A subtle bug in pip’s wheel extraction logic has produced CVE‑2026‑1703 — a limited path‑traversal flaw that can allow specially crafted wheel (zip) archives to place files outside the intended installation directory during a normal pip install. The defect is narrowly scoped — the traversal is constrained to prefixes of the installation directory — but the finding is a clear reminder that archive unpacking remains a recurrent attack surface for supply‑chain and installer attacks across ecosystems. (nvd.nist.gov) (github.com)
Wheel files are the standard binary distribution format for Python packages: ZIP archives containing package files plus the RECORD metadata used by installers. Because wheels are archives, installation requires unpacking files into a chosen installation directory; that step must guard against filenames that include directory components such as ../ or pathological names that would result in files being written outside the intended target. Historically, extraction bugs and incorrect path containment checks have produced high‑impact vulnerabilities in many ecosystems — from tar and zip libraries to package managers — and CVE‑2026‑1703 follows the same class. (nvd.nist.gov)
The Python Software Foundation (the CNA for this CVE) and multiple vulnerability trackers summarize the issue succinctly: when pip installs and extracts a maliciously crafted wheel, files may be written outside the installation directory because the containment check was implemented incorrectly. However, the NVD notes that the traversal is limited to prefixes of the installation directory, reducing the scenarios where an attacker can reach system executables or otherwise escalate to a full‑blown remote code execution. The maintainers issued a code fix and unit tests that address the root cause. (nvd.nist.gov)
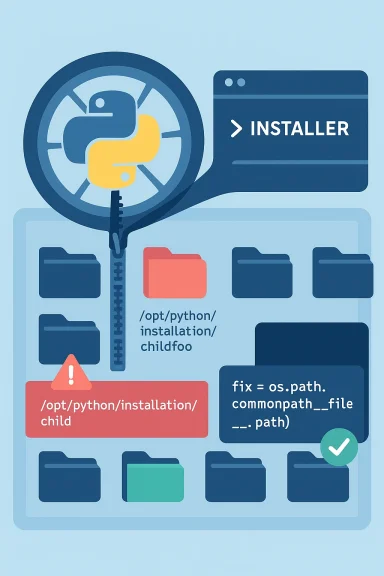
Put concretely: a string‑based prefix test can falsely claim that a path like /opt/python/installation/childfoo is inside /opt/python/installation/child because the character prefix of both strings matches. An attacker who crafts wheel entries whose file paths exploit that mismatch can induce extraction logic to accept writes that should have been rejected. The pip team fixed the check by replacing commonprefix() with commonpath(), and they added unit tests that specifically detect cases where a target path is a substring of a legitimate parent path (for example, parent/child vs parent/childfoo). The GitHub commit shows the one‑line change and the test additions that close this gap. (github.com)
This specific root cause — character‑level prefix vs component‑level path containment — has appeared repeatedly in other archive and unpacking advisories across ecosystems. Recent CVEs affecting tar libraries and node tar implementations show the same class of problem: path normalization and containment checks are easy to get wrong, and archives remain a preferred vehicle for deception because they combine compression, nested paths, and many file entries. That historical context makes the pip fix both unsurprising and necessary.
However, enterprise scenarios raise additional concerns:
For most users the practical risk is limited, but organizations that run pip installs in privileged contexts — CI runners, system images, or as service accounts — should treat this as a high‑priority operational issue: update pip, re‑build critical images, scan recent installations, and harden package handling pipelines. The incident is a timely reminder that archive extraction remains a perennial source of supply‑chain risk; defenses require both correct library code and system‑level hardening. (nvd.nist.gov)
(As of March 17, 2026 there are no confirmed, widespread in‑the‑wild exploit reports tied to CVE‑2026‑1703; the public advisories and tracker entries focus on the patch and distribution updates rather than active exploitation. Administrators should nonetheless patch and verify their environments promptly.) (nvd.nist.gov)
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
Wheel files are the standard binary distribution format for Python packages: ZIP archives containing package files plus the RECORD metadata used by installers. Because wheels are archives, installation requires unpacking files into a chosen installation directory; that step must guard against filenames that include directory components such as ../ or pathological names that would result in files being written outside the intended target. Historically, extraction bugs and incorrect path containment checks have produced high‑impact vulnerabilities in many ecosystems — from tar and zip libraries to package managers — and CVE‑2026‑1703 follows the same class. (nvd.nist.gov)The Python Software Foundation (the CNA for this CVE) and multiple vulnerability trackers summarize the issue succinctly: when pip installs and extracts a maliciously crafted wheel, files may be written outside the installation directory because the containment check was implemented incorrectly. However, the NVD notes that the traversal is limited to prefixes of the installation directory, reducing the scenarios where an attacker can reach system executables or otherwise escalate to a full‑blown remote code execution. The maintainers issued a code fix and unit tests that address the root cause. (nvd.nist.gov)
What went wrong: the technical root cause
