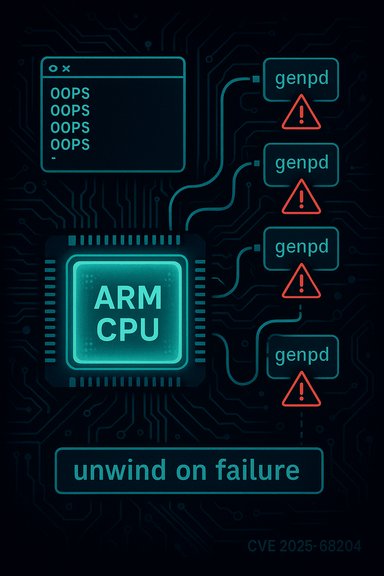
A recently assigned CVE, CVE-2025-68204, discloses a resource-handling bug in the Linux kernel’s ARM SCMI power-domain code that can leave generic power domains (genpds) allocated when provider registration fails — a leak that has been shown to eventually trigger a kernel panic during genpd debug initialization. This is a local kernel stability issue rather than a remote, network-exploitable hole, but it carries real risk for embedded ARM systems and distributions that ship affected kernel trees until the fix is pulled into stable kernels.
Background
What are genpd and SCMI, and why this matters
Generic power domains (genpd) are the kernel’s common abstraction for controlling power domains across SoCs. The System Control and Management Interface (SCMI) is a firmware/communication protocol used by many ARM platforms to expose power, performance, and sensor controls to the operating system. The ARM SCMI driver contains logic to register genpd providers for devices discovered via device-tree bindings. When that provider registration fails mid-probe, the kernel must fully unwind any partial initialization; failure to do so yields dangling or orphaned genpd structures that later subsystems may assume are valid. The specific failure chain reported for CVE-2025-68204 begins in the provider registration path around of_genpd_add_provider_onecell — the device-tree helper that creates and registers a onecell provider of genpds for a device. If that helper fails during probe, earlier-created domains were not being removed, producing a leak. The leak may remain dormant until genpd debug initialization code traverses the domain structures and dereferences invalid pointers, producing an OOPS and kernel panic. An example crash trace included in the advisory shows the failure surfacing in genpd_debug_add/genpd_debug_init during early kernel initialization on an ARM Juno development platform.Where this came from
The issue was identified and fixed upstream in kernel trees as part of a sequence of pmdomain/genpd cleanup and robustness fixes. Commit logs tied to the fix (message: “pmdomain: arm: scmi: Fix genpd leak on provider registration failure”) are present in kernel patch branches and mirrored repositories used by kernel integrators. That commit updates the ARM SCMI provider probe logic to explicitly unwind already-initialized domains if of_genpd_add_provider_onecell fails, ensuring resources are released before probe returns an error.Technical analysis
The bug: partial initialization and missing rollback
At probe time, device drivers commonly perform multi-step setup: allocate memory, create kernel objects, register sub-components, and then expose interfaces. Robust code ensures that a failure at any step triggers cleanup of prior steps. In this bug, the driver path that creates per-domain genpd objects succeeded for a set of domains, but a later call to of_genpd_add_provider_onecell returned an error. The expected pattern would be to iterate backwards over the already-created domains and call the appropriate destroy/unregister routine.Instead, the error path returned to the caller leaving those created genpd objects registered in an inconsistent or partially initialized state. Those orphaned objects later confuse genpd debug helpers and other parts of the genpd core that iterate domains and assume objects are valid. The kernel trace included with the advisory shows a paging fault within genpd debug code, which indicates dereferencing an invalid pointer — consistent with a partially initialized or corrupted genpd data structure.
