A small, one-line upstream kernel change fixed a subtle hardware‑synchronization bug in the Exynos4 camera driver — but the security conversation that followed has been about more than code: it’s about how vendors map open‑source components to products, what a vendor attestation actually means, and whether Microsoft’s public statement naming Azure Linux implies that only Azure Linux is at risk. This piece walks through the technical facts of CVE‑2025‑38237, explains what Microsoft’s advisory text does — and does not — assert, and gives practical, prioritized guidance for admins and engineers who need to determine exposure and remediate risk in heterogeneous environments.
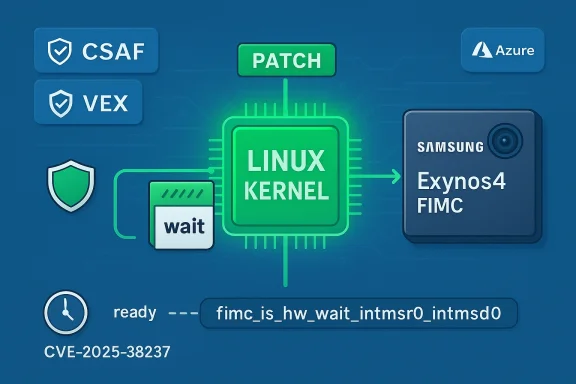
The vulnerability known as CVE‑2025‑38237 lies in the Linux kernel’s media platform driver for Samsung Exynos4 SoCs. In the function
Microsoft’s public advisory for this CVE (the MSRC product update guide) includes a short FAQ line stating, in effect, that “Azure Linux includes this open‑source library and is therefore potentially affected.” Microsoft has also publicly rolled out machine‑readable CSAF/VEX attestations — starting in October 2025 — that map upstream CVEs to specific Microsoft products (Azure Linux being the initial scope). Microsoft promises to expand or update those attestations if additional Microsoft products are found to ship the same upstream component.
Those two facts — the upstream one‑line kernel fix and Microsoft’s product‑mapping statement — are the anchors for this article. What follows is a technical explainer, a forensic checklist for operators, and a pragmatic assessment of why Microsoft’s wording should be read as attestation not exclusion.
This distinction matters operationally: treat Microsoft’s statement as a positive identification for Azure Linux (do patch those images), but do not assume all Microsoft‑published artifacts are safe simply because they are not named.
This is good for transparency — customers running Azure Linux have immediate, authoritative guidance — but it’s also conservative language that can be misread. A short line that names a single product can easily be misinterpreted by readers as an exclusive claim (“only Azure Linux is affected”), when the correct interpretation is: “we have verified Azure Linux ships the component; we will identify and update other Microsoft artifacts if/when we find them to ship it.” Multiple community analyses have reached that same interpretation and recommended artifact‑level verification for environments that consume multiple Microsoft images or kernels.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
The vulnerability known as CVE‑2025‑38237 lies in the Linux kernel’s media platform driver for Samsung Exynos4 SoCs. In the function fimc_is_hw_change_mode() the driver changed camera modes without waiting for the hardware to report that it had completed the transition, opening a race that could lead to corrupted camera data or system hangs. Upstream maintainers addressed the problem by inserting a wait call — fimc_is_hw_wait_intmsr0_intmsd0() — immediately after mode configuration so the kernel synchronizes with the hardware before proceeding.Microsoft’s public advisory for this CVE (the MSRC product update guide) includes a short FAQ line stating, in effect, that “Azure Linux includes this open‑source library and is therefore potentially affected.” Microsoft has also publicly rolled out machine‑readable CSAF/VEX attestations — starting in October 2025 — that map upstream CVEs to specific Microsoft products (Azure Linux being the initial scope). Microsoft promises to expand or update those attestations if additional Microsoft products are found to ship the same upstream component.
Those two facts — the upstream one‑line kernel fix and Microsoft’s product‑mapping statement — are the anchors for this article. What follows is a technical explainer, a forensic checklist for operators, and a pragmatic assessment of why Microsoft’s wording should be read as attestation not exclusion.
What the code change actually did
The technical bug (short, precise)
- The offending function,
fimc_is_hw_change_mode(), wrote new mode registers and then returned without waiting for the hardware to indicate completion. - If subsequent operations were issued immediately, they could race with pending hardware transitions, producing corrupted frames or causing the camera controller to hang.
- The upstream fix adds one call:
fimc_is_hw_wait_intmsr0_intmsd0(is);after the configuration writes, which polls the hardware interrupt/status registers until the hardware signals readiness or a timeout occurs. This reintroduces the same synchronization pattern used elsewhere in the driver.
Why this is a real operational problem
- Camera and ISP code frequently runs in tight real‑time loops where mode changes are triggered by hot plug, power management, or runtime reconfiguration. Missing synchronization allows race windows that are small but exploitable by normal activity patterns.
- The fix is minimal but important: it enforces the established hardware protocol (wait → write → trigger) and avoids subtle, non‑deterministic failures that are hard to reproduce in lab conditions.
