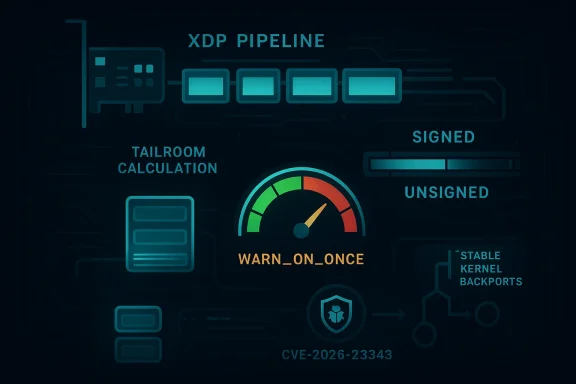
The Linux networking stack is getting a small but important hardening fix that matters well beyond its one-line title. Microsoft has cataloged the issue as CVE-2026-23343, and the underlying upstream change is a Linux XDP patch that now warns when a calculated tailroom goes negative instead of letting the bad value silently cascade into memory corruption or undefined behavior. In practical terms, this is the kind of bug that can turn an edge-case packet layout into instability in high-performance networking paths, especially in XDP and AF_XDP deployments that rely on tightly packed buffers. The fix has already moved into stable kernel streams, which is a strong signal that maintainers view it as a real production problem rather than a cosmetic cleanup.
XDP, or eXpress Data Path, is Linux’s fast path for packet processing. It sits close to the NIC driver layer, where performance is measured in microseconds and correctness depends on exact buffer accounting. That makes it a powerful tool for packet filtering, load balancing, and user-space networking, but it also means that a small arithmetic mismatch can have outsized consequences. The kernel documentation for XDP and AF_XDP shows how much the model depends on precise metadata, buffer size assumptions, and careful transitions between XDP frames and the networking stack.
The CVE-2026-23343 issue centers on that accounting boundary. The upstream patch explains that many Ethernet drivers report XDP receive-queue fragment size as if it were the DMA write size, while the only consumer of the field,
What makes the bug particularly notable is that the fix is not merely a bounds check. The patch changes the tailroom variable to a signed integer and adds a
Microsoft’s decision to assign a CVE also reflects a broader reality: modern kernel vulnerabilities are often published through enterprise-facing security channels even when the root cause lives upstream in Linux. That matters because many organizations will first see the issue through their Microsoft security tooling or vulnerability dashboards, not through kernel mailing lists. It is a reminder that Linux kernel maintenance and enterprise patch management are now tightly connected, even when the affected code is entirely open source.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
XDP, or eXpress Data Path, is Linux’s fast path for packet processing. It sits close to the NIC driver layer, where performance is measured in microseconds and correctness depends on exact buffer accounting. That makes it a powerful tool for packet filtering, load balancing, and user-space networking, but it also means that a small arithmetic mismatch can have outsized consequences. The kernel documentation for XDP and AF_XDP shows how much the model depends on precise metadata, buffer size assumptions, and careful transitions between XDP frames and the networking stack.The CVE-2026-23343 issue centers on that accounting boundary. The upstream patch explains that many Ethernet drivers report XDP receive-queue fragment size as if it were the DMA write size, while the only consumer of the field,
bpf_xdp_frags_increase_tail(), actually expects a truesize-like value. When that mismatch occurs, the calculated tailroom can go negative, and an unsigned representation can misreport it as a huge positive value instead of failing cleanly. That is exactly the kind of subtle arithmetic bug that kernel maintainers spend years eliminating because it is both easy to overlook and hard to diagnose once deployed.What makes the bug particularly notable is that the fix is not merely a bounds check. The patch changes the tailroom variable to a signed integer and adds a
WARN_ON_ONCE(tailroom < 0) guard so the kernel can flag the bad condition in development and test environments. That tells us the maintainers are treating this as a correctness problem with security implications, not just a driver quirk. In kernel networking, a warning often means the code has found a place where a bad assumption can be turned into an operational fault.Microsoft’s decision to assign a CVE also reflects a broader reality: modern kernel vulnerabilities are often published through enterprise-facing security channels even when the root cause lives upstream in Linux. That matters because many organizations will first see the issue through their Microsoft security tooling or vulnerability dashboards, not through kernel mailing lists. It is a reminder that Linux kernel maintenance and enterprise patch management are now tightly connected, even when the affected code is entirely open source.
