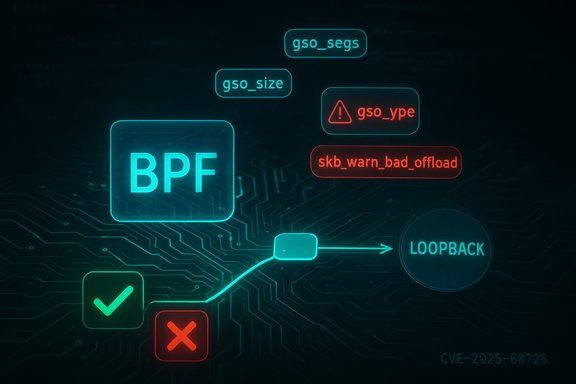
A recently assigned CVE has drawn attention to a subtle but important correctness gap between BPF test infrastructure and the Linux Generic Segmentation Offload (GSO) machinery: CVE-2025-68725 — described as “bpf: Do not let BPF test infra emit invalid GSO types to stack” — fixes a case where a fuzzer-driven BPF program could cause malformed GSO metadata to reach the kernel GSO code and trigger offload warnings and defensive feature masking. The defect is local in scope and primarily an availability problem: malformed GSO state leads the kernel to disable hardware/software offload for the packet and emit skb_warn_bad_offload diagnostics, with potential for dropped packets or test harness instability. The fix — committed into upstream stable trees and being packaged by distributions — prevents the test infra path (bpf_clone_redirect from pushing packets that lack a valid gso_type into the GSO engine. This article explains what went wrong, why it matters for kernel and networking teams, how vendors and distributions are handling the patch, and what administrators, developers, and CI maintainers should do next to mitigate operational risk and validate remediation.
BPF (Berkeley Packet Filter) has evolved far beyond simple packet filtering. Modern eBPF programs are used for tracing, networking (CNIs, XDP), and in-kernel test harnesses. Those programs interact with kernel packet structures (struct sk_buff, or skb) and sometimes redirect or clone packets between devices. The Linux GSO stack performs packet segmentation for large frames and cooperates with device offload features; it relies on several skb metadata fields — notably gso_segs, gso_size and gso_type — to decide whether and how to segment or offload packets.
The root of CVE-2025-68725 is a mismatch in how a test-path conversion populated skb GSO fields: convert___skb_to_skb set gso_segs and gso_size but left gso_type unset. When that malformed skb was injected into the loopback device via bpf_clone_redirect (an eBPF helper used by kernel test infra), later checks in netif_skb_features -> gso_features_check saw an invalid or missing gso_type, called skb_warn_bad_offload, and disabled GSO-related features for those packets. The maintainers decided to reject such malformed skbs at the producer side (bpf_clone_redirect rather than add deeper fast-path checks in the general GSO path. Why this matters in practice:
This CVE arises because the conversion path used by BPF test infra populated gso_segs and gso_size but did not set gso_type, producing an internally inconsistent skb. The result is a legitimate warning and a defensive masking off of offload features.
Key cross-checks:
Priority checklist (short-term):
Possible trade-offs to watch for:
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
BPF (Berkeley Packet Filter) has evolved far beyond simple packet filtering. Modern eBPF programs are used for tracing, networking (CNIs, XDP), and in-kernel test harnesses. Those programs interact with kernel packet structures (struct sk_buff, or skb) and sometimes redirect or clone packets between devices. The Linux GSO stack performs packet segmentation for large frames and cooperates with device offload features; it relies on several skb metadata fields — notably gso_segs, gso_size and gso_type — to decide whether and how to segment or offload packets.The root of CVE-2025-68725 is a mismatch in how a test-path conversion populated skb GSO fields: convert___skb_to_skb set gso_segs and gso_size but left gso_type unset. When that malformed skb was injected into the loopback device via bpf_clone_redirect (an eBPF helper used by kernel test infra), later checks in netif_skb_features -> gso_features_check saw an invalid or missing gso_type, called skb_warn_bad_offload, and disabled GSO-related features for those packets. The maintainers decided to reject such malformed skbs at the producer side (bpf_clone_redirect rather than add deeper fast-path checks in the general GSO path. Why this matters in practice:
- The immediate symptom is a kernel warning (skb_warn_bad_offload and disabled offload features for the affected packets, which can reduce throughput or cause packet drops under certain test workloads.
- The attack/exposure model is local — an unprivileged fuzzer or a BPF program that can be loaded on the host (or by an attacker who has the ability to load BPF programs) can trigger the condition.
- The fix is a correctness/robustness change to the kernel networking path and is being handled via upstream stable commits and distribution backports.
Technical deep dive
What is GSO and why does gso_type matter?
