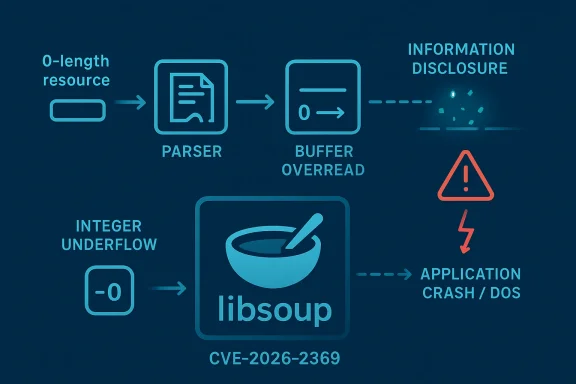
A newly disclosed libsoup vulnerability tracked as CVE-2026-2369 deserves attention because it combines a classic integer-underflow bug with a very practical impact: a buffer overread triggered while processing a zero-length resource. Red Hat’s CVE entry describes the flaw as a buffer overread caused by integer underflow, with potential consequences ranging from sensitive information disclosure to application-level denial of service y guide mirrors the same advisory, underscoring that this is not just a theoretical parser bug but one with broad downstream relevance for any platform that ships libsoup-based components.
libsoup is one of those infrastructural libraries that rarely gets headlines, yet quietly touches large parts of the desktop and server software stack. It is the GNOME project’s HTTP client/server library, and it has been embedded in countless applications over the years, from desktop utilities to network-aware services. That makes any memory-safety flaw in libsoup interesting not because it is flashy, but because it can propagate through a wide ecosystem of products that developers and users do not always associate with GNOME.
The vulnerability class matters as much as the library itself. An integer underflow occurs when arithmetic wraps past zero and produces a large unintended value, often because a subtraction is performed on a size or offset that was already at the lower bound. In parsers and network-facing code, that can feed into the wrong bounds check, allow a read operation to wander outside the intended buffer, and expose memory contents that should never have been accessible.
What is especially notable here is the trigger condition: zero-length resources. Those are easy to overlook in test coverage because they look harmless. But resource length edge cases are exactly where memory bugs like this tend to hide, especially when code assumes that “empty” inputs can be skipped without special handling. In practice, an attacker who can feed crafted content into a vulnerable path may be able to provoke the overread and observe memory disclosure or a crash.
The initial CVE record was received from Red Hat on March 19, 2026, with NVD enrichment still pending at the time the record was published. Red Hat tagged the issue as CWE-191 Integer Underflow, and assigned a CVSS v3.1 base score of 6.5 with network attack vector, no privileges required, no user interaction, and impacts to both confidentiality and availability . That combination plserious enough to patch quickly” category, even if it is not the most catastrophic memory-corruption class.
The project has also accumulated a security history that shows the same broad pattern of risk: parsing code, boundary checks, and memory arithmetic are where these bugs tend to surface. That is not a libsoup-specific curse so much as the reality of HTTP tooling in C, where performance, compatibility, and low-level memory management coexist in a very unforgiving environment. Once a library is widely embedded, even a modest bug can become an enterprise concern.
In recent years, the Linux desktop ecosystem has become more security-conscious about foundational libraries because supply-chain risk is no longer limited to flashy package manager exploits or browser CVEs. Organizations now track vulnerabilities in the libraries that drive package managers, content fetchers, web service clients, and desktop integration layers. In that context, libsoup issues matter because they can affect not just a single application, but the broader behavior of a desktop or server platform.
There is also a larger trend at work: small parser mistakes have big blast radii. That is true for image libraries, compression libraries, font engines, and HTTP stacks alike. A zero-length resource may sound banal, but in a networked application it can be the difference between a harmless edge case and a memory disclosure primitive.
That is precisely why integer-underflow bugs are so dangerous in C. They can appear in code that looks tidy and well-structured, yet still fail under the one edge case a developer did not expect. In other words, the logic is often locally sensible and globally unsafe.
The CVSS profile reinforces that interp-exploitable bug with no authentication requirement and no user interaction** gets defenders’ attention quickly, especially when the likely outcome is either data leakage or service disruption. The absence of integrity impact does not make it harmless; it simply means the attacker’s leverage is more about observation and crashing than direct modification.
A few implications stand out:
The other problem is that overreads often behave non-deterministically. A service might not crash every time, which makes the bug harder to notice during routine testing. That kind of intermittent instability is precisely what gives attackers room to experiment while defenders misdiagnose the root cause.
There is also a support cost. Applications that crash under malformed input can trigger retries, queue buildup, or watchdog restarts. In services that process traffic at scale, a low-rate crash bug can still become a meaningful availability problem.
The downstream impact could be especially visible in Linux desktop environments, GNOME-based applications, and any software distribution that bundles libsoup as part of a broader runtime stack. The CVE record’s presence in Red Hat’s security data suggests that enterprise Linux users should expect package-specific remediation guidance, even if the exploitability in a given deployment depends on how the library is used .
The consumer impact is often broader but quieter. Instead of a loud compromise, the most realistic outcome may be a crash, a freeze, or a subtle disclosure that users never notice. That makes patch adoption especially important because users generally do not have the telemetry needed to distinguish a random application crash from a vulnerability-triggered one.
A strong remediation plan starts with determining whether the affected version is present, then checking whether the package maintainer has released a backported fix. In enterprise Linux environments, that often means waiting for distribution-specific errata rather than upstream release notes alone. The fact that Red Hat has already posted a CVE record is a strong signal that downstream packaging work is in motion or imminent .
That broader pattern matters because defenders should not treat this as an isolated event. If one edge case in a resource-length calculation can produce an overread, other edge cases may exist in adjacent parsing logic. A mature vulnerability response therefore includes code review, fuzzing, and attention to upstream hardening as well as patching.
There is an opportunity here for better dependency hygiene, too. Organizations that use the incident to improve inventory, update cadence, and fuzzing coverage will come out stronger than they went in. Every library CVE is also a chance to tighten operational discipline.
There is also the evergreen problem of patch lag. Even when fixes are available upstream, enterprise deployment cycles, ABI compatibility constraints, and test queues can slow adoption. That gives attackers a window in which the vulnerability is public, the fix exists, but the affected code is still deployed in production.
It will also be worth watching whether additional libsoup issues surface from the same general code area. When a library hits one boundary-condition bug, security researchers often revisit adjacent parsing and size-calculation paths. That does not guarantee more flaws, but it is a very plausible outcome in mature C codebases.
Source: NVD Security Update Guide - Microsoft Security Response Center
 Overview
Overview
libsoup is one of those infrastructural libraries that rarely gets headlines, yet quietly touches large parts of the desktop and server software stack. It is the GNOME project’s HTTP client/server library, and it has been embedded in countless applications over the years, from desktop utilities to network-aware services. That makes any memory-safety flaw in libsoup interesting not because it is flashy, but because it can propagate through a wide ecosystem of products that developers and users do not always associate with GNOME.The vulnerability class matters as much as the library itself. An integer underflow occurs when arithmetic wraps past zero and produces a large unintended value, often because a subtraction is performed on a size or offset that was already at the lower bound. In parsers and network-facing code, that can feed into the wrong bounds check, allow a read operation to wander outside the intended buffer, and expose memory contents that should never have been accessible.
What is especially notable here is the trigger condition: zero-length resources. Those are easy to overlook in test coverage because they look harmless. But resource length edge cases are exactly where memory bugs like this tend to hide, especially when code assumes that “empty” inputs can be skipped without special handling. In practice, an attacker who can feed crafted content into a vulnerable path may be able to provoke the overread and observe memory disclosure or a crash.
