Microsoft’s short advisory line — “Azure Linux includes this open‑source library and is therefore potentially affected by this vulnerability” — is accurate for the product Microsoft has inventory‑checked, but it is a product‑scoped attestation, not proof that no other Microsoft product or artifact can contain the same vulnerable Linux kernel code. ([vulnerability.cirability.circl.lu/vuln/msrc_cve-2025-38197))
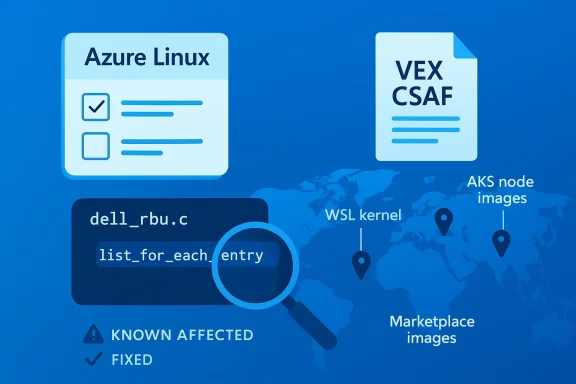
CVE-2025-38197 is a kernel-level defect in the Dell Remote BIOS Update driver (dell_rbu) that was fixed upstream by correcting improper list traversal in the packet-list handling code. The bug arose because the code passed an incorrect list head to list_for_each_entry*() when iterating the packet list; the practical symptoms reported upstream included incorrect data returned by sysfs reads and, more seriously, a NULL pointer dereference when clearing the packet list. (vulnerability.circl.lu)
The Linux kernel upstream and downstream trackers assigned and tracked fixes across stable branches; major distribution and vulnerability trackers recorded the issue and mapped it to the stable commits that carry the corrections. Microsoft’s MSRC entry for the CVE explicitly maps the vulnerable component to Azure Linux (specific azl3 kernel package versions are listed) and shows vendor remediation entries for fixed azl3 kernel builds. That is Microsoft’s machine‑readable attestation for the product it has inspected. (vulnerability.circl.lu)
Why enterprises are asking whether Azure Linux is “the only” affected Microsoft product is straightforward: many operations and vulnerability orchestration tools treat CVE→product mappings as decisive for patching and ticketing. If administrators assume the MSRC sentence implies exclusivity, they risk blind spots in environments that consume many different Microsoft artifacts (VM and Marketplace images, WSL kernels, container base images, AKS node images, custom Marketplace appliances, and vendor-supplied images running on Azure).
However, the sentence does not logically imply that Microsoft has scanned every Microsoft-distributed kernel, image, or related ar clean. Large vendors publish product‑level attestations in phases; Microsoft has explicitly said it will update VEX/CSAF mappings if additional Microsoft products are found to include the implicated upstream component. Treat “not named” as “not yet attested,” not as “proven safe.” (vulnerability.circl.lu)
1.) Inventory and prioritize
Be precise in your remediation tickets: list the assets you inspected, the kernel package or image identifiers you used, the presence/absence of CONFIG_DELL_RBU, and whether you applied azl3 kernel updates or performed module removal. That documentation will close the loop operationally and make future attestations easier to reconcile with your inventory.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CVE-2025-38197 is a kernel-level defect in the Dell Remote BIOS Update driver (dell_rbu) that was fixed upstream by correcting improper list traversal in the packet-list handling code. The bug arose because the code passed an incorrect list head to list_for_each_entry*() when iterating the packet list; the practical symptoms reported upstream included incorrect data returned by sysfs reads and, more seriously, a NULL pointer dereference when clearing the packet list. (vulnerability.circl.lu)The Linux kernel upstream and downstream trackers assigned and tracked fixes across stable branches; major distribution and vulnerability trackers recorded the issue and mapped it to the stable commits that carry the corrections. Microsoft’s MSRC entry for the CVE explicitly maps the vulnerable component to Azure Linux (specific azl3 kernel package versions are listed) and shows vendor remediation entries for fixed azl3 kernel builds. That is Microsoft’s machine‑readable attestation for the product it has inspected. (vulnerability.circl.lu)
Why enterprises are asking whether Azure Linux is “the only” affected Microsoft product is straightforward: many operations and vulnerability orchestration tools treat CVE→product mappings as decisive for patching and ticketing. If administrators assume the MSRC sentence implies exclusivity, they risk blind spots in environments that consume many different Microsoft artifacts (VM and Marketplace images, WSL kernels, container base images, AKS node images, custom Marketplace appliances, and vendor-supplied images running on Azure).
