Microsoft’s brief public guidance on CVE-2025-4432 — that “Azure Linux includes this open‑source library and is therefore potentially affected” — is an authoritative, product‑level attestation for Azure Linux, but it is not a categorical exclusion that other Microsoft products cannot also contain the vulnerable ring crate; absence of attestations for other products is not proof of absence.
CVE-2025-4432 is an availability/denial‑of‑service class bug affecting the Rust cryptography crate ring. In short, certain AES-related functions in ring can panic when Rust overflow checks are enabled; this can be triggered in network protocols (notably QUIC header‑protection handling) or by processing very large single-chunk encrypt/decrypt operations on 64‑bit targets. The maintainers released fixes in the 0.17.x series; upstream advisories mark fixed versions as 0.17.12 and later (the ring release and advisory timelines vary slightly across trackers). The practical footprint of this vulnerability is narrow: overflow checking is disabled in optimized release builds by default, and many protocols and libraries break data into smaller chunks — making the high‑volume single‑chunk AES path relatively uncommon in production. Nevertheless, QUIC header protection code paths and debug builds or non‑standard RUSTFLAGS where overflow checks are enabled are plausible attack surfaces. Security advisories and trackers assigned a medium severity (CVSS ~5.3) and treat the primary impact as availability (panics/DoS).
Two important, connected meanings flow from Microsoft’s wording:
Appendix — Quick reference commands and checks
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CVE-2025-4432 is an availability/denial‑of‑service class bug affecting the Rust cryptography crate ring. In short, certain AES-related functions in ring can panic when Rust overflow checks are enabled; this can be triggered in network protocols (notably QUIC header‑protection handling) or by processing very large single-chunk encrypt/decrypt operations on 64‑bit targets. The maintainers released fixes in the 0.17.x series; upstream advisories mark fixed versions as 0.17.12 and later (the ring release and advisory timelines vary slightly across trackers). The practical footprint of this vulnerability is narrow: overflow checking is disabled in optimized release builds by default, and many protocols and libraries break data into smaller chunks — making the high‑volume single‑chunk AES path relatively uncommon in production. Nevertheless, QUIC header protection code paths and debug builds or non‑standard RUSTFLAGS where overflow checks are enabled are plausible attack surfaces. Security advisories and trackers assigned a medium severity (CVSS ~5.3) and treat the primary impact as availability (panics/DoS). What Microsoft actually published (and how to read it)
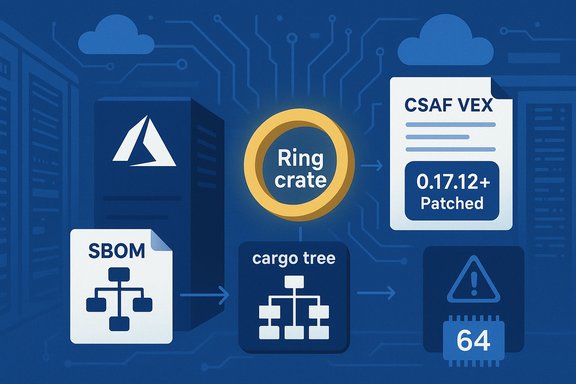
Microsoft’s Security Response Center (MSRC) published a machine‑readable VEX/CSAF attestation that maps the upstream ring component into the Azure Linux product family and states that “Azure Linux includes this open‑source library and is therefore potentially affected.” That statement is a precise inventory result: Microsoft checked the Azure Linux images they maintain and found the implicated component, so Azure Linux is in‑scope for remediation and should be treated as such by site operators. Microsoft also explained that it began publishing CSAF/VEX attestations in a phased rollout and will update CVE records if additional Microsoft products are identified as carriers.Two important, connected meanings flow from Microsoft’s wording:
- Authoritative yes for Azure Linux: Microsoft has inventory evidence that Azure Linux contains the implicated crate. If you run official Microsoft Azure Linux images, treat the Microsoft attestation as a definitive vendor signal to patch or otherwise mitigate.
- Not proof of exclusivity: The attestation does not assert that Microsoft has scanned every product or binary it ships; it only records what inventory work has been completed and published so far. Microsoft’s public commitment to expand VEX/CSAF coverage means other Microsoft products may be added to the attestation set later if they are found to ship the same vulnerable component.
Technical summary of CVE‑2025‑4432
- Affected component: ring crate (Rust cryptography library), AES/AEAD/QUIC header‑protection paths.
- Failure mode: panic (Rust unwind/abort) when overflow checks are enabled; in QUIC header protection code a specially crafted packet can induce the panic. On 64‑bit targets, AES encrypt/decrypt of ~68,719,476,700 bytes (~64 GiB) in a single chunk can trigger overflow-checked arithmetic paths that panic.
- Typical exposure: debug builds or builds with RUSTFLAGS="-C overflow-checks" or Cargo.toml profile flags that enable overflow checking, or unusual single‑chunk encryption workloads. Release builds with default settings are generally not affected.
- Fix status: upstream fixes were rolled into the 0.17.x release line; distributions and package maintainers have published patched packages. Developers should upgrade to the fixed ring release (0.17.12+ per upstream advisory) and rebuild binaries where ring is linked.
Short, operational answer to the user’s question
- Is Azure Linux the only Microsoft product that includes the ring library and is therefore potentially affected?
No — Azure Linux is the only Microsoft product Microsoft has publicly attested (via CSAF/VEX) as including the ring crate in the context of CVE‑2025‑4432 at the time of the advisory. That attestation is authoritative for Azure Linux images Microsoft publishes. However, the statement is not an exclusion; other Microsoft artifacts could also include ring and therefore be potentially affected until Microsoft inventories them and updates its VEX/CSAF attestations.
Why the difference matters: attestation vs. exclusivity
Vendor attestations are a crucial step toward automation and clarity: a VEX/CSAF file is a machine‑readable mapping between a CVE and the product artifacts a vendor has checked. But inventory is an operational process with scope and phasing. Microsoft began its CSAF/VEX rollout with Azure Linux; this is a practical choice, not a statement that no other Microsoft product can carry the same upstream component. In short:- An attestation is a positive confirmation that a given product ship includes a component; it is not a blanket statement about other products.
- Microsoft ships a wide range of Linux‑adjacent and Rust‑using artifacts (cloud images, Marketplace appliances, container images, SDKs, agent binaries, developer tools). Any of those artifacts that embed or package a Rust binary linking ring could carry the vulnerability until confirmed otherwise.
Microsoft products and artifacts that could plausibly carry ring
Ring is a userland Rust crate. That means typical Microsoft places to look are userland artifacts and packages rather than kernel builds. Plausible carriers include:- Azure Linux (attested): Microsoft’s own CBL‑Mariner/Azure Linux lineage — already flagged in the VEX/CSAF attestation.
- Marketplace VM images and partner appliances that Microsoft distributes: images can include Rust programs or distro packages that bundle ring as a dependency. Inventory for each image is per‑artifact.
- Container images and AKS node images: container images often include distribution packages or language runtimes that could depend on ring. If a container image contains a Rust binary linked against ring, it’s in scope.
- Microsoft‑published Rust code and SDKs: Microsoft’s open‑source repositories (for example, Azure SDKs or telemetry/agent code) may include Rust projects; those are source artifacts that become carriers if Microsoft or downstream consumers ship compiled binaries with ring. Search the code base and CI/CD outputs to see if ring is included in built artifacts.
- Third‑party packages included in Microsoft runtime environments: many distributions include ring indirectly (for example, via rustls or other crates). Distributors that repack userland components into images or packages can bring ring into Microsoft artifacts.
How to determine whether a Microsoft artifact you run is affected (practical checklist)
- Inventory scope first. Enumerate the Microsoft images and binaries you run:
- Azure Linux images (official images and any custom images derived from them).
- AKS/VM images from the Azure Marketplace.
- Container images used in your environment that were built from Microsoft base images.
- Any Microsoft‑distributed agents, SDKs, or software that are compiled as Rust binaries in your environment.
- Search build artifacts and SBOMs for ring:
- Check Cargo.lock, Cargo.toml, and compiled dependency manifests for “ring” or for crates that depend on ring (for example, older rustls versions). Use cargo tree or scanning tools to find transitive dependencies.
- If images include distribution packages, search package lists (rpm/dpkg) for Rust packages and then inspect the package contents; some distributions bundle Rust binaries in language‑specific packages.
- Use automated tools:
- Run cargo-audit or RustSec checks on any in‑house or third‑party Rust projects in your supply chain.
- Use SBOM tooling and artifact scanners that detect crates and crate versions inside images or binaries.
- For containers and images, use image scanners that enumerate package contents and language runtime artifacts.
- Verify build flags and modes:
- If a binary was built in release mode with default flags, overflow checks are normally disabled; debug builds or CI/test builds may enable overflow checking and therefore carry higher risk. Check CI build configuration for RUSTFLAGS or Cargo.toml profile settings.
- Confirm patched versions:
- If a project depends on ring, ensure it has been updated to the patched release (0.17.12+ per upstream advisory) and recompiles all artifacts. Rebuilding a binary with an updated ring dependency removes the exposure.
- For Azure Linux images specifically:
- Follow Microsoft’s published guidance for Azure Linux updates and rely on the VEX/CSAF attestation for the product‑level status; treat Azure Linux instances as in‑scope until Microsoft marks them fixed.
