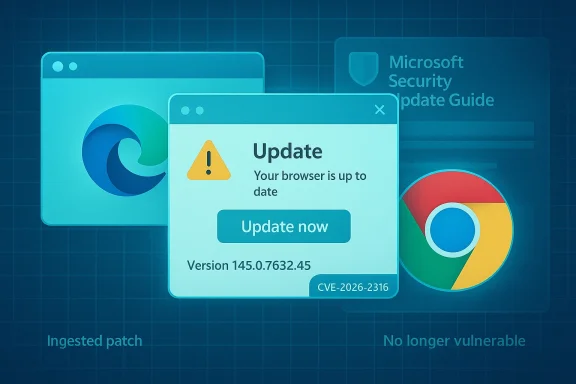
Chromium’s CVE-2026-2316 — an insufficient policy enforcement in Frames issue that allows UI spoofing via a crafted HTML page — has been logged not only in Chromium/Chrome advisories but also inside Microsoft’s Security Update Guide (SUG). That single cross-listing raises a common question: why does Microsoft publish a Chrome-assigned CVE in its own database, and what does that mean for your Microsoft Edge installation? This article explains the mechanics behind the listing, verifies which upstream and downstream builds contain the fix, and gives step‑by‑step guidance (and checks) so you can confirm whether your browser is protected.
Chromium is an open-source browser engine that underpins many modern browsers — including Google Chrome, Microsoft Edge (Chromium-based), Brave, Vivaldi, and many embedded runtimes. When a vulnerability is discovered and assigned a CVE by Chromium/Google, the upstream project publishes a fixed Chromium/Chrome build. Downstream vendors then merge those upstream changes into their own browser releases on their own release cadence. Microsoft’s Security Update Guide documents vulnerabilities that affect Microsoft products — including cases where the root issue is in third-party open-source components consumed by Microsoft products.
The short, practical headline for readers: CVE‑2026‑2316 is a Chromium-origin UI-spoofing risk that was fixed upstream in Chrome/Chromium 145.0.7632.45 (and later builds). Microsoft lists this CVE in SUG to indicate whether the Microsoft Edge builds that ingest that Chromium revision remain vulnerable or are already remediated. Use the version-check steps below to confirm whether your local browser is running a patched build.
Two concise points to keep in mind:
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
Chromium is an open-source browser engine that underpins many modern browsers — including Google Chrome, Microsoft Edge (Chromium-based), Brave, Vivaldi, and many embedded runtimes. When a vulnerability is discovered and assigned a CVE by Chromium/Google, the upstream project publishes a fixed Chromium/Chrome build. Downstream vendors then merge those upstream changes into their own browser releases on their own release cadence. Microsoft’s Security Update Guide documents vulnerabilities that affect Microsoft products — including cases where the root issue is in third-party open-source components consumed by Microsoft products.The short, practical headline for readers: CVE‑2026‑2316 is a Chromium-origin UI-spoofing risk that was fixed upstream in Chrome/Chromium 145.0.7632.45 (and later builds). Microsoft lists this CVE in SUG to indicate whether the Microsoft Edge builds that ingest that Chromium revision remain vulnerable or are already remediated. Use the version-check steps below to confirm whether your local browser is running a patched build.
What is CVE‑2026‑2316?
Technical summary
- The public description for CVE‑2026‑2316 is: “Insufficient policy enforcement in Frames in Google Chrome prior to 145.0.7632.45 allowed a remote attacker to perform UI spoofing via a crafted HTML page.” That language is used in multiple trackers and reflects Chromium’s own summary of the issue.
- UI spoofing in this context means a web page can present or manipulate visual UI elements (or the user’s interaction flow) so that the user is misled about what action they are taking or what page they are interacting with. This is not arbitrary code execution, but it can be a precursor to phishing, social-engineering, and unintended clicks that trigger dangerous behavior (for example, approving downloads, uploading files, or revealing credentials). The Chromium classification for this issue is Medium.
Why severity matters
While UI‑spoofing vulnerabilities do not directly yield remote code execution, they facilitate deception attacks that remain highly dangerous in real-world phishing scenarios. UI-level integrity loss is often exploited in targeted phishing, drive‑by social engineering, and red-team techniques to bypass UI-based defenses. Treat medium‑severity UI spoofing issues seriously — especially in environments where users handle sensitive data or approval workflows.Why is the Chrome-assigned CVE included in Microsoft’s Security Update Guide?
