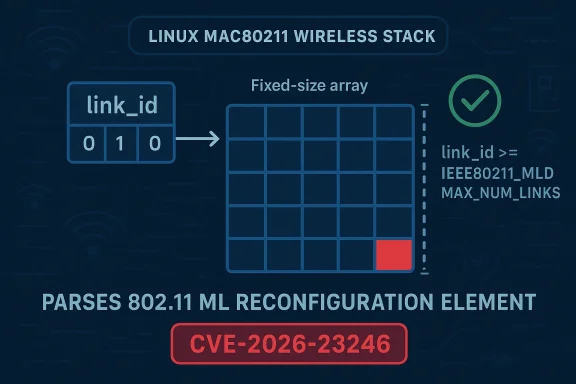
In the Linux kernel’s mac80211 wireless stack, a newly assigned vulnerability tracked as CVE-2026-23246 highlights a classic but still dangerous bug class: an out-of-bounds write caused by trusting an unvalidated index in a low-level parser. The issue sits in
The vulnerability lands in a part of the kernel that many users never think about directly: the 802.11 management and reconfiguration path that powers modern Wi‑Fi behavior. In Linux, mac80211 is the software layer that implements core Wi‑Fi functionality and mediates between drivers and higher-level networking logic. That matters because bugs in mac80211 are not just “driver issues”; they can affect a broad range of wireless devices and configurations, especially on systems that rely on upstream kernel networking code.
The CVE description says the flaw was fixed in code handling the ML Reconfiguration element, where
This is happening in the broader context of Multi-Link Operation (MLO) support in Wi‑Fi 7-era networking. MLO allows a device to use multiple links more flexibly, which improves throughput, latency, and resilience, but it also expands the amount of state the kernel must track. More links mean more bookkeeping, more control-plane messages, and more opportunities for parsing mistakes to turn into memory-safety bugs. That tradeoff is common in systems code: capability growth often arrives with a larger attack surface.
Linux kernel CVEs are typically issued after a fix is already in a stable tree, which helps explain why the record points to kernel.org and stable commit references rather than speculative exploit analysis. The kernel project also documents that CVE assignment is generally tied to published fixes in supported branches, not hypothetical vulnerabilities. In other words, this is not a theoretical bug report; it is a resolved defect that has been identified, patched, and then assigned a CVE for tracking and downstream remediation.
For enterprise Linux users, the most important takeaway is that wireless stack issues can be security issues even when they do not look remotely user-facing. A malformed management frame or reconfiguration element may be enough to trigger the parser path, and kernel memory corruption always deserves attention. Whether a device can be reached remotely in practice depends on deployment details, but the underlying flaw class is the kind security teams treat seriously. Stack out-of-bounds bugs are especially concerning because they can crash the kernel or open the door to escalation.
The kernel fix is as elegant as it is necessary: reject or skip any subelement whose
A second-order issue is that this code lives in a reconfiguration path, which often runs in privileged kernel context and may process data from complex protocol exchanges. That means the parser is not operating in a sandbox. If a malformed element gets through, the kernel itself pays the price, not a helper process with weaker privileges. That distinction matters enormously in risk analysis.
The challenge with MLO is not simply that there are more code paths. It is that those code paths often involve compact bitfields, state synchronization across links, and legacy assumptions from single-link Wi‑Fi that no longer hold. A four-bit field seems small and safe, but it is precisely the kind of field that can create off-by-one mistakes when the protocol definition and the implementation’s array sizes diverge. That kind of bug is easy to miss in code review because it looks superficially like a bounded integer.
This is especially relevant for wireless, where handling malformed over-the-air input is part of the job description. The kernel has to be robust even when the radio environment is hostile, noisy, or actively malicious. That makes a seemingly small bounds check an important defensive barrier rather than a cosmetic cleanup.
This kind of fix also reflects a broader kernel principle: validate as close to the boundary as possible. Once invalid data gets deep into a parser, the code tends to fan out across helper functions and state machines, making the eventual bug harder to reason about. Here, the correction appears to happen where the element is processed, which is exactly where one wants the guardrail.
It also shows why kernel fixes are often deceptively small. A one-line bounds check can hide days or weeks of analysis, particularly in a complex subsystem like Wi‑Fi where the interaction between protocol spec, implementation detail, and memory layout must all line up. Small patches can represent a large amount of technical debt being paid down at once.
The biggest uncertainty is exploitability in the field. A vulnerability may be technically reachable yet still hard to weaponize due to driver behavior, packet formatting constraints, or kernel mitigations such as stack protections. But security teams should resist the temptation to downgrade a bug just because exploitation is not immediately obvious. In kernel land, memory corruption plus parser reachability is enough to merit prompt patching.
