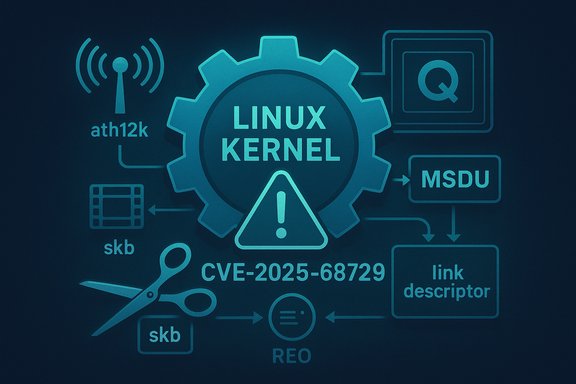
A Linux kernel vulnerability tracked as CVE-2025-68729 has been published: a logic error in the ath12k Wi‑Fi driver’s RX error path that can leave received packet buffers unaccounted-for, with the potential to cause kernel crashes and buffer leaks unless the upstream patch is applied.
The ath12k driver is the in‑tree Linux kernel driver that supports several Qualcomm Atheros Wi‑Fi chipsets (the “ath12k” family). It implements receive (RX) and transmit (TX) paths, hardware descriptor parsing, and error handling for Qualcomm REO/RX rings and HAL descriptor formats. Over the past few years maintainers have hardened the driver’s parsing and error paths multiple times because wireless firmware and hardware can deliver a variety of descriptor shapes under recovery and error conditions; when the kernel driver misclassifies or mishandles those descriptors, the consequences range from leaked memory to kernel oopses. CVE-2025-68729 is a focused correctness fault in the RX error-handling path: packets arriving on the REO exception ring from unassociated peers can be packaged as MSDU buffer type entries, while the error-path parsing function expected link descriptor type packets. The parsing routine returns early in that case and — crucially — fails to free the associated socket buffer (skb). That leaves the skb hanging and can lead to kernel instability via memory exhaustion or crashes when error handling proceeds. Upstream maintainers fixed the behavior by changing the RX error handler to explicitly drop MSDU‑type packets received on the REO exception ring so they are not forwarded into code paths that assume a different descriptor format. The change has been merged into the kernel stable trees.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
The ath12k driver is the in‑tree Linux kernel driver that supports several Qualcomm Atheros Wi‑Fi chipsets (the “ath12k” family). It implements receive (RX) and transmit (TX) paths, hardware descriptor parsing, and error handling for Qualcomm REO/RX rings and HAL descriptor formats. Over the past few years maintainers have hardened the driver’s parsing and error paths multiple times because wireless firmware and hardware can deliver a variety of descriptor shapes under recovery and error conditions; when the kernel driver misclassifies or mishandles those descriptors, the consequences range from leaked memory to kernel oopses. CVE-2025-68729 is a focused correctness fault in the RX error-handling path: packets arriving on the REO exception ring from unassociated peers can be packaged as MSDU buffer type entries, while the error-path parsing function expected link descriptor type packets. The parsing routine returns early in that case and — crucially — fails to free the associated socket buffer (skb). That leaves the skb hanging and can lead to kernel instability via memory exhaustion or crashes when error handling proceeds. Upstream maintainers fixed the behavior by changing the RX error handler to explicitly drop MSDU‑type packets received on the REO exception ring so they are not forwarded into code paths that assume a different descriptor format. The change has been merged into the kernel stable trees. What went wrong — technical root cause
At a high level, the bug is an error‑path mismatch between descriptor type and cleanup logic.- On normal RX paths the driver expects a certain descriptor layout (a link descriptor) and parses the descriptor to create an skb and hand it to the network stack.
- In the REO exception ring — a special ring used when the hardware indicates an exception or error — packets from unassociated stations can arrive packaged as MSDU buffer type. The MSDU layout differs from the link descriptor layout.
- The parsing helper (ath12k_hal_desc_reo_parse_err checks the packet type and returns when it is not the expected kind, but the caller’s error path assumed the helper handled cleanup. Because the skb associated with the MSDU entry is not freed on the early return, the kernel ends up with an un-freed skb reference.
- Repeated or pathological conditions can therefore cause buffer leaks and in some sequences trigger crashes or oopses when subsequent code assumes resources have been released.
What the upstream fix does
The upstream patch set updates the RX error handler so that it:- Recognizes MSDU buffer‑type packets received on the REO exception ring and treats them as invalid in that context.