At the heart of CVE‑2026‑1703 is a deceptively small programming mistake: pip’s extraction code used os.path.commonprefix() to test whether an extracted file path lies inside the intended installation directory. The problem is that commonprefix() operates on strings character‑by‑character, not on path components. That makes it unsafe for path containment checks because it can return a prefix that matches partial path segments rather than whole directory names. By contrast, os.path.commonpath() compares path components and is the correct choice for this use. (github.com)Put concretely: a string‑based prefix test can falsely claim that a path like /opt/python/installation/childfoo is inside /opt/python/installation/child because the character prefix of both strings matches. An attacker who crafts wheel entries whose file paths exploit that mismatch can induce extraction logic to accept writes that should have been rejected. The pip team fixed the check by replacing commonprefix() with commonpath(), and they added unit tests that specifically detect cases where a target path is a substring of a legitimate parent path (for example, parent/child vs parent/childfoo). The GitHub commit shows the one‑line change and the test additions that close this gap. (github.com)
This specific root cause — character‑level prefix vs component‑level path containment — has appeared repeatedly in other archive and unpacking advisories across ecosystems. Recent CVEs affecting tar libraries and node tar implementations show the same class of problem: path normalization and containment checks are easy to get wrong, and archives remain a preferred vehicle for deception because they combine compression, nested paths, and many file entries. That historical context makes the pip fix both unsurprising and necessary.
How exploitation would (theoretically) work
- An attacker publishes or distributes a wheel that contains malicious files whose archive member names are chosen to exploit the faulty prefix check.
- When pip unpacks the wheel into the target installation directory, the flawed containment check incorrectly treats one or more archive members as being within the target.
- As a result, files are extracted to locations adjacent to or above the intended folder — for example, to sibling directories or parent directories that share the same string prefix.
- The attacker’s payload can be anything the file system and file permissions allow: configuration files, data files, or items that can be consumed by other components. Because traversal is limited to prefixes of the installation directory, arbitrary writes to system directories (for instance, overwriting critical executables in /usr/bin on well‑segregated systems) are typically prevented in standard installations; however, the actual impact depends heavily on how pip is invoked (user‑local installs vs system installs) and on the environment’s permission model. (nvd.nist.gov)
Affected packages and distributions
- The vulnerability is in pip’s extraction logic; therefore, most installations that use pip to install wheel packages may be affected until pip is updated. The OSV and NVD entries list pip as the affected component.
- Distribution trackers show how this ripples into packaged versions. Debian’s security tracker lists multiple pip package versions and identifies which releases remain vulnerable and which have been fixed; for example, Debian unstable (sid) has a fixed version while several stable branches were flagged vulnerable prior to being updated. That tracking is important for administrators who rely on distribution packaging rather than upstream pip releases. (security-tracker.debian.org)
- Independent vulnerability databases and vendor advisories (OSV, AWS ALAS, Tenable and others) have indexed the CVE and note the same technical details and recommended action: upgrade to the patched pip release. These independent sources corroborate the fix and provide distribution‑specific guidance for package consumers and maintainers.
Mitigation and detection: practical steps for administrators and developers
Immediate actions to reduce risk:- Upgrade pip promptly.
- If you use pip directly (python -m pip), upgrade to the pip release that includes the merged fix (the upstream commit and subsequent release include the change). If you rely on a distribution package, apply the vendor or distribution updates that include the patched pip package. Distribution trackers such as Debian’s security tracker are useful to verify whether your packaged pip has been updated. (github.com)
- Treat wheel archives from untrusted sources as suspect.
- Avoid installing wheels from unverified external sources. Use cryptographic verification where available (package signatures, vendor mirrors, or pinned hashes) and favor installing packages from trusted registries with provenance controls.
- Harden CI and build pipelines.
- Run builds in least‑privileged containers and avoid running pip installs as root in CI agents where possible. If builds require elevated rights, restrict the set of allowed package sources and scan wheel contents before extraction.
- Scan wheel contents before installing.
- When you must accept third‑party wheels, inspect the archive contents for suspicious paths (entries containing ../, drive‑relative constructs on Windows, or names that might be interpreted as device names). Automated pre‑installation checks can be added to CI pipelines.
- Monitor for unexpected filesystem changes.
- Use host‑based file integrity monitoring to detect new or modified files in directories adjacent to Python installation directories. Alert on writes to parent/sibling directories that coincide with package installs.
- Adopt defense‑in‑depth.