Why the crash can be delayed and non-deterministic
Memory leaks and partially initialized objects in kernel drivers are often latent. The initial probe failure may be innocuous for a while, but later runtime paths — particularly diagnostic or debug initialization code that runs at late init time — will iterate lists and references that assume provider registration succeeded completely. When that traversal encounters inconsistent state, a NULL or invalid pointer dereference may occur, producing an OOPS that can crash the whole system. The timing depends on when those traversal or debug codepaths execute, hence the crash can appear later and produce baffling traces that point away from the original probe error.Scope of affected code
The vulnerability name highlights specific subsystems: pmdomain: arm: scmi. That ties it to the ARM SCMI provider implementation that integrates with the genpd subsystem. While the core issue is an error-handling omission (missing unwind), the practical effect is that any platform using the ARM SCMI provider code path with device-tree bindings that create genpds could be affected if that path encounters the particular probe failure scenario. Embedded SoCs, development boards, and vendor kernels that carry the affected commit range are the primary exposure surface.The upstream fix and commit details
What the patch does
Upstream kernel maintainers resolved the issue by adding error-path cleanup in the ARM SCMI provider probe: when of_genpd_add_provider_onecell signals failure, the probe now iterates over the previously created domains and removes/unregisters them before returning the error to the caller. This is a classical resource-management fix: ensure that any successful allocations are properly released on failure. The commit message explicitly notes the genpd leak and documents the crash mode (genpd_debug_add causing paging fault) as the motivating reason for the change.Where the fix landed
The change appears in pmdomain-related patch merges and stable tree updates; traces of the commit exist in kernel integration trees and vendor mirrors (for example, the android.git kernel/common history shows the commit message in a pmdomain merge tag). Distribution-level merges and vendor kernel updates will depend on their maintainers pulling the upstream stable fixes into their release branches. As of the advisory’s publication, many trackers list the CVE and reference the upstream commit, but vendor advisories and distro patches may lag until they verify and rebundle the fix.Impact assessment: who’s at risk and how severe is it?
Likely impact
- Denial-of-service / kernel panic: the immediate risk documented is a kernel crash (panic/OOPS) caused by invalid memory access in genpd debug code. That is a clear local DoS against the device running the affected kernel.
- Device classes affected: ARM SoCs and embedded boards using the SCMI driver and genpd device-tree bindings are the primary concern. The example crash trace included a vendor development board (ARM Juno), showing this class of hardware in the investigative trail.
- Remote exploitation: there is no indication this is remotely exploitable via network; the defect originates in device probe code and manifests as instability, not an obvious remote code execution vector. Most public vulnerability trackers list this as not remotely exploitable. However, as with all kernel bugs, local access could be combined with other issues to produce more impactful outcomes in complex attack chains.
Severity and scoring status
As of the first public disclosures for CVE-2025-68204, CVSS scoring and EPSS probability had not been universally published. Several vulnerability aggregators included the record with a description but without an assigned CVSS or exploit score at the time the advisory went live. That said, the practical severity for production systems depends on deployment context: kernel stability bugs causing panics are high-impact for appliances, embedded devices, and systems requiring high availability. Administrators should treat this as a high-priority fix for affected ARM systems.Unverifiable or uncertain points
- Public advisories contain the upstream commit message and crash trace, but distribution-level exposure (which kernel package versions in Debian/Red Hat/Ubuntu/others include the vulnerable commit) is variable and must be checked against each vendor’s security tracker. At the time of writing, some scanners (Nessus plugin listings) flagged the issue but listed vendor patches as “not yet available.” This distribution mapping is time-sensitive and should be verified against vendor advisories for Debian, Red Hat, SUSE, Ubuntu, and embedded vendors.
Recommended actions for administrators, vendors, and integrators
- Identify whether your environment uses affected ARM SCMI provider code paths.
- Check kernel configuration and dmesg logs for arm_scmi or scmi-power-domain driver entries, and review device-tree usage of genpd providers.
- Update the kernel to a release that includes the upstream fix.
- Apply vendor-supplied patches or upgrade to the stable kernel version that pulls the pmdomain/genpd fix. If using rolling or vendor kernels, track your distribution’s security tracker for an official package patch.
- If an immediate kernel upgrade is not possible, mitigate risk by:
- Limiting access to local consoles and well-known local attack vectors (this is a local bug; reducing local untrusted access lowers exploitation likelihood).
