The Linux kernel’s CVE-2026-23359 is a classic example of how a small-looking bounds mistake in BPF devmap code can turn into a real memory-safety problem. The issue sits in
The NVD description for CVE-2026-23359 says the vulnerable code was fixed in the Linux kernel after maintainers discovered that
That distinction mabugs are often born in the gaps between abstractions. A helper like
The reproduction guidance included in the advisory makes the attack surface concrete. If an administrator creates more than
The kern is full of places where array sizing by convention can go wrong. Developers often start with a best guess, then later discover that topology, stacking, or feature growth has outpaced the guess. Here, the problem was amplified by the fact that the allocation itself lived on the stack, which raises the stakes for any overflow.
The bug is therefore not merely “too many devices exist.” The deeper issue is thatd a policy constant as if it were a hard architectural limit. Those are not the same thing. A constant like
The kernel fix works by making the helper aware of the caller’s limit. Once
The documented trigger requires an attached XDP program using
The scenario here is especially interesting because the exploitability is tied to a topology that many ordinary systems will never create. That lowers broad consumer exposure, but it does not make the issue trivial. In enterprise, telco, test-lab, and cloud-hosting contexts, complex interface stacks are common, and that is where bugs like this become operationally meaningful.
This approach is preferable to “just make the array bigger” because the larger issue is not buffer size alone. If the topology can be deeper than the helper expected, then any hardcoded sally brittle unless the helper is constrained. A bigger buffer might postpone the problem, but it would not solve the architectural mismatch.
Why
Returning
This is also a good example of fail closed behavior. In networking security, silently proceeding after a violated invariant is usually the worst option. A redirect that cannot safely enumerate all upper devices should not guess. It should stop.
The packet trigger also matters. You do not need a special payload or a malformed frame to reach the bug; you need ordinary traffic arriving at a sufficiently complex device hierarchy. That means the vulnerability lives in a normal control flow that becomes unsafe only when the structure above it becomes more complex than the code anticipated.
In operational terms, the most relevant question is not “Do we use XDP?” but “Do we stack enough virtual interfaces to exceed the helper’s assumption?” That makes inventory and topology review more important than feature-checking alone.
BPF and XDP make that tension sharper. These subsystems give operators enormous control over packet processing, but they also move more logic into the kernel fast path. The more flexible the topology, the more careful the kernel must be about counting, sizing, and validating. That is why bugs like this are so consequential even when they seem niche on paper.
This is also why stack allocation in networking code always deserves extra scrutiny. A stack buffer is fast, but it offers no forgiveness for count drift. Once the code exceeds the expected number of entries, the damage happens immediately and locally. In the kernel, that is enough to be serious.
The good news is that the remediation is straightforward from a deployment standpoint. This is not a redesign of network policy or a major user-space compatibility break. It is a kernel update problem, which means the fix should generally arrive through normal vendor or distribution patch channels. For many administrators, the real task will be identifying which hosts use the affected topology and making sure those systems pick up the patched kernel quickly.
Security teams should also remember that kernel vulnerabilities often have a disproportionate operational blast radius even when exploitation is not widely advertised. A stack out-of-bounds write may crash a host, destabilize a dataplane, or create a reliability event even if the bug is never weaponized.
