The Linux kernel’s CVE-2026-23292 is a classic example of a bug that looks narrow on paper but matters because it sits in the kernel’s core synchronization machinery. The issue was assigned after maintainers fixed a recursive locking problem in
The vulnerability description shows the failure path clearly:
This kind of bug iernel semaphores are not just synchronization primitives; they are also enforcement boundaries for correctness. If the code holds one while calling into a function that may try to reacquire it, the behavior may range from lock contention to a hard deadlock, depending on the exact path and scheduling conditions. In kernel space, even “just” a deadlock is serious because it can stall I/O, freeze control paths, or cascade into broader system instability.
The fix is conceptually simple but technically important: switch the validation mechanism from filesystem-opening semantics to a lower-level pathname resolution call. By using
The CVE landed on March 25, 2026, and Ning enrichment, which is a reminder that the security ecosystem often learns about kernel bugs faster than it can fully score them. The practical lesson is that the absence of a CVSS score does not mean the issue is trivial; it often means the upstream fix is known, but the broader downstream analysis has not yet finished.
The core failure is not a buffer overflow, memory leak, or a use-after-free. It is a lock recursion hazard caused by the store method using a function that can re-enter configfs’s open path while the write path already holds a semaphore. That is a particularly nasty kind of bug because it usually appears only when the code tries to validate or inspect a path that points back into the same configfs subtree.
The report’s clue is the message
The upstream fix changes
A normal filesystem path open may be routine, but in configfs, open and write are often tightly coupled with object state. If the code tries to open an object while holding the write-side semaphore for that same object, the system can end up with a lock cycle even without any malicious intent. That makes “safe enough” patterns from ordinary file I/O potentially unsafe in configfs.
That is exactly why
The specific function mentioned,
Enterprise administrators should care because storage paths are frequently configured during boot, provisioning, or automation. A stuck control path in target setup can delay deployment, interfere with recovery workflows, or cause management tooling to hang at exactly the wrong time.
That matters because
In practical terms, the compatibility work matters because kernel fixes are only useful if they can land in real vendor trees. A pristine upstream patch that is impossible to backport is less helpful to users than a slightly more constrained solution that distributors can ship quickly.
That distinction matters because many vulnerability management programs still over-index on exploitability headlines. This bug is more operational than theatrical. If it triggers, the result is more likely to be a hung configuration operation, a blocked storage-management task, or in the worst case a broader kernel stall affecting dependent work.
A practical checklist:
A deadlock in a storage-control interface can prevent a system from being configured, remediated, or recovered. If the affected path is used during deployment or automation, the impact compounds quickly. For this reason, Linux kernel security disclosures routinely include fixes that are about concurrency correctness rather than attacker-controlled memory corruption.
This CVE also highlights an opportunity for kernel teams to audit similar store callbacks that validate paths by opening them. The pattern is dangerous whenever the validation path lives in the same subsystem as the object being accessed. In that sense, the vulnerability can improve code review discipline well beyond the specific SCSI target path.
Another concern is backport drift. Even when the fix is simple in mainline, vendor trees often need compatibility adjustments, and those adjustments can delay rollout. Since the CVE record was still awaiting NVD enrichment at publication time, some organizations may not get immediate severity guidance and could undervalue the patch.
A second thing to watch is whether this fix prompts broader review of configfs store methods in other subsystems. Bugs like this often reveal a ther than an isolated mistake. If one subsystem validated a path by reopening it under lock, it would not be surprising to find nearby code with similar assumptions.
