A newly assigned Linux-kernel vulnerability, tracked as CVE-2025-38485, exposes a race-condition use‑after‑free in the Industrial I/O (IIO) accelerometer driver for the FXLS8962AF sensor: a kernel interrupt handler can observe and use device state after the associated device object has left buffer mode, producing a NULL-dereference and possible kernel crash. Microsoft’s public Security Response Center (MSRC) update for the CVE explicitly states that Azure Linux includes the affected open‑source component and is therefore potentially affected, and that Microsoft will expand its CSAF/VEX attestations to other product families if additional impact is identified. That MSRC attestation is authoritative for Azure Linux, but it does not by itself prove that Azure Linux is the only Microsoft product that could carry the vulnerable code — any Microsoft-distributed artifact that ships a Linux kernel build containing the fxls8962af driver (module or built‑in) may also be a carrier until it is inventoried and attested or patched.
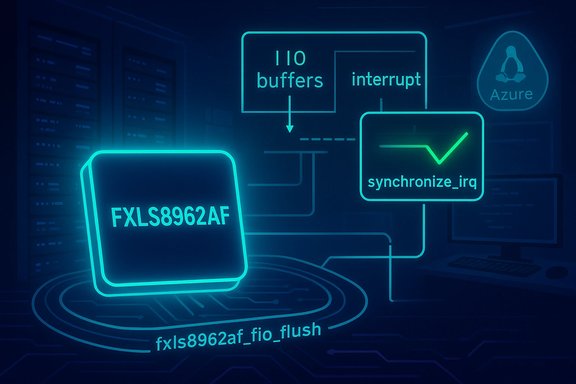
The vulnerability sits in drivers/iio/accel/fxls8962af-core.c inside the Linux kernel: the fifo‑flush routine references indio_dev->active_scan_mask via the iio_for_each_active_channel macro without guaranteeing that the indio_dev remains in buffer mode for the duration of the interrupt handling sequence. A race can occur when buffer mode is disabled concurrently with an interrupt that attempts to flush the device FIFO; the upstream fix synchronizes the disable path with the interrupt path by calling synchronize_irq before switching off buffer mode. The practical symptom reported in public kernel traces is a kernel NULL-pointer dereference leading to an OOPS/crash. Multiple independent vulnerability catalogs and Linux distributors have published identical technical summaries (NVD, Ubuntu, Debian, SUSE, OSV, and others), and the kernel stable‑tree commits that implement the correction were accepted into several stable branches (6.1, 6.12, 6.15, etc.. That cross‑corroboration makes the technical facts of the bug and the upstream remediation verifiable. Why this matters operationally: even though the vulnerability is not an obvious remote code‑execution primitive, a kernel crash on a VM, appliance, or endpoint is an operational availability incident that can take services offline, trigger reboots, and complicate forensic collection. In multi‑tenant cloud environments a local kernel crash on a host or a hypervisor‑level instability can be especially consequential. The practical remediation is to install vendor or distribution kernel updates that incorporate the upstream stable commits, or to disable/blacklist the driver where it is not needed.
