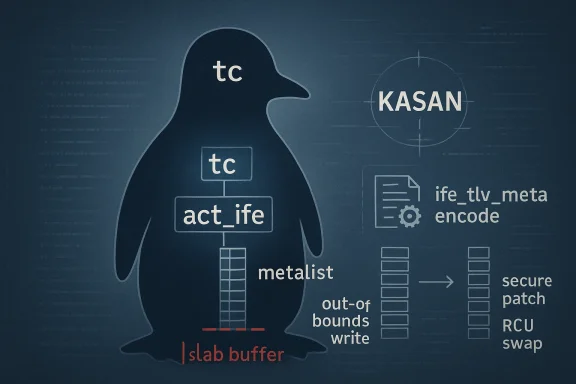
CVE-2026-23378 is a Linux kernel flaw in the act_ife traffic-control action that turns a seemingly routine metadata update into a memory-safety problem. The bug sits in the metalist handling path, where replacing an ife action could append new metadata instead of replacing the old entries, allowing the list to grow without bound and eventually tripping a slab-out-of-bounds write during encoding. The upstream report ties the issue directly to KASAN evidence in
The subsystem is one of those parts of the kernel that rarely gets attention until something goes wrong. It sits in the path between user configuration and packet processing, which means small bookkeeping errors can have outsized effects when they’re exercised at scale. The act_ife component is used to encode metadata into packets, so its correctness depends on careful alignment between stored metadata, list management, and runtime encoding rules.
The CVE description makes clear that theulative concern but a reproduced memory-safety fault. The bug trace shows a KASAN report in
What makes the vulnerability especially relevant is the way ie” behavior in the control plane rather than a packet parser in the data plane. In other words, the dangerous state can be created by reconfiguration, not necessarily by inbound traffic alone. That broadens the operational concern: any system that uses tc actions and updates ife metadata over time could, in principle, build up the corrupted state.
The fix landed through the normal kernel-stable pipeline, which is another signal idered it suitable for backporting rather than leaving it as a future-tree cleanup. The stable-thread version of the patch explicitly identifies the root cause and frames the fix as a repair to metalist update behavior, with the upstream commit credited to Jamal Hadi Salim.
At a high level, this is a classic kernel pattern: the code worked under the assumption that a configurld reset old state, but the implementation appended instead. That kind of bug is easy to underestimate because it doesn’t look dramatic until repeated updates push the list beyond the bounds the encoder expects. Once that boundary is crossed, the kernel’s memory model does the rest.
That behavior is especially bad in kernel code because list length is not just a cosmetic metric. It often serves as an implicit contract betweenand encode logic. If the encoder thinks it is processing a bounded set of metadata entries but the underlying list has accumulated stale entries, then the loop controlling writes can walk off the end of the allocated buffer before anyone notices. That is the mechanism reflected in the KASAN report.
The upstream text is blunt that the behavior is “inappropriate” and can lead to unbounded metadata addition. That wording is important because it tells us the maintainers viewed the issueismatch and a safety hazard. It’s one thing to preserve old configuration state for compatibility; it’s quite another to let a supposedly replaced list keep accumulating forever.
The upshot is that CVE-2026-23378 is not about a vague risk of instability; it is about a reachable out-of-bounds write triggered by invalid growth in metadata bookkeeping. That distinction makes the issue much more actionable foh more meaningful for operators who need to decide whether a kernel update is worth prioritizing.
What stands out is that the maintainers did not need a wholesale redesign of the feature. Instead, they corrected the representation of the metalist in the ife RCU data structure so updates would properly replace prior state. That is a very Linux-kernel kind of fix: smald at restoring the intended invariant instead of layering on broad defensive checks everywhere.
That progression matters for triage. Security teams often ask whether a CVE is “really exploitable” or “just a bug.” In this case, the answer is straightforward: it is a bug with direct memory-safety implications. Even without a ready-made exploit chain, a slab out-of-bounds write is a serious kernel correctnessremediation.