CVE-2026-23292 is therefore best read as a reminder that the most dangerous bugs in mature kernels are often not dramatic ones. They are the ones that violate a subsystem’s own assumptions, especially when control paths, locking, and filesystem semantics collide. The fix is already clear, the diagnosis is clean, and the broader takeaway is durable: in kernel space, how you validate a path can matter just as much as whether the path is valid.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
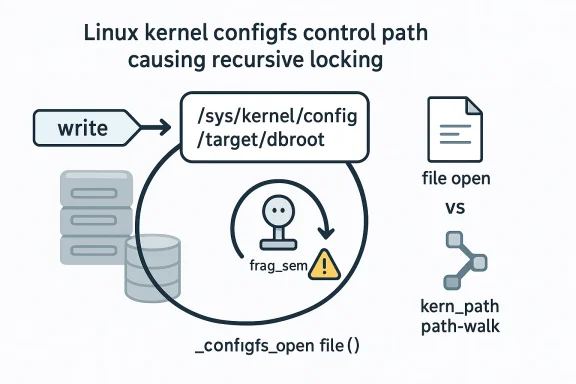
__configfs_open_file(), where target_core_item_dbroot_store() could end up reopening a configfs path while already holding frag_sem, creating a self-referential lock acquisition path and a risk of deadlock-style behavior. The upstream description says the fix replaces the path validation logic with kern_path() instead of filp_open(), specifically to avoid triggering __configfs_open_file() again when the target is already the same configfs object under write context first glance, CVE-2026-23292 appears to be a filesystem oddity, but it is better understood as a locking discipline failure inside the Linux kernel’s configfs and SCSI target code. Configfs is not a normal user-facing filesystem in the desktop sense; it is a kernel configuration interface where writes often translate directly into subsystem state changes. That means the code paths are expected to be extremely careful about reentrancy, semaphores, and object lifetime.The vulnerability description shows the failure path clearly:
flush_write_buffer() acquires &p->frag_sem, then calls a store method, which in this case is target_core_item_dbroot_store(). That store method attempts to validate a new file path by opening it, but the reported failure case shows the path was already the same configfs entry, /sys/kernel/config/target/dbroot, meaning the code was trying to open a file it was actively servicing. The resulting call chain loops back through __configfs_open_file() and related VFS helpers, making the lock acquisition effectively recursive .This kind of bug iernel semaphores are not just synchronization primitives; they are also enforcement boundaries for correctness. If the code holds one while calling into a function that may try to reacquire it, the behavior may range from lock contention to a hard deadlock, depending on the exact path and scheduling conditions. In kernel space, even “just” a deadlock is serious because it can stall I/O, freeze control paths, or cascade into broader system instability.
The fix is conceptually simple but technically important: switch the validation mechanism from filesystem-opening semantics to a lower-level pathname resolution call. By using
kern_path() rather than filp_open(), the kernel avoids re-entering the filesystem-specific open logic that is tied to configfs internals. That design choice matters because it preserves the intent of path validation without invoking the very machinery that caused the lock recursion in the first place .The CVE landed on March 25, 2026, and Ning enrichment, which is a reminder that the security ecosystem often learns about kernel bugs faster than it can fully score them. The practical lesson is that the absence of a CVSS score does not mean the issue is trivial; it often means the upstream fix is known, but the broader downstream analysis has not yet finished.
 What Actually Broke
What Actually Broke
The core failure is not a buffer overflow, memory leak, or a use-after-free. It is a lock recursion hazard caused by the store method using a function that can re-enter configfs’s open path while the write path already holds a semaphore. That is a particularly nasty kind of bug because it usually appears only when the code tries to validate or inspect a path that points back into the same configfs subtree.The report’s clue is the message
db_root: not a directory: /sys/kernel/config/target/dbroot. That line tells us the code tried to interpret the very configfs entry it was manipulating as a file path to be opened. In other words, the validation logic crossed the boundary from “check whether this path exists” to “open this path as though it were a normal file,” which dragged it back through configfs’s own open machinery .Why recursive locking is so dangerous
Recursive lockinginsidious in kernel code because they often look harmless in testing until a specific path is hit. Once the same lock is taken twice by the same execution path, the kernel can wedge the thread, stall dependent work, or trigger watchdog symptoms if the lock is held long enough.- It can block progress in unrelated threads waiting on the same semaphore.
- It can turn a path-validation routine into a system-wide stall.
- It can be hard to reproduce unless a caller feeds the subsystem its own configfs path.
- It often escapes unit testing because the trigger is a behavioral edge case, not an input parsing mistake.
The upstream fix changes
target_core_item_dbroot_store() so that it validates the path using a kernel path lookup that does not invoke the open path in the same way. That is a narrow fix, but narrow is good here: it solves the reentrancy problem without redesigning configfs or the SCSI target interface .Why the lock path mattered
The key detail is the semaphore&p->frag_sem. Ince, flush_write_buffer() has already acquired it before the store callback runs. If that callback then calls filp_open(), the file open can come back through __configfs_open_file() and attempt to re-enter the same state machine. That is the exact pattern kernel maintainers try to eliminate in subsystem code: open-like behavior inside a write callback, especially when the target object is itself part of configfs.Why Configfs Bugs Are Special
Configfs is unlike many other virtual filesystems because it is not just a place to read and write metadata; it is a control plane for kernel objects. That means a write can instantiate, reconfigure, or validate live subsystem state. Once you accept that model, it becomes clear why lock ordering is so important.A normal filesystem path open may be routine, but in configfs, open and write are often tightly coupled with object state. If the code tries to open an object while holding the write-side semaphore for that same object, the system can end up with a lock cycle even without any malicious intent. That makes “safe enough” patterns from ordinary file I/O potentially unsafe in configfs.