Longer, operationally precise answer:
Conclusion: CVE‑2025‑38485 is an availability‑focused kernel defect with a small, backportable fix; Microsoft’s MSRC entry correctly flags Azure Linux as potentially affected and promises broader VEX feed coverage over time. Operational security teams should treat the Azure Linux attestation as high‑priority actionable data, but must not assume exclusivity — verify and patch every Microsoft‑distributed Linux artifact in your estate or confirm Microsoft’s attestations before declaring hosts remediated.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
The vulnerability sits in drivers/iio/accel/fxls8962af-core.c inside the Linux kernel: the fifo‑flush routine references indio_dev->active_scan_mask via the iio_for_each_active_channel macro without guaranteeing that the indio_dev remains in buffer mode for the duration of the interrupt handling sequence. A race can occur when buffer mode is disabled concurrently with an interrupt that attempts to flush the device FIFO; the upstream fix synchronizes the disable path with the interrupt path by calling synchronize_irq before switching off buffer mode. The practical symptom reported in public kernel traces is a kernel NULL-pointer dereference leading to an OOPS/crash. Multiple independent vulnerability catalogs and Linux distributors have published identical technical summaries (NVD, Ubuntu, Debian, SUSE, OSV, and others), and the kernel stable‑tree commits that implement the correction were accepted into several stable branches (6.1, 6.12, 6.15, etc.. That cross‑corroboration makes the technical facts of the bug and the upstream remediation verifiable. Why this matters operationally: even though the vulnerability is not an obvious remote code‑execution primitive, a kernel crash on a VM, appliance, or endpoint is an operational availability incident that can take services offline, trigger reboots, and complicate forensic collection. In multi‑tenant cloud environments a local kernel crash on a host or a hypervisor‑level instability can be especially consequential. The practical remediation is to install vendor or distribution kernel updates that incorporate the upstream stable commits, or to disable/blacklist the driver where it is not needed. Microsoft’s public attestation: what was said, and what it means
The MSRC statement and the CSAF/VEX rollout
Microsoft’s MSRC pages for a number of Linux-kernel CVEs now include a short FAQ answering the question “Is Azure Linux the only Microsoft product that includes this open‑source library and is therefore potentially affected by this vulnerability?” The consistent answer highlights two points: (1) Microsoft has inspected and is committed to keeping Azure Linux (its cloud‑focused Linux distribution) up to date with secure upstream code, and (2) Microsoft began publishing machine‑readable CSAF/VEX attestations in October 2025 and will update the CVE if additional Microsoft products are identified as impacted. That wording appears repeatedly across MSRC entries for Linux CVEs and is the specific language quoted in the question you supplied.How to read Microsoft’s attestation
- The MSRC VEX/CSAF entry is a product‑level inventory statement. When Microsoft explicitly says Azure Linux “includes the open‑source library and is therefore potentially affected,” that is an authoritative attestation for the Azure Linux product family. Treat it as the canonical signal for Microsoft‑published Azure Linux images.
- That attestation is not an automatic or implied statement about every Microsoft artifact. Microsoft ships many independent Linux artifacts — WSL kernels, linux‑azure kernels used by some images, curated Marketplace images, AKS node images, appliance kernels, and other Microsoft-maintained images — each of which is built from possibly different kernel trees and build configurations. Whether those artifacts include the fxls8962af driver depends on build‑time kernel configuration and the kernel version shipped, not on the Azure Linux attestation alone.
- In short: Microsoft has confirmed Azure Linux as known to include the affected code; Microsoft has not implied that no other Microsoft product could contain the same upstream component. Microsoft’s public commitment is to update the CVE/VEX entries if further product impact is found.
Independent verification: what the public record shows
Several trustworthy, independent sources corroborate the technical description and the remediation path:- The National Vulnerability Database (NVD) entry for CVE‑2025‑38485 reproduces the upstream description and links to the kernel.org patch identifiers that implement the fix. This confirms the official industry‑level description and the change set in the kernel stable trees.
- Multiple Linux distributions (Ubuntu, Debian, SUSE) include vendor advisories and package updates mapping the CVE into distribution kernels and shipping fixed packages or backports. Those vendor pages list the CVE as resolved in patched kernel packages.
- The upstream kernel patch and stable‑tree commits (as discussed on maintainers’ lists and stable commit notices) explicitly add synchronize_irq in the buffer‑disable path to avoid the interrupt race; the patch annotations indicate it was accepted for a range of stable branches and should be found in the corresponding stable kernel releases. That patch provenance lets packagers and distributors identify which kernel snapshots contain the remediation.
Short technical summary (for engineers)
- Fault: use‑after‑free / NULL dereference in fxls8962af_fifo_flush when an interrupt flushes FIFO while the device is being disabled from buffer mode.
- Root cause: fifo flush code iterates indio_dev->active_scan_mask without ensuring the device remains in buffer mode for the duration of the interrupt handling. A concurrent path can turn off buffer mode while the interrupt is in progress.
