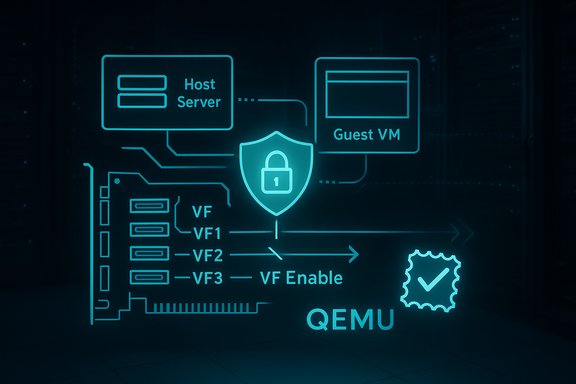
The QEMU SR-IOV implementation contains a subtle but meaningful bug: hw/pci/pcie_sriov.c in QEMU through 10.0.3 mishandles the VF Enable bit write mask, a logic error tracked as CVE-2025-54567 that can lead to incorrect registration/unregistration of virtual functions (VFs) and inconsistent SR-IOV state. This vulnerability is tied to a broader class of SR-IOV register-handling issues previously exposed by CVE-2024-26327, and it was addressed upstream with a targeted fix that fixes how configuration writes are consumed and how migration state is synchronized.
SR-IOV (Single Root I/O Virtualization) exposes multiple Virtual Functions (VFs) of a physical PCIe device to virtual machines. That hardware-level sharing depends on precise register semantics — which bits are writable, which writes are masked, and which writes should be ignored — because incorrect handling allows a guest to change hardware-visible state in ways the host expects to control. The CVE-2025-54567 issue stems from a write-mask handling mistake: pcie_sriov_config_write assumed values had already been masked and therefore could process the VF Enable bit even when the write mask should have prevented that change. That assumption permitted unexpected enabling or disabling of VFs under some write patterns. This bug was raised and fixed in July 2025 via an upstream patch that introduced a unified consume_config routine to read configuration registers correctly and synchronize internal state with the actual register values. The fix was backported or bundled into downstream vendor updates; major Linux distributions began shipping patched QEMU packages soon after the upstream change.
Longer answer:
CVE‑2025‑54567 is a reminder that virtualization subsystems — particularly SR‑IOV and device emulation — require rigorous, artifact-level inventory and rapid coordination between upstream projects, Linux distributions, and platform vendors. The combination of an upstream fix, rapid distro updates, and Microsoft’s move to machine‑readable VEX attestations reduces ambiguity and improves the speed at which operators can make evidence-based remediation decisions. The immediate operational path is clear: identify QEMU instances that present SR‑IOV to guests, patch to vendor-supplied fixed packages (or apply the upstream patch), validate VF behavior post‑patch, and, where a rapid patch is impossible, disable SR‑IOV until remediation is applied.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
SR-IOV (Single Root I/O Virtualization) exposes multiple Virtual Functions (VFs) of a physical PCIe device to virtual machines. That hardware-level sharing depends on precise register semantics — which bits are writable, which writes are masked, and which writes should be ignored — because incorrect handling allows a guest to change hardware-visible state in ways the host expects to control. The CVE-2025-54567 issue stems from a write-mask handling mistake: pcie_sriov_config_write assumed values had already been masked and therefore could process the VF Enable bit even when the write mask should have prevented that change. That assumption permitted unexpected enabling or disabling of VFs under some write patterns. This bug was raised and fixed in July 2025 via an upstream patch that introduced a unified consume_config routine to read configuration registers correctly and synchronize internal state with the actual register values. The fix was backported or bundled into downstream vendor updates; major Linux distributions began shipping patched QEMU packages soon after the upstream change. What CVE‑2025‑54567 actually is
The root cause, in plain terms
- The code handling PCIe SR‑IOV configuration writes wrongly treated its incoming write value as already masked, ignoring the hardware/guest-provided write mask.