For consumers, the more immediate concern is stability. A kernel crash triggered through wireless handling can look like random rebooting, frozen networking, or hard-to-reproduce system faults. If the path is attacker-triggerable in proximity, consumer devices in dense environments may be more exposed than users realize, especially in public spaces with lots of Wi‑Fi activity. Close-range does not mean low-risk when the vulnerable code sits in the kernel.
That workflow has benefits and tradeoffs. On the one hand, it ensures administrators can often find a concrete commit to backport or verify. On the other hand, it means the vulnerability may become visible to the public only after the fix exists, leaving a gap where defenders know something was wrong but may not yet have all the downstream packaging details they need. That lag is operationally important for large fleets.
For security teams, the operational lesson is simple: when a kernel CVE is tied to a wireless parser, verify the exact package version rather than relying on broad version ranges alone. The same upstream fix can appear under different downstream build numbers, vendor backports, or kernel flavors. That makes inventory accuracy just as important as patch availability.
It is also a reminder that array constants and protocol constants should be reviewed together, not in isolation. A constant such as
Another useful practice is to treat parser state as tainted until fully validated. That is especially relevant in wireless, where control frames and management elements can be deeply nested. The more code that depends on those inputs, the more expensive an unvalidated assumption becomes. Conservative parsing is not just stylistic discipline; it is security engineering.
For vendors competing in the Wi‑Fi 7 era, the message is mixed. On one hand, support for advanced features like MLO is a differentiator and a performance win. On the other hand, every new capability creates a larger maintenance burden and a more visible security surface. Organizations choosing platforms increasingly weigh not only speed and throughput, but also how quickly a vendor can ship kernel fixes and prove that backports are complete.
The competitive angle is not just about shipping fast; it is about shipping reliably. Enterprises increasingly judge platform maturity by the quality of security response, the clarity of advisories, and the speed of confirmed remediation. In that sense, CVE-2026-23246 is not only a kernel bug—it is a test of ecosystem discipline.
In the longer term, CVE-2026-23246 will likely be remembered less for its individual impact than for what it illustrates about the transition to multi-link Wi‑Fi. As protocols get richer, kernel implementations need correspondingly better guardrails, fuzzing, and review discipline. The organizations that treat this as a one-off patch will miss the larger lesson; the ones that treat it as a signal may prevent the next, harder-to-detect memory-safety issue.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
ieee80211_ml_reconfiguration, where link_id can legally range from 0 to 15, but the destination array has only 15 entries, making index 15 invalid. The upstream fix is straightforward in concept—skip any subelement whose link_id is greater than or equal to IEEE80211_MLD_MAX_NUM_LINKS—but the security implications are serious because a stack write past bounds can destabilize the kernel and, in the worst case, become a code-execution primitive.
 Background
Background
The vulnerability lands in a part of the kernel that many users never think about directly: the 802.11 management and reconfiguration path that powers modern Wi‑Fi behavior. In Linux, mac80211 is the software layer that implements core Wi‑Fi functionality and mediates between drivers and higher-level networking logic. That matters because bugs in mac80211 are not just “driver issues”; they can affect a broad range of wireless devices and configurations, especially on systems that rely on upstream kernel networking code.The CVE description says the flaw was fixed in code handling the ML Reconfiguration element, where
link_id is extracted from control & 0x000f. That means the parser accepts values from 0 through 15, but the associated link_removal_timeout[] array has only IEEE80211_MLD_MAX_NUM_LINKS elements, which is 15. Put plainly, the valid array indexes are 0 through 14, so 15 falls off the end.This is happening in the broader context of Multi-Link Operation (MLO) support in Wi‑Fi 7-era networking. MLO allows a device to use multiple links more flexibly, which improves throughput, latency, and resilience, but it also expands the amount of state the kernel must track. More links mean more bookkeeping, more control-plane messages, and more opportunities for parsing mistakes to turn into memory-safety bugs. That tradeoff is common in systems code: capability growth often arrives with a larger attack surface.
Linux kernel CVEs are typically issued after a fix is already in a stable tree, which helps explain why the record points to kernel.org and stable commit references rather than speculative exploit analysis. The kernel project also documents that CVE assignment is generally tied to published fixes in supported branches, not hypothetical vulnerabilities. In other words, this is not a theoretical bug report; it is a resolved defect that has been identified, patched, and then assigned a CVE for tracking and downstream remediation.