That is why bugs like this often surprise people. They don’t begin as “attacker-controlled data causes overflow”; they begin as “the kernel kept the old state when it should have replaced it.” But in systems programming, those two statements can become the same thing once the state feeds a write loop.
The fact that the fault appears in
In effect, the patch changes the lifecycle model from “grow the list as needed” to “replace the list with the current configuration.” That is the right shape for a feature whose output encoding depends on a clean, bounded metadata set. It is also a reminder that good kernel fixes often come from moving data into a structure that matches the actual concurrency and replacement rules.
That slow-burn quality the bug operationally relevant. Large fleets tend to perform more configuration churn than lab systems, and rare state drift becomes statistically more likely as the number of updates rises. One host might run for months without issue, while a fleet with repeated policy changes or orchestration loops may eventually hit the bad path.
That matters because consumer-facing “it’s unlikely” bugs can stildents in small-office routers, home lab appliances, and embedded products that rely on Linux traffic control. If a vendor backports the fix unevenly—or not at all—the end user experience can diverge sharply from what upstream maintainers expect.
A second reason to care is that configuration-path vulnerabilities are easy to miss in eams often test packet flow, throughput, and basic policy correctness, but they do not always hammer reconfiguration paths with repeated replacement operations. That leaves a gap where this bug type can survive longer than a conventional crash-on-boot defect.
This is the sort of kernel fix that tends to age well. If the data structure itself now carries the correct replacement semantics, fewer downstream paths need to guess whether old metadata should still exist. That reduces the odds oftroduced later by someone who assumes the list behaves like a one-shot append buffer.
That choice also lowers maintenance burden. If the list replacement model is correct, future refactors in the encoding path are less likely to reintroduce the same class of bug. In security terms, that is the difference between suppressing a symptom and removing the condition that produortance of RCU correctness
RCU adds performance benefits, but it also imposes discipline on how shared data is published and replaced. The fix suggests the maintainers wanted the metalist to live in a structure that naturally supports that publication model. That is a strong architectural signal: the bug was not merely a typo, but a mismatch between data ownership and update semarnel development, those mismatches are often where the hardest bugs live. They don’t show up as obvious bad pointers or missing checks. They show up when one part of the code believes a list is disposable and another part believes it is cumulative. CVE-2026-23378 is a good example of why those aslicit.
Second, the vulnerability is clearly tied to a concrete path in
It would be a mistake to claim the bug automatically yields remote code execution or easy privilege escalation. The evidence available here supports a memory-safety flaw triggered through state replacement and encoding, not an end-to-end exploit chain. That still makes it serious, but serious is not the same as everywhere exploitable.
That nuance is useful for defenders. It helps teams prioritize accurately, communicate clearly with management, and avoid the kind of triage fatoverclaiming every kernel CVE as catastrophic. The right message is that this is a real kernel memory-safety bug with a clear fix path, not a speculative theory.
Finaliate enrichment data from NVD means some vulnerability management platforms may present this CVE with less context than usual at first. That is not a reason to wait; it is a reason to lean on the upstream kernel description and the stable patch trail until vendor advisories catch up.
A second thing to watch is whether additional tc or act_ife cleanups follow this patch. Once maintainers uncover a replacement-semantic flaw in one part of a subsystem, it often prompts a broader audit of adjacent data structures and lifecycle assumptions. Th outcome, because bugs like this are rarely isolated in a truly complicated networking path.
A third watch item is whether vendor advisories describe the issue accurately enough for automation tools to map the fix to the correct build. In practice, this is where real-world exposure gets resolved or left hangin vague, security teams may know the CVE number but still not know whether their image is actually protected.
