Microsoft’s short public attestation that “Azure Linux includes this open‑source library and is therefore potentially affected” is accurate — but it is a product‑scoped inventory statement, not proof that no other Microsoft product can include the same vulnerable kernel code.
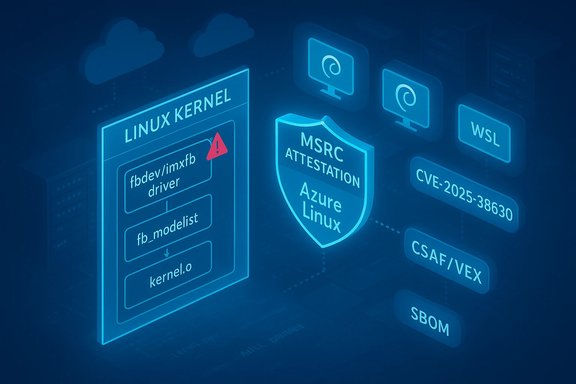
CVE‑2025‑38630 is a Linux kernel robustness fix in the framebuffer (fbdev) subsystem. The defect arises when the imxfb fbdev driver registers a framebuffer while a call to fb_add_videomode fails to allocate its internal mode list; a later helper (fb_videomode_to_var) can then dereference a NULL pointer and cause a kernel oops or panic. The fix is a small defensive check in the kernel source that prevents the registration of an incomplete framebuffer mode state. This technical picture is documented in public vulnerability trackers and the upstream stable kernel commits. Microsoft’s published MSRC line that you quoted — that Azure Linux includes the implicated open‑source component and is therefore potentially affected — is an authoritative, machine‑readable attestation for that Microsoft product family. Microsoft also said it will update the CVE/VEX/CSAF mapping if it identifies additional Microsoft products that ship the same component. That procedural commitment means the MSRC statement is a snapshot of what Microsoft has inventory‑checked so far, not an exclusion of other Microsoft artifacts.
The potential misreading arises when consumers treat a single product attestation as a guarantee that other vendor artifacts are unaffected. That leap can be costly in environments that mix Microsoft artifacts (WSL, linux‑azure kernels, Marketplace images, etc.. The secure operational posture is to treat Microsoft’s attestation as authoritative for the named product and to independently verify every other Microsoft‑supplied artifact you run.
However, to translate that vendor signal into secure operational action, teams must:
That said, the attestation is product‑scoped and not a universal guarantee that other Microsoft artifacts are clean. Any Microsoft artifact that ships a Linux kernel binary — such as WSL2 kernels, linux‑azure kernels for some VM SKUs, curated Marketplace images, AKS node images, or appliance images — can still carry the vulnerable code depending on kernel version and configuration. Absence of a published MSRC attestation for a Microsoft product is absence of evidence, not evidence of absence; customers should therefore verify those artifacts directly using the artifact‑level checklist above and apply vendor fixes or backports as available.
For immediate action: prioritize patching Azure Linux images per Microsoft guidance, inventory other Microsoft‑supplied kernels in your estate, verify kernel builds for fbdev presence, and apply vendor kernel updates or the upstream backport commits where necessary. Use the detection and mitigation steps in this article to reduce exposure until patches are widely applied.
(Verified technical details cross‑checked against the NVD entry for CVE‑2025‑38630 and distribution advisories from Debian/Ubuntu; Microsoft’s attestation and procedural wording are summarized in MSRC VEX/CSAF commentary and vendor guidance.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CVE‑2025‑38630 is a Linux kernel robustness fix in the framebuffer (fbdev) subsystem. The defect arises when the imxfb fbdev driver registers a framebuffer while a call to fb_add_videomode fails to allocate its internal mode list; a later helper (fb_videomode_to_var) can then dereference a NULL pointer and cause a kernel oops or panic. The fix is a small defensive check in the kernel source that prevents the registration of an incomplete framebuffer mode state. This technical picture is documented in public vulnerability trackers and the upstream stable kernel commits. Microsoft’s published MSRC line that you quoted — that Azure Linux includes the implicated open‑source component and is therefore potentially affected — is an authoritative, machine‑readable attestation for that Microsoft product family. Microsoft also said it will update the CVE/VEX/CSAF mapping if it identifies additional Microsoft products that ship the same component. That procedural commitment means the MSRC statement is a snapshot of what Microsoft has inventory‑checked so far, not an exclusion of other Microsoft artifacts.What CVE‑2025‑38630 actually is (technical summary)
- Affected component: Linux kernel fbdev — imxfb (framebuffer driver).
- Fault: fb_add_videomode can return an error (for example -ENOMEM) if its internal kmalloc cannot allocate the fb_modelist structure. If the driver proceeds to register the framebuffer without an initialized modelist, later code that assumes the mode exists can dereference NULL.