- Upstream fix: call synchronize_irq(data->irq) in the predisable path to ensure no interrupt handler is running before switching off buffer mode, preventing the race window.
- Impact: local availability (kernel OOPS/crash). Not reported as remote code execution or privilege escalation. Attackability depends on local access to the IIO interface for the device (rare on multi‑tenant server images, more common on embedded/SoC device images that expose the accelerometer).
Is Azure Linux the only Microsoft product affected?
Short answer: No — not necessarily.Longer, operationally precise answer:
- Azure Linux is the only Microsoft product that Microsoft has publicly attested to include the implicated upstream component (fxls8962af driver) for CVE‑2025‑38485 at the time of the MSRC entry. That attestation is authoritative for Azure Linux customers and should be acted upon.
- That attestation is product-scoped and phased. Microsoft stated it began publishing CSAF/VEX attestations in October 2025 and will update CVE mappings as it continues inventory work. Absence of a VEX/CSAF mapping for another Microsoft product is not proof the product is free of the vulnerable code — it simply means Microsoft has not yet published an inventory result for it.
- Any other Microsoft artifact that ships a Linux kernel build (for example, the WSL2 kernel Microsoft distributes, linux-azure kernel packages, AKS node images, Marketplace images maintained by Microsoft, or appliance kernels) could include the fxls8962af driver if the kernel source and build configuration used to produce that artifact included drivers/iio/accel/fxls8962af. Presence is an artifact‑level property (CONFIG_* flags and kernel version matter). Therefore, these artifacts must be verified individually.
Practical triage and remediation playbook
The following runbook is engineered for operations, SecOps, and kernel packagers. Apply steps in order and adapt for your environment.1. Identify Microsoft‑supplied artifacts you run
- Inventory all Linux images, kernels, appliance disk images, OS images, containers, and WSL kernels that are Microsoft‑published or Microsoft‑maintained in your estate (Azure VM images, AKS node images, Marketplace images, WSL2 kernels shipped with Windows, linux‑azure kernels, appliance images).
- Treat Azure Linux images as confirmed in‑scope and prioritize them for patching.
2. Check whether a given kernel includes the fxls8962af driver
Run these checks on a running host or in the image you want to inspect:- Identify kernel version:
- uname -a
- Check installed modules:
- lsmod | grep fxls8962af
- modinfo fxls8962af (if module exists)
- Inspect the module tree for presence:
- find /lib/modules/$(uname -r) -type f -name "fxls8962af" -print
- Inspect kernel config:
- zgrep -i "CONFIG_IIO" /proc/config.gz
- grep -i fxls8962af /boot/config-$(uname -r) || grep -i fxls8962af /proc/config.gz
3. For WSL users
- WSL2 uses a Microsoft‑published kernel binary by default on many Windows versions. Check the kernel used by WSL:
- wsl uname -r
- If using a custom WSL kernel, inspect that kernel image and its config.
- If the WSL kernel has the driver compiled in, contact your Windows update and WSL guidance channels for remediation steps or apply a custom WSL kernel rebuild with the upstream fix and configure WSL to use it.
4. Patch or mitigate
- Primary remediation: install vendor/distro kernel updates that explicitly reference CVE‑2025‑38485 or the upstream stable commit IDs. Reboot into patched kernel.
- If kernel update is not immediately possible and the driver is a module:
- Unload or blacklist the module: echo "blacklist fxls8962af" > /etc/modprobe.d/blacklist-fxls8962af.conf and reboot.
- Restrict access to the IIO device nodes in /sys or /dev (LSM/SELinux policies) to reduce unprivileged triggers.
- For embedded BSPs and custom kernels: backport the upstream patch to your branch and rebuild the kernel; the upstream change is intentionally small and backport‑friendly.
5. Validate
- After patching and rebooting, confirm the kernel changelog or package metadata includes the kernel stable commit ID that addresses the CVE.
- Reproduce representative device attach/use scenarios in a test environment and confirm absence of the OOPS traces that referenced fxls8962af_fifo_flush in earlier reports.
