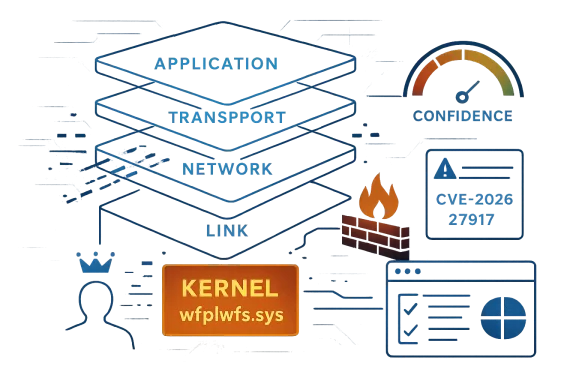
Microsoft’s entry for CVE-2026-27917 frames the issue as a Windows WFP NDIS Lightweight Filter Driver elevation-of-privilege flaw in wfplwfs.sys, and the confidence metric attached to the advisory is the key clue for defenders. In Microsoft’s terminology, that metric reflects how certain the vendor is that the vulnerability exists and how credible the technical details are, which matters because it tells administrators whether they are dealing with a confirmed bug, a suspected issue, or something still being validated. In practical terms, that makes this the kind of local privilege-escalation problem that security teams treat as high value for patching even before exploit details become public. The public discussion around similar Microsoft kernel and driver issues in recent Patch Tuesday cycles shows why these records get so much attention: once the vendor acknowledges a driver-level flaw, defenders have to assume the attack surface is real until proven otherwise. Windows Filtering Platform sits deep in the Windows networking stack and mediates traffic inspection, filtering, and policy enforcement across user-mode and kernel-mode boundaries. The NDIS lightweight filter model is especially important because it allows third-party and Microsoft components to observe or influence packet flow without replacing the entire networking stack. That design makes the subsystem powerful, but it also means that bugs in a filter driver can carry disproportionately large consequences. A weakness in a component like wfplwfs.sys is not just another application bug; it is a problem in code that operates close to the kernel’s trust boundary.
Driver bugs also matter because they are frequently abused as local privilege escalation stepping stones. An attacker who already has a foothold on a machine often does not need remote code execution to cause serious damage. Instead, they look for a vulnerable kernel component that will let them go from a low-privilege account to SYSTEM or kernel-level control. That is why Microsoft’s driver and kernel CVEs tend to receive immediate scrutiny from incident responders, patch managers, and red teams alike. The pattern is familiar: the exploit chain begins with a local execution foothold, then uses a driver bug to break out of the sandbox and seize the host.
This is also why Microsoft’s confidence indicator is important. If the company has a high degree of confidence in the flaw’s existence, then defenders can prioritize remediation even when the public description is brief. If the confidence level is lower, administrators may treat the record more cautiously and wait for corroboration. In either case, the signal helps separate a fully acknowledged vulnerability from a theoretical concern. That distinction is especially valuable in driver security, where kernel bugs can be difficult to validate from the outside and where exploitability can be heavily dependent on build, configuration, and runtime state.
The broader Windows security landscape in 2026 has continued to emphasize local privilege escalation, kernel memory safety, and driver hardening as recurring themes. Publicly disclosed Microsoft issues in related subsystems during the same period show a recurring story: small implementation mistakes in components that sit near the kernel boundary can have outsized consequences for enterprise fleets. The result is a patching environment where administrators increasingly have to balance incomplete public detail against the operational reality that a confirmed Microsoft CVE is probably more than a paper cut.
Microsoft’s confidence metric is not a casual label. It is a structured signal about how much trust defenders should place in the public advisory and its technical characterization. When the vendor publishes a record with a meaningful confidence score, it is effectively telling administrators that the vulnerability is not just rumor or community speculation. That is significant for wfplwfs.sys, because driver-level bugs are often hard to independently inspect and may sit behind relatively sparse public descriptions.
The metric also helps separate known risk from possible risk. A public advisory with moderate or high confidence suggests that the issue has been sufficiently validated to justify active remediation planning. By contrast, a lower-confidence entry may signal that the vendor has not fully confirmed root cause, exploitability, or impact. In a local EoP case, that distinction can shape whether security teams push an emergency update or fold it into a scheduled maintenance window.
That is especially relevant on machines where security software, VPNs, and traffic inspection tools are layered on top of Microsoft’s networking framework. Even if the vulnerable path is not always exercised, the presence of a confirmed driver bug can create a broad remediation obligation because the same subsystem is often shared across many deployed configurations. A single driver defect can therefore affect both client devices and servers in ways that are hard to predict without inventory data.