CVE-2026-23378 is a reminder that not all serious Linux vulnerabilities arrive through dramatic exploit primitives. Some begin as stale state being appended where replacement was intended, then become a slab overflow once the list grows beyond the assumptions of the encoder. That makes this one a clean example of why kekernel security are so tightly intertwined—and why even a small semantic mistake in a control path can deserve urgent attention.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
ife_tlv_meta_encode(), making this one of those kernel bugs where a subtle state-management mistake becomes a concrete safety failure. t is not just that the bug exists, but that it exposes a mismatch between intended lifecycle behavior and actual implementation. In kernel code, “replace” should mean replace, not accumulate stale state across successive configuration changes. Here, that distinction matters because the encoded metadata path assumes the metalist remains bounded and internally consistent, and once that assumption breaks, the encoding routine can write beyond its slab object. The patch’s solution, as described in the upstream discussion, is to move the metalist into the IFE RCU data structure so replacement semantics can be enforced correctly.
 Background
Background
The subsystem is one of those parts of the kernel that rarely gets attention until something goes wrong. It sits in the path between user configuration and packet processing, which means small bookkeeping errors can have outsized effects when they’re exercised at scale. The act_ife component is used to encode metadata into packets, so its correctness depends on careful alignment between stored metadata, list management, and runtime encoding rules.The CVE description makes clear that theulative concern but a reproduced memory-safety fault. The bug trace shows a KASAN report in
ife_tlv_meta_encode() with a write beyond the allocated slab area, which is exactly the sort of diagnostic kernel maintainers rely on when turning a correctness bug into a documented security issue. That context is important because it tells administrators this is not just a cosmetic behavior bug; it is a real out-of-bounds condition reachable under the right configuration and update sequence.What makes the vulnerability especially relevant is the way ie” behavior in the control plane rather than a packet parser in the data plane. In other words, the dangerous state can be created by reconfiguration, not necessarily by inbound traffic alone. That broadens the operational concern: any system that uses tc actions and updates ife metadata over time could, in principle, build up the corrupted state.
The fix landed through the normal kernel-stable pipeline, which is another signal idered it suitable for backporting rather than leaving it as a future-tree cleanup. The stable-thread version of the patch explicitly identifies the root cause and frames the fix as a repair to metalist update behavior, with the upstream commit credited to Jamal Hadi Salim.
At a high level, this is a classic kernel pattern: the code worked under the assumption that a configurld reset old state, but the implementation appended instead. That kind of bug is easy to underestimate because it doesn’t look dramatic until repeated updates push the list beyond the bounds the encoder expects. Once that boundary is crossed, the kernel’s memory model does the rest.
What Broke in act_ife
The direct problem is simple to state: when an ife action was replaced and the metalist changwas appended rather than replacing the old data. That means repeated updates could grow the metadata list even though the action’s configuration was supposed to represent a single current state. Over time, the list could become unbounded, which is precisely the kind of state drift that eventually turns into a write past the end of a slab object.That behavior is especially bad in kernel code because list length is not just a cosmetic metric. It often serves as an implicit contract betweenand encode logic. If the encoder thinks it is processing a bounded set of metadata entries but the underlying list has accumulated stale entries, then the loop controlling writes can walk off the end of the allocated buffer before anyone notices. That is the mechanism reflected in the KASAN report.
Why append-vs-replace bugs matter
Append-versus-replace mistakes are notoriously dangerous in systems code because they hide behind valid-looking API semantics. ays “replace,” the kernel stores new data, and if the old data is not discarded, the bug can persist silently until enough churn builds up. In packet-processing code, that kind of latent growth is particularly risky because operational changes often happen gradually, not in a single dramatic transaction.The upstream text is blunt that the behavior is “inappropriate” and can lead to unbounded metadata addition. That wording is important because it tells us the maintainers viewed the issueismatch and a safety hazard. It’s one thing to preserve old configuration state for compatibility; it’s quite another to let a supposedly replaced list keep accumulating forever.
The role of KASAN
KASAN is doing what it is supposed to do here: expose a real memory violation at the point it becomes visible. The trace in the CVE description shows the fault inside `ife_tlv_meta_encothe write size and address, which gives the fix a strong empirical basis. This matters because kernel CVEs are often most credible when the report includes sanitizer-backed evidence rather than only a theoretical argument.The upshot is that CVE-2026-23378 is not about a vague risk of instability; it is about a reachable out-of-bounds write triggered by invalid growth in metadata bookkeeping. That distinction makes the issue much more actionable foh more meaningful for operators who need to decide whether a kernel update is worth prioritizing.