What the MSRC wording actually is — and what it is not
A product attestation, not a global inventory scan
When MSRC states “Azure Linux includes this open‑source library and is therefore potentially affected,” it is declaring the outcome of a targeted inventory check for that product family. That attestation is authoritative and operationally useful for customers running Azure Linux images: treat those images as known carriers and apply Microsoft’s remediation guidance. The VEX/CSAF data published by Microsoft maps specific azl3 kernel package versions to the CVE and records which versions are “known affected” and which are “fixed.” (vulnerability.circl.lu)However, the sentence does not logically imply that Microsoft has scanned every Microsoft-distributed kernel, image, or related ar clean. Large vendors publish product‑level attestations in phases; Microsoft has explicitly said it will update VEX/CSAF mappings if additional Microsoft products are found to include the implicated upstream component. Treat “not named” as “not yet attested,” not as “proven safe.” (vulnerability.circl.lu)
Why the nuance matters operationally
- Microsoft ships many kernel artifacts and images in different contexts: Azure Marketplace VM images, container base images, Azure‑tuned kernels used for specific VM SKUs, WSL2 kernel images distributed to Windows clients, and managed node images (AKS). Each artifact is built from a specific kernel snapshot, with its own configuration and potential backports.
- A vulnerable upstream commit may be present in many separate builds until each build is verified and patched; whether the vulnerable code is actually present in a binary depends on three verifiable facts for each artifact: the snapshot/commit el, the kernel configuration (is CONFIG_DELL_RBU enabled or not?), and whether any vendor backport or local patch already addressed the issue.
- Therefore, the safe operational posture is: Azure Linux = confirmed affected (until patched). All other Microsoft artifacts = unverified. Verify or inventory them before assuming they are unaffected.
Technical anatomy of CVE-2025-38197 (what defenders need to know)
Where the bug lives
- Component: drivers/platform/x86/dell/dell_rbu.c — the Dell Remote BIOS Update driver.
- Root cause: wrong list head passed to list_for_each_entry*() when iterating packet lists; this leads to off‑by‑one reads when exposing packet data via sysfs and can lead to a NULL pointer dereference when clearing the list. (vulnerability.circl.lu)
Practical impact and attack surface
- Exploitability: The vulnerability affects kernel-space driver code. The immediate impacts documented by maintainers are incorrect sysfs data and a kernel crash (NULL pointer dereference) during list clear operations. As such, the principal operational impact is availability (kernel OOPS/panic) rather than an obvious remote code execution path.
- Attack vector: Local (an attacker/process that can interact with the driver interface or trigger the driver logic). In many cases, the driver is a module that ships only for certain Dell platforms; not all hosts will have the component loaded or compiled.
- Severity: Trackers categorized the issue as significant enough to merit upstream fixes and distribution backports; CVSS scores in trackers vary by asset and vendor. Administrators should treat it as a high‑priority kernel stability issue for hosts that expose or load the driver.
Is Azure Linux the only Microsoft product that ships the library and could be affected?
Short, precise answer:- Azure Linux is the only Microsoft product Microsoft has publicly attested — via its CSAF/VEX artifact — to include the vulnerable upstream dell_rbu code at the time of the advisory. That attestation names specific azl3 kernel package versions and shows which azl3 kernels are Known Affected and which are Fixed. Treat Azure Linux as a confirmed remediation priority. (vulnerability.circl.lu)
- No — Azure Linux being named does not prove exclusivity. Any Microsoft artifact that ships a Linux kernel build compiled from an upstream snapshot containing the vulnerable commit and with the driver enabled could be a carrier until proven otherwise. Examples of artifacts you must verify include:
ibuted by Microsoft (WSL often uses a Microsoft‑built kernel image). - Azure Marketplace images and Azure VM SKUs that embed a Linux kernel.
- AKS node images or other managed node images published or maintained by Microsoft.
- Microsoft-published container base images that may contain child kernel dependencies or be used in contexts where kernel drivers are present.