The configfs contract
The code path shown in the CVE description suggests the contract is simple but strict: a store method should process input and update state, not accidentally re-enter the same interface. When it needs to validate a pathname, it should do so with the least invasive mechanism possible.That is exactly why
kern_path() is the right kind of fix. It resolves a path without participating in the file-open semantics that can trigger configfs-specific callbacks. In kernel terms, this is a contain the blast radius fix.- Avoid recursive entry into configfs handlers.
- Preserve the write path’s lock ownership.
- Validate paths without fully opening them.
- Reduce the chance of lock inversion or semaphore self-deadlock.
The SCSI Target Angle
The affected code lives in the SCSI target subsystem, which is responsible for presenting storage targets from the kernel side. That makes this vulnerability more than a generic configfs concern. Storage targets are the kind of kernel feature that enterprise environments rely on for virtualization, test harnesses, and network-attached storage use cases.The specific function mentioned,
target_core_item_dbroot_store(), suggests the code is managing a database root or backing storage path for target configuration. In that context, path validation is a necessary step, but it must not be done in a way that loops back through the same virtual filesystem plumbing. The bug is therefore a good example of how storage management paths can fail when validation logic is written too literally.Why storage subsystems feel this first
Storage code is often where locking mistakes become visible because the operations are deeply layered. A configuration write can touch:- configfs state,
- VFS path resolution,
- target subsystem state,
- and downstream I/O logic.
Enterprise administrators should care because storage paths are frequently configured during boot, provisioning, or automation. A stuck control path in target setup can delay deployment, interfere with recovery workflows, or cause management tooling to hang at exactly the wrong time.
How the Fix Works
The fix is elegant in the best kernel sense: it changes the mechanism without changing the goal. Instead of usingfilp_open() to validate a path, target_core_item_dbroot_store() is modified to use kern_path(), which keeps the resolution in path-walk territory instead of full file-open territory .That matters because
filp_open() can invoke filesystem-specific open handlers, including configfs’s ntrast, kern_path() is designed for kernel-side pathname resolution and avoids the same kind of object open lifecycle that caused the recursive lock interaction.What the patch is really doing
The patch is not merely replacing one helper with another. It is changing the trust boundary around path validation.- The store function receives input from configfs.
- It needs to confirm the path is valid.
- It now resolves that path without opening it through the same filesystem machinery.
- The write path keeps its lock discipline intact.
- The recursive path back into
__configfs_open_file()is avoided.
Why compatibility mattered
The description notes that the fix was further modified “to make this fix compatible.” That usually means the patch had to be adjusted so it would work across kernel contexts, API expectations, or stable backport constraints. That is common in Linux security work: the ideal fix in mainline often needs a second pass before it can be safely applied to supported branches.In practical terms, the compatibility work matters because kernel fixes are only useful if they can land in real vendor trees. A pristine upstream patch that is impossible to backport is less helpful to users than a slightly more constrained solution that distributors can ship quickly.
- Lower risk of configfs reentrancy.
- More predictable validation behavior.
- Better fit for stable branch backports.
- Reduced chance of side effects in SCSI target configuration.
What This Means for Linux Operators
For most desktop users, this CVE is invisible. For administrators of systems that use Linux SCSI target functionality or configfs-driven storage configuration, it is a real patch item. The impact is not likely to be remote code execution or privilege escalation; it is more about availability and kernel correctness under specific configuration operations.That distinction matters because many vulnerability management programs still over-index on exploitability headlines. This bug is more operational than theatrical. If it triggers, the result is more likely to be a hung configuration operation, a blocked storage-management task, or in the worst case a broader kernel stall affecting dependent work.
Where the risk is highest
The practical exposure is greatest in environments that:- expose SCSI target configuration through configfs,
- automate storage target provisioning,
- use scripts that manipulate
/sys/kernel/config/target/, - or have management tooling that validates paths dynamically.