- Symptom: kernel oops/KASAN traces showing null‑ptr‑deref in fb_videomode_to_var and call stacks crossing fbcon, fbmem and ioctl entry points.
- Remediation: upstream kernel patches add checks and careful error handling in do_register_framebuffer / fb_add_videomode to avoid registering incomplete state. The commits have been merged into stable kernel trees and distribution vendors have mapped fixes into package updates.
How to read Microsoft’s statement: attestation vs. exclusivity
Microsoft’s wording performs two roles:- It reports a completed inventory check for a named product family — Azure Linux — and declares that product potentially includes the upstream component that maps to the CVE. That attestation is actionable for anyone running Azure Linux images.
- It does not assert that other Microsoft components are definitively free of the same upstream code. Microsoft’s wording expressly says it will update the CVE if additional Microsoft products are identified, which implies that the initial attestation was scoped to what the company had scanned so far. In other words: absence of an attestation is not evidence of absence.
Is Azure Linux the only Microsoft product that includes the library and is therefore potentially affected?
Short answer: No — not necessarily.- Azure Linux is the only Microsoft product Microsoft has publicly attested as including the affected component for this CVE at the time of the advisory. That is the authoritative “yes” for Azure Linux customers and automation that consumes MSRC’s machine‑readable VEX/CSAF artifacts.
- However, the attestation’s scope is limited to the artifacts Microsoft has completed inventory checks for. Other Microsoft‑distributed artifacts that ship Linux kernel binaries or include vendor kernels could include the same fbdev code depending on kernel version and build configuration. Examples of plausible Microsoft artifacts to check include:
- WSL2 kernel images that Microsoft publishes and ships with Windows — these are Microsoft‑built kernels and their CONFIG_* choices determine inclusion of fbdev drivers.
- linux‑azure kernel packages that Microsoft publishes for some VM SKUs.
- Curated Marketplace VM images or partner appliances that Microsoft distributes in Azure (publisher images can embed different kernel builds).
- AKS node images or container base images where a vendor kernel or userland might include framebuffer code.
- Internal test images, appliance firmware, or partner deliverables that embed custom kernels.
Why the attestation approach is reasonable — and where it can be misread
Vendors are increasingly publishing machine‑readable VEX/CSAF attestations to make triage easier for customers. The practical reason Microsoft started with Azure Linux is simple: Azure Linux is a Microsoft‑built Linux distribution and kernel family where Microsoft controls and can inspect the build artifacts end‑to‑end. Publishing per‑product attestations first for that family produces deterministic, machine‑actionable signals for customers running those images.The potential misreading arises when consumers treat a single product attestation as a guarantee that other vendor artifacts are unaffected. That leap can be costly in environments that mix Microsoft artifacts (WSL, linux‑azure kernels, Marketplace images, etc.. The secure operational posture is to treat Microsoft’s attestation as authoritative for the named product and to independently verify every other Microsoft‑supplied artifact you run.
Practical verification checklist (artifact‑level triage)
Below is a prioritized, practical checklist to determine whether a running host or image is susceptible. These steps are short, artifact‑focused, and repeatable in automation.- Inventory and identify candidate Microsoft artifacts to check
- Azure Linux VM images (attested by MSRC).
- WSL2 kernel images on Windows hosts.
- linux‑azure kernel packages on managed VM SKUs.
- Marketplace or partner images and any custom appliance kernels.
- Container base images that may carry vendor kernels (less common for kernel code, but check host kernels).
- On a running Linux host (VM or WSL) — immediate checks
- Confirm kernel version:
uname -r - Inspect kernel build and config (if available):
zgrep 'CONFIG_FB' /proc/config.gzorgrep -E 'CONFIG_FB' /boot/config-$(uname -r) - Check for framebuffer device nodes:
ls -l /dev/fb*(presence indicates runtime framebuffer support) - Check loaded modules:
lsmod | grep -E 'fbcon|fbdev|imxfb|vesafb' - Search System.map for the symbol (if present):
grep -F 'fb_videomode_to_var' /boot/System.map-$(uname -r) || true - Match kernel version to vendor advisories and upstream commits
- Compare
uname -rto distribution CVE advisories or kernel stable backports; Debian/Ubuntu and NVD list affected and fixed versions for this CVE. - If your vendor has released a kernel package with the fix, upgrade to that package and reboot.
- For WSL2
- Check the WSL kernel version (inside the WSL distro:
uname -r) and, if you run the Microsoft‑distributed kernel, consult Microsoft’s WSL kernel release notes or the WSL kernel git repo/config to determine whether the build includes fbdev support. - If you run a custom WSL kernel, rebuild with the upstream fix applied.