Generic Segmentation Offload (GSO) is a kernel mechanism that lets the networking stack hand large logical packets to lower layers which will segment them (or let the NIC do it), improving throughput by avoiding per-segment processing in the software path. GSO logic expects three related skb fields to be consistent:- gso_segs — number of segments the skb represents,
- gso_size — the size of each segment,
- gso_type — a bitmask describing the type of segmentation (TCPv4, TCPv6, GRE, FCOE, partial features, etc..
This CVE arises because the conversion path used by BPF test infra populated gso_segs and gso_size but did not set gso_type, producing an internally inconsistent skb. The result is a legitimate warning and a defensive masking off of offload features.
The specific path: BPF test infra → bpf_clone_redirect → loopback
The test harness scenario that exposed the bug was:- A BPF program (used in kernel selftests or generated by fuzzers such as syzbot) constructs or manipulates an skb and uses bpf_clone_redirect to push it to the loopback device.
- convert___skb_to_skb, a conversion helper used in this flow, set gso_segs and gso_size but left gso_type unset.
- Later, netif_skb_features calls into gso_features_check, which validates gso_type versus expected protocol and device capabilities.
- Seeing a missing/incorrect gso_type, gso_features_check triggers skb_warn_bad_offload, and the kernel disables GSO offload flags (feature masking via NETIF_F_GSO_MASK).
- The net result: offload features are rightfully disabled for the malformed skb, but the situation revealed a correctness hole — a producer-side path that can create malformed GSO metadata and push it into the stack.
Why the upstream change rejects the packet at bpf_clone_redirect
There are two general approaches to this class of problem:- Make the GSO check tolerant: mark gso_type “dodgy” (SKB_GSO_DODGY) and continue, or
- Block producers that are the only known source of such malformed skbs (in this case BPF test infra’s bpf_clone_redirect.
Scope and risk assessment
- Severity: Vendors and public trackers rate the issue moderate; many list a CVSSv3 base score around 5.5 due to the local vector and availability impact rather than data disclosure or code execution. The practical impact is packet drops and reduced throughput for corner-case test workloads rather than a clear remote RCE.
- Attack vector: Local. The attacker (or fuzzer) must be able to load or cause the kernel to run the specific BPF program that can manipulate skb fields and call bpf_clone_redirect.
- Privileges required: Low privileges may suffice if the system allows unprivileged BPF program loading (kernel.unprivileged_bpf_disabled config, CAP_BPF/CAP_SYS_ADMIN gating vary across distros). Many hardened systems disable unprivileged bpf by default; multi-tenant developer systems or CI runners may be exposed.
- Exploitability: Low for remote attack; medium operational impact for systems that run untrusted BPF programs or fuzzers. There is no public evidence of this being used to escalate privileges or perform arbitrary code execution at the time of disclosure. The real-world risk is service disruption or noisy kernel diagnostics in CI systems, developer VMs, or networking test rigs.
Where the fix landed and vendor status
Upstream kernel commits that reject malformed GSO-producing skbs in the bpf_clone_redirect path were merged into stable trees. Several public vulnerability trackers and vendor security pages have already ingested the CVE record and list distribution-specific advisories or “pending fixes” as vendors package the backport.Key cross-checks:
- The NVD entry documents the vulnerability description and rationale.
- Distribution trackers (SUSE, Amazon Linux ALAS, Debian/Ubuntu trackers) and vulnerability aggregators have added entries for CVE-2025-68725, typically classifying the issue as medium and indicating backports are being prepared or are pending. Administrators should expect fixes to appear in vendor kernel package updates over the coming maintenance cycles.
- Several public CVE aggregators and vulnerability databases also list kernel.org commit references (stable commit SHAs) that correspond to the fix; vendor advisories normally map those upstream commits to packaged kernel versions. When a vendor patch appears, its changelog should reference CVE-2025-68725 or cite the upstream commit.
Detection, hunting, and verification
Operational teams and security engineers should look for the following signals to detect past or attempted triggers of the condition:- Kernel logs containing the diagnostic string skb_warn_bad_offload or backtraces that include netif_skb_features and gso_features_check. These messages are the canonical symptom reported by the fuzzer-driven reproduction. Search via dmesg, journalctl -k, or central log aggregation.
- Regressions in throughput or sudden packet drops on hosts that run BPF workloads, test harnesses, or fuzzers. The issue manifests as disabled offload features for affected packets — under load that can reduce throughput.
- BPF program load events in CI logs or process activity windows that match the times of any observed kernel warnings. Correlate BPF program installs or selftest runs with kernel oops/warning events.
- For fleets: map which hosts allow unprivileged BPF loads (proc/sys/kernel/unprivileged_bpf_disabled) and prioritize those for log search and patching.
- Confirm kernel package changelog mentions CVE-2025-68725 or cites the upstream stable commit. Many vendors include CVE references in the package changelog; that is the primary non-invasive verification.
- Re-run representative BPF selftests or the workloads that previously triggered the warning and confirm the absence of skb_warn_bad_offload traces.
- Monitor for any unexpected packet drop counters or network-related regressions after the update in a pilot ring before broad rollout.
