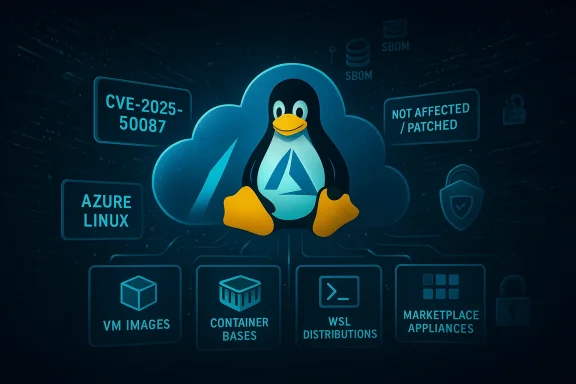
Microsoft’s MSRC attestation that “Azure Linux includes this open‑source library and is therefore potentially affected” is accurate — but it is not a categorical guarantee that only Azure Linux can contain the vulnerable MySQL component tracked as CVE‑2025‑50087. Azure Linux is the only Microsoft product Microsoft has publicly inventory‑attested so far for this specific CVE, which makes it the single confirmed Microsoft carrier at the time of the attestation. However, any Microsoft artifact that ships or embeds the same upstream MySQL server or client packages — including VM images, Marketplace appliances, container base layers, Windows Subsystem for Linux (WSL) distributions, or the tooling used inside managed services — could also carry the vulnerable code until it is explicitly inventoried and attested. In short: treat Azure Linux as confirmed in‑scope, and treat everything else as “potentially in scope” until you verify otherwise.
CVE‑2025‑50087 is a MySQL Server vulnerability disclosed in July 2025 as part of Oracle’s Critical Patch Update cycle. Public vendor matrices and vulnerability trackers describe the issue as an optimizer/server bug in MySQL that affects multiple modern release branches. The published affected upstream release ranges commonly cited are:
Microsoft’s Security Response Center (MSRC) published a short product attestation mapping the upstream component to Azure Linux, and also announced a phased rollout of machine‑readable CSAF/VEX attestations beginning in October 2025 to improve transparency about which Microsoft products include which upstream open‑source components.
CVE‑class supply‑chain issues are rarely binary: a single‑line vendor attestation is valuable, but it is only one piece of operational truth. Microsoft’s statement identifies a clear, immediate constituency — Azure Linux — and its move to publish machine‑readable VEX attestations materially improves transparency. That progress, however, does not replace rigorous artifact inventory, SBOM‑driven verification, and fast patching across the broad estate of VM images, containers, WSL distributions, and managed service tooling. Treat the MSRC attestation as a call to action: verify your artifacts, patch Azure Linux images promptly, and assume other Microsoft artifacts are potentially affected until proven otherwise.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CVE‑2025‑50087 is a MySQL Server vulnerability disclosed in July 2025 as part of Oracle’s Critical Patch Update cycle. Public vendor matrices and vulnerability trackers describe the issue as an optimizer/server bug in MySQL that affects multiple modern release branches. The published affected upstream release ranges commonly cited are:- MySQL 8.0.0 through 8.0.42 (inclusive)
- MySQL 8.4.0 through 8.4.5 (inclusive)
- MySQL 9.0.0 through 9.3.0 (inclusive)
Microsoft’s Security Response Center (MSRC) published a short product attestation mapping the upstream component to Azure Linux, and also announced a phased rollout of machine‑readable CSAF/VEX attestations beginning in October 2025 to improve transparency about which Microsoft products include which upstream open‑source components.
What the MSRC statement actually says — and what it does not
Microsoft’s one‑line mapping is a product‑level inventory attestation. Practically, that means:- It is an authoritative statement that Microsoft checked the Azure Linux distribution it publishes and found the upstream MySQL component mapped to the CVE in that product. Azure Linux is therefore a confirmed Microsoft product in‑scope for CVE‑2025‑50087.
- It is not an exclusivity statement. Microsoft did not say “no other Microsoft product contains this library.” The attestation reflects what Microsoft has checked and declared so far.
- MSRC’s broader program to publish CSAF/VEX attestations is phased; the company started with Azure Linux and has committed to updating VEX/CVE records if additional Microsoft products are found to ship the same component.
Why other Microsoft artifacts might be carriers
The vulnerable code lives upstream in MySQL server and client packages. Those binaries and packages are widely redistributed in many forms:- Linux distributions and their package repositories (Debian, Ubuntu, RHEL, SUSE, etc.)
- Cloud VM images and marketplace images (which are typically built from a distribution snapshot)
- Container base images and curated registry images
- Marketplace appliances and partner images published via vendor channels
- Windows Subsystem for Linux (WSL) distributions that use Linux userland packages
- Managed services and control‑plane tooling that might incorporate MySQL tools or libraries for backup/migration tasks
Technical snapshot of CVE‑2025‑50087 (concise, verifiable facts)
- Disclosure date (public): mid‑July 2025 as part of Oracle’s July CPU.
- Affected upstream releases (commonly cited): 8.0.0 → 8.0.42; 8.4.0 → 8.4.5; 9.0.0 → 9.3.0.
- Typical remediation target: upgrade to patched upstream point releases (for example, 8.0.43+) or apply vendor distribution patches.
- Attack vector and privileges: network reachable, but exploitation generally requires high database privileges (administrative or equivalent).
- Primary impact: integrity and/or availability depending on the variant and vendor assessment; many trackers characterize the risk as an availability/DoS or limited data integrity manipulation under constrained conditions.
- Exploit prevalence: at disclosure and in follow‑on months there were no broad, publicly verified RCE wormable exploits; the operational risk is concentrated where privileged accounts are exposed or where backup/migration automation runs with elevated rights.
Short, direct answer to the user’s question
- Is Azure Linux the only Microsoft product that includes this open‑source library and is therefore potentially affected by CVE‑2025‑50087?
- No — Azure Linux is the only Microsoft product Microsoft has publicly attested to include the vulnerable library so far. That makes Azure Linux the only confirmed Microsoft carrier. It is not proof that no other Microsoft product contains the library. Any Microsoft artifact that ships Linux userland packages (images, container layers, WSL distributions, Marketplace appliances, managed service tooling) should be considered potentially affected until you verify it through artifact‑level inspection or Microsoft VEX/CSAF attestations.
Practical, prioritized checklist for Microsoft customers (inventory → verify → remediate)
Follow this triage sequence to reliably determine exposure and remediate:- Inventory first — rapid discovery:
- Enumerate Microsoft‑published artifacts you run: Azure VM images, Marketplace appliances, container base images, WSL distributions, and managed service components.
- For each artifact, capture the OS distribution, package manager metadata, and any SBOMs you can access.
- Verify package versions — artifact‑level checks:
- On hosts (Debian/Ubuntu): dpkg -l | grep -E 'mysql|mariadb'
- On hosts (RHEL/CentOS/Fedora/Amazon Linux): rpm -qa | grep -E 'mysql|mariadb'
- Confirm mysqld or mysqldump versions directly: mysqld --version or mysqldump --version
- For container images: run a shell in a container or inspect image metadata; use static image scanners (Trivy, Clair, Grype) or extract the SBOM.
- If you have Microsoft VEX/CSAF ingestion in your toolchain, query the artifact IDs to see product-level attestations, and validate artifact IDs/timestamps against your deployed images.
- Prioritize remediation:
- Patch or rebuild images that run vulnerable MySQL server/client packages — prefer vendor distribution packages that incorporate the upstream fixes.
- If patching immediately is impossible, isolate or firewall database management planes, revoke exposed admin credentials, and temporarily disable automated backup/migration jobs that run mysqldump with elevated rights.
- Rebuild and redeploy container images after upgrading packages; gate CI/CD pipelines with image scanning and SBOM checks.
- Verify managed services and support channels:
- If you use Azure Database for MySQL or other Microsoft managed offerings, open a support ticket asking explicitly whether the managed control plane, backup tooling, or migration workflows use mysqld/mysqldump and confirm patch status and timelines.
- Automate long term:
- Ingest MSRC VEX/CSAF attestations as they appear, but do not treat a missing VEX entry as evidence of safety — treat VEX as an automation signal that must be corroborated with artifact scans and SBOM data.
Specific remediation steps (example, numbered)
- Identify hosts/images running vulnerable packages:
- Run package inventory commands across your estate and list all instances where package versions fall within the vulnerable ranges.
- Schedule and test vendor‑supplied patches in staging:
- Apply distribution security packages that map to upstream patched releases (for example, packages that correspond to MySQL 8.0.43+).
- Rebuild images and containers:
- Replace base images that include vulnerable MySQL packages and rebuild dependent images.
- Rotate credentials used by backups and automation:
- Assume any long‑lived admin credentials used by backup or migration scripts may have been exposed; rotate and tighten privileges.
- Harden access:
- Restrict network access to management ports, implement MFA for administrative access to backup tooling, and segment backup repositories.
