.” Microsoft has publicly explained that the phrasing is part of a phased rollout of machine‑readable CSAF/VEX attestations that began in October 2025; MSRC will expand those attestations to additional product families over time and will update CVE entries if additional Microsoft products are found to ship the same upstream component.
Whanot* claim is: “No other Microsoft product contains this code,” or “Other Microsoft artifacts have been exhaustively scanned and declared clean.” The MSRC attestation is intentionally narrow: it documents what Microsoft has examined so far and promises to update the CVE record if additional Microsoft products are later found to ship the same component. In practice, this is a phased, product‑by‑product inventory disclosure model. (archive.ph)
othat includes the vulnerable SFQ code?
Short answer: No — not necessarily. Azure Linux is the only Microsoft product Microsoft has publicly attested so far to include the implicated upstream component for this CVE. That makes Azure Linux a confirmed and immediate remediation priority. However, the ppstream code in other Microsoft artifacts is a build‑time property and remains an operational unknown until those artifacts are inventoried or attested.
However, the approach has inherent limitations and operational risks if misinterpreted. A single‑line attestation can be read incorrectly as an exclusivity guarantee by rushed teams; that leads to a false sense of security for environments that run other Microsoft images or kernel artifacts. The attestation model is phased: it documents what Microsoft has completed, not what Microsoft has not examined. Therefore defenders who rely solely on Microsoft’s Azure Linux attestation without performing artifact‑level discovery will leave blind spots in their estate.
In short: Microsoft’s attestation is good operational signaling for Azure Linux, but it is not a substitute for per‑artifact verification across multi‑product estates. Organizations should combine vendor attestations with internal SBOMs, image scans, and build‑time tracking to achieve comprehensive coverage.
That said, the attestation is deliberately scoped: it is not evidence that other Microsoft products or published images are free of the vulnerable code. Because kernel inclusion is a build‑time artifact property, other Microsoft artifacts — including WSL2 kernels, Marketplace and AKS images, linux‑azure kernels used in some VM SKUs, or other published images — could also carry the same upstream code until they are individually inventoried and attested. Administrators should therefore treat Azure Linux as confirmed in‑scope while performing artifact‑level discovery and remediation across other Microsoft images they run.
Actionable priorities remain clear: patch Azure Linux now, inventory Microsoft‑supplied kernels and images, cross‑check kernel configs and commit ranges against the upstream fix, and subscribe to MSRC’s VEX/CSAF feeds so attestations automatically reduce manual verification work as Microsoft expands its coverage.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CVE‑2025‑38193 was assigned to a Linux kernel defect filed as “net_sched: sch_sfq: reject invalid perturb period.” The bug arises because the SFQ (Stochastic Fair Queuing) qdisc accepted a perturb_period value without validating its range or ensuring ctl->perturb_period * HZ cannot overflow, creating conditions that can trigger a race fixed by follow‑on patches. The issue was publicly announced by upstream maintainers and included in standard CVE feeds.Multiple distro and vulnerability trackers cross‑reference the upstream announcement and list fixed kernel snapshots and backports. Distributors such as Ubuntu, Debian, Amazon Linux, and stable‑kernel maintenance channels have recorded affected and fixed kernel versions and provided guidance to their users. These independent listings corroborate the technical facts of the bug and the location in the tree (net/sched/sch_sfq.c).
At the same time Microsoft’s Security Response Center (MSRC) published a succinct product mapping line commonly used for recent Linux CVEs: “Azure Linux includes this open‑source library and is therefore potentially affected.” Microsoft has publicly explained that the phrasing is part of a phased rollout of machine‑readable CSAF/VEX attestations that began in October 2025; MSRC will expand those attestations to additional product families over time and will update CVE entries if additional Microsoft products are found to ship the same upstream component.
