 CVE-2026-23364 in ksmbd: why a constant-time MAC comparison matters more than it sounds
CVE-2026-23364 in ksmbd: why a constant-time MAC comparison matters more than it sounds
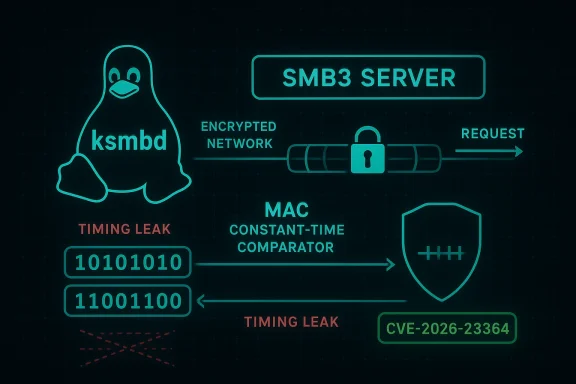
A new CVE-2026-23364 entry tied to ksmbd, the Linux kernel’s SMB3 server implementation, highlights a security property that can look minor at first glance but matters deeply in authentication code: comparing MACs in constant time. Microsoft’s Security Update Guide references the issue, and the broader ksmbd ecosystem has been seeing a steady stream of fixes in recent kernels and downstream distributions, underscoring how complex kernel-space SMB handling remains. Even when a flaw does not look like a classic crash or remote code execution bug, timing-sensitive comparison logic can still open the door to subtle authentication weaknesses. This is the kind of vulnerability that is easy to underestimate until you think through how SMB signing and request validation work under load.Overview
ksmbd is the in-kernel SMB3 server introduced to provide file-sharing services directly from Linux kernel space. That design gives it performance appeal, but it also places authentication, session handling, and request parsing in a highly privileged execution environment. The kernel documentation describes ksmbd as a dedicated SMB3 server with its own listener, work items, and support for SMB Direct and other enterprise features, which means bugs in this code path can have a broad blast radius.The specific wording associated with CVE-2026-23364 — “Compare MACs in constant time” — points to a hardening fix commonly used in cryptographic and authentication code. In plain English, constant-time comparison ensures that the time it takes to validate a message authentication code does not leak information about how much of the value matched. That sounds abstract, but it is exactly the sort of detail attackers exploit when they can repeatedly probe a service and observe tiny timing differences.
That matters because SMB signing is not decorative. It is part of the trust chain for requests entering the server, especially in environments where files, credentials, and domain-integrated workflows rely on SMB to keep traffic authenticated and tamper-resistant. A flawed comparison routine can become an oracle, and even if the exploitability is limited by network noise, limited is not the same as impossible. (ubuntu.com)
There is also an important ecosystem signal here. Recent Ubuntu security entries for ksmbd show multiple independent kernel fixes across 2025 and 2026, including problems involving request handling, locks, refcounts, and chained-message processing. The pattern suggests that ksmbd is maturing under real-world security pressure, and that downstream vendors are actively tracking kernel SMB issues rather than treating them as theoretical. (ubuntu.com)
Background
The Linux kernel has supported SMB client functionality for years, but ksmbd represented a more ambitious step: moving SMB server logic into the kernel rather than relying solely on user-space servers such as Samba. Kernel-space networking code can be fast and efficient, but every optimization creates pressure on correctness, isolation, and auditability. That tradeoff is especially sensitive in protocols like SMB, where authentication, signing, and message chaining all interact in complex ways.One reason constant-time comparison comes up in security reviews is that MACs, hashes, and signatures must be checked without revealing information through timing side channels. If the code exits early on the first mismatch, an attacker might infer how many leading bytes were correct and use that to iteratively recover a valid value. This is a classic defensive pattern in cryptography, but it remains easy to accidentally violate when developers prioritize performance or readability over side-channel resistance.
ksmbd has also faced a steady drumbeat of fixes that highlight the hazards of kernel request processing. Ubuntu’s CVE pages in 2026 show issues involving infinite loops in request handling, synchronization defects, use-after-free conditions, and refcount leaks. Taken together, these bugs suggest that the implementation is under continual hardening, which is not unusual for a relatively specialized kernel subsystem but is still a reminder that “in kernel” is not automatically “more secure.” (ubuntu.com)
Why SMB signing is a security boundary
SMB signing is more than a checkbox in enterprise deployment guides. It is a mechanism that protects messages from tampering and helps ensure that the server is validating requests from the intended peer. When the code that checks those values is weak, the security boundary becomes fuzzier, and attackers can start focusing on implementation details rather than the protocol design itself.Why timing side channels still matter
A lot of defenders assume timing attacks require lab-grade precision and local access. That is sometimes true, but not always. Networked services can still leak enough signal over repeated attempts, especially when the comparison routine is exercised in a hot authentication path and the attacker can average out noise over many probes. That is the uncomfortable part: you do not need a dramatic leak for an implementation weakness to be relevant.What the Vulnerability Signifies
The phrase “Compare MACs in constant time” suggests a code change focused on the method of comparison rather than a broad redesign of ksmbd. That is often a good sign, because it means the issue may be narrow and well-understood. It is also a warning sign, because narrow security flaws in authentication code can be precisely the kind that survive code review until a security researcher or downstream maintainer notices them.In practical terms, the fix is likely about eliminating early exits or data-dependent branching when validating a message authentication code. The kernel already documents the importance of careful low-level comparison routines, including how optimized equality checks can behave differently depending on architecture and memory access assumptions. That makes constant-time handling part of a broader discipline: not just “get the right answer,” but “get it in a way that does not leak useful hints.”