The second thing to watch is whether the bug description prompts wider review of adjacent devmap or XDP paths. In kernel security, one checked-bounds fix often reveals nearby code that was relying on similar assumptions. When that happens, a single CVE can become the first sign of a broader audit wave in the subsystem.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
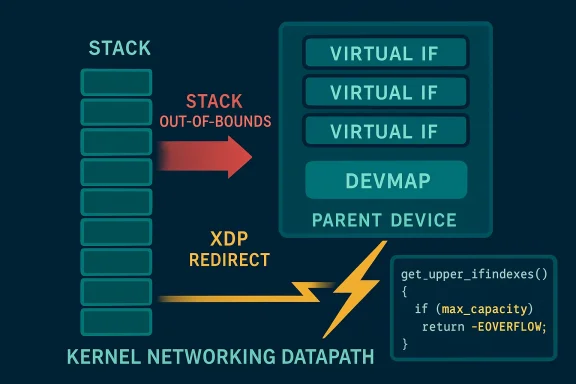
get_upper_ifindexes(), where the kernel walks every upper device and writes interface indices into an array without properly honoring the array’s capacity. In practice, that can become a stack-out-of-bounds write when a device has more upper devices than the code assumed, especially in configurations with many macvlan interfaces. The fix is surgical: add an explicit maximum parameter, stop once the caller’s buffer is full, and abort the redirect with -EOVERFLOW if the topology is larger than expected. based packet redirection has become one of the Linux networking stack’s most performance-sensitive paths, and devmap sits right in that fast lane. The helper infrastructure is designed to move packets quickly from one device to another, often in XDP contexts where every branch matters. That speed comes with a cost: kernel code in this area is often written under tight assumptions about object counts, device hierarchy, and stack allocation size. When one of those assumptions fails, the result is frequently not a graceful error but a memory corruption bug.The NVD description for CVE-2026-23359 says the vulnerable code was fixed in the Linux kernel after maintainers discovered that
get_upper_ifindexes() could write beyond the end of the excluded_devices stack array. The callers had assumed the maximum number of upper devices would fit within MAX_NEST_DEV, but the kernel’s actual topology rules do not guarantee that. In other words, the bug was not in the idea of tracking upper devices; it was in the mismatch between what the code expected and what the network stack could actually produce.That distinction mabugs are often born in the gaps between abstractions. A helper like
get_upper_ifindexes() looks simple: collect ifindexes, hand them back, and let a redirect routine decide whether to exclude ingress paths. But the Linux networking stack is layered, dynamic, and highly compositional. A device can sit beneath a surprising number of upper devices, and the code must defend against that reality rather than against a tidy diagram in a developer’s head.The reproduction guidance included in the advisory makes the attack surface concrete. If an administrator creates more than
MAX_NEST_DEV macvlans on a device with an XDP program attached using BPF_F_BROADCAST | BPF_F_EXCLUDE_INGRESS, then sends traffic to trigger the redirect path, the kernel can hit the bug. That is not a casual desktop scenario, but it is realistic in lab, appliance, container, or virtualization-heavy environments where macvlans and XDP are actively used.
 Why this bug class matters
Why this bug class matters
The kern is full of places where array sizing by convention can go wrong. Developers often start with a best guess, then later discover that topology, stacking, or feature growth has outpaced the guess. Here, the problem was amplified by the fact that the allocation itself lived on the stack, which raises the stakes for any overflow.- The issue affects a memory-safety boundary, not just logic correctness.
- The trigger path sits in XDP redirect, where performance optimizations can hide fragile assumptions.
- The bug becomes more plausible in high-density virtual networking setups.
- The fix does not redesign the subsystem; it simply makes the helper honor a caller-supplied maximum.
What the Vulnerability Actually Is
At the center ofhelper that walks the list of devices layered above the current interface and records their indices in an array. That sounds ordinary, but the kernel bug appears because the helper did not know how many slots the destination array really had. The callers allocatedexcluded_devices[1+MAX_NEST_DEV] on the stack and assumed that would be enough, but the number of upper devices can exceed MAX_NEST_DEV, especially when users stack multiple macvlans on a parent device.The bug is therefore not merely “too many devices exist.” The deeper issue is thatd a policy constant as if it were a hard architectural limit. Those are not the same thing. A constant like
MAX_NEST_DEV may express a common-case expectation, but it does not automatically define the maximum safe write count unless the code enforces it at every layer.Stack allocation is the dangerous part
The stack is fast, compact, and extremely unforgiving. When a helper writes past the end of a stack array, it can smash adjacent local variables, corrupt saved state, or create a crash that is hard to reproduce cleanly. Because this is inside a networking fast path, the overflow may also occur under load, which makes diagnosis even messier.The kernel fix works by making the helper aware of the caller’s limit. Once
get_upper_ifindexes() can stop at the right boundary, the redirect logic can detect the overflow case and bail out cleanly instead of writing garbage past the buffer. That is exactly the kind of change you want in low-level kernel code: small, targeted, and explicit.- The root cause is an unchecked write loop.
- The vulnerability depends on topology depth, nothe memory corruption target is stack memory.
- The kernel now treats excessive nesting as an error condition instead of a silent write.