What CVE‑2025‑38193 actually is — technical anatomy
The defect in plain terms
The flaw is a missing range check and overflow guard around the SFQ qdisc’s perturb_period control. Because perturb_period is multiplied by HZ to compute scheduler timing, an unchecked negative value or a very large value can cause unexpected behavior. Upstream maintainers added rejection logic so the qdisc refuses invalid perturb_period values and also applied follow‑on fixes to remove the race conditions that an attacker could induce. The affected source file is net/sched/sch_sfq.c.Affected kernels and fixed versions
Upstream announcements list affected and fixed kernel snapshots across the supported stable series. The Linux CVE announcement enumerated the commits that introduced and fixed the issue and identified the earliest affected kernel lineage (introduced around 2.6.12 and fixed in various stable releases such as 5.15.186, 6.1.142, 6.6.95 and other later stable snapshots). Distribution advisory pages and OSV entries mirror that mapping and should be consulted for distribution‑specific package names and fixed package versions.Impact and exploitability
This is primarily a local kernel stability and correctness issue. Exploitation requires the ability to configure qdisc parameters on an interface or to trigger operations that exercise the SFQ perturb path, which implies local or administrativeal host configurations. The real operational risk is availability (kernel panics, crashes, race‑condition instability) rather than remote code execution. However, the presence of the vulnerable code in a running kernel image is the necessary precondition for exploitation.Microsoft’s wording: what the MSRC attestation does — and does not — mean
Product‑scopedlusivity
When MSRC writes “Azure Linux includes this open‑source library and is therefore potentially affected,” they are stating the result of an inventory operation for the Azure Linux product family. That attestation is authoritative for the Azure Linux images and kernels Microsoft inspected. It signals to Azure Linux users that Microsoft has found the implicated upstream code in that product and therefore has prioritized it for remediation and VEX/CSAF reporting.Whanot* claim is: “No other Microsoft product contains this code,” or “Other Microsoft artifacts have been exhaustively scanned and declared clean.” The MSRC attestation is intentionally narrow: it documents what Microsoft has examined so far and promises to update the CVE record if additional Microsoft products are later found to ship the same component. In practice, this is a phased, product‑by‑product inventory disclosure model. (archive.ph)
Why vendors publish product attestations this way
Large vendors ship thousands of images, appliances, container base images, kernel builds, and binary artifacts. Exhaustively scanning every published binary and image for every upstream file is operationally heavy and often performed in phases. Publishing a product‑level attestation for a single product family (Azure Linux) gives customers an immediate, actionable signal for that product while the vendor continues to inventory other product lines. The attestation’s value is its clarity and automatable nature (via VEX/CSAF) for the covered product; it is not a global exclusion.othat includes the vulnerable SFQ code?
Short answer: No — not necessarily. Azure Linux is the only Microsoft product Microsoft has publicly attested so far to include the implicated upstream component for this CVE. That makes Azure Linux a confirmed and immediate remediation priority. However, the ppstream code in other Microsoft artifacts is a build‑time property and remains an operational unknown until those artifacts are inventoried or attested.
Why the distinction matters practically
- Inclusion of SFQ code is decided at kernel build time and depends on the kernel version and configuration flags used when the kernel was compiled. A product that ships a kernel that predatand that enables or compiles the SFQ qdisc — will contain the same vulnerable code unless Microsoft has backported the fix or .
- Microsoft publishes several different kernel artifacts: the Azure Linux distribution kernels, WSL2 kernel binaries, "linux‑azure" kernels uss, AKS node images, Marketplace VM images, and container base images. Each of those is a separate artifact that must be verified individually. Absence of a VEX/CSAF attestation for a given artifact is absence of attestation, not proof of absence.
- Until Microsoft updates the CVE/VEX mapping to list additional affected products, administrators running other Microsoft images (WSL2, Marketplace images, AKS node images, custom Azure VM images distributed by Microsoft, etc.) should treat those images as unverified rather than Not Affected.
Common carriers beyond Azure Linux that deserve inspection
The same upstream SFQ code can appear in other Microsoft‑distributed artifacts depending on when and how those kernels were built. Administrators should prioritize artifact discovery across the following categories:- WSL2 kernel images Microsoft distributes (public WSL2 kernel builds are available in a Microsoft‑maintained repo); these kernels often include many common in‑tree drivers and schedulers.