Security implications for attackers
If an attacker can distinguish valid from invalid MACs in a measurable way, they may gain a partial oracle for request forgery or signature guessing. In SMB, that could translate into attempts to tamper with session traffic, impersonate a client request, or force the server into revealing information about its validation process. This does not mean exploitation is guaranteed; it means the risk profile shifts from purely correctness-oriented to side-channel-aware.The most important takeaway is not that every constant-time flaw is catastrophic. It is that kernel authentication code should be built with the assumption that attackers will look for any difference in behavior, including timing, error messages, and retry handling. The fix embodied by this CVE reflects that mindset.
ksmbd in the Wider SMB Landscape
ksmbd exists alongside a long-established alternative: Samba in user space. That matters because enterprise buyers and Linux administrators now have a choice between a kernel-integrated SMB server and a mature user-space stack with a long security track record. The decision is not simply about raw performance; it is also about operational trust, patch cadence, feature completeness, and ecosystem familiarity.The kernel documentation shows that ksmbd is intended to support modern SMB3 features, including multi-channel and SMB Direct scenarios. Those capabilities are attractive in performance-sensitive environments, especially where low latency or high throughput matters. But every added feature increases the attack surface, and SMB is already a protocol family with a long history of complex state machines and interdependent security checks.
Enterprise vs. consumer impact
For most consumers, this CVE will be invisible unless they are running a Linux system configured as an SMB server. For enterprises, the situation is more consequential because ksmbd may appear in infrastructure roles, edge appliances, lab environments, or embedded deployments where Linux serves files directly. That means the issue belongs on the radar of administrators who treat SMB as a core service rather than a niche add-on.There is also a policy lesson here. When kernel subsystems start absorbing traditionally user-space services, the security team must think like both kernel developers and protocol implementers. Constant-time comparison is a textbook example of a protocol-level requirement that can be easy to mishandle when the implementation context changes.
What Downstream Vendors Tell Us
Ubuntu’s security record is useful here because it shows how downstream maintainers classify and communicate ksmbd issues. The CVE-2026-23220 entry, for example, describes an infinite loop caused by a reset in error paths, while other recent ksmbd CVEs track use-after-free bugs, race conditions, and refcount leaks. That is not directly the same as CVE-2026-23364, but it is strong context: ksmbd is an active security surface, not a dormant subsystem. (ubuntu.com)This pattern matters because vulnerability names often look isolated when viewed one at a time. In practice, they reveal a subsystem’s engineering maturity curve. The more often a subsystem handles authentication, concurrency, and request validation at once, the more likely it is to accumulate subtle bugs that are not obvious in unit tests or small-scale validation. (ubuntu.com)
Reading the signals carefully
A single CVE should not be overinterpreted as proof that a project is unsafe. But a cluster of related CVEs is meaningful, especially when they touch the same code paths or design decisions. In ksmbd’s case, the signal is not “panic,” but heightened diligence: patch quickly, test thoroughly, and monitor release notes closely. (ubuntu.com)The fact that the fix is framed as constant-time MAC comparison also suggests this is a security-review issue rather than a memory-corruption emergency. That distinction is important. It means risk may be lower than a remotely exploitable kernel crash, but it also means the bug reflects a security engineering gap that should not be dismissed.
Technical Interpretation
A constant-time comparison typically replaces a branchy equality check with logic that processes the full input regardless of where the first mismatch occurs. The goal is to keep execution behavior as uniform as possible, reducing the chance that an attacker can infer partial information from timing or cache effects. In security code, this is a well-established pattern, but one that must be applied consistently.In kernel code, the challenge is not just correctness but portability and compiler behavior. Low-level optimizations can be architecture-sensitive, and the Linux kernel documentation itself explains that seemingly simple comparison functions can have different implementation properties depending on access alignment and build configuration. That is why “constant-time” is often a deliberate design choice rather than something that happens automatically.
What this likely means in practice
The likely remediation path is straightforward conceptually: normalize the comparison logic so the code does not branch on the first mismatch. That sounds easy, but it often requires careful review to ensure the compiler does not undo the intended protections. It also requires test coverage that checks not only functional behavior but consistency under realistic execution paths.- The vulnerable area is likely in the SMB signing or request-verification path.
- The fix probably removes data-dependent behavior from MAC validation.
- The mitigation is as much about implementation discipline as it is about code cleanup.
- Constant-time handling is especially important when inputs are attacker-controlled.
- Security reviewers should verify that surrounding error paths remain uniform too.