- Avoiding hardware configurations or device-trees that force the problematic probe path — for integrators this may mean deferring SCMI genpd registration until a validated firmware path is in place. (This is platform-specific and may not be achievable on all devices.
- For embedded product vendors: test error paths in probe/initialization code.
- Ensure probe-time failures are exercised in CI to avoid latent resource leaks; add targeted regression tests for of_genpd_add_provider_onecell failure paths.
- Monitor vendor security trackers and subscribe to kernel-stable updates.
- Because distro-level timelines vary, track Debian, Red Hat, Ubuntu, and your embedded vendor advisories for coordinated patches. Security scanners and trackers have already indexed CVE-2025-68204, but vendor announcements will provide actionable package updates.
Practical guidance for kernel developers and maintainers
- Treat error-path cleanup as first-class code: any allocation or registration must have a corresponding cleanup path documented and covered by tests.
- Add unit or integration tests that intentionally fail each probe sub-step (mocking the failing calls) to validate the unwind paths. The genpd and pmdomain subsystems are subtle and historically brittle at the initialization/error boundaries.
- When merging platform support, prefer explicit and short-lived resource ownership during probe; avoid registering objects with global lists before all required initialization completes.
- Use static/dynamic analysis to find unbalanced alloc/register patterns in complex subsystems such as genpd; these are common sources of latent kernel panics.
Broader context: why small resource leaks matter in kernel space
Resource leaks in the kernel are not merely a matter of growing memory use. Kernel objects often own reference counts, cross-referenced lists, and callback pointers used by disparate subsystems. A partially-initialized kernel object can break invariants relied on by debugging, initialization, or runtime code, which in turn can cause early boot panics or intermittent crashes under load. Embedded and resource-constrained devices are especially vulnerable: a single leaked structure in a low-memory environment can cascade into unrecoverable kernel faults. The CVE-2025-68204 case is a textbook example — a small oversight in error handling that leads to a critical early-boot crash scenario on ARM platforms.How this affects different audiences
- Enterprise Linux users running ARM instances: If you run ARM-based virtual machines or bare-metal servers using kernels in the affected upstream range, prioritize kernel updates from your vendor. Do not assume that a distribution’s kernel is unaffected — verify package changelogs.
- Embedded and IoT vendors: This class is the most exposed. SCMI is common on modern SoCs, and vendor kernels often lag upstream. Integrators should audit platform firmware and kernel stacks, and coordinate over-the-air (OTA) patch plans for deployed devices.
- Kernel developers: Add regression tests for probe-time failure paths and review other subsystems for similar unwind omissions, especially code that interacts with genpd and PM domains.
- Security teams: Update asset inventories to flag ARM devices with SCMI/genpd-enabled kernels, and plan patch windows that consider device availability and embedded vendor timelines.
Final assessment and takeaways
CVE-2025-68204 is a reliability- and availability-impacting kernel bug caused by incomplete error handling in the ARM SCMI genpd provider registration path. It is not a flashy remote RCE, but it is a significant local kernel stability issue that can cause system panics on affected ARM hardware. The upstream fix is straightforward — add proper unwind logic on provider registration failure — but the practical challenge is ensuring that the fix reaches distribution and vendor kernels deployed across a diverse ARM ecosystem. Administrators and embedded vendors should treat this as high priority: audit affected kernels, apply vendor-staged patches or upstream kernel updates, and harden testing and CI against probe-time failure regressions.If there is any uncertainty about whether a given binary package in your environment contains the vulnerable code, compare the kernel tree/commit history shipped by your vendor against the upstream commits mentioned in kernel-stable merges and vendor mirrors; vendor security advisories and kernel-stable release notes will ultimately be the authoritative rollout vehicle for the fix. Conclusion: CVE-2025-68204 is a clear reminder that robust error-path handling is essential in kernel subsystems. The fix is straightforward and already present upstream; the critical work now is for maintainers, distributors, and integrators to propagate the patch into production kernels and for administrators to update affected systems promptly.
Source: MSRC Security Update Guide - Microsoft Security Response Center