What Microsoft actually said — and how to read it
The wording Microsoft used
Microsoft’s update guide and the CSRF/VEX rollout messaging include a consistent FAQ line across many Linux CVEs: Azure Linux “includes this open‑source library and is therefore potentially affected by this vulnerability.” Microsoft also announced it would publish machine‑readable VEX attestations beginning October 2025 and to update CVE records should other products be found to include the same upstream component. This is Microsoft’s stated, product‑level inventory approach.Attestation versus exclusivity — the crucial distinction
- Attestation (what Microsoft did): Microsoft inspected Azure Linux artifacts (their kernels, package builds, or SBOMs) and mapped the upstream kernel component to Azure Linux product lines. That attestation is authoritative for Azure Linux: if your organization runs Azure Linux, treat the product as in‑scope and patch accordingly.
- Exclusivity (what Microsoft did not — and cannot) say: Microsoft’s single‑line product mapping is not a technical proof that no other Microsoft product includes the same code. Other Microsoft artifacts — kernels for WSL, linux packages used in Marketplace images, Azure VM images, appliance images, or specialized kernels such as linux‑azure variants — could include the same upstream driver depending on build choices and kernel versions. Until Microsoft publishes a VEX attestation for another product, or you inspect the artifact yourself, you cannot assume it is unaffected. Multiple independent analyses and community commentary draw the same practical conclusion: Microsoft named Azure Linux because it is the product Microsoft has inventory‑checked so far, not because it is necessarily the exclusive carrier.
Short, plain answer to the user’s question
No — Azure Linux is not necessarily the only Microsoft product that includes the implicated open‑source kernel code. Microsoft has publicly attested that Azure Linux includes the component and therefore is potentially affected; that attestation is authoritative for Azure Linux. But the presence or absence of the same vulnerable code in other Microsoft images, kernels, containers, WSL builds or appliance images is an open question until Microsoft’s VEX/CSAF records are expanded or individual artifacts are inspected.This distinction matters operationally: treat Microsoft’s statement as a positive identification for Azure Linux (do patch those images), but do not assume all Microsoft‑published artifacts are safe simply because they are not named.
Practical steps to determine exposure (fast checklist)
If you operate on premises or in cloud and want to know whether you are affected, follow these prioritized steps.1. Start with Azure Linux images (highest priority)
- If you run Azure Linux VMs or Azure Marketplace images built from Azure Linux kernels, apply the vendor kernel updates immediately — Microsoft has attested these images include the component. Treat Azure Linux as in‑scope and patch promptly.
2. Identify all Linux kernels and images you run
- Inventory all kernel packages: list installed kernel versions on each host (uname -a; dpkg -l|rpm -qa for packages).
- For containers, check the base image: container images commonly include a kernel package only implicitly (but may depend on host kernel) — container runtimes share host kernel, so containerized apps are affected by host kernels, not container images, for kernel driver CVEs.
3. Check for the driver symbol or code in kernels you ship or consume
- On a host, search for the Exynos FIMC driver files or symbol names:
- For installed modules: lsmod | grep fimc; modinfo fimc-is (or similar module name).
- Inspect kernel source snapshots or package content for drivers/media/platform/samsung/exynos4-is.
- If you maintain custom kernels or vendor kernels in your supply chain (e.g., WSL kernels, appliance kernels, dedicated IoT images), inspect the kernel tree that produced those builds for the driver file and commit range. The upstream commit IDs are public and can be searched in kernel trees.
4. Use SBOMs and VEX/CSAF attestations where available
- If Microsoft or your third‑party vendors publish SBOMs or CSAF/VEX attestations for the product/artifact in question, consume those machine‑readable files and query them for the specific CVE or component mapping.
- Microsoft’s VEX rollout was explicitly designed to answer this product‑mapping question; watch for inventory updates beyond Azure Linux.
5. Scan images and artifacts with reproducible tooling
- Use binary/package scanning (syft, grype, OSV scanners, distro advisories) against VM images and containers.
- For Windows environments that host WSL or ship Linux artifacts, make sure WSL kernels are checked: WSL kernels are distinct artifacts Microsoft packages and can carry vulnerable code if they use the same upstream kernel version.
Remediation and mitigation (recommended sequence)
- Patch kernels where available
- Apply upstream kernel updates or vendor kernel package updates containing the fix. The upstream patch is small and has been backported to stable trees in many distributions; prioritize kernel updates on systems that run Exynos4 hardware or distribution kernels that include the driver.
- If you cannot patch immediately, implement mitigation controls
- On devices that do not need camera hardware (headless servers, VMs without Exynos hardware), the risk is low; but on ARM devices or appliances that ship Exynos4 platforms, apply vendor guidance or temporarily disable the module if safe to do so (blacklist the module, rebuild kernels without the driver, or use hardware isolation).
- Avoid rapid automated mode switches or scripts that trigger camera configuration changes until patched.
- Update image and CI/CD pipelines
- Rebuild and redeploy images with patched kernels. Ensure your image build pipeline consumes updated base kernels and that you publish SBOMs for the rebuilt artifacts.
- Use detection: monitor dmesg/kernel logs
- Look for kernel warnings or device timeouts related to FIMC/IS subsystems; the bug can manifest as timeout messages in
dmesgfromfimc_is_wait_event()calls when mode changes timeout.