For home users, the main concern is delayed patching and opportunistic malware. For enterprises, the concern is lateral movement, persistence, and the possibility that a low-privilege foothold can be turned into administrator control across managed systems. That is why a local driver CVE often ends up being treated as a fleet-wide priority rather than a niche technical issue.
That pattern is why vulnerability managers pay so much attention to attack complexity and privilege requirements. Even if exploitation is not trivial, a reliable local EoP bug is valuable because it is easier to operationalize than a remote exploit. For defenders, that means the absence of public weaponization is not much comfort once the CVE is real and patchable.
That is not a flaw in the disclosure process; it is a compromise. Vendors need to support defenders without handing attackers a roadmap. When the advisory is about a driver in a sensitive subsystem, the balance typically tips toward brevity. Administrators then rely on the update package, affected-build lists, and confidence indicators to guide response.
This also matters for Microsoft itself. Every high-profile driver issue increases pressure to keep tightening the platform’s attack surface. That can mean better code auditing, stricter driver signing expectations, more conservative kernel interfaces, and deeper investment in memory safety. The market increasingly rewards vendors that can demonstrate not just response speed but structural improvement.
The final concern is that driver vulnerabilities often age badly when left unpatched. Once public awareness spreads, attackers can focus on local escalation chains even if exploitation is not immediately widespread. That is why these issues deserve attention on the day they are disclosed, not after they become part of a larger incident report.
What matters most now is not whether attackers have already weaponized the flaw, but whether defenders can close the gap before that becomes relevant. For a driver bug in the Windows filtering stack, the safe bet is to assume that someone will eventually try to operationalize it. The best response is to make sure they do so on patched machines.
Source: MSRC Security Update Guide - Microsoft Security Response Center
Driver bugs also matter because they are frequently abused as local privilege escalation stepping stones. An attacker who already has a foothold on a machine often does not need remote code execution to cause serious damage. Instead, they look for a vulnerable kernel component that will let them go from a low-privilege account to SYSTEM or kernel-level control. That is why Microsoft’s driver and kernel CVEs tend to receive immediate scrutiny from incident responders, patch managers, and red teams alike. The pattern is familiar: the exploit chain begins with a local execution foothold, then uses a driver bug to break out of the sandbox and seize the host.
This is also why Microsoft’s confidence indicator is important. If the company has a high degree of confidence in the flaw’s existence, then defenders can prioritize remediation even when the public description is brief. If the confidence level is lower, administrators may treat the record more cautiously and wait for corroboration. In either case, the signal helps separate a fully acknowledged vulnerability from a theoretical concern. That distinction is especially valuable in driver security, where kernel bugs can be difficult to validate from the outside and where exploitability can be heavily dependent on build, configuration, and runtime state.
The broader Windows security landscape in 2026 has continued to emphasize local privilege escalation, kernel memory safety, and driver hardening as recurring themes. Publicly disclosed Microsoft issues in related subsystems during the same period show a recurring story: small implementation mistakes in components that sit near the kernel boundary can have outsized consequences for enterprise fleets. The result is a patching environment where administrators increasingly have to balance incomplete public detail against the operational reality that a confirmed Microsoft CVE is probably more than a paper cut.
 What Microsoft’s Confidence Metric Really Means
What Microsoft’s Confidence Metric Really Means
Microsoft’s confidence metric is not a casual label. It is a structured signal about how much trust defenders should place in the public advisory and its technical characterization. When the vendor publishes a record with a meaningful confidence score, it is effectively telling administrators that the vulnerability is not just rumor or community speculation. That is significant for wfplwfs.sys, because driver-level bugs are often hard to independently inspect and may sit behind relatively sparse public descriptions.Confidence as a practical prioritization tool
For patch teams, confidence functions as a decision accelerator. A highly credible vulnerability can move straight into urgent deployment queues, while a less certain issue may stay in monitoring until more evidence appears. In a complex fleet, that difference matters because patch windows are limited and every cycle carries competing priorities. Microsoft’s confidence signal helps compress uncertainty and allows defenders to act on the most operationally meaningful information first.The metric also helps separate known risk from possible risk. A public advisory with moderate or high confidence suggests that the issue has been sufficiently validated to justify active remediation planning. By contrast, a lower-confidence entry may signal that the vendor has not fully confirmed root cause, exploitability, or impact. In a local EoP case, that distinction can shape whether security teams push an emergency update or fold it into a scheduled maintenance window.
Why the metric matters more for kernel drivers
Kernel and driver vulnerabilities are harder to reason about than ordinary application bugs because their behavior depends on privilege, memory layout, and system state. A bug in a filter driver may only manifest under certain traffic conditions or on specific Windows builds. That means the vendor’s own confidence is a useful guide when public proof-of-concept data is unavailable. It tells defenders how seriously to take the advisory before outside researchers have had a chance to reproduce the issue.- Higher confidence usually means the vulnerability is real enough to drive immediate response.
- Lower confidence may indicate incomplete technical detail or a still-evolving assessment.
- Kernel drivers are especially sensitive because exploitability can be opaque.
- Local EoP flaws often require a foothold, but they are still highly valuable to attackers.
- Vendor acknowledgement is often the most important signal for enterprise prioritization.
The operational takeaway
Security teams should treat the confidence metric as an indicator of how aggressively they should respond, not as a substitute for patch validation. A high-confidence kernel CVE can justify rapid remediation even when exploit notes are sparse. A lower-confidence one might warrant additional telemetry review. Either way, once Microsoft assigns the issue to a real driver and publishes it in the Security Update Guide, the problem has crossed the threshold from speculative to actionable.Why wfplwfs.sys Deserves Attention
wfplwfs.sys belongs to a category of Windows components that most users never notice but that enterprise defenders depend on every day. Network filtering and firewall enforcement are foundational to modern endpoint management. A flaw in the driver layer can affect more than packet handling; it can influence trust boundaries, traffic inspection, and the stability of networking services that other software assumes are reliable.A kernel-adjacent attack surface
The WFP NDIS lightweight filter layer exists precisely because Windows needs to let filters operate close to traffic flow without giving every vendor direct control over the kernel. That tradeoff improves flexibility, but it also creates a sensitive attack surface. Any bug that allows local privilege escalation in this path is valuable to attackers because it can help them bypass user-mode controls, tamper with security tools, or neutralize endpoint protections.That is especially relevant on machines where security software, VPNs, and traffic inspection tools are layered on top of Microsoft’s networking framework. Even if the vulnerable path is not always exercised, the presence of a confirmed driver bug can create a broad remediation obligation because the same subsystem is often shared across many deployed configurations. A single driver defect can therefore affect both client devices and servers in ways that are hard to predict without inventory data.
Why local bugs are still urgent
Some administrators are tempted to down-rank local EoP issues because they are not remotely exploitable by default. That instinct is understandable but dangerous. Local privilege escalation is one of the most common phases in real-world intrusion chains. Once an attacker has a low-privilege foothold—via phishing, token theft, malicious software, or a separate RCE—they often need only one kernel bug to complete compromise.- Local does not mean low impact in enterprise environments.
- Privilege escalation is frequently the last mile in an intrusion.
- Kernel bugs are attractive because they can defeat endpoint controls.
- Driver flaws may be leveraged for persistence or defense evasion.
- Patch latency gives attackers a window to operate on unpatched hosts.
Enterprise versus consumer exposure
Consumer machines may face a narrower practical threat model because they are less likely to be targeted for sophisticated local escalation chains. But enterprises live in a different world. They have more software installed, more privilege diversity, and more opportunities for an attacker to land with a standard user token and then climb. In that environment, a single confirmed kernel driver bug can be the difference between containment and domain-wide compromise.For home users, the main concern is delayed patching and opportunistic malware. For enterprises, the concern is lateral movement, persistence, and the possibility that a low-privilege foothold can be turned into administrator control across managed systems. That is why a local driver CVE often ends up being treated as a fleet-wide priority rather than a niche technical issue.
How Windows Driver Vulnerabilities Become Exploitation Primitives
Microsoft driver vulnerabilities rarely matter only for their immediate crash or corruption potential. In practice, they often become exploitation primitives—small building blocks that attackers combine into a more powerful chain. A driver bug in the Windows networking stack can be used to escape a constrained context, weaken security products, or obtain the authority needed to disable defenses.The usual attacker workflow
An attacker who discovers or receives access to a local vector often follows a predictable path. They first establish code execution in a low-privilege context. Then they look for a route into a vulnerable kernel object, driver interface, or access-control boundary. If the bug yields arbitrary kernel read/write, privilege escalation, or token manipulation, they can often convert that into full host compromise.That pattern is why vulnerability managers pay so much attention to attack complexity and privilege requirements. Even if exploitation is not trivial, a reliable local EoP bug is valuable because it is easier to operationalize than a remote exploit. For defenders, that means the absence of public weaponization is not much comfort once the CVE is real and patchable.