- Azure VM images and custom Marketplace images that include linux kernels built from upstream snapshots prior to the fix.
- AKS node images and container host images that use Microsoft’s Azure Linux or other kernels.
- Any customer VM images based on Microsoft’s published images if those images include an older kernel without the upstream fix.
How to verify whether a given Microsoft artifact is affected — practical checks
Below are step‑by‑step checks you can run on any Linux host or image to determine whether it includes the vulnerable SFQ code and whether mitigation is required.- Identify the running kernel and build info:
- Run uname -a and read /proc/version. This gives the kernel version string and the compiled timestamp.
- Check whether your kernel contains the upstream fix:
- Look up the upstream stable commit IDs listed in the Linux CVE announcement (the announcement enumerates the fixes and commit hashes). Compare your kernel’s commit range or consult your distro’s security advisory to see if the fix is included. The upstream CVE announcement and distro advisories list the specific fixed commits.
- Inspect the kernel config to see if SFQ is enabled:
- zgrep CONFIG_SFQ /proc/config.gz or check your distribution’s /boot/config‑$(uname -r). If CONFIG_SFQ is built into the kernel or available as a module, the SFQ qdisc code is present and must be checked for the fix.
- For offline images:
- Mount or unpack the image and inspect the kernel binary and /boot/config*. If you have an SBOM or Microsoft VEX/CSAF attestation for a product image, use that as an authoritative inventory signal.
- Use package/distro advisories:
- Consult your Linux distribution’s security advisory (Ubuntu, Debian, Amazon Linux, Red Hat, SUSE) for fixed package numbers and CVE mappings. Distribution advisories are the canonical source for the exact package or kernel version you should install.
Remediation and mitigation options
- Apply the official kernel updates your distribution provides. Then merged into stable kernel series and many distributions have shipped backports or updated kernel packages. This is the recommended route for production systems.
- If you must operate with an older kernel (temporary), disable or avoid configuring SFQ on exposed interfaces. Avoid using tc qdisc add ... sfq perturb ... until you can confirm the kernel is fixed. This reduces the local attack surface associated with the perturb_period path.
- For managed Microsoft images: prioritize applying vendor updates when MSRC or your cloud‑provider advisoryzure Linux or other Microsoft products. Azure Linux users should follow Microsoft’s published patch guidance and image updates.
- Leverage VEX/CSAF and SBOM feeds: subscribe to Microsoft’s VEX/CSAF feeds so you are notified when attestations change from “Under Investigation” to “Known Affected” or “Fixed.” Use SBOMs and image scanning as an internal control to find copies of susceptible code across your estate.
Monitoring and detection
- Log and monitor kernel oops/panic traces and net/sched error messages. The upstream announcement contains sample tcd error messages for invalid perturb_period values; these can help you identify misconfigurations or attempts to exercise the vulnerable path.
- Watch for repeated use of tc qdisc commands that set perturb; command‑line auditing on build and orchestration nodes can reveal accidental or malicious use. Instrument your CI/CD pipelines that produce images to detect builds that compile in CONFIG_SFQ and to ensure the fixed kernel is used.
Risk assessment: who should care and why
- Azure Linux customers: high priority. Microsoft has attested that Azure Linux includes the implicated upstream component; treat Azure Linux images as confirmed carriers until Microsoft marks them Fixed in VEX/CSAF or you confirm a patched kernel is present. Apply Microsoft’s updates promptly.
- Enterprise tenants using mixed images: medium‑to‑high priority. If you run Marketplace images, AKS node pools, WSL2 images, or other Microsoft published artifacts, you must verify those artifacts rather than assume safety. The attestation for Azure Linux is authoritative for that product, but it does not prove other Microsoft artifacts are free of the code.
- Small deployments and edge hosts: medium priority. If you run kernels that enable SFQ and lack easy update paths, consider temporary mitigations (avoid SFQ usage) and plan for kips://ubuntu.com/security/CVE-2025-38193)
- Cloud and multi‑tenant platforms: high priority. Hosts that allow untrusted local users to manipulate qdisc settings increase the exploitable surface; these platforms should ensure hypervisor/host kernels are patched and that tenant VMs use patched gulicable.