The initial CVE record was received from Red Hat on March 19, 2026, with NVD enrichment still pending at the time the record was published. Red Hat tagged the issue as CWE-191 Integer Underflow, and assigned a CVSS v3.1 base score of 6.5 with network attack vector, no privileges required, no user interaction, and impacts to both confidentiality and availability . That combination plserious enough to patch quickly” category, even if it is not the most catastrophic memory-corruption class.
Background
libsoup has long occupied a strategic place in the open-source networking stack. It provides HTTP client and server capabilities for GNOME and other software projects, which means it is frequently pulled in as a dependency rather than chosen deliberately by end users. That dependency pattern is important, because security teams often discover that a single library vulnerability affects multiple applications that appear unrelated on the surface.The project has also accumulated a security history that shows the same broad pattern of risk: parsing code, boundary checks, and memory arithmetic are where these bugs tend to surface. That is not a libsoup-specific curse so much as the reality of HTTP tooling in C, where performance, compatibility, and low-level memory management coexist in a very unforgiving environment. Once a library is widely embedded, even a modest bug can become an enterprise concern.
In recent years, the Linux desktop ecosystem has become more security-conscious about foundational libraries because supply-chain risk is no longer limited to flashy package manager exploits or browser CVEs. Organizations now track vulnerabilities in the libraries that drive package managers, content fetchers, web service clients, and desktop integration layers. In that context, libsoup issues matter because they can affect not just a single application, but the broader behavior of a desktop or server platform.
There is also a larger trend at work: small parser mistakes have big blast radii. That is true for image libraries, compression libraries, font engines, and HTTP stacks alike. A zero-length resource may sound banal, but in a networked application it can be the difference between a harmless edge case and a memory disclosure primitive.
Why zero-length handling is risky
Zero-length inputs often bypass ordinary assumptions. Code may subtract one from a length to account for a terminator, derive a pointer to the “last byte,” or compute an offset that implicitly assumes a nonzero buffer. If those calculations are not guarded correctly, the resulting arithmetic can underflow and produce a value that looks valid to later code.That is precisely why integer-underflow bugs are so dangerous in C. They can appear in code that looks tidy and well-structured, yet still fail under the one edge case a developer did not expect. In other words, the logic is often locally sensible and globally unsafe.
- Zero-length data can short-circuit normal safety assumptions.
- Underflowed arithmetic can transform a harmless value into a huge one.
- Bounds checks may pass because they are checking the wrong derived value.
- Reads beyond the buffer can leak memory contents or crash a process.
What the Advisory Says
The public description of CVE-2026-2369 is clear and compact: libsoup can hit an integer underflow while handling content associated with a zero-length resource, and the resulting error enables a buffer overread. Red Hat’s record explicitly ties the bug to information disclosure and application-level denial of service, which is a useful reminder that overreads are not merely a privacy issue but also a stability issue .The CVSS profile reinforces that interp-exploitable bug with no authentication requirement and no user interaction** gets defenders’ attention quickly, especially when the likely outcome is either data leakage or service disruption. The absence of integrity impact does not make it harmless; it simply means the attacker’s leverage is more about observation and crashing than direct modification.
The scoring details
The published vector from Red Hat is CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:L/I:N/A:L with a base score of 6.5 . That is a middle-of-the-road severity rating, but in operatiol be painful if the vulnerable component sits in a high-value application path.A few implications stand out:
- Attack Vector: Network means remote delivery is plausible.
- Attack Complexity: Low suggests no exotic timing or environmental conditions.
- Privileges Required: None means the attacker need not be authenticated.
- User Interaction: None increases the chance of opportunistic exploitation.
- Confidentiality and Availability impacts mean the bug can leak memory or take a service down.
Why Buffer Overreads Still Matter
It is easy to dismiss a buffer overread as “just” a read bug, especially when the more dramatic headlines tend to favor code execution. That instinct is dangerous. Reading past the end of a buffer can still leak secrets, session material, object pointers, heap fragments, or other data that should remain private. In modern exploit chains, information disclosure is often the step that makes a later exploit practical.The other problem is that overreads often behave non-deterministically. A service might not crash every time, which makes the bug harder to notice during routine testing. That kind of intermittent instability is precisely what gives attackers room to experiment while defenders misdiagnose the root cause.