Why network filter drivers are especially attractive
Networking drivers sit in a part of the stack that many security tools must trust implicitly. VPN clients, packet inspectors, firewall products, and telemetry agents all rely on a stable networking foundation. If an attacker can influence that foundation, they may be able to interfere with enforcement logic or access privileged code paths indirectly. That makes a filter-driver CVE doubly important: it may offer privilege escalation and a path to subvert visibility.- Trusted kernel paths are often the easiest place to hide malicious behavior.
- Security tools can be undermined if the attacker reaches the right privilege level.
- Networking components are deeply embedded in normal system operations.
- Driver interfaces may expose attack paths that are not obvious from user mode.
- A single weakness can support multiple stages of intrusion.
The strategic value to attackers
If the flaw in wfplwfs.sys is confirmed as a privilege escalation, then the strategic value is straightforward: it can be used to turn user-level access into something much more powerful. That is particularly relevant in ransomware, espionage, and insider-threat scenarios. Attackers do not need every vulnerability to be spectacular; they just need one reliable path to the next rung on the ladder.Microsoft’s Disclosure Style and Why It Matters
Microsoft has long favored a disclosure model that balances actionability with caution. The company often publishes enough information to let defenders patch, but not so much that it hands attackers a turn-key exploit recipe. That approach is evident in many kernel and driver advisories, where the public description is intentionally concise. In the case of CVE-2026-27917, the confidence metric becomes part of the message because it supplements the limited text with a sense of certainty.Why minimal public detail is common
There are sound reasons for keeping technical detail restrained. Full root-cause descriptions can accelerate reverse engineering and aid weaponization. At the same time, Microsoft still has to provide enough information for security operations teams to identify affected systems and measure urgency. The result is a public record that is often operationally rich but technically sparse.That is not a flaw in the disclosure process; it is a compromise. Vendors need to support defenders without handing attackers a roadmap. When the advisory is about a driver in a sensitive subsystem, the balance typically tips toward brevity. Administrators then rely on the update package, affected-build lists, and confidence indicators to guide response.
The role of vendors and third parties
Independent trackers often fill in gaps left by the primary advisory. They may infer affected versions, identify the subsystem class, or correlate the issue with a known driver file. But those sources are still secondary, and in a case like this, Microsoft’s own update entry remains the authoritative starting point. When a vulnerability is vendor-acknowledged, defenders should assume the public record is enough to justify action even if external research remains incomplete.- Vendor advisories are the canonical source for remediation.
- Secondary trackers can help with context but may be incomplete.
- Confidence metrics can bridge the gap between sparse detail and urgent response.
- Affected-version mapping often matters more than exploit theory.
- Patch availability usually determines operational priority.
Why this fits Microsoft’s broader pattern
Microsoft has repeatedly shown that it will patch privilege-escalation defects across the Windows stack without immediately publishing exhaustive technical details. That creates a discipline for defenders: treat the advisory as real, patch quickly, and wait for research to catch up later. The fact that wfplwfs.sys is being handled in that same style strongly suggests that Microsoft wants administrators to focus on mitigation rather than on speculation.What Defenders Should Do First
The first priority is simple: confirm whether affected systems are running the vulnerable Windows builds and then apply the relevant security update as soon as operationally feasible. Because this is a local elevation-of-privilege issue in a kernel-adjacent driver, the safest assumption is that it can matter anywhere the component is present. Waiting for proof-of-concept code is not a good strategy when the vendor has already acknowledged the flaw.Immediate response steps
- Inventory all Windows endpoints and servers to identify the specific builds in scope.
- Map those builds to Microsoft’s patch guidance and verify the update is available.
- Prioritize internet-facing, high-value, and privilege-rich systems first.
- Confirm patch deployment success instead of assuming a policy push completed cleanly.
- Review local admin exposure and limit unnecessary elevated accounts.
- Monitor for suspicious driver-loading or privilege-escalation activity during the patch window.
- Validate security tooling to ensure endpoint controls remain healthy after remediation.
Why validation matters
Patch validation is particularly important for driver-related flaws because remediation can be uneven across editions and servicing branches. Some organizations discover that their inventory says one thing while the actual machine state says another. Others find that a third-party image, recovery partition, or long-term support branch complicates update accounting. The higher the confidence in the vulnerability, the less room there is for assuming that a delay is harmless.Enterprise controls that help
- WDAC and device control can reduce the chance of unapproved code execution.
- Least privilege limits the usefulness of a local EoP bug.
- Patch staging can help catch compatibility issues before broad rollout.
- Driver inventorying improves visibility into kernel exposure.