For enterprise Linux users, the most important takeaway is that wireless stack issues can be security issues even when they do not look remotely user-facing. A malformed management frame or reconfiguration element may be enough to trigger the parser path, and kernel memory corruption always deserves attention. Whether a device can be reached remotely in practice depends on deployment details, but the underlying flaw class is the kind security teams treat seriously. Stack out-of-bounds bugs are especially concerning because they can crash the kernel or open the door to escalation.
What the Bug Actually Is
At the technical core of CVE-2026-23246 is a mismatch between the valid value space and the size of the target buffer. The code interpretslink_id from a four-bit field, which naturally yields 16 possible values. Yet the array it indexes has only 15 entries, and the missing guard allows the highest valid field value to become an invalid memory access.The kernel fix is as elegant as it is necessary: reject or skip any subelement whose
link_id is out of range. That is the right engineering pattern for parsers and protocol handlers, especially in the kernel where one bad index is enough to corrupt memory. The fact that the remediation is a bounds check does not make the bug trivial; it makes it emblematic of a deeper rule in systems programming: parser inputs must never be assumed to line up perfectly with compile-time constants.Why the Stack Matters
The CVE text explicitly says the bug could cause a stack out-of-bounds write. Stack corruption is often more dangerous than a simple read past end because writes can alter return addresses, saved registers, or neighboring variables, depending on architecture and compiler behavior. Even when exploitability is uncertain, defenders usually treat stack writes as high-severity candidates until proven otherwise.A second-order issue is that this code lives in a reconfiguration path, which often runs in privileged kernel context and may process data from complex protocol exchanges. That means the parser is not operating in a sandbox. If a malformed element gets through, the kernel itself pays the price, not a helper process with weaker privileges. That distinction matters enormously in risk analysis.
- The parser accepts 16 possible
link_idvalues. - The backing array is sized for 15 links.
- The out-of-range value is
15. - The fix rejects subelements where
link_id >= IEEE80211_MLD_MAX_NUM_LINKS. - The memory-safety impact is a stack write beyond bounds.
Why MLO Makes This More Important
Multi-Link Operation is one of the defining architectural changes in next-generation Wi‑Fi. It is designed to let devices use more than one link at once, which can improve performance, reduce latency spikes, and offer better resilience when one band or channel degrades. But every added feature layer in a protocol stack increases complexity, and complexity is where memory bugs tend to hide.The challenge with MLO is not simply that there are more code paths. It is that those code paths often involve compact bitfields, state synchronization across links, and legacy assumptions from single-link Wi‑Fi that no longer hold. A four-bit field seems small and safe, but it is precisely the kind of field that can create off-by-one mistakes when the protocol definition and the implementation’s array sizes diverge. That kind of bug is easy to miss in code review because it looks superficially like a bounded integer.
Protocol Complexity and Security Debt
The security story here is familiar to anyone who tracks kernel hardening: new protocol capability arrives first, and the subtle cleanup work follows later. That does not mean the feature is unsafe by design; it means the implementation becomes a moving target. Each new element, counter, or optional substructure creates another place where the parser can drift away from the specification.This is especially relevant for wireless, where handling malformed over-the-air input is part of the job description. The kernel has to be robust even when the radio environment is hostile, noisy, or actively malicious. That makes a seemingly small bounds check an important defensive barrier rather than a cosmetic cleanup.
- MLO expands the number of state variables the kernel must manage.
- Compact protocol fields are easy to misread as “safe” simply because they are small.
- Off-by-one errors become more likely when array sizes and protocol ranges drift apart.
- Wireless parsers must assume hostile or malformed inputs.
- Security debt tends to accumulate during rapid feature evolution.
The Fix and Its Engineering Logic
The patch description points to a single decision point: skip any subelement whoselink_id is outside the valid link range. That is a classic kernel-hardening move because it preserves existing logic for good data while cleanly discarding malformed or unsupported inputs. In security terms, this is preferable to trying to “correct” the value or map it into range, which would risk hiding protocol errors.This kind of fix also reflects a broader kernel principle: validate as close to the boundary as possible. Once invalid data gets deep into a parser, the code tends to fan out across helper functions and state machines, making the eventual bug harder to reason about. Here, the correction appears to happen where the element is processed, which is exactly where one wants the guardrail.
Why the Patch Is Good Practice
There is a difference between a patch that merely stops a crash and a patch that makes the invalid state impossible. The latter is better. By rejectinglink_id values that cannot be represented safely in the array, the fix prevents the out-of-bounds write without changing the semantics of valid reconfiguration traffic. That is the sort of surgical remediation downstream vendors prefer.It also shows why kernel fixes are often deceptively small. A one-line bounds check can hide days or weeks of analysis, particularly in a complex subsystem like Wi‑Fi where the interaction between protocol spec, implementation detail, and memory layout must all line up. Small patches can represent a large amount of technical debt being paid down at once.