- Microsoft has committed to expanding coverage of VEX/CSAF attestations beyond Azure Linux; absence of a VEX entry for product B is not evidence of absence of the vulnerable code. Until Microsoft attests a product as Not Affected or Fixed, treat un‑attested artifacts as unknown and verify them. (vulnerability.circl.lu)
How to verify whether your Microsoft-managed artifacts are affected — a practical checklist
This is a step‑by‑step runbook you can apply across an estate that includes Microsoft images or kernels.1.) Inventory and prioritize
- Enumerate Microsoft-distributed artifacts in your estate: Azure VM images and SKUs, Marketplace images, AKS node pool images, WSL instances, vendor appliances from Mcontainer images.
- Prioritize production and multi‑tenant hosts, and any systems running on Dell hardware where the dell_rbu driver is relevant.
- Check whether the module is present or compiled in:
- lsmod | grep dell_rbu
- modinfo dell_rbu
- grep -i CONFIG_DELL_RBU /boot/config-$(uname -r) || zcat /proc/config.gz | grep CONFIG_DELL_RBU
- Check the kernel version and package metadata to map against vendor advisories:
- uname -r; dpkg -l | grep linux-image; rpm -q kernel
- If the driver is not built into the kernel and not present as a module, that host is not exposed via this driver — but that only covers that specific artifact and kernel build.
- WSL uses a Microsoft-distributed kernel by default on many systems. Verify your WSL kernel binary and its configuration:
- On Windows, run wsl --status to see whether a custom kernel is in use and inspect the kernel image if one is configured.
- If WSL is using Microsoft’s distributed kernel, ask or check whether the Microsoft WSL kernel build includes CONFIG_DELL_RBU (it commonly does not for trimmed kernels, but this must be verified).
- Treat Marketplace and Microsoft-maintained images as potentially carrying the same kernel sources until verified by you or attested by Microsoft.
- Use instance-level checks (commands above) to detect module presence during an image's boot.
- Map your running kernel version or the kernel commit used to build an image against the upstream commit range fixed by the kernel maintainers. Upstream stable commits and distributor advisories list the exact commit IDs that correct the defect; distribution security advisories list package releases that carry the fix. (vulnerability.circl.lu)
- Apply vendor patches / update to the fixed kernel package listed by your vendor (Microsoft lists azl3 kernel package versions that are fixed in its VEX data for Azure Linux).
- If you cannot update immediately, consider containment: unload the module (rmmod dell_rbu) where safe, or restrict access to any interfaces that interact with the driver (sysfs entries) until a patch is deployed. Be cautious: unloading modules for firmware/updating drivers in production can have side effects—test before mass deploy. (vulnerability.circl.lu)
Detection and mitigation guidance (examples and priorities)
- Immediate priority (if you run Azure Linux azl3 kernels): follow Microsoft’s remediation guidance and apply the azl3 kernel update Microsoft lists in its VEX/CSAF record. Microsoft’s published azl3 kernel updates map specific azl3 package versions to “fixed” status. (vulnerability.circl.lu)
- Host‑level detection commands (concise):
- Check module: lsmod | grep dell_rbu. If present, run modinfo dell_rbu to see the module version and build.
- Check kernel config: zgrep CONFIG_DELL_RBU /proc/config.gz or grep CONFIG_DELL_RBU /boot/config-$(uname -r).
- Check kernel package mapping: Debian/Ubuntu dpkg -l | grep linux-image; RHEL/CentOS rpm -q kernel.
- If module is built‑in (not a loadable module), you must rely on kernel package updates; unloading is not possible.
- If immediate patching is impossible, reduce exposure: restrict unprivileged access to the driver interfaces (if accessible via sysfs) and monitor logs for oops and kernel warning traces referencing dell_rbu. Configure kernel oops monitoring and PSK alerts for sudden increases in OOPS/panics.
Cross‑checking the record (what we verified)
- Upstream kernel changelogs and the patch series that fix the packet-list and buffer handling for dell_rbu were posted on platform‑driver and stable branches; the patch series and commit messages describe the exact corrections (list usage fix, buffer overwrite protection).
- Vendor and distribution trackers (Oracle errata, Rapid7, Ubuntu trackers) listed CVE-2025-38197 and mapped affected kernel versions and fixes in the usual way, confirming the upstream commit path and indicating downstream packaging.
- Microsoft’s VEX/CSAF data (the MSRC VEX entry for this CVE) explicitly lists Azure Linux 3.0 azl3 kernel package versions and marks certain azl3 kernels as Known Affected or Fixed; the VEX document shows Microsoft’s mapping and remediation dates for the vendor fix. This confirms Microsoft’s attestation is narrowly scoped to Azure Linux and that Microsoft has published remediation guidance for Azure Linux customers. (vulnerability.circl.lu)
- Kernel documentation for the dell_rbu driver and configuration entries show that CONFIG_DELL_RBU is a kernel config option present in many kernel series; whether it is enabled in a particular kernel build is a per-artifact question. That demonstrates the realistic potential for the same dacross many different artifacts and OS images.
Risk analysis — strengths and gaps in Microsoft’s approach
Strengths
- Microsoft’s decision to publish CSAF/VEX attestations and to start with Azure Linux is an istep: it gives Azure customers an explicit, machine‑readable mapping and remediation path for CVEs in third‑party components the company ships. That reduces noise and helps automation tools act decisively for the attested product.
- For Azure Linux customers, Microsoft’s attestation plus clear azl3 kernel package versions provides a fast route from discovery to remediation: the VEX shows which azl3 kernel packages are known affected and which are fixed. (vulnerability.circl.lu)
Risks and limitations
- Attestation scope is the core limitation. The VEX entry answers “Is Azure Linux affected?” with “Yes,” but it does not by itself answer whether other Microsoft artifacts are affected — and it cannot, without additional inventory work, guarantee that other Microsoft images, WSL kernels, or AKS node images are clean. Operators who assume the single product mapping is exhaustive create a blind spot.
- Large vendors frequently deliver many distinct artifacts and custom builds. The same upstream driver can be built into many different kernsoft attests those artifacts in VEX as Not Affected or Fixed, customers should treat them as unverified and run targeted discovery and verification.
- The practical attack surface for this specific CVE is local and platform-dependent (Dell hardware / driver presence). That reduces the immediate blast radius for the general population, but for any estate that runs Dell hardware or that uses Microsoft-built kernel artifacts across images, the issue is operationally relevant and must be triaged.
Recommendations — what organizations should do now
- Treat Microsoft’s attestation for Azure Linux as authoritative for Azure Linux images: apply the azl3 kernel updates Microsoft lists as “fixed” in its VEX data as an immediate priority. (vulnerability.circl.lu)
- Run an artifact‑level inventory across Microsoft-supplied images in your estate. Don’t assume “not named” means “safe.” Prioritize:
- Azure Marketplace images, AKS node images, and any Microsoft-published container images you consume.
- WSL2 kernels used on Windows clients that are part of your enterprise fleet.
- Any Marketplace appliances or images from third parties that may have been built from Microsoft-published base images.
- Perform the host checks listed above (lsmod/modinfo, kernel config check, package version checks) for each image or running host and map results to upstream commit IDs or fixed package revisions before you mark an asset as remediated.
- If a kernel is confirmed affected and immediate patching is not possible, apply mitigations: unload the module where safe, restrict access to driver sysfs nodes, and escalate monitoring for kernel oops/panics on affected hosts.
- Automate future coverage: ingest Microsoft’s CSAF/VEX feed into your vulnerability orchestration tooling so that product‑level attestations are visible to your inventory and triage systems; but also enforce artifact‑level verification for high‑impact kernel CVEs because VEX is being rolled out product‑by‑product.
Final assessmment that “Azure Linux includes this open‑source library and is therefore potentially affected” is a correct and useful product attestation: it tells Azure Linux customers what they need to know and where Microsoft has already performed inventory and remediation mapping. However, it is not, and cannot be, a blanket assertion that every Microsoft‑distributed artifact is free of the vulnerable code. Administrators should treat the attestation as high‑confidence for Azure Linux and follow Microsoft’s remediation path for those images, while simultaneously treating other Microsoft artifacts as unverified until they are explicitly attested or independently verified in your own environment.
For this specific kernel bug in dell_rbu the immediate operational risk is availability (kernel oops/crash) and the privilege/trigger model remains largely local and platform dependent. That reality reduces the mass-exploit surface but does not change the operational need for careful inventory, per‑artifact verification, and timely patching where the driver or affected kernel builds are present. Upstream commits and distribution advisories confirm the fix; Microsoft’s VEX mapping confirms Azure Linux has been checked and remedied for the listed azl3 kernels.Be precise in your remediation tickets: list the assets you inspected, the kernel package or image identifiers you used, the presence/absence of CONFIG_DELL_RBU, and whether you applied azl3 kernel updates or performed module removal. That documentation will close the loop operationally and make future attestations easier to reconcile with your inventory.
Source: MSRC Security Update Guide - Microsoft Security Response Center