How the Vulnerability Emerged
The published thread shows the upstream fix traveling through the Linux networking mailing lists before reaching stable branches. The patch title itself—“Fix metalist update behavior”—is a good hint that the rood in state-management logic rather than in a low-level memory primitive. The more precise the title, the more likely it is that the bug came from a subtle contract violation rather than a dramatic crash path.What stands out is that the maintainers did not need a wholesale redesign of the feature. Instead, they corrected the representation of the metalist in the ife RCU data structure so updates would properly replace prior state. That is a very Linux-kernel kind of fix: smald at restoring the intended invariant instead of layering on broad defensive checks everywhere.
From logic error to security issue
Many kernel bugs start as logic errors and only later get classified as security issues when they touch memory boundaries. That is exactly what happened here. As long as the list stayed within expected size, the flaw would look like a bad configurationated replacement caused an out-of-bounds write, the bug crossed into vulnerability territory.That progression matters for triage. Security teams often ask whether a CVE is “really exploitable” or “just a bug.” In this case, the answer is straightforward: it is a bug with direct memory-safety implications. Even without a ready-made exploit chain, a slab out-of-bounds write is a serious kernel correctnessremediation.
The kernel’s configuration plane is not safe by default
A useful lesson here is that user-facing configuration APIs can be just as security-sensitive as packet parsers. The act_ife path accepts control inputs that shape how metadata is represented and encoded later. If the configuration logic does not preserve a correct internapath inherits the mistake and can fail in ways that are much harder to contain.That is why bugs like this often surprise people. They don’t begin as “attacker-controlled data causes overflow”; they begin as “the kernel kept the old state when it should have replaced it.” But in systems programming, those two statements can become the same thing once the state feeds a write loop.
The Technical Failure Mode
At the technicus sequence is straightforward: the action is replaced, the metalist should change, but the old metadata is not discarded. Instead, new entries are appended to the existing list. When the encoder later walks the list and writes TLVs into the output buffer, it does so under assumptions that no longer matcture. That disconnect produces the out-of-bounds write seen in the KASAN report.The fact that the fault appears in
ife_tlv_meta_encode() is important. Encoding code often relies on upstream invariants being correct and bounded, because its job is to serialize existing state, not revalidate the entire world. If the data model behind it is corrupted by unbounded accumulation, the encoder becomes the first place the bug turns visible.Why the write lands out of boundsn in the trace is 4 bytes, which suggests a small field or TLV component overrunning the slab edge rather than a giant memcpy. Those smaller writes can be just as dangerous as larger ones because they may corrupt adjacent kernel metadata in a way that is harder to notice immediately. In other words, the bug is not only about “crashing”; it is about violating kernel memory.
The report also shows the task and CPU context at the time of failure, reinforcing that the issue was reproduced in a concrete execution path. That makes the vulnerability more than hypothetical, and it helps explain why the kernel patch author framed the problem as an incorrect update behavior instead of merely an efficiency or cleanup issue.The significance of the RCU data structure change
Moving the metalist into the ife RCUdesign choice with practical consequences. RCU-managed state is usually arranged so readers can safely observe a coherent snapshot while writers replace the old version with a new one. That makes replacement semantics much easier to reason about than mutation-in-place semantics, especially when the data should be considered authoritative only asIn effect, the patch changes the lifecycle model from “grow the list as needed” to “replace the list with the current configuration.” That is the right shape for a feature whose output encoding depends on a clean, bounded metadata set. It is also a reminder that good kernel fixes often come from moving data into a structure that matches the actual concurrency and replacement rules.