Disclosure is enough to hurt
Memory disclosure bugs can feed credential theft, address-space reconnaissance, and sandbox escape chains. Even if the leaked data looks random at first glance, it may reveal enough structure to help an attacker map a process’s memory layout or recover values from adjacent allocations. Once that happens, the bug stops being an isolated read issue and becomes part of a broader compromise strategy.There is also a support cost. Applications that crash under malformed input can trigger retries, queue buildup, or watchdog restarts. In services that process traffic at scale, a low-rate crash bug can still become a meaningful availability problem.
Enterprise Impact
For enterprises, the main issue is not whether every endpoint uses libsoup directly; it is whether the library sits beneath a business-critical application. Desktop fleets, internal tools, and network-facing utilities often rely on shared libraries that security inventories do not immediately spotlight. That means vulnerability management teams may need to trace package lineage before they know what is actually exposed.The downstream impact could be especially visible in Linux desktop environments, GNOME-based applications, and any software distribution that bundles libsoup as part of a broader runtime stack. The CVE record’s presence in Red Hat’s security data suggests that enterprise Linux users should expect package-specific remediation guidance, even if the exploitability in a given deployment depends on how the library is used .
What administrators should check
The immediate question is not “Do we run lickages or applications transitively depend on it?” That distinction matters because a vulnerable library may be pulled in through a desktop shell component, an updater, a file-transfer tool, or a custom application that rarely gets mapped in vulnerability dashboards.- Inventory packages that depend on libsoup.
- Check distribution advisories for patched builds.
- Identify any network-facing code paths that process untrusted content.
- Prioritize Internet-exposed and kiosk-like systems first.
- Validate whether the vulnerable code path is reachable in your deployment.
Consumer and Desktop Exposure
Consumer systems are less likely to face direct exploitation than enterprise services, but that does not make them immune. Desktop applications that fetch remote content, render metadata, or interact with web services may touch libsoup indirectly. The risk rises when an app processes attacker-controlled data from the web, an email preview, or a shared resource repository.The consumer impact is often broader but quieter. Instead of a loud compromise, the most realistic outcome may be a crash, a freeze, or a subtle disclosure that users never notice. That makes patch adoption especially important because users generally do not have the telemetry needed to distinguish a random application crash from a vulnerability-triggered one.
Why desktop fleets should care
Desktop software often updates more slowly than browser code, and that lag creates exposure windows. If a distro or enterprise image includes older libsoup builds, the vulnerable code can persist long after the issue is publicly known. In managed fleets, this is less about user behavior and more about the speed of package rollouts.- Desktop apps may inherit risk silently through dependencies.
- Users often cannot tell whether a crash was security-related.
- Managed fleets need package-level visibility, not just app-level visibility.
- Consumer systems are most vulnerable when they lag on updates.
Patch and Remediation Strategy
The most straightforward advice for CVE-2026-2369 is also the most boring: apply vendor updates as soon as they are available. That is because memory-safety bugs in core libraries are seldom something defenders can practically mitigate with configuration alone. Filtering inputs or disabling features may reduce exposure, but it is not a substitute for a fixed build.A strong remediation plan starts with determining whether the affected version is present, then checking whether the package maintainer has released a backported fix. In enterprise Linux environments, that often means waiting for distribution-specific errata rather than upstream release notes alone. The fact that Red Hat has already posted a CVE record is a strong signal that downstream packaging work is in motion or imminent .
Recommended response sequence
A sensible response sequence is as follows:- Confirm whether thekage is installed.
- Identify which applications link against it.
- Review vendor security advisories and backports.
- Patch the affected package or image.
- Restart impacted services where necessary.