- Explicitly frees the associated skb for these MSDU entries instead of returning early without cleanup.
- Ensures the error‑path codepath exits cleanly without leaving references or buffer ownership unresolved.
Who and what is affected
The bug is in the Linux kernel upstream ath12k driver logic and therefore affects any systems that:- Build and load the in‑tree ath12k driver (module or built‑in), and
- Expose the REO exception path that can receive packets from unassociated peers (typical on APs, gateways, or devices handling management/guest traffic).
- Embedded devices and appliances using Qualcomm Atheros Wi‑Fi silicon served by ath12k (for example, some IoT gateways and OEM boards).
- Linux-based access points and routers that rely on in-tree ath12k rather than vendor-specific out-of-tree firmware wrappers.
- Virtual machines or containers running custom kernels that include ath12k (for example, test images, custom appliances, and some cloud guest kernels when vendor kernels are used).
Severity and exploitability — practical assessment
From the public records and the technical nature of the flaw, here is a measured risk profile:- Primary impact: Availability & stability. The bug causes leaked skbs and buffer accounting errors that can escalate to kernel oopses or host instability if triggered repeatedly. That is the main, demonstrable impact.
- Privileges: No privileged local access required when the device acts as an AP or accepts management frames — a remote device within radio range can send frames that are processed by the hardware and driver. In that sense the attack vector can be network‑facing via radio proximity for access points and stations that process frames from unassociated peers.
- Remote exploitation potential: Unlikely to directly yield privilege escalation or remote code execution. The documented issue is a resource-management / cleanup defect, not a direct memory corrupting write or controlled code‑path that typically yields RCE. Nonetheless, kernel stability bugs are high-value primitives. In multi-stage scenarios or when combined with other flaws, they can sometimes be leveraged for more severe outcomes. Treat that as a cautious, hypothetical concern rather than a proven ability at disclosure time.
How to detect exposure and triage systems
Administrators and maintainers should perform a focused triage to determine whether hosts are exposed:- Inventory drivers:
- Check whether the running kernel includes ath12k: uname -r; lsmod | grep ath12k; cat /boot/config-$(uname -r) | grep ATH12K (or similar).
- Kernel logs:
- Search dmesg / journalctl -k for ath12k traces, REO/exception ring messages, or warnings referencing RX error handling.
- Network role:
- Identify devices acting as APs or handling unassociated peer traffic (public hotspots, guest SSIDs, IoT hubs).
- Package mapping:
- Consult distribution and vendor advisories to map whether your kernel package includes the fixed commit or backported patch. Distribution trackers (SUSE/DEBIAN/Ubuntu/RHEL) and OSV entries publish mapping details; if your vendor’s package changelog mentions the specific fix or the CVE, the package can be accepted as a patch.
Mitigation and remediation guidance
Definitive remediation is to install vendor/distributor kernel updates that include the upstream fix (the patches have been merged into stable trees and backported by some vendors). Remediation checklist:- Identify the kernel package and its vendor mapping for your environment (distribution kernel vs vendor/kernel fork).
- If an updated kernel package is available that references CVE-2025-68729 (or lists the stable commit IDs), schedule update and reboot into the updated kernel.
- For appliances or embedded devices that do not receive timely vendor images, coordinate with the OEM for a patched firmware/kernel image. If you maintain custom images, merge the upstream patch into your kernel branch and rebuild.
- Where operationally acceptable, restrict which stations may reach the AP’s management or exception processing paths (e.g., tighten guest/management isolation, use MAC‑filtering for critical management interfaces) — note this is a limited mitigation because many management frames are unauthenticated by design.
- If the vulnerable driver is modular and the device does not require Wi‑Fi functionality temporarily, consider unloading the ath12k module as a stopgap: sudo modprobe -r ath12k. This is generally disruptive and not viable for production APs or devices needing wireless connectivity.
- Use host or network telemetry to throttle or isolate radios exposed to untrusted clients (for example, place critical APs on separate physical radios or VLANs).
Patch provenance and verification
Multiple independent trackers (NVD, OSV, CVE aggregators, and vendor security pages) include consistent descriptions of the issue and reference the upstream stable commits that implement the behavior change. These trackers also reference the hardware target used in testing (QCN9274 hw2.0 PCI). When verifying in your environment:- Prefer vendor or distribution advisories that map the CVE to a package version or stable commit ID. Do not rely solely on generic CVE text if you must demonstrate a fix for compliance records.