- As a consequence, the VF Enable bit could be processed in situations where the write mask should have prevented it, leading to incorrect VF registration/unregistration and a mismatch between intended configuration and internal host state.
The practical implication
- A guest could, under constrained conditions, cause the hypervisor’s SR‑IOV state machine to behave inconsistently. That inconsistency can create confusion around which VFs are available and registered and — in worst cases — enable unexpected access paths or trigger denial-of-service-like conditions for VF resources. The vulnerability’s CVSS vector reflects a moderate severity with limited integrity impact but not complete confidentiality or availability breaks.
Relationship to CVE‑2024‑26327
- CVE-2024-26327 was a buffer-overflow class bug in the same hw/pci/pcie_sriov.c codepath (register_vfs handling), illustrating that this area of QEMU’s SR‑IOV implementation has been repeatedly error-prone. CVE‑2025‑54567 is a different bug class (incorrect write-mask consumption), but the two are related by component and attack surface. Administrators responsible for systems that expose SR‑IOV must therefore treat this family of fixes as a cohesive security hygiene requirement.
Where this vulnerability lives: which QEMU versions are affected
Upstream advisories and CVE records identify QEMU releases up to and including 10.0.3 as containing the flawed code path. The upstream patch was posted in July 2025 and was backported into vendor/stable branches by maintainers; downstream package upgrades for affected distributions followed the patch. Distribution security trackers (Debian, for example) mark affected package versions and list the updated packages that remedied the issue. Administrators should treat QEMU versions with upstream commit ranges that include the introduced commits (rooted in v10.0.0-rc0) as vulnerable until they install a vendor-supplied fixed package or the upstream patch.Microsoft’s public attestation and what it means
Microsoft’s VEX/CSAF approach
Microsoft has started publishing machine-readable attestations (CSAF/VEX) that state whether particular Microsoft products include specific open-source components and whether those included components are affected by a given CVE. This transparency program began its public VEX pilot for Azure Linux in October 2025; the aim is to provide precise, artifact-level answers that help customers reduce noisy false positives from supply-chain scanning.What MSRC’s VEX for CVE‑2025‑54567 says
Microsoft’s VEX/CSAF record for CVE‑2025‑54567 lists a product tree that includes both Azure Linux (Azure Linux 3.0 / “azl3 qemu 8.2.0-17”) and CBL Mariner 2.0 (cbl2 qemu 6.2.0-26) as items of interest. Critically, MSRC’s attestation declares the status for those artifacts: CBL Mariner’s qemu component is listed as a known affected product, while Azure Linux’s qemu component is explicitly flagged as not affected (component_not_present / known_not_affected) in that particular VEX document. In other words, Microsoft’s published data shows the company has identified CBL Mariner as carrying an affected QEMU component for this CVE while the specific Azure Linux artifact they referenced does not contain the vulnerable component. That answer is precise but limited: the VEX file is an inventory attestation for the artifacts Microsoft evaluated. A “not affected” mark there applies to the specific Azure Linux qemu artifact Microsoft listed, not to every conceivable Microsoft SKU or to every image a customer might be running. Microsoft’s VEX records also state they will update the CVE entries if additional Microsoft products are found to include the same upstream code. That means this is a continuously updated inventory process, not an immutable claim of exclusivity.So — is Azure Linux the only Microsoft product that includes the library?
Short answer: No.Longer answer:
- Microsoft’s published VEX/CSAF data shows more than one Microsoft product entry in the product tree for this CVE: Azure Linux and CBL Mariner are both present in the MSRC attestation. CBL Mariner’s qemu artifact is identified as known affected, while Azure Linux’s listed qemu artifact is identified as known not affected / component_not_present. That demonstrates Microsoft’s inventory includes multiple Microsoft artifacts related to QEMU and that the affected flag applies to CBL Mariner, not the specific Azure Linux qemu package Microsoft listed.