How the Redirect Path Becomes a Risk
The vulnerable path is part of the XDP redirect flow in devmap, which is ost performance-oriented packet-processing paths. In practice, that means the code is optimized to do as little work as possible between packet arrival and forwarding. When code is built around speed, developers must be exceptionally careful about every assumption they place in helper functions and temporary arrays.The documented trigger requires an attached XDP program using
BPF_F_BROADCAST | BPF_F_EXCLUDE_INGRESS. That matters because it means the bug is tied not just to generic packet reception, but to a very specific feature combination where the redirect engine has to determine which upper devices should be excluded. The helper’s job is to enumerate those devices, and that enumeration is exactly where the bounds problem appears.Why feature combinations matter
Kernel vulnerabilities often live in combinations rather than in single features. One feature may be safe in or three features together create a path nobody fully bounded during code review. That is why modern Linux security work often focuses on intersection bugs: not “BPF,” not “macvlan,” not “devmap” alone, but the precise way they meet.The scenario here is especially interesting because the exploitability is tied to a topology that many ordinary systems will never create. That lowers broad consumer exposure, but it does not make the issue trivial. In enterprise, telco, test-lab, and cloud-hosting contexts, complex interface stacks are common, and that is where bugs like this become operationally meaningful.
- The trigger uses packet forwarding logic rather than a malformed packet payload.
- The relevant topology can be created intentionally in lab environments.
- The bug is most relevant where virtual networking density is high.
- The kernel’s fast path offers very little room for defensive overhead.
The Fix and Why It Is Good Kernel Hygiene
The upstream fix adds a maximum parameter toget_upper_ifindexes(), which turns an implicit assumption into That is a textbook kernel remediation pattern: instead of trying to prove the topology can never exceed a threshold, the code now enforces a threshold and returns an error when it is violated. In this case, that error is -EOVERFLOW, and the redirect path is aborted.This approach is preferable to “just make the array bigger” because the larger issue is not buffer size alone. If the topology can be deeper than the helper expected, then any hardcoded sally brittle unless the helper is constrained. A bigger buffer might postpone the problem, but it would not solve the architectural mismatch.
Why -EOVERFLOW is the right signal
Returning -EOVERFLOW communicates that the operation failed because the topology exceeded the available storage. That is a clean, semantically accurate failure mode. It prevents silent corruption, avoids misleading success states, and gives the caller a way to stop processing before the kernel writes beyond its bounds.This is also a good example of fail closed behavior. In networking security, silently proceeding after a violated invariant is usually the worst option. A redirect that cannot safely enumerate all upper devices should not guess. It should stop.
- The patch replaces an implicit limit with an explicit one.
- Excess nesting now produces a controlled failure.
- The fix preserves the fast path for normal cases.
- The change is narrow enough to be backportable without architectural churn.
Reproducibility and Real-World Exposure
The advisory’s reproduction recipe tells us quite a bit about practical risk. Creating more than eight macvlans on a device with an XDP program attached is nohome user is likely to do, but it is very plausible in test environments, networking appliances, container hosts, and automation-heavy setups. In those environments, interface stacking is routine and topology depth can grow quickly.The packet trigger also matters. You do not need a special payload or a malformed frame to reach the bug; you need ordinary traffic arriving at a sufficiently complex device hierarchy. That means the vulnerability lives in a normal control flow that becomes unsafe only when the structure above it becomes more complex than the code anticipated.
Practical exposure profile
For consumer desktops, the likely risk is low unless the system is being used in an unusually advanced networking role. For servers, lab systems, and cloud images that rely on macvlan or XDP-based ure is much more credible. That split is important: low prevalence does not equal low severity when the vulnerable code is in the kernel and the failure mode is memory corruption.In operational terms, the most relevant question is not “Do we use XDP?” but “Do we stack enough virtual interfaces to exceed the helper’s assumption?” That makes inventory and topology review more important than feature-checking alone.
- Consumer impact is probably limited.
- Enterprise and lab impact is more plausible.
- The bug is reachable through ordinary packet flow.
- Attackers with local topology control may have a path to trigger the overflow.
Why This Looks Like a Classic Linux Networking Bug
This CVE fits a familiar kernel pattern: a helper was written for a common-case limit, then real-world topology pushed past the limit, and the code failed to check bounds before writing to etworking is full of these tensions because it has to balance speed, flexibility, and compatibility across many kinds of devices.BPF and XDP make that tension sharper. These subsystems give operators enormous control over packet processing, but they also move more logic into the kernel fast path. The more flexible the topology, the more careful the kernel must be about counting, sizing, and validating. That is why bugs like this are so consequential even when they seem niche on paper.