- For images and offline artifacts
- Inspect the image manifest/SBOM if available.
- Mount the image and inspect
/boot/config-[I],/lib/modules/[/I]and/boot/System.map-*to detect fbdev symbols. - Look for exploit indicators
- Search logs and SIEM for kernel oops/KASAN traces referencing
fb_videomode_to_var,modedb.c,fbcon.c, orfbmem.c. Such traces indicate the defective code path executed.
Short‑term mitigations and remediation
Preferred remediation: install vendor kernel packages that contain the upstream fix and reboot hosts according to change windows. Distribution vendors and the upstream kernel stable trees include the defense; apply the packaged updates from your distro or Microsoft‑supplied kernel images as they become available. Debian and Ubuntu trackers already list fixed package versions for the kernel trees fixing this CVE. If immediate kernel updates or reboots are infeasible, consider these mitigations:- If framebuffer console support is not needed, blacklist related modules (test first):
- Create
/etc/modprobe.d/blacklist-fb.confcontaining: blacklist fbconblacklist fbdevblacklist imxfb- Update initramfs if required and reboot to ensure modules do not get loaded.
- Note: disabling fbdev can affect console output and devices that rely on framebuffer drivers — evaluate impact.
- Restrict local attack surface:
- Tighten access to device nodes (for example, ensure untrusted containers/tenants cannot access
/dev/fb[I]or/dev/dri/[/I]unless explicitly required). - Use host hardening and container runtime seccomp/SELinux/AppArmor policies to reduce the ability of unprivileged processes to reach ioctl paths that interact with framebuffer drivers.
- Monitor aggressively:
- Add SIEM alerts for oops/KASAN messages referencing fbdev symbols and track any kernel crashes in affected pools.
Risk assessment — who should care most?
- Operators of Azure Linux images: Microsoft has attested Azure Linux includes the implicated code; these images should be prioritized for remediation.
- Environments that host multi‑tenant workloads, CI runners, or shared systems: kernel oopses or panics can cause wide availability impact and can be triggered by local interactions with device drivers.
- Appliance and embedded device vendors who still ship legacy framebuffer drivers: these code paths are more commonly present in images intended for graphical or SoC platforms.
- Administrators of Windows hosts running WSL2 where the WSL kernel image is Microsoft‑distributed: verify whether the specific WSL kernel build includes fbdev support and whether Microsoft has published a WSL kernel update addressing the issue.
Why Microsoft’s attestation model is helpful — and how customers should use it
Microsoft’s phased rollout of machine‑readable CSAF/VEX attestations (beginning with Azure Linux in October 2025) is a pragmatic and useful evolution in vendor transparency: it provides automation‑friendly signals that map specific CVEs to named product families. For customers who run Azure Linux images, the attestation cuts the triage time significantly because it states Microsoft has already performed an artifact inspection and found the component.However, to translate that vendor signal into secure operational action, teams must:
- Ingest VEX/CSAF metadata into their vulnerability management pipelines.
- Treat each vendor attestation as product‑scoped and still verify other vendor artifacts you run.
- Maintain artifact‑level inventory (SBOMs, image manifests) so you can answer whether a particular WSL kernel, marketplace image, or appliance uses a vulnerable component.
Conclusion — practical takeaway
Microsoft’s MSRC statement is correct and helpful: Azure Linux is confirmed to include the affected fbdev code and is potentially affected by CVE‑2025‑38630. That attestation is authoritative for Azure Linux customers and should be treated as a high‑priority remediation target.That said, the attestation is product‑scoped and not a universal guarantee that other Microsoft artifacts are clean. Any Microsoft artifact that ships a Linux kernel binary — such as WSL2 kernels, linux‑azure kernels for some VM SKUs, curated Marketplace images, AKS node images, or appliance images — can still carry the vulnerable code depending on kernel version and configuration. Absence of a published MSRC attestation for a Microsoft product is absence of evidence, not evidence of absence; customers should therefore verify those artifacts directly using the artifact‑level checklist above and apply vendor fixes or backports as available.
For immediate action: prioritize patching Azure Linux images per Microsoft guidance, inventory other Microsoft‑supplied kernels in your estate, verify kernel builds for fbdev presence, and apply vendor kernel updates or the upstream backport commits where necessary. Use the detection and mitigation steps in this article to reduce exposure until patches are widely applied.
(Verified technical details cross‑checked against the NVD entry for CVE‑2025‑38630 and distribution advisories from Debian/Ubuntu; Microsoft’s attestation and procedural wording are summarized in MSRC VEX/CSAF commentary and vendor guidance.
Source: MSRC Security Update Guide - Microsoft Security Response Center