- Microsoft’s VEX approach is iterative and artifact-specific: a product-level attestation answers the question “which of our known build artifacts ship this upstream component?” It does not, on its own, prove that no other Microsoft product or internal image includes the vulnerable upstream file unless Microsoft has explicitly enumerated and attested every possible internal or derivative artifact. Microsoft has said they will update the records if additional products are discovered to carry the vulnerable component. That means absence of additional product entries in the VEX file should not be interpreted as a blanket guarantee about every Microsoft SKU.
- Practically, the MSRC VEX file is the authoritative public statement on Microsoft inventory to date. Based on the current VEX, Azure Linux is not the only Microsoft product related to QEMU in the listing, and CBL Mariner is explicitly listed as affected. For environments where Microsoft-supplied artifacts are used (for example, CBL Mariner-based appliances or Azure Linux images), the VEX file provides actionable, machine-readable guidance for prioritized responses.
Risk assessment for admins and cloud operators
- Systems exposing SR‑IOV devices to guests have a larger attack surface for this vulnerability because the buggy code path sits squarely in the SR‑IOV management code. Hypervisors that do not enable SR‑IOV, or hosts that never present SR‑IOV-capable devices to guests, have little to no practical exposure from this specific bug. However, environments that rely on SR‑IOV for NIC offload and performance (common in telco, HPC, NFV, and certain cloud instances) should treat this as material.
- The vulnerability is not a high-severity remote RCE by default: published scoring places it at a moderate level (CVSS ~4.2) reflecting an adjacent-network vector and higher complexity. Yet, the real-world impact is dependent on configuration details (whether the platform enables SR‑IOV, how VFs are assigned, and whether guest code can easily arrange the necessary writes). Attack feasibility is therefore environment-specific.
- Because this is a register-handling bug, migration, snapshot, and live-guest state paths were called out in the upstream analysis — inconsistent state after live migration can lead to unexpected behavior after a guest move. Environments that perform frequent migrations should prioritize review and updates.
Concrete, prioritized actions (for administrators and security teams)
- Inventory: Identify any hosts, images, and appliances that include QEMU. Use package tools to enumerate QEMU packages and versions:
- On Debian/Ubuntu: dpkg -l | grep -i qemu
- On RHEL/CentOS/OL: rpm -qa | grep -i qemu
- On SUSE: zypper se --installed-only qemu
- For custom appliances, check the build manifest or image manifest for qemu packages or upstream commits.
These steps identify candidate hosts for targeted remediation. - Confirm versions: Treat any QEMU package with a version or commit range that maps to upstream releases <= 10.0.3 as vulnerable unless the vendor’s package notes indicate the patch was backported. Consult your distribution vendor security tracker or the vendor-provided changelog for confirmation.
- Apply vendor updates: Install the vendor-provided fixed QEMU package. Most major distributions released patched packages or backports shortly after the upstream fix; use the distribution’s security channels to obtain the correct update for your release. If a vendor update is not yet available, consider applying the upstream patch or a vendor-provided backport.
- Short-term mitigation: If you cannot patch immediately, consider temporarily disabling SR‑IOV on affected hosts or avoid attaching SR‑IOV-capable devices to untrusted guests. That reduces exposure because the vulnerable code is exercised principally when SR‑IOV configuration writes occur. Note this is a functional mitigation that can impact performance and must be weighed against operational requirements.
- Verify vendor attestations: For Microsoft customers, ingest Microsoft’s CSAF/VEX attestations and map them to your estate. The MSRC VEX file for this CVE already shows which Microsoft artifacts were examined and their status; use that to prioritize patching of Microsoft-supplied images that are listed as affected (for example, CBL Mariner artifacts in the MSRC record). Keep watching MSRC for updates if your environment uses other Microsoft SKUs that might later be added.
- Post‑patch validation: After applying fixes, validate SR‑IOV behavior using benign test cases (bring up VFs, attach/detach to guests, perform migrations) and confirm VF counts and registration/unregistration behavior are consistent with hardware expectations. Keep migration logs and hypervisor hooks under observation for anomalies during the next maintenance window.