Practical checklist for IT teams (concise)
- Prioritize patching of Azure Linux images and kernels. Microsoft has attested Azure Linux and is publishing VEX/CSAF updates.
- Inventory all Microsoft‑supplied kernels and images you run (WSL2, Marketplace, AKS, linux‑azure, custom images). Treat un‑attested artifacts as unverified.
- Verify kernel config for CONFIG_SFQ and check kernel versions againseferenced in the linux‑cve‑announce message.
- Use distro advisories (Ubuntu, Debian, Amazon Linux, RHEL/SUSE) to obtain fixed package names and backport guidance.
- If immediate patching is impossible, avoid enabling SFQ perturb configuration and monitor for anomalous tc traffic/deployments.
Strengths and limitations of Microsoft’s approach — critical analysis
Microsoft’s public VEX/CSAF program and its initial focus on Azure Linux show clear strengths: customers receive an authoritative, machine‑readable attestation for a named product family that enables rapid triage and automation of remediation tasks. Microsoft’s transparency commitment (publishing VEX/CSAF and product mappings) makes it easier for automation tooling and enterprise patch programs to act quickly on known affected products.However, the approach has inherent limitations and operational risks if misinterpreted. A single‑line attestation can be read incorrectly as an exclusivity guarantee by rushed teams; that leads to a false sense of security for environments that run other Microsoft images or kernel artifacts. The attestation model is phased: it documents what Microsoft has completed, not what Microsoft has not examined. Therefore defenders who rely solely on Microsoft’s Azure Linux attestation without performing artifact‑level discovery will leave blind spots in their estate.
In short: Microsoft’s attestation is good operational signaling for Azure Linux, but it is not a substitute for per‑artifact verification across multi‑product estates. Organizations should combine vendor attestations with internal SBOMs, image scans, and build‑time tracking to achieve comprehensive coverage.
If you find other Microsoft artifacts that appear affected: responsible next steps
- If your verification shows a Microsoft‑published image or artifact other than Azure Linux contains the vulnerable kernel code, report it through Microsoft’s standard security reporting channels and to your vendor support contact. Microsoft has stated it will update CVE/VEX mappings when additional products are identified.
- Meanwhile, isolate or mitigate the affected artifacts (avoid SFQ usage, restrict local qdisc manipulation privileges, schedule maintenance to deploy fixed kernels). Use image replacement with patched artifacts where available.
- Track updates to MSRC VEX/CSAF feeds and subscribe to distribution advisories so you receive automated indicators when Microsoft or your distribution vendor marks a product Fixed or Not Affected.
Conclusion
CVE‑2025‑38193 is a straightforward, upstream kernel correctness issue in net/sched’s SFQ perturb handling that has been fixed in upstream stable snapshots and backported by many distributors. Microsoft’s MSRC line that “Azure Linux includes this open‑source library and is therefore potentially affected” is a correct, authoritative, product‑level attestation for Azure Linux images that have been inspected; it is an actionable signal that Azure Linux customers must prioritize patching.That said, the attestation is deliberately scoped: it is not evidence that other Microsoft products or published images are free of the vulnerable code. Because kernel inclusion is a build‑time artifact property, other Microsoft artifacts — including WSL2 kernels, Marketplace and AKS images, linux‑azure kernels used in some VM SKUs, or other published images — could also carry the same upstream code until they are individually inventoried and attested. Administrators should therefore treat Azure Linux as confirmed in‑scope while performing artifact‑level discovery and remediation across other Microsoft images they run.
Actionable priorities remain clear: patch Azure Linux now, inventory Microsoft‑supplied kernels and images, cross‑check kernel configs and commit ranges against the upstream fix, and subscribe to MSRC’s VEX/CSAF feeds so attestations automatically reduce manual verification work as Microsoft expands its coverage.
Source: MSRC Security Update Guide - Microsoft Security Response Center