Mitigation and recommended immediate actions
Patching the kernel to a vendor-provided package that includes the upstream fix is the definitive remediation. Because this is a kernel-level change, the typical remediation workflow requires package update and a reboot (or live-patching if supported by your environment and vendor):Priority checklist (short-term):
- 1. Inventory: Identify hosts that run BPF-enabled kernels and which allow unprivileged BPF loading. Use uname -r and /proc/sys/kernel/unprivileged_bpf_disabled to map exposure.
- 2. Acquire vendor updates: Monitor your distribution’s security tracker for patches that reference CVE-2025-68725 and install them in a staged manner.
- 3. Pilot: Apply patches to a small, representative pilot group that runs typical BPF workloads or tests.
- 4. Deploy: Roll out the kernel update across production hosts that are at risk.
- 5. Verify: Confirm the absence of previous skb_warn_bad_offload traces and validate networking behavior.
- Disable unprivileged BPF on multi-tenant or sensitive hosts: set kernel.unprivileged_bpf_disabled = 1 (persist via sysctl configuration). This prevents unprivileged users from loading BPF programs.
- Restrict CAP_BPF / CAP_SYS_ADMIN capability assignments so only trusted processes, users, or services can load BPF programs.
- Limit or quarantine fuzzing/test harness runners and CI resources that execute untrusted BPF code on shared hosts.
- If a host is a test box used by developers for building and running selftests with BPF, consider isolating those workloads (dedicated VM/container) to reduce blast radius.
Developer and kernel maintainer guidance
For kernel and BPF developers the incident highlights two durable lessons:- Producer-side correctness is preferable to complex fast-path checks. The maintainers’ decision to reject malformed skbs at bpf_clone_redirect keeps the GSO fast-path simpler and avoids recurring runtime cost for a corner-case primarily exhibited by test harnesses or fuzzers. That trade-off is appropriate when the set of producers that can emit malformed skbs is narrowly scoped.
- Selftest and fuzz harnesses must mimic production contract semantics. Test infra that constructs packets must ensure internal kernel expectations (headers, offsets, and metadata like gso_type) are respected. Fuzzers that generate inconsistent metadata are excellent for finding issues, but harness conversions that create inconsistent state should be hardened so the kernel doesn’t receive malformed packets in product paths.
- Map upstream stable commits to package versions and publish clear advisories describing affected versions and the remediation package.
- If you backport fixes, ensure changelogs explicitly reference CVE IDs to make validation straightforward for operators.
Potential for regressions and trade-offs
The fix is narrowly scoped and defensive: it rejects malformed GSO-producing skbs emitted by the BPF test path rather than expanding the GSO code to accept dodgy metadata. That reduces the surface for regressions in the performance-critical GSO path.Possible trade-offs to watch for:
- Test suites or userland tooling that intentionally relied on relaxed behavior (unlikely) will see BPF-driven pushes to loopback rejected. Affected test harnesses should be updated to construct fully formed skbs (with gso_type set) or avoid using bpf_clone_redirect in this manner.
- Edge-case hardware drivers that rely on subtle behavior in test harnesses are unlikely to be impacted, but operators should validate kernel upgrade in a pilot ring for workloads that exercise kernel BPF redirection heavily.
Actionable checklist (for sysadmins and SREs)
- Inventory hosts: identify where BPF is used and whether unprivileged BPF loading is allowed.
- Watch vendor advisories: look for kernel package updates referencing CVE-2025-68725 or the upstream commit.
- Stage patching: apply updates to a pilot group and run representative BPF workloads and selftests.
- Harden policy: until patched, disable unprivileged_bpf and restrict CAP_BPF/CAP_SYS_ADMIN to trusted contexts.
- Monitor: alert on kernel logs containing skb_warn_bad_offload, netif_skb_features, or gso_features_check traces.
- Validate: after patching, re-run reproducer tests to confirm absence of the warning, and confirm no unexpected network regressions under representative traffic.
Conclusion
CVE-2025-68725 is a practical example of how test infrastructure can unintentionally trigger correctness checks in a high-performance kernel subsystem. The vulnerability is not a remote RCE; rather, it exposed a gap where BPF test paths could emit skbs with inconsistent GSO metadata, prompting defensive warnings and feature masking deep in the networking stack. Upstream maintainers have chosen a conservative fix — reject malformed skbs at the BPF test-path helper — and distributions are packaging backports. Operators should prioritize patching hosts that accept untrusted BPF programs, harden BPF loading policy for multi-tenant systems, and validate kernel updates in pilot rings to catch any unforeseen regressions. The incident is a reminder that kernel test harnesses and fuzzers are powerful tools for uncovering latent correctness problems, and that the production-grade remedy is disciplined, minimal, and designed to preserve fast-path performance while restoring semantic correctness.Source: MSRC Security Update Guide - Microsoft Security Response Center