Microsoft’s Security Update Guide includes vulnerabilities that affect Microsoft products — and that explicitly includes CVEs assigned by other parties when the vulnerable code is part of open-source components Microsoft consumes. In other words, Microsoft uses SUG as a downstream remediation status tracker: when a Chromium CVE is added to SUG, Microsoft is telling administrators whether Microsoft Edge (or other Microsoft products that bundle the same OSS) is still vulnerable or has already ingested the upstream patch. This is an operational transparency measure, not an admission Microsoft introduced the bug.Two concise points to keep in mind:
- The CVE origin (Chromium/Chrome) remains the primary assigner; Microsoft’s SUG entry documents the downstream ingestion status for Microsoft Edge.
- If SUG shows “no longer vulnerable” for a Chrome-origin CVE, Microsoft’s Edge builds have been updated to include the upstream fix; if it shows “vulnerable,” Edge has not yet incorporated that specific Chromium revision. Always check the SUG entry and Microsoft Edge release notes for the authoritative downstream statement.
How to verify whether you are protected: see the browser version
The quickest way to verify whether your browser is patched is to identify the exact version string your browser reports and compare it to the fixed upstream build (Chrome 145.0.7632.45 or later) or the Microsoft Edge build that ingested Chromium 145. The following sections walk you through those checks for both Chrome and Edge.A. Check Google Chrome (desktop)
- Open Google Chrome.
- Click the three-dot menu (Customize and control Google Chrome) in the upper-right corner.
- Go to Help → About Google Chrome. The About page shows the full Chrome version and automatically checks for updates. If an update is available it will download and ask you to Relaunch. Alternatively, you can type chrome://version or chrome://help into the address bar to see the full version string.
B. Check Microsoft Edge (desktop)
- Open Microsoft Edge.
- Click Settings and more (three dots) in the top-right corner → Settings.
- Select About Microsoft Edge from the left-hand sidebar (or go directly to edge://settings/help). Edge will show the full product version and will check for updates automatically.
C. Quick command-line checks (for scripted verification)
- Windows: run msedge --version or chrome --version in a CMD or PowerShell prompt to get the product version for scripting and inventories.
- Cross-platform: navigate to chrome://version or edge://version and copy the version string for automated comparison.
Mapping Chrome/Chromium fixed builds to Microsoft Edge
Chromium fixes are published by Google as Chrome builds. Downstream vendors (including Microsoft) must merge upstream Chromium commits into their own source trees; that means the upstream patch becomes available at different times for different browsers. For CVE‑2026‑2316, Chromium/Chrome’s published fix baseline is Chrome/Chromium 145.0.7632.45. To know whether Microsoft Edge is protected, you must either:- Check Microsoft’s Security Update Guide entry for CVE‑2026‑2316 (SUG will indicate whether Edge builds are vulnerable or not) — or —
- Check Microsoft Edge release notes which list Chromium security updates incorporated into Edge builds and the Edge product version that contains those artifacts.
Enterprise implications and special cases
Embedded Chromium runtimes remain a frequent blind spot
Many enterprise applications and internal tools embed Chromium via runtimes such as WebView2, Electron, or custom packaged Chromium binaries. Those embedded runtimes do not necessarily update when the system browser updates; vendors must rebuild and re-release their application to include upstream Chromium fixes.- Action: inventory your environment for embedded Chromium runtimes (Electron apps, packaged browsers, kiosk apps, WebView2 hosts). Ask the vendor which Chromium revision they ship and when they will update. If a third‑party vendor cannot commit to a timely update, consider compensating controls (restricting untrusted content load, sandboxing, or isolating the process).
Staged rollouts and partial wave effects
Both Chrome and Edge often roll out updates in waves. Two identical devices checked at the same time can report different point releases until the update wave completes. Rely on the installed product version — not assumptions — to determine protection. For compliance evidence capture the About/version page and the corresponding SUG or vendor release note stating ingestion.When to prioritize remediation
- Users who handle sensitive data, perform approvals, or access corporate credential vaults should be prioritized for immediate update.
- Unmanaged devices that might not auto-update should be targeted first.
- Systems running older OS versions where browsers cannot auto-update may require alternative mitigations (e.g., replacing with updated browsers, using isolated VMs for risky browsing, or network-level filtering).