Overview
At a high level, the patch addresses a negative tailroom calculation in the XDP frags path. The upstream report notes that this can occur when the fragment size reported by a driver does not match the assumptions in the tail-adjustment code, especially in multi-buffer cases. In the cited example, ixgbevf’s maximum DMA write size of 3 KB can produce a problematic mismatch during anXDP_ADJUST_TAIL_GROW_MULTI_BUFF test, where the kernel ends up reasoning about space as if there were more usable room than there actually is.Why the bug matters
This is not the sort of issue that looks dramatic on its face. There is no obvious “execute arbitrary code” headline in the patch itself, and the upstream wording is intentionally conservative. But kernel bugs that convert a negative arithmetic result into a huge positive number are a classic source of silent corruption, because later code can act on a value that is simply wrong. That wrong value may not crash immediately; instead, it can destabilize packet handling, trigger odd call traces, or manifest as intermittent memory corruption.Why signedness is central
The patch’s change fromunsigned int to int is the real heart of the fix. In C, signedness is not a style choice; it determines whether a negative result is preserved as an error or turned into a misleadingly large positive integer. In this case, the maintainers explicitly wanted the kernel to recognize “negative tailroom” as invalid and stop pretending there is usable space. That is an important distinction because it prevents bad arithmetic from becoming bad control flow.What “warning” means here
The new warning is both a diagnostic and a guardrail. It signals to developers, distro maintainers, and driver authors that the assumptions in the frags path are wrong for at least some device configurations. In other words, the patch is not just trying to prevent a crash; it is trying to surface a class of driver mismatches before they spread into production systems. That is why the stable backport matters so much.- The bug is in the XDP frags tail-growth path.
- The trigger is a mismatch between reported fragment size and actual truesize expectations.
- Negative tailroom was previously vulnerable to unsigned wraparound.
- The fix uses a signed variable and a warning to catch invalid state.
- Stable kernel branches have already picked up the patch.
How the XDP Frags Path Works
The XDP frags path is one of those kernel features that looks straightforward until you trace all the assumptions. Packets may be split across fragments, and the code that grows or adjusts the tail must know exactly how much writable room remains in the last fragment. If the kernel thinks there is room when there is not, later operations can overrun boundaries or corrupt metadata. The documentation around XDP metadata and AF_XDP shows how tightly these pieces are coupled.Tailroom versus truesize
The upstream report makes a subtle but important observation: driver-reportedfrag_size was being treated like the space the code should rely on, but the consumer expected something closer to a true allocation size. That difference matters because actual usable space depends on page offset and buffer layout, not just the nominal DMA write capacity. Once those values diverge, the tailroom calculation can go negative even though the surrounding code still assumes a normal packet shape.Why multi-buffer makes it worse
Multi-buffer packets amplify accounting mistakes because the last fragment often carries the least slack. A single off-by-assumption can push the calculation over the edge, especially when a 6 KB packet is spread across two DMA-writable buffers and the last one is already tightly packed. That is why the example in the stable patch discussesXDP_ADJUST_TAIL_GROW_MULTI_BUFF; the bug is easiest to reproduce in precisely those cases where the system is doing the most sophisticated buffer choreography.The risk of unsigned wraparound
Unsigned wraparound is one of those bugs that can look harmless in code review and disastrous at runtime. If a negative value becomesUINT_MAX-like territory, the kernel can think it has abundant tailroom and proceed with an adjustment it should have rejected. The patch prevents that by making the intermediate value signed and warning as soon as the calculation goes below zero.- Buffer layouts in XDP depend on precise fragment accounting.
- A driver can be “correct” locally but still incompatible with the consumer’s expectations.
- Multi-buffer traffic increases the chance of edge-case failures.
- Signedness bugs are especially dangerous in low-level C code.
- The warning helps convert a hidden fault into a visible one.