Why This Matters to Enterprise Linux Users
For enterprise teams, this kind of issue iic-control actions can be part of network shaping, encapsulation, packet manipulation, or appliance-style Linux deployments where operators assume kernel configuration changes are stable and repeatable. If the same action gets replaced multiple times and the metalist silently accumulates stale entries, the risk rises over time rather than appearing instantly.That slow-burn quality the bug operationally relevant. Large fleets tend to perform more configuration churn than lab systems, and rare state drift becomes statistically more likely as the number of updates rises. One host might run for months without issue, while a fleet with repeated policy changes or orchestration loops may eventually hit the bad path.
Consumer impact is narrower, but not zero
Consumer Linux users are less likely to be manipulating tc actions by hand, so the practical eStill, the presence of a memory-safety bug in a networking subsystem means the issue should not be dismissed as “just enterprise.” Appliances, embedded devices, and specialized distributions often reuse the same kernel plumbing, and those environments can behave more like enterprise fleets than desktop machines.That matters because consumer-facing “it’s unlikely” bugs can stildents in small-office routers, home lab appliances, and embedded products that rely on Linux traffic control. If a vendor backports the fix unevenly—or not at all—the end user experience can diverge sharply from what upstream maintainers expect.
Why administrators should care even without an exploit narrative
Not every kernel CVE needs a dramatic exploit chain to be worth patching. A slab out-of-bounds write can corrupt adjacent kernel data structures, create instabionfidence in traffic-control deployments. For operators, the practical question is usually simpler: does the machine run the affected code path, and is the fix available in the vendor kernel? In this case, the answer should guide patch priority.A second reason to care is that configuration-path vulnerabilities are easy to miss in eams often test packet flow, throughput, and basic policy correctness, but they do not always hammer reconfiguration paths with repeated replacement operations. That leaves a gap where this bug type can survive longer than a conventional crash-on-boot defect.
The Patch Strategy
The upstream fix is notable because it addresses the structure of the problem rather than just slapping a guard around the encoder. By adding the metalist to the ife RCU data structure, the patch restores the placement operation replaces the prior list state. That is a more durable solution than trying to compensate later in the encode path.This is the sort of kernel fix that tends to age well. If the data structure itself now carries the correct replacement semantics, fewer downstream paths need to guess whether old metadata should still exist. That reduces the odds oftroduced later by someone who assumes the list behaves like a one-shot append buffer.
Why this is better than a band-aid
A band-aid fix would likely have checked list length or capped writes in the encoder. That would reduce the immediate crash risk, but it would leave the semantic error intact. The upstream approach is better because it corrects the source of truth, which is what kerny prefer when state lifecycles are the real problem.That choice also lowers maintenance burden. If the list replacement model is correct, future refactors in the encoding path are less likely to reintroduce the same class of bug. In security terms, that is the difference between suppressing a symptom and removing the condition that produortance of RCU correctness
RCU adds performance benefits, but it also imposes discipline on how shared data is published and replaced. The fix suggests the maintainers wanted the metalist to live in a structure that naturally supports that publication model. That is a strong architectural signal: the bug was not merely a typo, but a mismatch between data ownership and update semarnel development, those mismatches are often where the hardest bugs live. They don’t show up as obvious bad pointers or missing checks. They show up when one part of the code believes a list is disposable and another part believes it is cumulative. CVE-2026-23378 is a good example of why those aslicit.
Signals for Security Teams
The first thing security teams should notice is that NVD had not yet completed enrichment at the time of the record, so the primary actionable detail comes from kernel.org and the stable patch trail. That means triage should focus on the upstream fix and any vendor backports, not on waiting for a polished CVSS narrative to arrive later. The kernel report igh to justify prioritization.Second, the vulnerability is clearly tied to a concrete path in
act_ife, which should make scoping easier for administrators. If the kernel configuration or product image never uses that action, the practical exposure may be lower. But if tc-based packet manipulation is part of the workload, the issue de if exploitability looks narrow at first glance.Key triage questions
- Does the affected kernel build include the upstream fix for CVE-2026-23378?