- Invalid input is discarded before it can touch memory.
- The fix preserves behavior for legitimate link IDs.
- The patch follows a defensive boundary-validation pattern.
- The remediation avoids changing protocol semantics.
- The change is minimal, which usually helps backporting.
Exposure and Real-World Risk
At the moment, the public record does not provide a CVSS score from NVD, so defenders do not yet have an official severity number from that source. Even without that score, the nature of the bug is enough to justify attention: kernel stack corruption in a networking path is not the kind of issue organizations can safely ignore. The practical severity will depend on whether the flaw is reachable from ordinary wireless traffic, what hardware and kernel versions are affected, and what mitigations are in place.The biggest uncertainty is exploitability in the field. A vulnerability may be technically reachable yet still hard to weaponize due to driver behavior, packet formatting constraints, or kernel mitigations such as stack protections. But security teams should resist the temptation to downgrade a bug just because exploitation is not immediately obvious. In kernel land, memory corruption plus parser reachability is enough to merit prompt patching.
Enterprise Versus Consumer Impact
For enterprises, the risk profile is broader because fleets often include laptops, embedded gateways, kiosks, and specialized devices that may run older kernel branches. The operational burden is also heavier: patch windows, firmware dependencies, and distribution-specific kernel packaging can all delay remediation. That means even a bug with limited real-world exploitability can become an exposure-management issue if patching lags.For consumers, the more immediate concern is stability. A kernel crash triggered through wireless handling can look like random rebooting, frozen networking, or hard-to-reproduce system faults. If the path is attacker-triggerable in proximity, consumer devices in dense environments may be more exposed than users realize, especially in public spaces with lots of Wi‑Fi activity. Close-range does not mean low-risk when the vulnerable code sits in the kernel.
- Severity is not yet quantified by NVD.
- Kernel stack writes are inherently concerning.
- Reachability may depend on specific Wi‑Fi scenarios.
- Enterprises face slower patch cycles and mixed hardware estates.
- Consumers may notice instability before they understand the cause.
How This Fits the Linux Kernel CVE Process
The Linux kernel documentation explains that CVEs are generally assigned after a fix is available and applied to a stable tree, which helps keep the public record tied to actionable remediation rather than speculation. That model is visible here: the record is grounded in a specific fix and linked stable references. It is a reminder that Linux security tracking is often patch-first rather than disclosure-first.That workflow has benefits and tradeoffs. On the one hand, it ensures administrators can often find a concrete commit to backport or verify. On the other hand, it means the vulnerability may become visible to the public only after the fix exists, leaving a gap where defenders know something was wrong but may not yet have all the downstream packaging details they need. That lag is operationally important for large fleets.
What the References Suggest
The published references point to multiple stable kernel commits, which usually signals that the fix has been propagated across more than one supported branch. That is good news for maintainers and package vendors because it suggests the patch is in a form suitable for backporting. Still, administrators should not assume their specific distribution has already shipped it; distribution kernels often lag upstream stable by days or weeks.For security teams, the operational lesson is simple: when a kernel CVE is tied to a wireless parser, verify the exact package version rather than relying on broad version ranges alone. The same upstream fix can appear under different downstream build numbers, vendor backports, or kernel flavors. That makes inventory accuracy just as important as patch availability.
- Identify the running kernel version on affected hosts.
- Compare it against your distribution’s advisory or backport notes.
- Confirm whether the wireless stack is compiled in or modular.
- Validate that the vendor kernel includes the bounds check.
- Reboot or roll through maintenance if the fix requires it.
Broader Security Lessons for Kernel Developers
This bug is a reminder that small protocol fields are not inherently safe. A four-bit value can still be dangerous if the implementation assumes the maximum value maps cleanly onto a buffer. Kernel code must treat every parsed integer as suspect until its relationship to the destination storage is proved correct.It is also a reminder that array constants and protocol constants should be reviewed together, not in isolation. A constant such as
IEEE80211_MLD_MAX_NUM_LINKS may describe current implementation limits, while a wire-format field may describe protocol encoding capacity. Those two numbers can easily drift apart as features evolve, and when they do, bugs like this become almost inevitable. That mismatch is where many kernel CVEs are born.Defensive Coding Patterns That Help
Kernel maintainers and driver authors can reduce this class of bug with a handful of habits that sound mundane but pay real dividends. These include explicit range checks, helper functions that centralize index validation, and tests that deliberately exercise boundary values like zero, the maximum valid value, and the first invalid value. When code is touched repeatedly for feature growth, those patterns become far more valuable than cleverness.Another useful practice is to treat parser state as tainted until fully validated. That is especially relevant in wireless, where control frames and management elements can be deeply nested. The more code that depends on those inputs, the more expensive an unvalidated assumption becomes. Conservative parsing is not just stylistic discipline; it is security engineering.