Broader security lesson
The lesson here is not just “add a bounds check.” It is that kernel code should never assume a network topology can be deduced from a folklore limit. The actual topology must be measured, bounded, and handled as a live input. Anything less turns a performance optimization into a security liability.This is also why stack allocation in networking code always deserves extra scrutiny. A stack buffer is fast, but it offers no forgiveness for count drift. Once the code exceeds the expected number of entries, the damage happens immediately and locally. In the kernel, that is enough to be serious.
- The bug reflects a common kernel assumption failure.
- It shows how fast-path code can become fragile.
- It reinforces the importance of caller-controlled capacity.
- It highlights why topological complexity is a security issue.
Impact on Enterprise Deployments
Enterprise operators should think about this CVE through the lens of network density and kernel privileges. Systems that build complex interface stacks for containers, overlays, testing, or traffic steering are more likely to caoints. That is especially true where XDP is used for high-performance packet handling, because the vulnerable path sits inside a feature set typically chosen for precision and speed.The good news is that the remediation is straightforward from a deployment standpoint. This is not a redesign of network policy or a major user-space compatibility break. It is a kernel update problem, which means the fix should generally arrive through normal vendor or distribution patch channels. For many administrators, the real task will be identifying which hosts use the affected topology and making sure those systems pick up the patched kernel quickly.
Consumer versus enterprise priority
For consumers, the issue is probably more theoretical unless they are experimenting with advanced Linux networking. For enterprises, especially those using Linux hosts as infrastructure nodes, the issue belongs on the patch radar immediately. The key question is whether the affected systems are exposed to the exact BPF/XDP/multidevice combination described in the advisory.Security teams should also remember that kernel vulnerabilities often have a disproportionate operational blast radius even when exploitation is not widely advertised. A stack out-of-bounds write may crash a host, destabilize a dataplane, or create a reliability event even if the bug is never weaponized.
- Enterprise hosts with XDP-based forwarding deserve priority review.
- Container and virtualization stacks may be more exposed.
- Patch management should focus on kernel build lineage, not just distro branding.
- The fix is likely to be distributed through normal maintenance channels.
Strengths and Opportunities
The best thing about the fix for CVE-2026-23359 is that it is clean, comprehensible, and highly targeted. It addresses the precise bug without introducing broad behavior changes, which is exactly what you want in mature kernel networking code. It also gis a patch that is easy to reason about and backport.- Narrow fix scope reduces regression risk.
- Explicit bounds enforcement is easy to audit.
- The error path now fails safely instead of corrupting memory.
- The reproduction path is concrete, which helps validation.
- The fix preserves normal behavior for common topologies.
- The change aligns with good defensive kernel design.
- The vulnerability is now visible enough for vendors to prioritize.
Risks and Concerns
The main concern is that this is a kernel memory-safety issue in a networking path, which means the downside can range from a crash to deeper instability depending on how the overflow manifests. Even when a bug is difficult to trigger casually, kernel stack corruption is not somethinld shrug off. The other concern is exposure drift: as more systems adopt complex virtual networking, a bug that once seemed niche can become much more relevant.- Stack corruption can cause crashes or worse.
- Complex network topologies are increasingly common.
- Some vendor kernels may lag behind upstream fixes.
- The vulnerable path is performance-sensitive, so hidden assumptions are harder to spot.
- Reproduction may be limited in basic QA, allowing the bug to persist longer.
- Attackers with control over topology may be able to reach the bug more easily.
- The issue underscores how assumption bugs evade casual review.
Looking Ahead
The key question now is how quickly the patch propagates into stable Linux trees and downstream enterprise kernels. Because the vulnerability is rooted in a reusable helper and a clearly bounded memory-safety issue, it is the kind of fix that stable maintainers and distro security teams generally like to absold help shorten the exposure window for supported systems.The second thing to watch is whether the bug description prompts wider review of adjacent devmap or XDP paths. In kernel security, one checked-bounds fix often reveals nearby code that was relying on similar assumptions. When that happens, a single CVE can become the first sign of a broader audit wave in the subsystem.
- Watch for stable backports across supported kernel lines.
- Check whether your hosts use macvlan-heavy or stacked topologies.
- Verify kernel package updates from your distribution or vendor.
- Monitor whether adjacent devmap/XDP helpers receive hardening patches.
- Prioritize systems where XDP is used in production datapaths.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center