- Monitor for unusual crashes or memory-related logs.
The Broader libsoup Security Pattern
CVE-2026-2369 fits a pattern that security teams have seen repeatedly in HTTP and parsing libraries: arithmetic mistakes, malformed inputs, and inadequate edge-case handling. Similar bugs in other libsoup code paths have shown how small miscalculations can manifest as request manipulation, information disclosure, or denial-of-service issues. The lesson is not that libsoup is uniquely brittle, but that all network parsers are high-risk code.That broader pattern matters because defenders should not treat this as an isolated event. If one edge case in a resource-length calculation can produce an overread, other edge cases may exist in adjacent parsing logic. A mature vulnerability response therefore includes code review, fuzzing, and attention to upstream hardening as well as patching.
Why C libraries keep attracting these bugs
C remains a performance-oriented language with thin abstractions around memory. That gives developers speed and control, but it also makes length arithmetic, pointer math, and buffer ownership easy to get wrong. Libraries like libsoup live at the intersection of performance and parsing complexity, where the probability of edge-case mistakes is simply higher.- Parsing code must tolerate malformed inputs.
- Length calculations need multiple layers of validation.
- Compatibility pressure can preserve old assumptions too long.
- Fuzzing often finds the bugs that manual review misses.
- Backward-compatible fixes are harder than fresh rewrites.
Strengths and Opportunities
The good news is that this vulnerability is the kind of problem that vendors and maintainers understand well, and that makes remediation realistic. Because the flaw is in a foundational library rather than a bespoke business workflow, it is also more likely to receive coordinated downstream fixes across distributions and enterprise channels.There is an opportunity here for better dependency hygiene, too. Organizations that use the incident to improve inventory, update cadence, and fuzzing coverage will come out stronger than they went in. Every library CVE is also a chance to tighten operational discipline.
- Clear bug class with well-known remediation patterns.
- Downstream vendors can backport fixes without waiting for major upgrades.
- Package inventories can be improved around shared libraries.
- Fuzzing and CI coverage can be expanded to edge cases.
- Crash telemetry can be used to identify real-world exposure.
- Dependency mapping can reduce future blind spots.
- Security teams can refine alerts for memory-safety indicators.
Risks and Concerns
The main concern is reachability: teams may underestimate how many applications transitively depend on libsoup, which delays patching. Another risk is the quiet nature of the flaw; if exploitation first appears as intermittent crashes or small data leaks, defenders may dismiss it as ordinary instability rather than a security event.There is also the evergreen problem of patch lag. Even when fixes are available upstream, enterprise deployment cycles, ABI compatibility constraints, and test queues can slow adoption. That gives attackers a window in which the vulnerability is public, the fix exists, but the affected code is still deployed in production.
- Transitive dependencies may hide exposure.
- Memory disclosures can be more damaging than they look.
- Application crashes may be misclassified as routine instability.
- Patch lag can leave long-lived exposure windows.
- Backported fixes may vary by distribution and package version.
- Edge-case bugs are often easy to miss in testing.
- Zero-length resource paths may be overlooked in validation plans.
Looking Ahead
The next phase of this story will be about where the fix lands and how broadly it propagates. If distribution maintainers push backported packages quickly, the practical risk window could remain relatively short. If not, administrators will need to rely on their own inventories and update workflows to catch vulnerable versions before they become a problem.It will also be worth watching whether additional libsoup issues surface from the same general code area. When a library hits one boundary-condition bug, security researchers often revisit adjacent parsing and size-calculation paths. That does not guarantee more flaws, but it is a very plausible outcome in mature C codebases.
What to watch next
- Distribution advisories for fixed libsoup builds.
- Whether the upstream GNOME issue tracker publishes a root-cause explanation.
- Any mention of affected application classes beyond the library itself.
- Backported patches in enterprise Linux errata.
- Follow-up hardening or fuzzing work in libsoup parsing code.
Source: NVD Security Update Guide - Microsoft Security Response Center