- Use runtime isolation (containers, virtual envs), enforce application whitelisting where possible, and avoid mixing system‑level and user‑level package installations. Consider policies that enforce pip --user or virtual environment installs for build and runtime separation.
- Review recently installed wheels’ RECORD entries and the list of files extracted during installation for any path entries that resolved outside the intended installation target.
- In logs and CI trace artifacts, look for pip extraction errors or warnings and for file creation events in directories adjacent to installation targets within a short window after package installs.
- Use file‑system monitors (auditd, Windows File Auditing, or host IDS) to flag unexpected modifications in parent directories of site‑packages or virtualenv roots.
Risk assessment — what this means for Windows users and enterprises
For many desktop and developer environments, pip installs are performed by individual users into per‑user folders (for example, user site‑packages, virtual environments). In those contexts, the limited nature of the traversal makes high‑impact exploitation less probable: attackers can write into user‑writable locations that are already under the control of the installing user, and the ability to escalate beyond that depends on other misconfigurations. NVD’s record reinforces this, noting the traversal is limited to prefixes of the installation directory. (nvd.nist.gov)However, enterprise scenarios raise additional concerns:
- CI‑based builds and container image production frequently run package installs with elevated privileges or as part of layered filesystem commits. A malicious wheel that writes files in places used by build tooling, or that persists into a docker image layer, can lead to supply‑chain contamination reaching production artifacts.
- On Windows, path semantics and device names have caused surprising bypasses in other path‑validation code (for example, handling of device names like CON, NUL, COM1 or drive‑relative paths). While pip’s fix addresses the specific commonprefix misuse, defenders should still validate archive entry names against platform‑specific rules and watch for unusual archive members that exploit Windows path semantics. Prior incidents in other projects underscore the importance of platform‑aware checks. (nvd.nist.gov)
Broader ecosystem implications and the repeat‑pattern problem
CVE‑2026‑1703 is not an isolated programming error; it sits atop a long sequence of archive extraction flaws across languages and package managers. The recurring pattern is the same: subtle differences between string operations and path component semantics, or improper normalization and symlink handling, repeatedly produce escape vectors from an extraction root. The antidote is multi‑pronged:- Libraries and package managers must favor well‑tested, component‑aware path containment checks and canonicalization that handle platform specifics, symlinks, and device names.
- Upstream unit tests should include malicious archive testcases — archives that intentionally include edge cases, substrings, drive‑relative paths and symlinks — to ensure future regressions are caught before release.
- Distribution packagers and downstream integrators should treat archive handling in their dependencies as a security‑critical surface, and apply vendor patches quickly into distro builds and images. Debian’s tracker and other distro advisories are a good example of how to map upstream fixes into packaged releases. (security-tracker.debian.org)
Checklist: What to do now (for sysadmins, developers, and CI owners)
- Verify pip versions on hosts and in CI images. If your pip predates the upstream fix, schedule updates or rebuild images that include the patched pip package. For packaged distributions, consult your distro’s security tracker to confirm the patched package is installed. (security-tracker.debian.org)
- Update build agents and container base images, especially images used to build production artifacts, to use the patched pip version.
- Run an audit of recent installations in privileged contexts (CI agents, build servers, system pip installs) looking for unusual file writes around package install times.
- Add pre‑install archive inspection to CI pipelines where external wheels are used: flag ../ entries, drive‑relative constructs, or entries whose normalization escapes the intended root.
- Enforce the principle of least privilege for pip installs: prefer virtual environments, --user installs, and non‑root build agents.
- Subscribe to vendor advisories and distro trackers to catch follow‑on fixes for related unpacking issues in other packaging code (wheel, setuptools, zipfile, tar wrappers).
Conclusion
CVE‑2026‑1703 is a compact but instructive vulnerability: a single choice of string‑based prefix comparison introduced a path containment weakness that could be exploited by malicious wheel archives. The pip maintainers responded with a minimal, correct fix — swapping os.path.commonprefix for os.path.commonpath — and added targeted unit tests, which is the right engineering response to this class of defect. (github.com)For most users the practical risk is limited, but organizations that run pip installs in privileged contexts — CI runners, system images, or as service accounts — should treat this as a high‑priority operational issue: update pip, re‑build critical images, scan recent installations, and harden package handling pipelines. The incident is a timely reminder that archive extraction remains a perennial source of supply‑chain risk; defenses require both correct library code and system‑level hardening. (nvd.nist.gov)
(As of March 17, 2026 there are no confirmed, widespread in‑the‑wild exploit reports tied to CVE‑2026‑1703; the public advisories and tracker entries focus on the patch and distribution updates rather than active exploitation. Administrators should nonetheless patch and verify their environments promptly.) (nvd.nist.gov)
Source: MSRC Security Update Guide - Microsoft Security Response Center