Recommended actions: step-by-step
- Identify affected endpoints. Use centralized inventory tools to gather the reported version strings for Chrome (chrome --version or chrome://version) and Edge (msedge --version or edge://version).
- Compare the reported Chromium/Chrome revision to the upstream fixed baseline: 145.0.7632.45 (or later). If your Chrome is at or above that build, Chrome is patched upstream.
- For Microsoft Edge, check the Chromium revision shown in edge://version — confirm ingestion by comparing to Microsoft’s SUG entry or Edge release notes. Don’t assume a patched Chrome means a patched Edge.
- Apply updates: For end users, update Chrome via Help → About Google Chrome and Edge via Settings → About Microsoft Edge. For managed fleets, push the vendor-provided updates or use your management tools to enforce the update.
- For apps embedding Chromium (Electron / WebView2 / packaged runtimes), contact vendors for updated releases and prioritize remediation for apps exposed to untrusted content. If vendor fixes are delayed, consider isolating those apps (application control, network segmentation, or dedicated VMs).
Detection and mitigation advice
- Detection: Look for suspicious click patterns, unexpected permission dialogs, or user reports of UI oddities. While UI spoofing leaves little forensic trace like memory corruption, correlated telemetry (sudden downloads, unauthorized file uploads, or anomalous interactions) can be useful signals. Employ EDR rules that track unusual browser dialogs or downloads initiated without clear user intent.
- Mitigations until patched:
- Train users to be wary of contextless dialogs and unexpected file-selection prompts.
- Disable or restrict untrusted web content in sensitive environments.
- Use content security policies (CSP) and browser-managed site‑isolation features where feasible.
- Consider enterprise policies that limit extensions or unapproved navigation flows on managed devices.
Critical analysis: strengths and limitations of Microsoft’s SUG approach
Strengths
- Operational transparency: Listing third‑party CVEs in SUG with an “ingestion” status provides enterprise customers a single, authoritative place to check whether Microsoft’s consumer and enterprise products have been remediated downstream. This saves administrators from monitoring dozens of upstream projects independently. Microsoft documented the policy change in its MSRC blog, and SUG’s Assigning CNA field was introduced explicitly to handle third‑party OSS issues.
- Actionable mapping: When SUG states “no longer vulnerable,” that is effectively a downstream “fix shipped” signal — useful for audit evidence and patch-tracking. Edge release notes and SUG together form an evidentiary record for IT compliance workflows.
Limitations and risks
- Rollout timing mismatch: Upstream fixes exist before downstream vendors publish their ingesting builds. If administrators rely only on Chrome advisories, they may mistakenly assume Edge is protected when it is not. The inverse is also true: Edge may be patched downstream after Chrome's staged rollout — making synchronous checks necessary. Always check the installed product version string.
- Opaque details for some CVEs: Chromium and Google sometimes withhold details until a majority of users are updated. That protects users but can make enterprise risk assessments harder in the short term. SUG entries may include limited technical detail, so defenders must combine vendor announcements, CVE descriptions, and telemetry to fully assess exposure.
- Third‑party runtime exposure: WebView2, Electron, and other embedded runtimes may remain vulnerable long after both Chrome and Edge are patched. SUG does not directly reach into third‑party packaged apps your organization runs — you must inventory and coordinate with vendors.
Final takeaways and practical checklist
- CVE‑2026‑2316 is an upstream Chromium UI‑spoofing issue fixed in Chrome/Chromium 145.0.7632.45 (or later). Confirm this upstream baseline when mapping your product status.
- Microsoft lists Chrome-assigned CVEs in the Security Update Guide to document whether Microsoft Edge (or other Microsoft products that bundle the same OSS) is still vulnerable or has ingested the patch. Use SUG plus Edge release notes as the authoritative downstream signal.
- How to verify quickly:
- Chrome: Menu → Help → About Google Chrome or chrome://version; patched if ≥ 145.0.7632.45.
- Edge: Settings → About Microsoft Edge or edge://version; check the embedded Chromium revision and match against Microsoft’s SUG / release notes.
- If you manage devices, script a version inventory (msedge --version / chrome --version / chrome://version snapshots), compare strings against the fixed baseline, prioritize updates for high-risk users, and inventory embedded Chromium runtimes separately.
Source: MSRC Security Update Guide - Microsoft Security Response Center