What administrators should verify
Administrators should not stop at the CVE number. They should confirm whether their kernel build includes the upstream fix or an equivalent vendor backport. Since the NVD entry was still awaiting enrichment, the best immediate signal is the presence of the underlying kernel patch in the shipped kernel version or vendor advisory stream .A practical checklist:
- Confirm whether your kernel branch contains the
kern_path()change. - Audit whether SCSI targetproduction.
- Check for vendor backport notes rather than version numbers alone.
- Test storage-management scripts after patching.
- Watch for hangs around target configuration or dbroot validation.
Why This Is Not “Just a Deadlock Bug”
It is tempting to dismiss recursive locking as an old-fashioned stability issue rather than a security concern. That would be a mistake. In kernel space, reliable control paths are part of the security posture because a failure in one management path can affect availability, state integrity, and recovery behavior.A deadlock in a storage-control interface can prevent a system from being configured, remediated, or recovered. If the affected path is used during deployment or automation, the impact compounds quickly. For this reason, Linux kernel security disclosures routinely include fixes that are about concurrency correctness rather than attacker-controlled memory corruption.
Security significance in practice
The importance of this CVE lies in the fact that it affects a privileged kernel path that can be exercised by legitimate administrative activity. That means it may be reachable in environments where operators are least expecting trouble: during setup, change management, or automated target provisioning.- Kernel locking bugs can cause denial of service.
- Configuration paths often run with elevated trust.
- Recursive entry bugs are difficult to diagnose after the fact.
- A bug in management plumbing can have fleet-wide consequences.
Strengths and Opportunities
The biggest strength of this fix is its precision. Rather than broadening locking or refactoring configfs, the patch changes the path validation method so it no longer re-enters the same open path. That keeps the fix focused and reduces the chance of collateral regressions. It also makes the issue easier for downstream maintainers to reason about when backporting.This CVE also highlights an opportunity for kernel teams to audit similar store callbacks that validate paths by opening them. The pattern is dangerous whenever the validation path lives in the same subsystem as the object being accessed. In that sense, the vulnerability can improve code review discipline well beyond the specific SCSI target path.
- Targeted remediation instead of broad serialization.
- Lower reentrancy risk in configfs-backed control paths.
- Better backportability for stable kernels.
- Cleaner mental model for path validation code.
- Useful audit signal for nearby configfs store methods.
- Reduced chance of management-path hangs in storage automation.
- Improved subsystem robustness without altering user-visible behavior.
Risks and Concerns
The primary concern is that this is exactly the sort of bug that can sit quietly until a production administrator or automation system trips it. Because the trigger is path validation involving the same configfs object, many test environments may never see it. That creates a false sense of safety, especially for teams that rely on routine validation scripts rather than adversarial testing.Another concern is backport drift. Even when the fix is simple in mainline, vendor trees often need compatibility adjustments, and those adjustments can delay rollout. Since the CVE record was still awaiting NVD enrichment at publication time, some organizations may not get immediate severity guidance and could undervalue the patch.
- Rare trigger conditions can delay discovery.
- Vendor backports may lag behind upstream.
- Management tools may unknowingly exercise the bug.
- Recursive lock behavior can be hard to reproduce consistently.
- A hang in a storage-control path can disrupt recovery workflows.
- Similar patterns may exist in adjacent configfs callbacks.
- Partial patch adoption can create mixed-kernel fleets with uneven exposure.
Looking Ahead
The next thing to watch is how quickly downstream Linux vendors absorb thekern_path()-based fix into stable kernels and enterprise distributions. In practice, that will matter more than the CVE label itself. For administrators, what counts is whether the kernel currently in service still uses the old filp_open() validation path inside target_core_item_dbroot_store() .A second thing to watch is whether this fix prompts broader review of configfs store methods in other subsystems. Bugs like this often reveal a ther than an isolated mistake. If one subsystem validated a path by reopening it under lock, it would not be surprising to find nearby code with similar assumptions.
Practical watch list
- Stable and vendor kernel backports.
- Distribution advisories mapping fixed builds.
- Any follow-on configfs locking fixes.
- Reports of hangs during target/dbroot setup.
- Audit findings in storage automation tooling.
CVE-2026-23292 is therefore best read as a reminder that the most dangerous bugs in mature kernels are often not dramatic ones. They are the ones that violate a subsystem’s own assumptions, especially when control paths, locking, and filesystem semantics collide. The fix is already clear, the diagnosis is clean, and the broader takeaway is durable: in kernel space, how you validate a path can matter just as much as whether the path is valid.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center