- When possible, corroborate vendor packages by checking the package changelog for the commit IDs or patch descriptions, or by verifying the kernel source under your packaging tree includes the corresponding changes to the RX error handler.
- If you build custom kernels, apply the patch from the upstream stable commit(s) and run a brief hardware validation on representative test devices before deploying to production. Public CVE entries list commit references that can be used to locate the patch in upstream stable trees.
Operational impact and prioritization
How high should this be on a remediation queue?- For devices that act as Wi‑Fi APs or otherwise process management frames from unassociated stations (public hotspots, guest networks, IoT hubs), prioritize remediation: the attack surface is wide and the impact is availability of a network service.
- For endpoint laptops or desktops that do not serve as APs and are not exposed to frequent unassociated client traffic, the immediate risk is lower; still schedule updates as part of normal kernel patching cadence.
- For embedded appliances where vendor backports lag, treat these as high‑priority because they commonly run for long periods without updates and can be accessible to adjacent radio attackers or malicious devices during provisioning/test flows.
- Does the host act as an access point or gateway exposed to unassociated peers?
- Can you apply a kernel update with minimal service disruption?
- Is the host part of a critical control plane (e.g., IoT management, industrial control) where an availability failure would cascade into operational outages?
Broader context: why small driver fixes matter
Kernel drivers routinely manipulate DMA descriptors, hardware rings, and skbs under strict ownership rules. Small mistakes in error paths often translate into high operational cost:- Resource leaks in the kernel are more dangerous than similar leaks in userland because they accumulate across all workloads and sometimes require reboots.
- Drivers deal directly with hardware-provided data that can vary under error or recovery conditions; defensive programming in parsing and cleanup is essential.
- Because many distributions backport fixes, a single upstream change can appear in multiple kernel minor versions — operators must vet vendor update notes rather than relying solely on kernel release numbers.
How to communicate this to stakeholders
When briefing operators or customers:- Explain that CVE-2025-68729 is an upstream kernel driver fix for an RX error-handling bug in ath12k that can cause leaked packet buffers and kernel instability.
- Emphasize the recommended action: install the vendor-supplied kernel update or patched firmware image and reboot into the updated kernel.
- If customers run constrained embedded devices, advise them to check with OEM support for patched images and to plan safe replacement or over‑the‑air update paths for devices in the field.
- Document the package version or commit ID used to validate the fix for compliance or audit trails.
Unverifiable or evolving points — flagged
- At the time of this writing, some public trackers had not yet published a CVSSv3 numeric score for CVE‑2025‑68729; the NVD and several aggregators show the vulnerability details but leave severity fields unpopulated or deferred. This is common in recently assigned CVEs. Treat the lack of a numeric score as an absence of assigned severity by those indexes and use the technical analysis above for operational prioritization.
- Access to upstream git.kernel.org commit pages may be intermittently rate‑limited from automated fetches in some tooling; vendors’ package changelogs are the most reliable source for proof that a backport is present in your environment. If you cannot fetch upstream commits directly, validate using your distribution’s advisory and package metadata.
Action checklist (quick reference)
- Inventory: Confirm which machines load ath12k (lsmod, package lists).
- Triage: Check logs for ath12k/REO exception ring messages and monitor skb/slab growth under wireless load.
- Patch: Apply vendor/distribution kernel updates that list CVE-2025-68729 or the upstream stable commit; reboot.
- Test: Validate connectivity and stability on representative devices; monitor kernel logs after deployment.
- Communicate: Record package versions and commits used to remediate for audit reporting.
Conclusion
CVE‑2025‑68729 is a focused but important kernel correctness fix for the ath12k wireless driver that closes a resource-leak and cleanup gap in the RX error path. The fix is small and low-risk from a regression standpoint, but the operational consequences of leaving it unpatched — particularly on APs, gateways, and long-lived embedded images — can be real: leaked buffers, kernel instability, and service disruption. Operators should verify whether the ath12k driver is present in their images, map vendor kernel packages to the upstream fixes, and prioritize patches for network‑facing wireless infrastructure and embedded endpoints. The upstream stable commits and multiple independent CVE trackers document the change; the most practical route to remediation is installing vendor-provided kernel packages that incorporate the upstream backport as soon as those are available.Source: MSRC Security Update Guide - Microsoft Security Response Center