Recommended remediation steps (for operators and developers)
- Prioritize Azure Linux workloads: because Microsoft has attested Azure Linux as potentially affected, ensure Azure Linux images are updated with the patched ring packages and that VMs/containers using those images are rebuilt and restarted as necessary.
- For Rust developers and CI owners:
- Update Cargo.toml/Cargo.lock to require ring >= 0.17.12.
- Rebuild release artifacts and redeploy.
- Run cargo-audit and RustSec checks in CI to catch regressions or transitive dependencies.
- Ensure debug/test infrastructure is isolated and monitored; debug builds enabling overflow checks are the more likely environment to trigger panics.
- For image/container owners:
- Scan images for the ring crate or binaries that statically include ring. Replace or rebuild images that include an affected ring dependency.
- For organizations using third‑party or marketplace software:
- Ask vendors for SBOMs or build manifests. If a vendor‑published artifact includes ring, request confirmation of patching or a fixed repack.
- Monitor Microsoft VEX/CSAF feeds:
- Microsoft committed to updating CVE entries and VEX/CSAF attestations if more products are found to ship the vulnerable component. Monitor MSRC and the VEX feeds for changes to product mappings.
Risk assessment — who should worry most
- High priority: cloud operators running Azure Linux images (Microsoft attested). If you run official Azure Linux images or descendant images, patch and redeploy promptly.
- Medium priority: teams running Rust‑based network daemons that use QUIC header protection code or that perform very large single‑chunk AES operations, especially when debug or overflow‑checked builds are used in production or test harnesses.
- Low priority: most typical release-mode web servers and TLS stacks that chunk data and are built with default release flags; these environments are less likely to trigger the condition.
- Unknowns / posture decisions: environments using third‑party Microsoft artifacts (Marketplace images, agent binaries, compiled SDK deliverables) — treat as unknown until verified and handled per the checklist above.
Strengths and limitations of Microsoft’s VEX/CSAF approach
Strengths:- Machine‑readable attestations are useful for automation: security teams can programmatically triage artifacts specifically called out as “known affected” and reduce noise from generic distro CVE alerts. Microsoft’s decision to publish VEX/CSAF for Azure Linux gives a clear signal for those images.
- Phased rollout leaves windows of uncertainty: until Microsoft has inventoried other product families and published corresponding attestations, customers must assume that other Microsoft‑distributed artifacts could be carriers. Absence of a VEX entry for a product is not the same as a vendor‑verified “not affected” status.
- Per‑artifact variability: whether a product is affected is an artifact property (depends on dependency set, build flags, static linking, and packaging). Automated OS-level scanners that only look at distro package names may miss statically compiled Rust binaries that embed vulnerable crates.
What to watch for next (timeline and signals)
- Vendor updates and distribution patches: upstream ring releases (0.17.12+) are the single source of truth for fixes; watch the ring releases and distribution package updates. Confirm the exact patched version your tooling expects.
- Microsoft VEX/CSAF expansions: Microsoft stated it will update CVE entries and attestations if it discovers other affected products; watch MSRC VEX feeds for product list changes.
- CVE trackers and RustSec entries: RustSec provides an advisory and is a reliable place to check whether the crate is patched and whether transitive dependencies are at risk; cross‑reference with NVD/other vendor advisories for severity and EPSS metrics.
Conclusion
Microsoft’s public advisory that “Azure Linux includes this open‑source library and is therefore potentially affected” should be read precisely — it is a product‑scoped inventory attestation that tells Azure Linux users to prioritize remediation. It does not mean Azure Linux is the only Microsoft product that could include ring. Any Microsoft‑distributed artifact that packages or ships Rust binaries dependent on ring — whether marketplace images, container images, SDK builds, or other artifacts — remains a plausible carrier until Microsoft inventories it and issues a VEX/CSAF attestation or until the artifact is verified and rebuilt with a fixed ring version. Security teams should treat Azure Linux as confirmed in‑scope, perform per‑artifact verification across their Microsoft‑supplied images and binaries, and use SBOM/Cargo checks and cargo‑audit/RustSec scans to identify and remediate exposed Rust artifacts.Appendix — Quick reference commands and checks
- Detect ring in a Rust project:
- cargo tree | grep ring
- Audit Rust dependencies:
- cargo install cargo-audit
- cargo audit --ignore RUSTSEC-IDs-if-you-really-need-to
- Check an image for ring:
- Extract container filesystem and search for Cargo.lock, compiled Rust binaries, or known dependency metadata.
- Use SBOM/image scanners to enumerate contents if available.
- Confirm patched ring version:
- Ensure Cargo.lock or packaged distro shows ring >= 0.17.12 (or the specific downstream patched package version your distro publishes).
Source: MSRC Security Update Guide - Microsoft Security Response Center