- Validate indexes immediately after parsing.
- Keep protocol bounds and buffer sizes in obvious proximity.
- Prefer dropping malformed inputs over trying to normalize them.
- Add tests for boundary values and malformed elements.
- Review feature additions for hidden off-by-one assumptions.
Competitive and Market Implications
Wireless stack security matters far beyond the Linux kernel tree because it feeds into distributions, device vendors, enterprise deployments, and embedded systems. A flaw in mac80211 can ripple through laptops, access-point software, industrial devices, and other systems that depend on upstream Linux networking code. That gives the vulnerability a broader footprint than the concise CVE description might suggest.For vendors competing in the Wi‑Fi 7 era, the message is mixed. On one hand, support for advanced features like MLO is a differentiator and a performance win. On the other hand, every new capability creates a larger maintenance burden and a more visible security surface. Organizations choosing platforms increasingly weigh not only speed and throughput, but also how quickly a vendor can ship kernel fixes and prove that backports are complete.
Why This Matters to OEMs and Distributors
OEMs and Linux distributors often absorb the practical cost of these issues. They must validate whether upstream fixes integrate cleanly with their own kernel branches, packaging systems, and hardware enablement stacks. A tiny upstream patch can still require substantial QA when it touches a subsystem as sensitive as wireless networking.The competitive angle is not just about shipping fast; it is about shipping reliably. Enterprises increasingly judge platform maturity by the quality of security response, the clarity of advisories, and the speed of confirmed remediation. In that sense, CVE-2026-23246 is not only a kernel bug—it is a test of ecosystem discipline.
- Wireless innovation increases the value of robust security response.
- Vendors with strong backport processes have an advantage.
- Enterprise buyers care about patch clarity as much as features.
- Security reputations can be affected by repeated parser bugs.
- Reliability in kernel maintenance is a market differentiator.
Strengths and Opportunities
The positive side of this disclosure is that the fix is precise, understandable, and low-risk to apply. More broadly, the incident creates an opportunity for maintainers and vendors to tighten boundary checks across the wireless stack, especially in new MLO-related code paths. It also reinforces the value of upstream stable processes, which turn latent defects into actionable patches before the problem spreads further.- The patch is narrowly targeted and easy to reason about.
- The bug was found before NVD had assigned a score, giving vendors time to respond.
- The issue creates a chance to audit adjacent MLO parsing logic.
- Stable-tree references make downstream backporting more straightforward.
- The fix improves trust in the wireless stack’s input validation.
- Security teams can use this CVE as a reminder to inventory kernel versions carefully.
- The incident may motivate broader fuzzing and boundary testing in mac80211.
Risks and Concerns
The concern is not only the specific out-of-bounds write, but what it says about the attack surface of increasingly complex Wi‑Fi features. Kernel memory corruption is always serious, and wireless parsing paths are reachable in environments where users have limited visibility into what is happening on the air. Until vendors confirm patches are deployed, administrators should assume exposure could exist on any system that ships the affected code path.- The flaw affects a privileged kernel component.
- Stack writes can lead to crashes or more severe exploitation.
- Reachability may be easier in dense wireless environments.
- Some systems may remain unpatched because they use older LTS kernels.
- Downstream backports can lag behind upstream fixes.
- Complex MLO parsing raises the chance of adjacent bugs.
- A lack of NVD scoring means defenders must assess risk themselves for now.
Looking Ahead
The immediate next step is straightforward: distribution maintainers and enterprise patch teams need to verify that their Linux kernels include the relevant bounds check in mac80211. After that, the more interesting work begins—reviewing whether similar assumptions exist elsewhere in the wireless reconfiguration path. One bug fixed is good; a class of bugs understood is better.In the longer term, CVE-2026-23246 will likely be remembered less for its individual impact than for what it illustrates about the transition to multi-link Wi‑Fi. As protocols get richer, kernel implementations need correspondingly better guardrails, fuzzing, and review discipline. The organizations that treat this as a one-off patch will miss the larger lesson; the ones that treat it as a signal may prevent the next, harder-to-detect memory-safety issue.
- Confirm patched kernel builds across all fleets.
- Watch for downstream advisories from your Linux vendor.
- Audit nearby mac80211 MLO parsing code for similar off-by-one patterns.
- Prioritize systems with active Wi‑Fi exposure, especially mobile endpoints.
- Track whether NVD publishes a severity score and whether vendor guidance changes.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center