A recently disclosed Linux kernel vulnerability in the ksmbd subsystem — tracked as CVE-2025-40039 — fixes a subtle but consequential race condition in the kernel SMB server’s RPC handle list that could lead to inconsistent state, data corruption, or use‑after‑free when RPC handles are accessed concurrently; maintainers remedied the flaw by correcting rw_semaphore usage and adding the appropriate read/write locking around XArray operations.
ksmbd is the in‑kernel implementation of an SMB server for Linux that aims to provide high‑performance SMB services without relying on userland daemons. It exposes server functionality directly inside the kernel, managing per‑session state and RPC handles via kernel primitives such as XArray and rw_semaphores. The kernel’s XArray API is powerful but sensitive: callers must correctly serialize concurrent accesses when using xa_store, xa_erase, and xa_load to avoid races and memory-consistency hazards.
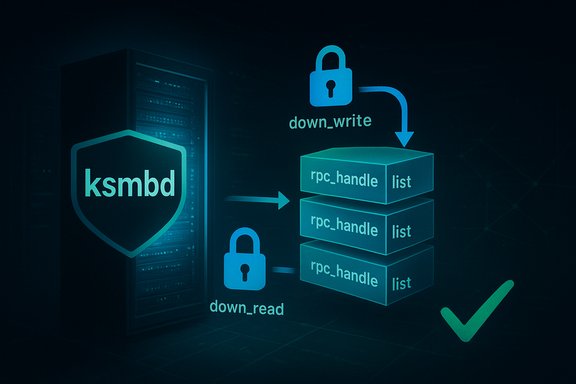
The public advisory and vendor indexes describe CVE‑2025‑40039 as a race in the way ksmbd guards its session RPC handle list (sess->rpc_handle_list) with sess->rpc_lock. In several code paths developers acquired the wrong lock type or omitted locking altogether: ksmbd_session_rpc_open took a read lock before invoking xa_store and xa_erase, and ksmbd_session_rpc_method performed xa_load without any lock. The fix converts the modifying path to obtain a write lock (down_write/up_write) and protects the lookup path with a read lock (down_read/up_read).
Practical remediation steps:
Treat this CVE as important because it affects a kernel component that runs in privileged context; even timing/race bugs require careful handling since skilled adversaries can amplify timing windows into reliable exploit primitives. Apply patches as soon as possible, monitor systems for ksmbd instability, and, where practical, restrict network reachability to reduce exposure while the update is deployed. For operators tracking vendor communications, Microsoft’s public advisory platforms and major distribution security trackers have ingested the CVE and provide vendor mappings; consult your distro’s advisory and kernel package changelog for the authoritative package that contains the stable backport or updated kernel.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
ksmbd is the in‑kernel implementation of an SMB server for Linux that aims to provide high‑performance SMB services without relying on userland daemons. It exposes server functionality directly inside the kernel, managing per‑session state and RPC handles via kernel primitives such as XArray and rw_semaphores. The kernel’s XArray API is powerful but sensitive: callers must correctly serialize concurrent accesses when using xa_store, xa_erase, and xa_load to avoid races and memory-consistency hazards.The public advisory and vendor indexes describe CVE‑2025‑40039 as a race in the way ksmbd guards its session RPC handle list (sess->rpc_handle_list) with sess->rpc_lock. In several code paths developers acquired the wrong lock type or omitted locking altogether: ksmbd_session_rpc_open took a read lock before invoking xa_store and xa_erase, and ksmbd_session_rpc_method performed xa_load without any lock. The fix converts the modifying path to obtain a write lock (down_write/up_write) and protects the lookup path with a read lock (down_read/up_read).
Overview of the vulnerability
- Vulnerability identifier: CVE-2025-40039.
- Component: ksmbd (Linux kernel SMB server implementation).
- Root cause: incorrect synchronization — read locks used where write locks were required, and unprotected reads of a shared XArray that can be concurrently modified.
- Primary functions implicated: ksmbd_session_rpc_open (modifies XArray with xa_store/xa_erase while holding only a read lock) and ksmbd_session_rpc_method (reads XArray with xa_load without locking).
- Remediation approach: replace read locking with write locking on modification paths, and add read locks for lookups; ensure correct lock release on error paths.
Technical anatomy — what went wrong, in plain terms
The ksmbd implementation keeps an XArray (sess->rpc_handle_list) that maps handle IDs to per‑RPC data structures. The XArray API supports concurrent access, but the caller must guarantee proper synchronization semantics depending on the operations:- xa_load can read pointers that another concurrent thread may free if it also removes the entry.
- xa_store and xa_erase modify the XArray structure and must be performed with exclusive access to prevent structural races and corruption.
- ksmbd_session_rpc_open intended to create or remove RPC handles but only acquired a read lock (rwsem read mode). A read lock admits multiple concurrent readers and, crucially, does not prevent other threads from performing modifications. Calling xa_store or xa_erase under a read lock therefore opened the door to concurrency races where multiple modifier paths interleave or where reads observe intermediate state, potentially causing data corruption or free‑while‑use scenarios.
- ksmbd_session_rpc_method performed a direct xa_load to return a handle pointer without acquiring any lock. That left a window where the entry could be removed by another thread, freeing the referenced structure while the reader still dereferenced it — classic use‑after‑free territory. The correct discipline is to shield xa_load with a read lock so that removals must obtain the write lock (and therefore cannot proceed concurrently).
Code‑level summary of the fix
At the code level the upstream patch series implements the following changes:- Replace the read lock acquisition in ksmbd_session_rpc_open with a write lock via down_write and up_write so that xa_store and xa_erase run under exclusive access.
- Add a read lock (down_read/up_read around the xa_load in ksmbd_session_rpc_method so lookups cannot race with removals.
- Ensure locks are released on all error paths (explicitly handling early returns that previously missed up_* calls).
- Keep the XArray structure use otherwise untouched — the patches are surgical and focused on synchronization rather than redesigning the ksmbd RPC subsystem.
Impact and exploitability
Real‑world impact depends on a few practical factors:- ksmbd runs inside the kernel and therefore any memory‑safety violation or use‑after‑free can have outsized consequences: kernel oopses, panics, or, in worst cases, exploitable memory corruption enabling privilege escalation. Because ksmbd is a kernel component, consequences are not limited to a single process.
- The attack vector is local for many practical deployments: an attacker must be able to reach and interact with ksmbd RPC endpoints in ways that trigger the affected code paths. Whether that is local or remote depends on deployment: if a host exposes the kernel SMB server over a network interface reachable by an attacker, the vector becomes network‑accessible. Many vulnerability landing pages emphasize the need to assess exposure according to your topology and whether ksmbd is reachable.
- Timing sensitivity and required primitives: the bug is a classic race condition — exploitation generally requires an ability to race concurrent operations reliably. Skilled exploit developers can often stabilize such races (via repeated attempts, thread/process affinity tricks, or heap grooming), but the complexity is higher than a trivial memory corruption. Public trackers assign moderate-to-high severity ratings to this CVE because of the kernel context and potential impact, even if remote exploitation is not trivially universal.
- Public evidence as of disclosure: at the time the advisory and indexes were published there were no widely circulated weaponized exploit PoCs. Absence of proof‑of‑concept does not imply safety — kernel races are frequently weaponized once details are public unless mitigations are applied quickly. Treat the advisory as actionable.
Which kernel versions and distributions are affected
Upstream advisories and vulnerability trackers do not always enumerate every downstream distribution mapping; instead they point to upstream commits and stable commit IDs that include the fix. Security vendors and distro trackers (Debian, SUSE, etc. have ingested the CVE entry and will map it to distribution kernel package updates in their advisories. Confirm the presence of the fix by:- Checking your distribution's security tracker or advisories for CVE‑2025‑40039 and the kernel package that contains the backport or the updated kernel version.
- For custom kernels, verify the upstream stable commits are present in your tree (the stable commit references are published in tracker pages and stable.git records). The kernel commit IDs implementing the fix are published in public stable trees.
Detection and verification
To verify whether a host is vulnerable or patched, operators should:- Inspect kernel package changelogs and vendor advisories for explicit mention of CVE‑2025‑40039 or the ksmbd synchronization fix. Distribution security pages (Debian, SUSE, etc. are already indexing the CVE and will show which package releases include the patch.
- If building kernels manually, search your kernel source tree for the relevant commit messages and the changed locking calls in ksmbd_session_rpc_open and ksmbd_session_rpc_method. Confirm down_write/up_write and down_read/up_read invocations are present. Kernel stable commit links cited in advisories are authoritative.
- Monitor kernel logs (dmesg/journal) for oopses or warnings produced by ksmbd during high concurrency RPC activity. Reproducers for races are fragile; a steady stream of RPC activity that touches handle management could reveal instability on unpatched hosts. While this is not a definitive detection method, unexplained ksmbd crashes or oops traces correlated with RPC operations are strong indicators.
- Use distro‑provided vulnerability scanners and patch‑management tools to inventory CVE presence across fleets and to validate package updates. These tools will often map CVE entries to shipped packages once distros release updated kernels.
Remediation and mitigation
The authoritative remediation is to install a kernel update that includes the upstream patch or a vendor backport and reboot into the patched kernel.Practical remediation steps:
- Identify affected hosts running ksmbd and determine exposure (is ksmbd network-facing, embedded in appliances, or running on multi-tenant build hosts?. Prioritize hosts with public or untrusted network exposure.
- Apply vendor/distribution kernel updates as soon as they are available and validated in your environment. Use your standard change control and test the updated kernels in a controlled pilot ring before wide deployment.
- Where immediate patching is impossible, mitigate exposure by:
- Restricting network access to SMB services (firewall rules blocking SMB ports and kernel SMB interfaces).
- Removing or disabling ksmbd if it is not required in a given environment (ensure you understand functional impacts before disabling).
- Enforcing host‑level segmentation to prevent untrusted local users from being able to reach ksmbd RPC paths.
- After patching, verify the fix by confirming package changelogs or kernel commit presence and monitor logs for the absence of rsmbd/ksmbd crash signatures during representative workloads.
Operational risk assessment — who should act first
- Appliance vendors and embedded device operators: devices that ship a kernel with ksmbd enabled and that accept SMB connections from external networks should prioritize patches; embedded kernels are often slow to update and may require vendor assistance.
- Cloud and multi‑tenant CI/Build hosts: environments that run untrusted workloads or let users provide arbitrary code have an elevated attack surface, because local processes combined with race conditions can be chained into broader escalations. Prioritize these machines for immediate patching.
- Servers exposing SMB services publicly or to broad internal networks: if ksmbd is present on hosts accessible by many clients, prioritize remediation and network segmentation. Confirm whether the host actually uses ksmbd or a userland SMB server; only active ksmbd instances are directly affected.
Critical analysis — strengths and residual risks
Strengths of the upstream fix- The patch is surgical and small in scope: it corrects locking semantics rather than rearchitecting the RPC subsystem. Small, focused fixes reduce regression risk and are straightforward for downstream backports.
- The remedy aligns with standard kernel concurrency discipline: writers obtain exclusive locks, readers obtain shared locks, and the locking behavior is now consistent with XArray modification requirements. This is a recognized best practice and lowers the chance of similar races recurring on the same code paths.
- Race conditions are inherently context sensitive. Even with the specific XArray races fixed here, other ksmbd paths that manage shared state may harbor distinct races. Comprehensive concurrency audits and testing remain necessary.
- Kernel patches that change locking behavior can introduce performance tradeoffs. Using write locks where previously read locks were allowed may serialize some operations more than before; this is correct for safety but could affect throughput under heavy RPC churn. Operations teams should validate performance in test rings where RPC load is representative.
- The fix prevents the specific inconsistent‑read/use‑after‑free pattern described, but does not eliminate the need for continued vigilance: kernel subsystems that mix dynamically allocated objects, asynchronous completions, and shared collections remain high‑risk. Invest in fuzz testing, concurrency testing, and review of similar XArray usage sites.
- Any assertion that CVE‑2025‑40039 was exploited in the wild before the fix was applied should be treated cautiously unless corroborated by incident reports or vendor notices. Public vulnerability feeds at disclosure did not present confirmed in‑the‑wild exploitation evidence; absence of evidence is not proof of safety, so treat the CVE as actionable and patch promptly while investigating telemetry for suspicious signs.
Practical checklist for administrators
- Inventory: identify all systems running ksmbd or any kernel that claims ksmbd support. Use package inventories and kernel configuration audits.
- Map: consult your distribution security tracker or vendor advisory for the CVE → package mapping and KB notes; do not rely on generic advisories only.
- Patch: schedule and test the vendor kernel update that contains the stable commit or backport. Reboot hosts into the patched kernel.
- Mitigate: if patching is delayed, block or restrict SMB access to untrusted networks and consider disabling ksmbd where unused.
- Verify: confirm the fix by checking kernel package changelogs or by grepping the kernel source for down_write/down_read invocations in the ksmbd RPC code.
- Monitor: add or review telemetry for kernel oopses, ksmbd crashes, and abnormal SMB RPC behavior. Preserve logs for forensics if anomalies appear.
Closing assessment
CVE‑2025‑40039 is an instructive example of how a minor mismatch between intended synchronization policy and actual code can create serious, kernel‑level risk. The upstream fix is appropriately surgical — converting mistaken read locks into write locks for modifying operations and adding read protection for lookups — and has been merged into the stable kernel trees. Operators must still act: confirm whether ksmbd is in use on your hosts, prioritize patch rollouts for exposed or multi‑tenant systems, and validate the fix in controlled test rings.Treat this CVE as important because it affects a kernel component that runs in privileged context; even timing/race bugs require careful handling since skilled adversaries can amplify timing windows into reliable exploit primitives. Apply patches as soon as possible, monitor systems for ksmbd instability, and, where practical, restrict network reachability to reduce exposure while the update is deployed. For operators tracking vendor communications, Microsoft’s public advisory platforms and major distribution security trackers have ingested the CVE and provide vendor mappings; consult your distro’s advisory and kernel package changelog for the authoritative package that contains the stable backport or updated kernel.
Source: MSRC Security Update Guide - Microsoft Security Response Center