Patch Timeline and Upstream Path
The upstream trail is fairly clear. The patch first appeared in the netdev and bpf mailing list discussion in early February 2026, then evolved through review iterations, and by March it was already entering stable backports for multiple kernel branches. That progression is important because it shows the bug moved through normal maintenance channels quickly, which usually means the maintainers believed the issue was concrete and reproducible.From review to stable
The stable listings are especially revealing. They show the same fix landing in 6.19, 6.18, and 6.12 stable streams, which is exactly what you would expect for a patch that affects widely deployed networking code. Stable inclusion does not automatically mean the issue is remotely exploitable, but it does mean the kernel community considers it important enough to backport across supported lines.Why backports matter more than upstream elegance
For enterprises, the upstream patch is only half the story. What matters operationally is whether distributions can apply the fix to the kernels actually running in production. Stable backports are how a fix stops being an interesting kernel discussion and becomes a practical remediation item in patch cycles, maintenance windows, and OEM release trains.The role of the Fixes tag
The patch references the original frags-support change with aFixes: tag, which helps maintainers identify the exact code path that introduced the bug. That is useful not only for bisecting but also for deciding how far back to backport the correction. In kernel maintenance, that kind of metadata can determine whether a patch is a quick cherry-pick or a complicated branch-specific repair.- Early February 2026: the patch appears in mailing list review.
- Mid-March 2026: stable branches start carrying it.
- Multiple supported kernel lines receive the fix.
- The
Fixes:tag anchors the change to the frags-support API introduction. - Backport readiness suggests maintainers saw a real production risk.
Enterprise Impact
Enterprise users are the audience most likely to care about this CVE even if the practical trigger is niche. XDP is not usually deployed on casual desktop systems; it is used in high-throughput networking environments, appliances, edge systems, and performance-sensitive infrastructure where packet handling is intentionally pushed close to the hardware. In those settings, a malformed or misaccounted packet path can become a reliability issue that spreads quickly across fleets.Operational reliability versus exploitability
This kind of kernel bug does not need to be a textbook remote-code-execution flaw to be serious. A warning that surfaces in a hot path, or a corruption bug that appears under specific traffic patterns, can still cause outages, kernel noise, packet drops, or service degradation. In enterprise environments, stability bugs are often security bugs by another name because they create the conditions for outages, misrouting, and emergency rollbacks.Driver diversity complicates remediation
The patch discussion specifically notes that the issue can be fixed in in-tree drivers, but out-of-tree drivers cannot simply be trusted to behave correctly. That matters because enterprise fleets often include vendor kernels, custom NIC drivers, appliance images, and hardware enablement stacks that lag mainline changes. A fix in the core kernel reduces risk, but it does not automatically eliminate driver-side mismatch.AF_XDP and user-space networking exposure
AF_XDP deployments deserve special attention because they are often chosen precisely for low-latency packet processing. Any bug in the frags or metadata path can create hard-to-debug performance regressions that look like network instability from the outside. In a tightly engineered packet-processing stack, one invalid tailroom calculation can ripple through queue behavior, test harnesses, and observability systems.- High-throughput environments are the most likely to hit the bug.
- Vendor kernels may need separate validation beyond upstream fixes.
- User-space networking stacks can be sensitive to subtle packet accounting errors.
- The impact may appear as instability before it appears as a clear crash.
- Out-of-tree driver variance increases operational complexity.
Competitive and Ecosystem Implications
The broader market implication is that XDP’s performance gains continue to come with an engineering tax. The more aggressively vendors optimize packet paths, the more they rely on exact agreement between hardware, drivers, and kernel assumptions. That creates a competitive tension: faster fast paths are attractive, but they also demand a stricter maintenance discipline than ordinary networking code.What it means for NIC vendors
NIC vendors and driver maintainers now have another reminder that fragment-size semantics cannot be treated casually. If a driver reports a size that is technically accurate for one purpose but wrong for another, the burden shifts to the kernel to defend itself. That is not ideal engineering, but it is the reality of a heterogeneous driver ecosystem where not every implementation aligns perfectly.What it means for Linux distributions
Distributions will likely view this as a routine but important networking fix, not a marquee exploit disclosure. Still, kernel teams have to decide how quickly to push the stable backport into supported releases, especially for enterprise and real-time builds where XDP usage is more common. The fact that the patch is already in stable review reduces ambiguity, which is usually welcome in distro security operations.What it means for users of XDP tooling
Users running XDP selftests,xskxceiver, or other packet-path validation tools may see this as a correctness fix that stabilizes behavior under edge conditions. The upstream report uses XDP_ADJUST_TAIL_GROW_MULTI_BUFF as the illustrative trigger, which suggests the problem can be exercised in test and benchmarking environments without exotic hardware conditions. That makes the fix useful not just for security posture, but for making test outcomes more trustworthy.- NIC vendors need tighter agreement on fragment semantics.