Cross‑vendor status and patches
- Upstream QEMU accepted and published the patch in July 2025; maintainers discussed and reviewed the change on the qemu-devel and qemu-stable lists. Vendors backported the fix to stable branches and released updated packages to their users.
- Distribution trackers (Debian, for one) list fixed package versions and show which releases required backports. Administrators should consult their distribution’s security advisory for the precise fixed package name and version to install in their environment. Debian’s security tracker and package changelogs list the relevant fixes and which package release contains them.
- For environments that source QEMU from project snapshots or custom builds, apply the upstream commit that implements the consume_config change (the patch was included in the stable trees and the commit text explicitly cites CVE-2025-54566 and CVE-2025-54567). If you vendor your own QEMU builds, rebasing onto the patched upstream tag is the correct development action.
Why Microsoft’s statement about Azure Linux matters — and its limits
Microsoft’s public message emphasizes two points: that Azure Linux receives continuous, proactive maintenance of open-source components and that Microsoft is publishing machine-readable VEX attestations so customers can quickly determine product-exposure. Both are helpful for customers who rely on Microsoft-supplied artifacts and for automated supply-chain scanners trying to resolve “is this CVE actionable for this product?” However, public VEX attestation is inherently a scoped inventory disclosure. The attestation is authoritative for the artifacts Microsoft has enumerated; it does not—by itself—prove completeness across every Microsoft binary and internal SKU unless Microsoft explicitly attests to that effect. MSRC has acknowledged this by committing to update CVE/VEX entries if additional products are identified as carriers of the upstream code. Customers should therefore use VEX files as a precise starting point for automated triage while retaining the standard due diligence of cross-checking package versions in their own environment.Detection and forensic cues
- Check hypervisor and QEMU logs for spurious VF registration or unregistration events, especially around guest writes to PCIe configuration space. The vulnerable code produced inconsistent state in some migration scenarios; anomalous VF count changes after migration are a red flag.
- For packagers: code review of the hw/pci/pcie_sriov.c diff and the upstream commit is the fastest way to verify whether your QEMU build contains the fix. For operators: rely on vendor package changelogs and CVE tracking; do not assume a package version number alone proves a fix unless the vendor changelog explicitly mentions this patch or CVE.
Final analysis — strengths, risks, and practical takeaway
- Strengths:
- The issue was responsibly reported, discussed on upstream lists, and fixed with a focused code change that improves correctness by consuming actual configuration values rather than relying on fragile special-case assumptions. That upstream transparency enabled downstream vendors to produce timely updates.
- Microsoft’s adoption of CSAF/VEX and its early VEX pilot for Azure Linux improves clarity for customers and reduces the workload of manual artifact mapping. The public manifestation of a VEX file for this CVE makes it easier to determine whether particular Microsoft artifacts are impacted.
- Risks:
- The root problem is in SR‑IOV register semantics, which are inherently sensitive to hardware and firmware variants; testing every combination across vendor NICs, BIOS/firmware, and hypervisor settings is difficult. That means subtle, environment-specific failures could remain until operators validate functional behavior post-patch.
- VEX attestations are only as complete as the inventories that produce them. Customers should not assume a lack of public attestation equals a lack of exposure — especially in large, heterogeneous estates with custom images. Microsoft’s VEX program reduces ambiguity but must be paired with estate-specific package auditing.
CVE‑2025‑54567 is a reminder that virtualization subsystems — particularly SR‑IOV and device emulation — require rigorous, artifact-level inventory and rapid coordination between upstream projects, Linux distributions, and platform vendors. The combination of an upstream fix, rapid distro updates, and Microsoft’s move to machine‑readable VEX attestations reduces ambiguity and improves the speed at which operators can make evidence-based remediation decisions. The immediate operational path is clear: identify QEMU instances that present SR‑IOV to guests, patch to vendor-supplied fixed packages (or apply the upstream patch), validate VF behavior post‑patch, and, where a rapid patch is impossible, disable SR‑IOV until remediation is applied.
Source: MSRC Security Update Guide - Microsoft Security Response Center