Risk analysis: strengths of the upstream fix and residual concerns
Strengths
- The upstream patch is minimal and follows a proven kernel pattern (synchronize interrupts in predisable paths). Smaller patches reduce the risk of regressions.
- The change was accepted into several stable kernel branches, which makes distribution backporting straightforward for packagers.
- Multiple distributions have mapped the CVE and prepared updates, so remediation coverage via normal vendor channels is available for most environments.
Residual concerns and operational risks
- Long tail: embedded vendors, OEM boards, and appliance vendors with slow patch processes may continue to ship vulnerable kernels for months. Those devices often expose IIO drivers and are higher risk.
- Microsoft product footprint: Microsoft’s public VEX/CSAF attestations are phased. Until Microsoft inventories and attests every product family, other Microsoft artifacts may remain an unknown. Relying on the Azure Linux attestation alone is insufficient to prove absence of risk in other Microsoft‑distributed kernels.
- Visibility: kernel OOPSes that auto‑reboot a host can destroy forensic traces. Operators should ensure crash dumps and ring‑buffer logs are captured for post‑incident analysis when possible.
Recommended monitoring and detection signals
- SIEM rule: alert on kernel OOPS traces referencing fxls8962af_fifo_flush, fxls8962af_interrupt, or stack traces that include _find_first_bit_le originating from the fxls8962af call chain.
- Host intrusion detection: monitor dmesg and journalctl for kernel OOPS and panic records and correlate with recent syscalls or device events that touch IIO buffer controls.
- Inventory automation: add an artifact‑level check to your patch pipeline that scans Microsoft‑published images (AKS/Marketplace/WSL kernels) for the fxls8962af module or symbol presence and flags unpatched images for remediation.
What defenders should tell executives and customers
- The outcome of Microsoft’s MSRC entry is positive operationally: Microsoft has confirmed and documented that Azure Linux includes the impacted upstream component and is therefore a known in‑scope product for remediation. That attestation is a useful, machine‑readable signal for automation. However, this attestation is not an implicit guarantee that every Microsoft artifact is safe — absence of attestation is not proof of absence. Microsoft has committed to updating the CVE/VEX record if more products are discovered to be affected.
- Actionable steps: prioritize patching Azure Linux images, inventory all other Microsoft‑distributed Linux artifacts you run, check kernel build config and modules for fxls8962af, and apply vendor kernel updates or mitigations. Document the artifact provenance (SBOM or kernel config) so future VEX attestations can be matched to your environment with confidence.
Final assessment and closing recommendations
- Technical verdict: CVE‑2025‑38485 is a real use‑after‑free NULL‑dereference in the FXLS8962AF IIO accelerometer driver; the upstream patch is small, has been merged across stable kernel trees, and distribution updates are available.
- Microsoft product scope: Azure Linux is the only Microsoft product Microsoft has publicly attested to include the involved upstream code so far; that attestation is authoritative for Azure Linux but does not exclude other Microsoft artifacts from being carriers until they are inventoried and attested or independently inspected. Treat Azure Linux as confirmed in‑scope and audit/validate all other Microsoft‑supplied kernels in your environment.
- Operational priority: patch Azure Linux images immediately where they are used, and execute the inventory, detection, and mitigation playbook above across any other Microsoft images or kernels you operate. If your environment includes embedded devices or vendor appliances, coordinate with vendors for backports or consider short‑term mitigations (blacklisting the driver) when feasible.
Conclusion: CVE‑2025‑38485 is an availability‑focused kernel defect with a small, backportable fix; Microsoft’s MSRC entry correctly flags Azure Linux as potentially affected and promises broader VEX feed coverage over time. Operational security teams should treat the Azure Linux attestation as high‑priority actionable data, but must not assume exclusivity — verify and patch every Microsoft‑distributed Linux artifact in your estate or confirm Microsoft’s attestations before declaring hosts remediated.
Source: MSRC Security Update Guide - Microsoft Security Response Center