For cloud customers: special considerations
- Azure VM images: guest VM kernels are managed by the image publisher. If you run an Azure Marketplace image that uses a Microsoft‑published kernel (for example, an image built from Azure Linux), patching will be provided by Microsoft’s image update process. If you maintain a custom kernel, you are responsible for updating it.
- WSL and Windows‑hosted Linux artifacts: WSL’s kernel is a Microsoft artifact; if Microsoft has not attested WSL kernels in a VEX for this CVE it does not mean WSL is unaffected. You must either:
- Check the kernel version that WSL is using, or
- Inspect WSL’s published SBOM/VEX (if available), or
- Wait for Microsoft to expand the attestation and update the CVE record — but don’t rely on waiting if you have risk exposure.
- Azure Marketplace images or vendor appliances: these are independent artifacts; many are maintained by third parties who may or may not have applied the upstream fix — scan these images directly.
Risk analysis: who should care, and why
- High priority (must patch): devices that actually run Exynos4 hardware (embedded devices, IoT appliances, phones or boards based on Exynos4). The driver is hardware‑specific; where the hardware exists, the flaw can cause data corruption or hangs.
- Medium priority: servers and VMs in cloud environments that ship kernels including Exynos4 driver code (this is uncommon on x86 cloud hosts but can appear in distro packages or specialized kernels).
- Low priority: conventional x86 servers without Exynos hardware — the driver will generally not be loaded or used in those environments, so the practical attack surface is limited. However, because kernels are shared components, inventory and verification are essential to avoid blind spots.
Why Microsoft’s wording makes operational sense — but also why it can create confusion
Microsoft’s decision to announce Azure Linux as included and to publish VEX attestations for that product first is consistent with a product‑centric vulnerability response model: identify the product you have inventory for, publish attestations for that product, and commit to expanding coverage.This is good for transparency — customers running Azure Linux have immediate, authoritative guidance — but it’s also conservative language that can be misread. A short line that names a single product can easily be misinterpreted by readers as an exclusive claim (“only Azure Linux is affected”), when the correct interpretation is: “we have verified Azure Linux ships the component; we will identify and update other Microsoft artifacts if/when we find them to ship it.” Multiple community analyses have reached that same interpretation and recommended artifact‑level verification for environments that consume multiple Microsoft images or kernels.
What we could not verify (and how to proceed when evidence is missing)
- We cannot, from Microsoft’s single‑line attestation alone, determine whether other Microsoft products (WSL kernel binaries, specific Marketplace images, appliance kernels inside Azure services, or older linux‑azure kernels) include the vulnerable code. That is an artifact‑level question and requires either:
- A published VEX/SBOM asserting inclusion, or
- Direct inspection of the artifact (kernel tree, package contents, module list).
- Until Microsoft expands its VEX attestations or until vendors publish SBOMs, organizations must assume potential exposure for any Microsoft artifact that includes Linux kernel components and run the checks described earlier.
Recommended action plan for IT/security teams (30/60/90 day)
Day 0–7 (urgent)
- Identify any Azure Linux systems in your environment and apply Microsoft’s kernel updates immediately. Microsoft has attested Azure Linux; treat those images as confirmed carriers.
- Inventory all running Linux kernels and list kernel versions and loaded modules.
- For any systems that run Exynos4 hardware, patch, or mitigate by disabling the module if safe.
Day 7–30 (operational)
- Scan all Marketplace images, appliance images, and WSL kernels in your environment for the Exynos driver.
- Require SBOMs / VEX from third‑party vendors running in your environment and prioritize updates where attested.
- Rebuild images in CI with patched kernels and publish SBOMs for the rebuilt artifacts.
Day 30–90 (strategic)
- Integrate VEX/CSAF processing into your vulnerability management pipeline so vendor attestations update your triage automatically.
- Work with suppliers to obtain SBOMs and confirm whether their artifacts include vulnerable upstream components.
- Where feasible, move to reproducible image builds and pinned kernel versions to avoid unexpected regressions and to make artifact verification deterministic.
Final assessment and takeaways
- The kernel fix for CVE‑2025‑38237 is straightforward and upstream: a synchronization wait was added to
fimc_is_hw_change_mode()to eliminate a hardware race window. The code change is minimal but important for devices that use the Exynos4 FIMC driver. - Microsoft’s public statement that “Azure Linux includes this open‑source library and is therefore potentially affected” is an authoritative attestation for Azure Linux, and Microsoft’s rollout of CSAF/VEX improves transparency. However, that wording is not an exclusive claim: other Microsoft products may include the same upstream component depending on kernel versions and build configuration. Do not assume absence of risk for other Microsoft artifacts until Microsoft publishes additional attestations or you inspect those artifacts yourself.
- Operators should prioritize patching Azure Linux images and any devices that run Exynos4 hardware, inventory all kernels and artifacts, and integrate SBOM/VEX consumption into vulnerability triage to remove ambiguity in future cases.
Source: MSRC Security Update Guide - Microsoft Security Response Center