Competitive and Market Implications
ksmbd is part of a broader conversation about whether Linux kernel services can replace or complement user-space daemons for enterprise protocols. If vulnerabilities continue to cluster around request handling and authentication, skeptics will use them as evidence that the kernel is the wrong place for SMB server logic. Supporters will counter that the performance and integration benefits are real, and that the answer is better hardening rather than abandonment.For rivals like Samba, the security implication is more nuanced. Samba’s user-space architecture gives it different operational properties, and many administrators trust it because of its maturity and long battle-testing. ksmbd does not need to “beat” Samba on every axis, but every fix like this one affects perceptions of whether the in-kernel model is ready for wider production adoption.
Enterprise procurement considerations
Procurement teams often evaluate more than features. They ask whether the project has stable maintenance, a predictable patch stream, and a low rate of security regressions. A constant-time MAC fix is the sort of issue that can either reassure buyers — because it shows the maintainers are taking subtle threats seriously — or worry them, because it reveals the code still needs security hardening in foundational paths.That tension is normal in infrastructure software. The market rarely punishes a project for having vulnerabilities; it punishes projects that appear slow to learn from them. In that sense, how quickly maintainers and downstream vendors adapt after CVE-2026-23364 may matter more than the flaw itself. (ubuntu.com)
Operational Impact for Administrators
Administrators running Linux as an SMB server should treat this as a routine but important patch-management item. The exact exposure depends on whether ksmbd is deployed, which kernel build is in use, and whether vendor backports have already folded in the fix. Because kernel CVEs are often handled through distribution updates rather than upstream source changes alone, checking vendor advisories is essential. (ubuntu.com)The practical burden is usually low: identify the affected package, apply the updated kernel, and schedule a reboot if the remediation is not live-patched. But the enterprise lesson is broader. SMB servers sit on the trust boundary between storage, identity, and endpoint access, so even “small” fixes can have outsized operational value.
Recommended admin response
- Confirm whether ksmbd is actually enabled on any production host.
- Check your distribution’s security advisory for the kernel package that includes the fix.
- Prioritize systems exposed to untrusted networks or broader internal client populations.
- Reboot hosts only after validating service windows and cluster dependencies.
- Review adjacent ksmbd CVEs so you do not patch one issue while leaving another unresolved. (ubuntu.com)
- Inventory servers that export SMB shares from Linux.
- Verify kernel version and vendor backport status.
- Confirm SMB signing and authentication settings.
- Coordinate updates with any high-availability failover design.
- Recheck logs after patching for authentication anomalies.
- Track whether multiple ksmbd fixes are being bundled together.
Strengths and Opportunities
This CVE also shows something positive: the security ecosystem around ksmbd is active, watching, and increasingly precise about subtle weaknesses. A constant-time MAC fix is not glamorous, but it is the kind of hardening that materially improves trust in the subsystem.- It addresses a classical side-channel concern rather than a vague best-practice issue.
- It reinforces security expectations for SMB signing and request verification.
- It shows downstream maintainers are tracking ksmbd closely.
- It may reduce attack surface in exposed SMB deployments.
- It nudges the codebase toward more disciplined cryptographic handling.
- It gives administrators a clear remediation target rather than a hand-wavy mitigation.
- It strengthens confidence that the subsystem is being reviewed beyond crash bugs.
Risks and Concerns
The most obvious concern is that timing-sensitive bugs are notoriously hard to reason about, test, and prove absent. Even when a fix is applied, reviewers must be confident that compilers, optimizations, and surrounding logic do not reintroduce the same leak through a different route. That is why these vulnerabilities often feel deceptively small.- Side-channel exposure may be subtle but still exploitable under repeated probes.
- Kernel-space authentication code leaves little room for mistakes.
- Different architectures can behave differently under low-level comparison logic.
- Security fixes may need to be backported across many vendor kernels.
- Administrators may miss the issue if they only track generic “high severity” advisories.
- Multiple ksmbd issues in a short time can erode trust in the subsystem.
- Feature pressure could tempt future regressions if performance wins are overvalued.
What to Watch Next
The next few weeks will tell us whether CVE-2026-23364 is treated as a narrow hardening patch or folded into a larger ksmbd maintenance wave. Watch vendor advisories, especially if your environment depends on kernel SMB services, because the true remediation path may arrive through your distribution rather than from upstream source code directly. The broader question is whether this fix becomes part of a larger narrative about ksmbd’s maturation or another data point in a pattern of incremental security repairs. (ubuntu.com)The most useful practical outcome would be a quieter security posture around SMB signing paths, with fewer surprises in authentication handling and clearer documentation for administrators. The least desirable outcome would be complacency: treating the CVE as “just timing” and failing to review adjacent code paths that compare secrets or handle signed request validation. Those are exactly the kinds of places where related bugs tend to cluster.
Watch list
- Distribution kernel advisories that mention ksmbd backports.
- Any follow-up CVEs touching SMB signing or session setup.
- Kernel release notes that describe additional constant-time or crypto-related cleanup.
- Enterprise guidance from vendors shipping Linux SMB services.
- Whether the fix is bundled with other ksmbd hardening patches. (ubuntu.com)
Source: MSRC Security Update Guide - Microsoft Security Response Center