- Monitor for anomalous use:
- Increase telemetry on mysqld/mysqldump invocations, large outbound transfers, and repeated mysqld crashes or restarts.
Detection and monitoring: what to watch for
- Repeated mysqld process crashes or thread‑pool errors in MySQL logs.
- Unexpected mysqldump invocations from CI runners, container hosts, or orchestration nodes.
- Large outbound data transfers immediately after a backup; spike in egress traffic from machines that run privileged backup/automation tasks.
- Sudden changes in replication or binary logs consistent with unauthorized DML (where vendor advisories suggest a possible limited integrity impact).
- Any evidence of administrative credential misuse across multi‑tenant or hosted control plane environments.
Critical analysis — strengths and limitations of Microsoft’s attestation approach
Strengths- Machine‑readable CSAF/VEX attestations are a meaningful operational improvement: they make vendor inventory data consumable by automation, reduce ambiguity, and accelerate customer decisioning.
- Publishing product‑level attestations for Azure Linux demonstrates a commitment to transparency and gives a clear remediation path for users of that distribution.
- Phased rollout means incomplete coverage: attesting one product does not mean all related artifacts are covered. Organizations that run a mix of Azure Marketplace images, custom images, WSL distributions, container images, and managed services still need to run their own artifact verification.
- VEX is a signal, not a substitute for artifact scanning: a “Not Affected” VEX entry may apply to a specific artifact ID; if your deployed image differs, you must still verify.
- Low numerical CVSS scores for client tools or certain server variants can lull teams into deprioritization. For CVE‑2025‑50087 and related MySQL fixes, the operational risk is concentrated where privilege exposure exists — backup systems, automation scripts, multi‑tenant platforms — and those deserve high priority even when numeric scores are modest.
- Publish per‑image SBOMs for Marketplace and common base images and keep them synchronized with image updates.
- Expand VEX coverage faster across image families (VM images, container images, WSL packs) and managed service internals.
- Provide explicit guidance about managed service internals (do you use mysqldump in the control plane?) so customers can assess exposure more accurately.
FAQ (concise answers for busy defenders)
- Q: Can I rely on Microsoft’s one‑line Azure Linux attestation to clear the rest of my Microsoft footprint?
- A: No. Use it as an authoritative indicator for Azure Linux only; verify other artifacts.
- Q: If I don’t run Azure Linux images, do I need to act?
- A: Yes — any Microsoft artifact that embeds MySQL server/client packages should be inventoried and scanned. Don’t assume safety by absence of a Microsoft attestation.
- Q: What is the immediate priority for patching?
- A: Prioritize images and hosts where MySQL runs with elevated privileges, and any automation/backups that execute mysqldump with admin rights.
- Q: Are there workarounds if I cannot patch immediately?
- A: Isolate hosts, restrict network management access, disable or reconfigure backup jobs that run mysqldump as an admin, rotate credentials, and increase monitoring.
Final recommendations — a defensible checklist you can apply now
- Treat Microsoft’s MSRC line as a high‑quality signal: Azure Linux = confirmed affected; prioritize patching for those images.
- Inventory all Microsoft artifacts you run that could contain Linux userland packages and scan them for vulnerable MySQL server/client package versions.
- Ingest MSRC VEX/CSAF attestations into automation but corroborate with artifact‑level scans and SBOM verification before acting.
- Patch vendor‑supplied packages or rebuild images to include the upstream fixes (e.g., MySQL 8.0.43+ and the equivalent patched 8.4/9.x releases).
- Harden backup and migration workflows: reduce privileges, rotate credentials, gate image builds with SBOM checks, and increase telemetry on dump activity and mysqld crashes.
- If you use Microsoft managed database services, open support channels and request explicit statements about whether managed control‑plane tooling uses vulnerable binaries and whether they have been patched.
CVE‑class supply‑chain issues are rarely binary: a single‑line vendor attestation is valuable, but it is only one piece of operational truth. Microsoft’s statement identifies a clear, immediate constituency — Azure Linux — and its move to publish machine‑readable VEX attestations materially improves transparency. That progress, however, does not replace rigorous artifact inventory, SBOM‑driven verification, and fast patching across the broad estate of VM images, containers, WSL distributions, and managed service tooling. Treat the MSRC attestation as a call to action: verify your artifacts, patch Azure Linux images promptly, and assume other Microsoft artifacts are potentially affected until proven otherwise.
Source: MSRC Security Update Guide - Microsoft Security Response Center