- Distributions can use stable backports to reduce exposure quickly.
- XDP testing tools benefit from more deterministic accounting behavior.
- The bug underscores the cost of heterogeneous driver ecosystems.
- Performance features still require conservative safety checks.
Technical Root Cause in Plain English
The simplest way to explain the flaw is this: the kernel was calculating “how much room is left at the tail of this buffer” using values that could go negative, but the code path did not treat that negative result as an error soon enough. Because the value was previously unsigned, the bad result could masquerade as a very large positive number, which is the exact opposite of what a validation path should do.Why this is more than a cosmetic bug
Once a bad value is accepted, downstream logic starts making decisions on false premises. In networking code, that can mean attempting to grow a tail, reading or writing beyond intended boundaries, or taking a branch that only makes sense when the buffer is valid. Even when the immediate symptom is “just” a warning, the real issue is that the kernel has already crossed a line it should have rejected.Why the warning is the right engineering move
Some bugs should be silently corrected; this is not one of them. A warning is useful because it exposes a broken assumption without hiding the fact that the underlying data path is still wrong. That gives kernel developers and driver authors a chance to find the bad combination in testing rather than discovering it later in production under packet load.Why the issue was likely hard to spot
The patch discussion suggests the bad condition depends on a specific combination of driver-reported size, page offset, and multi-buffer geometry. Those are exactly the kinds of conditions that normal functional tests may never hit, especially if they rely on standard MTU-sized frames rather than carefully constructed boundary cases. In kernel networking, the bugs that survive longest are often the ones that only appear when several “reasonable” assumptions fail at once.- Negative arithmetic in kernel code is a red flag, not a corner case.
- Unsigned types can hide invalid state by wrapping it into a large value.
- Warnings help make the failure visible during development and QA.
- Multi-condition bugs are notoriously hard to reproduce casually.
- The fix improves both safety and diagnosability.
Strengths and Opportunities
The good news is that the fix is narrow, well-motivated, and already spreading through maintained kernel branches. It also improves observability, which is often as valuable as the immediate code change itself in a subsystem as intricate as XDP. Just as importantly, it gives driver authors a clearer contract for how fragment accounting is supposed to work.- The patch is small and low-risk in code scope.
- Signed arithmetic prevents hidden wraparound.
- The warning improves diagnostics for developers and vendors.
- Stable backports are already underway.
- The fix clarifies the contract between drivers and XDP core code.
- Test tools can now catch the invalid condition more reliably.
- The change hardens a high-value fast path without redesigning it.
Risks and Concerns
The biggest concern is not that the patch fails to fix the immediate problem, but that the bug reveals how much trust the XDP path still places in driver-reported sizing assumptions. Any out-of-tree or vendor-specific driver that gets this wrong could continue to produce fragile behavior even after the core kernel change lands. That means administrators should think in terms of validation, not just patch installation.- Out-of-tree drivers may still carry incompatible assumptions.
- Some enterprise kernels may lag the stable fix.
- The bug could surface as instability rather than a clean failure.
- Testing may miss the condition unless it exercises boundary cases.
- A warning is helpful, but it does not magically fix vendor driver logic.
- Multi-buffer packet paths remain complex and easy to misconfigure.
- Silent corruption risk is the main reason this should not be ignored.
Looking Ahead
The next phase is likely to be mostly about propagation and validation. Kernel maintainers have already done the hard part by identifying the bad arithmetic, converting the type, and adding the warning, but the real-world question is how quickly distribution kernels and OEM images absorb the change. In high-performance networking environments, a bug like this tends to show up in the field only when traffic patterns are unusual enough to reach the edge of the buffer model.What to watch next
- Whether downstream vendors backport the fix into enterprise and cloud kernels.
- Whether additional XDP drivers are audited for similar fragment-size assumptions.
- Whether the warning triggers new selftest coverage or regression tests.
- Whether any distro advisories frame the issue as reliability, security, or both.
- Whether out-of-tree NIC drivers need follow-up fixes of their own.
Source: MSRC Security Update Guide - Microsoft Security Response Center
Last edited: