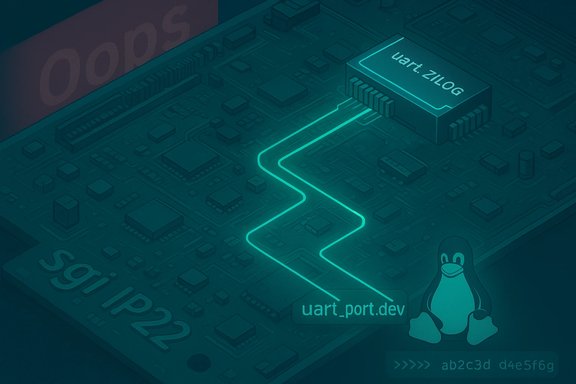
A recently assigned CVE identifier, CVE-2025-68311, documents a Linux kernel issue in the tty serial stack involving the ip22zilog driver that can trigger a kernel oops when the driver does not populate the uart_port.dev field after internal serial core changes. The root cause was introduced by a prior commit that began managing serial controllers for runtime power management, and the fix converts ip22zilog to use a platform device during probing and sets up the serial device in the SGI ip22 platform code. This update affects specific legacy MIPS/SGI platform support and has been recorded in multiple vulnerability trackers and distribution advisories; distributors have begun mapping affected kernel packages and introducing fixes in newer kernel trees.
The Linux kernel's serial subsystem historically contains a variety of architecture- and platform-specific drivers that present TTY interfaces via low-level UART drivers. One such driver, ip22zilog, supports Zilog-based UARTs found in SGI IP22-class MIPS systems. In late 2025, kernel maintainers identified that a change in serial core behavior — specifically, a commit that started actively managing serial controllers to enable runtime power management — created a new requirement: serial drivers must provide a valid device pointer in
Immediate actions:
In short, CVE-2025-68311 underscores the need for diligent cross-platform testing when kernel core components change behavior and the importance of rapid distribution-level remedial action for platform-specific drivers. Systems that match the affected hardware profile should receive updated kernels or implement the recommended mitigations without delay to prevent stability incidents.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
The Linux kernel's serial subsystem historically contains a variety of architecture- and platform-specific drivers that present TTY interfaces via low-level UART drivers. One such driver, ip22zilog, supports Zilog-based UARTs found in SGI IP22-class MIPS systems. In late 2025, kernel maintainers identified that a change in serial core behavior — specifically, a commit that started actively managing serial controllers to enable runtime power management — created a new requirement: serial drivers must provide a valid device pointer in struct uart_port.dev. When the ip22zilog driver failed to supply that pointer, code paths in the core could dereference a NULL or invalid pointer, producing a kernel oops (crash). The offending transition ties into the serial core’s move toward proper runtime PM handling. The commit in question, summarized as “serial: core: Start managing serial controllers to enable runtime PM,” changed expectations about what driver authors must initialize before the core performs controller management. When those expectations are not met, the kernel behavior is unstable and can result in an oops — a kernel-level fault that typically terminates the running kernel or leaves the system in an unusable state. Multiple vulnerability databases have logged the issue with a consistent description and references to upstream kernel commits and patch series that remediate the problem. Distribution security trackers (Debian, Ubuntu) and open vulnerability databases (OSV, NVD/mitigation records) have captured the CVE entry and are tracking affected package versions and the kernel commits that contain the fix. What changed in the kernel and why it matters
The serial core requirement
The serial core's runtime power management changes meant that a device context (thedevice pointer inside struct uart_port) must be available so that controller-level power management and driver model operations can be performed safely. Without that pointer, higher-level serial controller management can perform operations against a non-existent device, triggering kernel faults. This represents a classic regression-induced stability problem: a benign refactoring or new feature in the core imposes stricter initialization ordering on drivers. The ip22zilog driver’s role
The ip22zilog driver is a platform-specific driver mapping Zilog UARTs on SGI IP22 systems. The fix implemented for ip22zilog follows a pragmatic approach: convert the driver to a platform driver and ensure that the platform device representing the UART gets created and assigned during the SGI IP22 platform probe sequence. This change ensures theuart_port.dev field is populated prior to serial core controller management. The patch series adds platform device setup code in arch/mips/sgi-ip22/ip22-platform.c and modifies drivers/tty/serial/ip22zilog.c accordingly. Technical takeaways
- The underlying bug is not a remote code execution vulnerability; it is a stability/denial-of-service issue caused by kernel oopses when drivers fail to meet new initialization requirements.
- The problem is introduced by changes in kernel internals (serial core) that tighten driver expectations — a common source of regressions when core infrastructure gains new responsibilities like runtime PM.
- The fix is driver-level and platform-level: convert the driver model so
uart_port.devis valid and perform platform device setup earlier in the probe. The authoritative patch is already circulated and queued in kernel trees.
Scope and affected systems
Which kernels and distributions are affected
Upstream vulnerability records and distribution trackers list affected kernel versions and the commits that contain the fix. Distribution tracking summaries show that several packaged kernels used in mainstream distributions were vulnerable until the kernels received the upstream fixes or were rebuilt with the corrected trees.- Debian’s tracker lists several package versions in Bullseye, Bookworm, and Triscky trees as vulnerable, with fixes appearing in unstable and later kernel trees (fixed version entries reference the 6.17/6.18 series commits).
- Ubuntu’s advisory lists the issue with a medium priority for its packaged kernels and flags which releases include the affected packaging.
Real-world impact: who should care
- Owners/operators of legacy SGI MIPS platforms (IP22-based machines) and any environment where the ip22zilog driver gets compiled into the running kernel are the primary audience. On typical x86_64 servers, this driver is irrelevant; the vulnerability chiefly affects specific architecture/platform combinations.
- Embedded, hobbyist, or archival deployments that boot MIPS SGI images with newer kernel trees (which include the runtime PM serial changes) may observe boot-time or runtime oopses. Systems that never load or use the ip22zilog driver are unaffected in practice.
Severity and exploitability — objective assessment
Different sources assign different severity scores or leave scoring to NVD. At the time of reporting:- The NVD record for CVE-2025-68311 was posted but awaiting enrichment and a formal NVD CVSS scoring. That means NVD had not published a definitive CVSS score at the time tracking pages were updated.
- Independent scanners and commercial vendors (Nessus/Tenable) have assigned their own severity interpretations and CVSS vectors based on the nature of the impact (kernel oops/denial-of-service), producing high CVSSv3-style scores in some instances — these reflect an assessment of potential confidentiality/integrity/availability impact for local attackers or untrusted local users on affected systems. Those vendor assessments are useful for prioritization but may differ from NVD’s eventual rating.
- Open vulnerability indexes (OpenCVE, OSV) and aggregated feeds report low EPSS and list the nature of the problem as an oops rather than a remote code-execution exploit. That consensus suggests the practical exploitation risk to typical, network-facing systems is low.
- Treat the issue as a stability and local-denial-of-service risk for systems where the ip22zilog driver is present.
- Treat the issue as low remote risk for the vast majority of Linux installations; typical cloud, desktop, and server deployments on x86_64 do not include the affected MIPS-specific driver.
The patch: what maintainers changed
The publicly posted patch series and mailing-list submission clarifies the exact changes:- Convert ip22zilog from its current probing model to a platform driver model so a platform device representing the UART exists before the serial core performs controller management. This change ensures
uart_port.devis set. - Add platform-device creation and registration in the SGI IP22 platform probe code (
arch/mips/sgi-ip22/ip22-platform.c) to supply the required device context early in boot/probe sequences. - Modify
drivers/tty/serial/ip22zilog.cto operate as a platform driver and remove or adjust code paths that assumed a different probe model. The net effect is to comply with the serial core’s new requirement for runtime PM.
Risk analysis and mitigation guidance
Short-term mitigation (if you cannot update immediately)
- If you run an affected kernel on SGI IP22 hardware and see oopses or instability:
- Boot with an earlier kernel that predates the serial core change (if that’s feasible and supported by other hardware).
- Alternatively, rebuild the kernel without the ip22zilog driver enabled (remove the driver from the build/configuration) to avoid the problematic probe path. This is a blunt mitigation that trades serial device support for stability.
- For administrators using distribution kernels:
- Check your distribution’s security tracker or package changelog for the presence of fixes in updated kernel packages. Distros like Debian and Ubuntu map the upstream fixes to specific package revisions and provide upgrade guidance.
- If the driver is built as a module and not loaded, confirm it remains unloaded on vulnerable systems. Unloaded code generally cannot be triggered. Use
lsmodanddmesglogs to verify. This is practical for systems where kernel rebuilds are costly.
Recommended remediation steps (best practice)
- Upgrade to a kernel that contains the upstream patches that convert ip22zilog to a platform driver and add the platform device setup. Vendors and distribution package maintainers have begun shipping kernels that include the fix; apply distribution-supplied kernel updates as soon as they are available.
- If running custom kernels or embedded images:
- Pull the upstream commits referenced in vulnerability trackers (or rebase onto a fixed stable kernel release) and rebuild. The kernel commit identifiers cited by trackers and fix branches are the authoritative references for this change.
- For environments relying on legacy SGI MIPS hardware:
- Validate serial functionality after the update in a test environment before rolling changes into production. The patch alters driver binding and platform device registration — test scripts and serial-based console workflows may require verification.
Monitoring and detection
- Watch dmesg and kernel logs for serial-related oopses or error messages after kernel updates or hardware changes. The oops conditions that prompted the vulnerability assignment are usually evident in kernel console logs during probe or runtime controller management.
- Use distribution advisory feeds and vulnerability trackers to receive notifications for updated kernel packages that include the fix. Many package managers and vulnerability scanners (Nessus, Tenable) already flag the issue in their plugin sets.
Why this matters beyond legacy hardware
This CVE is a textbook example of modern kernel maintenance trade-offs and how infrastructure improvements can create driver model regressions:- As the kernel core acquires new responsibilities (like runtime PM for serial controllers), driver authors must meet new initialization contracts. Failure to do so can convert benign drivers into crash triggers. The lesson is that core API and behavioral changes require careful driver tree-wide audits.
- For system integrators and distribution maintainers, the CVE highlights the importance of early integration testing across architecture-specific code paths. Changes verified on x86_64 may still regress MIPS or other niche architectures if those platforms are not in the CI loop.
- For security and operations teams, the CVE illustrates the difference between code execution vulnerabilities and stability/DoS vulnerabilities — both matter, but they require different triage and remediation priorities. This CVE is in the latter category for most users, but it commands urgency for affected environments because an oops can render a critical system unusable.
How maintainers and packagers handled the fix
The patch was submitted to maintainers and discussed on architecture and serial driver mailing lists; the approach taken was to retrofit the driver to provide the necessary platform device registration so the serial core can rely on a validuart_port.dev. Distribution maintainers have tracked the upstream commits and prepared package rebuilds or kernel updates to include the corrected driver. Security trackers have been populated with vulnerability entries and mappings to distribution package versions that are vulnerable or fixed. Commercial scanners and vulnerability management vendors have also added detection rules and Nessus/Tenable plugins to flag unpatched kernels. These vendor tools sometimes apply their own CVSS assessments, which can differ from NVD’s later assignment; use vendor scores for operational prioritization but rely on upstream fixes for remediation. Final assessment and practical advice
CVE-2025-68311 is a targeted Linux kernel stability issue caused by a mismatch between serial core expectations and a platform-specific serial driver initialization path. For most modern x86_64 Linux installations, the issue is largely irrelevant because the ip22zilog driver is architecture-specific to SGI IP22 MIPS platforms. For the small population of users and organizations that operate SGI IP22-class hardware or compile kernel images for MIPS targets, the issue can cause kernel oopses and should be treated as a high-priority stability fix.Immediate actions:
- Operators of affected systems should prioritize kernel updates provided by their distribution or rebuild kernels that include the upstream fix.
- If updates are not immediately possible, temporarily disabling the ip22zilog driver (remove module or kernel configuration) is a practical mitigation while you plan for a kernel rebuild and test verification.
- Monitor vendor advisories, distribution trackers, and kernel mailing lists for any follow-up patches or rollups that may further refine the fix or expand it to other platform drivers.
In short, CVE-2025-68311 underscores the need for diligent cross-platform testing when kernel core components change behavior and the importance of rapid distribution-level remedial action for platform-specific drivers. Systems that match the affected hardware profile should receive updated kernels or implement the recommended mitigations without delay to prevent stability incidents.
Source: MSRC Security Update Guide - Microsoft Security Response Center