- Does the environment use tc, act_ife, or related metadata-encoding actions?
- Are there vendor backports that change the version number but not the actual fix?
- Are repeated configuration replacements part of normal operations?
- Is the system a firewall, router, appliance, orwith frequent tc changes?
- Has the vendor advisory mapped the fix to the exact shipped build?
It would be a mistake to claim the bug automatically yields remote code execution or easy privilege escalation. The evidence available here supports a memory-safety flaw triggered through state replacement and encoding, not an end-to-end exploit chain. That still makes it serious, but serious is not the same as everywhere exploitable.
That nuance is useful for defenders. It helps teams prioritize accurately, communicate clearly with management, and avoid the kind of triage fatoverclaiming every kernel CVE as catastrophic. The right message is that this is a real kernel memory-safety bug with a clear fix path, not a speculative theory.
Strengths and Opportunities
The good news is that this is a relatively clean bug to reason about once the root cause is understoodeproduction path, a visible memory-safety symptom, and a patch that restores the intended semantics rather than obscuring them. That gives maintainers and downstream vendors a solid basis for remediation.- The flaw is clearly localized to act_ife metalist replacement behavior.
- The KASAN report provides strong evidence of a real out-of-bounds write.
- The patccause instead of only guarding the symptom.
- RCU-based replacement semantics are easier to maintain long term.
- Backporting should be straightforward for stable kernel trees.
- Enterprise triage can be focused on workloads that actually use tc actions.
- The CVE should be easy to map to vendor backports once they appear.
Risks and Concerns
The main concern is that bugs in configuration until systems have been running long enough to accumulate unusual state. That means a fleet can appear healthy for weeks or months and still contain a latent fault that only emerges after repeated replacement operations. In practice, that makes the bug more annoying than a single obvious crash.- Unbounded growth can stay invisible until the encoder finally walks off the slab boundary.
- Systems that rarely reconfigure may not reveal the issue in normal testing.
- Vendor backports may be uneven, cree in patch status.
- Appliance and embedded deployments may lag behind general-purpose servers.
- Configuration-path bugs are easy to misclassify as routine stability problems.
- Repeated tc updates can be more common in automation-heavy environments than administrators expect.
- A memory-safety issue in a controlbilize critical networking services.
Finaliate enrichment data from NVD means some vulnerability management platforms may present this CVE with less context than usual at first. That is not a reason to wait; it is a reason to lean on the upstream kernel description and the stable patch trail until vendor advisories catch up.
What to Watch Next
The next thing to watch is straightforward: which downstream stable branches and vendor kernels pick up the fix, and how quickly. Kernel CVEs often become operationally relevant not when they are published upstream, but when operators can finally see them reflected in the packages they actual references associated with this record make that backport path the key follow-up signal.A second thing to watch is whether additional tc or act_ife cleanups follow this patch. Once maintainers uncover a replacement-semantic flaw in one part of a subsystem, it often prompts a broader audit of adjacent data structures and lifecycle assumptions. Th outcome, because bugs like this are rarely isolated in a truly complicated networking path.
A third watch item is whether vendor advisories describe the issue accurately enough for automation tools to map the fix to the correct build. In practice, this is where real-world exposure gets resolved or left hangin vague, security teams may know the CVE number but still not know whether their image is actually protected.
Practical watch list
- Stable kernel backports for the affected Linux branches.
- Vendor-specific advisories that identify the fixed builds.
- Any follow-on commits touching act_ife or related tc metadata paths.
- Fleet inventories that show tc/traffic-control usage.
- Testing updates that add repeated replace op.
- Security-tooling updates that map the CVE to package-level fixes.
CVE-2026-23378 is a reminder that not all serious Linux vulnerabilities arrive through dramatic exploit primitives. Some begin as stale state being appended where replacement was intended, then become a slab overflow once the list grows beyond the assumptions of the encoder. That makes this one a clean example of why kekernel security are so tightly intertwined—and why even a small semantic mistake in a control path can deserve urgent attention.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center