- EDR telemetry may help spot exploitation attempts or post-exploitation behavior.
Broader Market and Security Implications
A confirmed Microsoft driver CVE always has implications beyond the immediate patch cycle. It affects how enterprises view Windows hardening, how security vendors tune detection, and how attackers assess whether it is worth investing in exploitation. If CVE-2026-27917 is widely applicable, it reinforces the idea that even mature networking subsystems can still harbor privilege-escalation paths.Competitive pressure on security tooling
Endpoint security vendors depend on trustworthy kernel behavior. If a driver flaw can be chained into control evasion, then products that rely on the Windows networking stack may need to adjust their monitoring and protection strategies. That often leads to stronger kernel telemetry, better exploit detection, and more aggressive driver policy enforcement. In other words, a single CVE can push the ecosystem toward more hardened defaults.This also matters for Microsoft itself. Every high-profile driver issue increases pressure to keep tightening the platform’s attack surface. That can mean better code auditing, stricter driver signing expectations, more conservative kernel interfaces, and deeper investment in memory safety. The market increasingly rewards vendors that can demonstrate not just response speed but structural improvement.
Why this reinforces patch discipline
Organizations that have already built strong patch hygiene will absorb the impact of a driver CVE more gracefully. Those that rely on ad hoc updates will feel it more sharply. As with many Windows security issues, the real story is not just the vulnerability but the organization’s ability to move from advisory to deployment without friction. The faster that transition happens, the smaller the opportunity window for attackers.The role of incident responders
Incident responders should treat a driver privilege-escalation CVE as a useful signal even before exploitation is observed. If a machine is compromised and the vulnerable driver is present, the path from foothold to full control becomes more plausible. That changes the triage math. A seemingly small local issue may turn out to be the missing link in a much larger intrusion.- Detection teams should baseline driver-related activity.
- Threat hunters should look for post-exploitation privilege changes.
- IR teams should not dismiss local EoP as low impact.
- Patch teams should coordinate tightly with operations.
- Security architects should treat kernel trust boundaries as strategic assets.
Strengths and Opportunities
The strongest aspect of Microsoft’s handling here is that the company has surfaced the issue with enough clarity for defenders to act. The combination of a named driver, a specific class of impact, and a confidence metric gives security teams a workable basis for prioritization. That is valuable because it keeps the response focused on practical remediation instead of endless speculation.- Clear vendor acknowledgement reduces ambiguity.
- Driver-level specificity helps asset owners map exposure.
- Confidence metadata improves prioritization.
- Patch guidance allows rapid operational response.
- Enterprise relevance is easy to explain to stakeholders.
- Opportunity for hardening exists beyond the immediate fix.
- Telemetry review can improve detection readiness.
Risks and Concerns
The biggest risk is underestimating the issue because it is “only” a local privilege escalation vulnerability. That framing can lull organizations into treating the advisory as lower priority than a remote code execution flaw, even though a local EoP bug is often exactly what attackers need to complete an intrusion. In enterprise settings, local can quickly become domain-wide.- Patch delay leaves a real exploitation window.
- Partial inventory can hide affected systems.
- Admin sprawl magnifies the value of escalation bugs.
- Driver complexity makes validation harder.
- Third-party security tools may be indirectly affected.
- Rollback issues can create false confidence.
- Sparse public detail complicates root-cause analysis.
The final concern is that driver vulnerabilities often age badly when left unpatched. Once public awareness spreads, attackers can focus on local escalation chains even if exploitation is not immediately widespread. That is why these issues deserve attention on the day they are disclosed, not after they become part of a larger incident report.
Looking Ahead
The next few days and weeks will likely determine how much operational weight CVE-2026-27917 carries in practice. If Microsoft’s confidence level is high and the patch is straightforward, the issue may fade quickly into the long tail of routine Windows remediation. If enterprise customers encounter compatibility problems or delayed backports, it could linger as a scheduling headache even after the advisory is public.What matters most now is not whether attackers have already weaponized the flaw, but whether defenders can close the gap before that becomes relevant. For a driver bug in the Windows filtering stack, the safe bet is to assume that someone will eventually try to operationalize it. The best response is to make sure they do so on patched machines.
- Confirm affected build coverage across clients and servers.
- Deploy Microsoft’s fix through normal change-control channels.
- Verify successful installation with post-patch validation.
- Watch for privilege-escalation indicators in endpoint telemetry.
- Reassess local admin policies to reduce exploitation value.
- Track any follow-up advisory changes from Microsoft.
Source: MSRC Security Update Guide - Microsoft Security Response Center
Last edited: