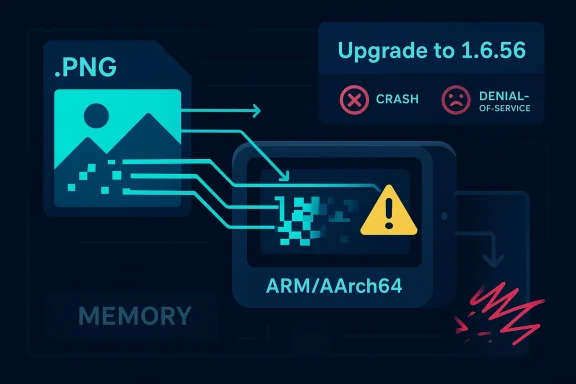
CVE-2026-33636 is another reminder that image decoding remains one of the most attack-prone corners of the software stack, especially where hand-tuned SIMD code meets attacker-controlled input. In libpng, the flaw sits in the ARM/AArch64 Neon-optimized palette expansion path, where a final partial chunk can be processed without first confirming that enough pixels remain. The result is an out-of-bounds read and write on affected versions, and because the issue is reachable during normal decoding of crafted PNGs, the practical impact extends beyond theory. (nvd.nist.gov)
libpng is the canonical PNG reference implementation and a foundational dependency for countless applications, libraries, and embedded systems. The project’s longevity is part of the problem as well as the solution: decades of broad adoption mean that even niche bugs can propagate through large parts of the ecosystem. The official repository notes that libpng has been in extensive use since 1995 and that modern releases are still expected to preserve compatibility while continuing to evolve the internals. (github.com)
What makes CVE-2026-33636 notable is not simply that it is a memory-safety bug. It is a memory-safety bug in a path intended to make PNG decoding faster on ARM and AArch64 systems, where Neon SIMD support is often enabled by default in performance-sensitive builds. That means the vulnerable code is not an obscure optional component; it is exactly the sort of optimized path vendors are likely to rely on for throughput, battery life, and latency. (nvd.nist.gov)
NVD describes the flaw as affecting libpng versions 1.6.36 through 1.6.55, with version 1.6.56 fixing the issue. The record also identifies the weakness classes as CWE-125 out-of-bounds read and CWE-787 out-of-bounds write, which is an important combination because the bug can both expose memory and corrupt it. (nvd.nist.gov)
The severity picture is also worth noting. GitHub’s CNA-assigned rating lands at CVSS 3.1 7.6 High, with the vector AV:N/AC:L/PR:N/UI:R/S:U/C:L/I:L/A:H. That profile suggests a network-reachable attack surface in applications that decode untrusted PNG content, while still requiring user interaction or a workflow step that causes a vulnerable component to process the file. (nvd.nist.gov)
A lot of the security conversation around image libraries focuses on code execution, but availability can be just as important. Microsoft’s update guide summary for the CVE emphasizes a total loss of availability in the impacted component, which aligns with the idea that even a relatively narrow memory bug can become a reliable denial-of-service vector when the decoder crashes or enters undefined behavior. That framing matters because many administrators triage “read” issues as lower risk than “write” issues, when in practice the operational fallout can be immediate and persistent. (nvd.nist.gov)
That backward-processing strategy is central to understanding why the bug is dangerous. A vectorized routine often tries to process data in fixed-size blocks for speed, but once the row length leaves a remainder, the implementation has to either mask the tail carefully or switch to a safe cleanup path. Here, the tail case appears to be under-guarded, so the final iteration can dereference before the valid row memory and then write expanded pixel data into those underflowed positions. (nvd.nist.gov)
That detail matters for defenders because it means fuzzing and edge-case input generation are particularly valuable. Vulnerabilities like this often hide in valid-but-unusual image dimensions, palette sizes, or row alignments, not only in obviously malformed files. The exploit condition can therefore be triggered by content that appears normal to users and automation alike. (nvd.nist.gov)
The second question is whether the architecture restriction shrinks the risk enough to ignore. It does reduce the scope, but not by enough to be comforting. AArch64 is widespread in cloud infrastructure, mobile devices, SBCs, edge appliances, and modern desktops, and Neon support is a normal feature of that ecosystem rather than an exotic optional add-on. In other words, this is a targeted bug, but the target population is still large. (nvd.nist.gov)
For enterprises, the implications are more varied. Automated document ingestion, media scanning, content moderation, DAM systems, and image conversion pipelines often process untrusted files at scale. In those environments, a crash is not just an inconvenience; it can become a queue backlog, a failed job storm, or an outage in a service that depends on image normalization. That is how a decoder bug turns into an availability incident. (nvd.nist.gov)
A subtle point is that AArch64-heavy environments are often performance-tuned environments too. That means the very deployments most likely to enable SIMD acceleration are also the ones most sensitive to repeated crashes or degraded throughput. A vulnerability that seems architecture-specific can therefore have an outsized operational footprint in exactly the places where acceleration was chosen for business reasons. (nvd.nist.gov)
The availability component is especially severe, with the NVD vector marking A:H. That aligns with Microsoft’s description of total loss of availability in the impacted component, which is a strong reminder that many operational risks are cumulative: a single crash may be tolerable, but repeated crashes in an automated pipeline can block legitimate work and create a cascading service incident. (nvd.nist.gov)
There is also an architectural nuance here. SIMD code paths sometimes have different memory access patterns from scalar code, which can influence both exploitability and crash consistency. That does not make the bug less important; it makes analysis harder, because behavior may vary by compiler, build flags, and CPU feature detection. In security terms, variability is not comfort. It is just another reason the issue needs patching rather than hand-waving. (nvd.nist.gov)
That last point is easy to underestimate. Image libraries are often statically linked, vendored, or embedded inside larger software distributions, which means a patched system package does not necessarily eliminate the vulnerable copy that matters. In enterprise environments, software composition analysis and binary inventory can be more important than apt or dnf output. (nvd.nist.gov)
The choice of Neon also reflects a broader trend in software engineering: performance work often lives closest to the metal, which means it often inherits the least safety margin. Hand-written assembly or intrinsics can outperform generic code, but they are also harder to reason about formally and harder to fuzz comprehensively. The security tradeoff is not theoretical; it is visible in recurring SIMD-related bugs across many projects. (nvd.nist.gov)
The lesson is not that vectorization is bad. The lesson is that vectorization without airtight bounds logic is security debt. Libraries like libpng have to balance compatibility, performance, and correctness, but once a security issue lands in the accelerated path, the cost of that balance becomes visible in the patch cycle. Fast code is only an asset if it stays in bounds. (nvd.nist.gov)
This is also where release engineering matters. The more a software vendor relies on upstream libraries, the more quickly it can consume a fixed release. But if the vendor vendors or forks the library, the security burden shifts inward, and patch latency becomes a function of internal build, QA, and sign-off cycles. That is especially true for products that use static linking or ship self-contained bundles. (nvd.nist.gov)
For WindowsForum readers, the practical takeaway is to audit not just installed packages, but also application-local DLLs, embedded runtimes, and installer payloads. Security teams should assume the vulnerable version may exist in more than one place, and one patched package does not prove the ecosystem is clean. (nvd.nist.gov)
The other thing to watch is whether additional libpng issues appear around the same release family. The presence of multiple recent libpng advisories is not proof of systemic failure, but it does show that the code base is under active security pressure. For defenders, that means more attention to maintenance cadence, fuzz coverage, and architecture-specific testing, particularly on ARM and AArch64 systems. (nvd.nist.gov)
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Overview
Overview
libpng is the canonical PNG reference implementation and a foundational dependency for countless applications, libraries, and embedded systems. The project’s longevity is part of the problem as well as the solution: decades of broad adoption mean that even niche bugs can propagate through large parts of the ecosystem. The official repository notes that libpng has been in extensive use since 1995 and that modern releases are still expected to preserve compatibility while continuing to evolve the internals. (github.com)What makes CVE-2026-33636 notable is not simply that it is a memory-safety bug. It is a memory-safety bug in a path intended to make PNG decoding faster on ARM and AArch64 systems, where Neon SIMD support is often enabled by default in performance-sensitive builds. That means the vulnerable code is not an obscure optional component; it is exactly the sort of optimized path vendors are likely to rely on for throughput, battery life, and latency. (nvd.nist.gov)
NVD describes the flaw as affecting libpng versions 1.6.36 through 1.6.55, with version 1.6.56 fixing the issue. The record also identifies the weakness classes as CWE-125 out-of-bounds read and CWE-787 out-of-bounds write, which is an important combination because the bug can both expose memory and corrupt it. (nvd.nist.gov)
The severity picture is also worth noting. GitHub’s CNA-assigned rating lands at CVSS 3.1 7.6 High, with the vector AV:N/AC:L/PR:N/UI:R/S:U/C:L/I:L/A:H. That profile suggests a network-reachable attack surface in applications that decode untrusted PNG content, while still requiring user interaction or a workflow step that causes a vulnerable component to process the file. (nvd.nist.gov)
A lot of the security conversation around image libraries focuses on code execution, but availability can be just as important. Microsoft’s update guide summary for the CVE emphasizes a total loss of availability in the impacted component, which aligns with the idea that even a relatively narrow memory bug can become a reliable denial-of-service vector when the decoder crashes or enters undefined behavior. That framing matters because many administrators triage “read” issues as lower risk than “write” issues, when in practice the operational fallout can be immediate and persistent. (nvd.nist.gov)
How the Vulnerability Works
The bug sits in the ARM/AArch64 Neon-optimized palette expansion logic. In plain English, libpng uses a specialized vectorized loop to expand indexed-color images into RGB or RGBA output, and that loop can mis-handle the last partial group of pixels when the row length is not an exact multiple of the vector width. Instead of safely falling back to scalar processing, the code steps past the start of the row buffer when it works backward from the end of the row. (nvd.nist.gov)That backward-processing strategy is central to understanding why the bug is dangerous. A vectorized routine often tries to process data in fixed-size blocks for speed, but once the row length leaves a remainder, the implementation has to either mask the tail carefully or switch to a safe cleanup path. Here, the tail case appears to be under-guarded, so the final iteration can dereference before the valid row memory and then write expanded pixel data into those underflowed positions. (nvd.nist.gov)
Why the tail case is hard
SIMD code is almost always more fragile at the boundaries than in the main loop. The main body processes predictable full-width blocks, but the last few elements require special handling, and that is where off-by-one assumptions tend to surface. In this case, the issue is not a classic arithmetic overflow; it is a failure to prove that the remaining pixels are sufficient before the loop consumes them. (nvd.nist.gov)That detail matters for defenders because it means fuzzing and edge-case input generation are particularly valuable. Vulnerabilities like this often hide in valid-but-unusual image dimensions, palette sizes, or row alignments, not only in obviously malformed files. The exploit condition can therefore be triggered by content that appears normal to users and automation alike. (nvd.nist.gov)
Read and write, not just read
The NVD entry explicitly describes both an out-of-bounds read and an out-of-bounds write. That duality increases concern because the bug is not limited to leaking adjacent memory; it also touches memory it should not modify. Even if the most likely outcome in real-world software is a crash, the write primitive should not be dismissed, because memory corruption can cause unpredictable downstream effects. (nvd.nist.gov)- The vulnerable code path is ARM/AArch64 Neon-specific.
- The issue is triggered during palette expansion from indexed PNGs.
- The bug affects both RGB and RGBA expansion modes.
- The tail handling is the likely failure point.
- The flaw is reachable with attacker-controlled PNG input. (nvd.nist.gov)
Exposure and Real-World Reach
The first question most operators ask is simple: who is exposed? The answer is broader than it may first appear, because libpng is embedded in operating systems, desktop applications, mobile apps, server-side image pipelines, and toolchains that process uploaded or downloaded images. Any application that decodes untrusted PNGs through affected libpng builds on AArch64 can potentially trip the bug. (nvd.nist.gov)The second question is whether the architecture restriction shrinks the risk enough to ignore. It does reduce the scope, but not by enough to be comforting. AArch64 is widespread in cloud infrastructure, mobile devices, SBCs, edge appliances, and modern desktops, and Neon support is a normal feature of that ecosystem rather than an exotic optional add-on. In other words, this is a targeted bug, but the target population is still large. (nvd.nist.gov)
Consumer impact versus enterprise impact
For consumers, the most likely impact is application instability. A malformed image received through a browser, messaging app, photo viewer, or thumbnailer can crash the process or force repeated restarts, especially where image previews are generated automatically. The attack model is annoyingly mundane: a user only needs to encounter the file in a vulnerable workflow. (nvd.nist.gov)For enterprises, the implications are more varied. Automated document ingestion, media scanning, content moderation, DAM systems, and image conversion pipelines often process untrusted files at scale. In those environments, a crash is not just an inconvenience; it can become a queue backlog, a failed job storm, or an outage in a service that depends on image normalization. That is how a decoder bug turns into an availability incident. (nvd.nist.gov)
A subtle point is that AArch64-heavy environments are often performance-tuned environments too. That means the very deployments most likely to enable SIMD acceleration are also the ones most sensitive to repeated crashes or degraded throughput. A vulnerability that seems architecture-specific can therefore have an outsized operational footprint in exactly the places where acceleration was chosen for business reasons. (nvd.nist.gov)
- Desktop image viewers may crash on malformed PNGs.
- Server-side thumbnailers may fail in batch processing.
- Mobile apps may abort when decoding received media.
- Embedded systems may become unavailable if image processing is part of a control path.
- Automation pipelines may repeatedly retry and amplify the outage. (nvd.nist.gov)
Severity and Attack Surface
The published CVSS 7.6 High score is a useful signal, but the vector tells the real story. Network attackable does not necessarily mean “wormable”; it means the attacker can get malicious PNG content into a workflow that processes it. The required user interaction element suggests a file-open or decode action, but in modern systems that interaction can be indirect, such as a preview pane, sync client, or backend ingest job. (nvd.nist.gov)The availability component is especially severe, with the NVD vector marking A:H. That aligns with Microsoft’s description of total loss of availability in the impacted component, which is a strong reminder that many operational risks are cumulative: a single crash may be tolerable, but repeated crashes in an automated pipeline can block legitimate work and create a cascading service incident. (nvd.nist.gov)
Why the read/write mix matters
An out-of-bounds read alone might primarily imply information disclosure and process instability. An out-of-bounds write raises the stakes because it can corrupt adjacent state, potentially causing more severe faults or enabling secondary exploitation if the surrounding memory layout is favorable. Even when no direct code execution is demonstrated, the write path increases uncertainty for defenders and vendors. (nvd.nist.gov)There is also an architectural nuance here. SIMD code paths sometimes have different memory access patterns from scalar code, which can influence both exploitability and crash consistency. That does not make the bug less important; it makes analysis harder, because behavior may vary by compiler, build flags, and CPU feature detection. In security terms, variability is not comfort. It is just another reason the issue needs patching rather than hand-waving. (nvd.nist.gov)
- Confidentiality impact is limited but non-zero.
- Integrity impact exists because the bug writes out of bounds.
- Availability impact is the clearest and most operationally relevant.
- Exploitability depends on whether a vulnerable build enables Neon.
- Risk is workload-dependent, especially for image ingestion services. (nvd.nist.gov)
Patch Status and Remediation
The clean fix is straightforward: upgrade to libpng 1.6.56. NVD marks the issue as fixed in that version, and the GitHub advisory linked from the record provides the vendor-side context and patches. For organizations that ship their own libpng builds, the practical task is not just upgrading a package, but confirming the bundled library version in every binary, image, and firmware image that includes libpng. (nvd.nist.gov)That last point is easy to underestimate. Image libraries are often statically linked, vendored, or embedded inside larger software distributions, which means a patched system package does not necessarily eliminate the vulnerable copy that matters. In enterprise environments, software composition analysis and binary inventory can be more important than apt or dnf output. (nvd.nist.gov)
Practical remediation steps
A sensible response plan should be short and systematic. First, inventory which products, images, and services include libpng. Second, determine whether those builds run on ARM or AArch64 and whether Neon is enabled. Third, update to the fixed release and verify the patched binary is the one actually loaded in production. Fourth, test image-heavy workflows for regressions, because optimized paths can change performance characteristics as well as security posture. (nvd.nist.gov)- Identify all software that links against libpng.
- Determine which deployments are AArch64/ARM.
- Check whether Neon acceleration is enabled.
- Upgrade to 1.6.56 or a vendor package that incorporates it.
- Validate the runtime library actually changed.
- Retest image ingestion and thumbnailing workloads. (nvd.nist.gov)
Why ARM/AArch64 Matters Here
It is tempting to treat architecture-specific bugs as niche, but ARM’s rise has made that distinction obsolete. AArch64 now powers a large share of cloud instances, developer laptops, phones, tablets, and appliances. As a result, a defect confined to Neon can still affect a huge installed base, especially if the library is built into software distribution channels that default to optimized paths. (nvd.nist.gov)The choice of Neon also reflects a broader trend in software engineering: performance work often lives closest to the metal, which means it often inherits the least safety margin. Hand-written assembly or intrinsics can outperform generic code, but they are also harder to reason about formally and harder to fuzz comprehensively. The security tradeoff is not theoretical; it is visible in recurring SIMD-related bugs across many projects. (nvd.nist.gov)
Performance and safety are now intertwined
Modern libraries are expected to be fast by default, yet the speedups come from code paths that tend to receive less everyday scrutiny than the scalar baseline. That creates a structural asymmetry: the fastest code path is often the one with the most delicate boundary logic and the smallest error budget. This vulnerability is a textbook example of that tension. (nvd.nist.gov)The lesson is not that vectorization is bad. The lesson is that vectorization without airtight bounds logic is security debt. Libraries like libpng have to balance compatibility, performance, and correctness, but once a security issue lands in the accelerated path, the cost of that balance becomes visible in the patch cycle. Fast code is only an asset if it stays in bounds. (nvd.nist.gov)
- ARM/AArch64 adoption widens the practical blast radius.
- Neon makes the bug more relevant to performance-tuned builds.
- SIMD paths need especially careful boundary checks.
- Security bugs in optimized code often evade casual testing.
- Architecture-specific fixes can still affect mainstream deployments. (nvd.nist.gov)
What This Means for Windows and Cross-Platform Software
Although libpng is not a Windows-only component, Windows ecosystems are not insulated from it. Cross-platform applications, game engines, graphics tools, and packaged runtimes frequently bundle third-party libraries, and many of those products ship to Windows, Linux, macOS, and ARM-based devices from the same source tree. That means a flaw discovered in an ARM-focused code path can still show up in Windows-adjacent software supply chains. (nvd.nist.gov)This is also where release engineering matters. The more a software vendor relies on upstream libraries, the more quickly it can consume a fixed release. But if the vendor vendors or forks the library, the security burden shifts inward, and patch latency becomes a function of internal build, QA, and sign-off cycles. That is especially true for products that use static linking or ship self-contained bundles. (nvd.nist.gov)
The supply-chain angle
One of the most important lessons from libpng vulnerabilities is that a CVE in a library rarely stays inside the library. It surfaces in the products that consume it, the scanners that flag it, and the platforms that inherit it through dependency chains. In a world where applications bundle their own graphics stacks, the effective patch surface is much larger than the obvious package manager view. (nvd.nist.gov)For WindowsForum readers, the practical takeaway is to audit not just installed packages, but also application-local DLLs, embedded runtimes, and installer payloads. Security teams should assume the vulnerable version may exist in more than one place, and one patched package does not prove the ecosystem is clean. (nvd.nist.gov)
- Bundled third-party libraries can carry vulnerable libpng copies.
- Static linking can hide the true version in production binaries.
- Cross-platform apps may inherit the bug without obvious ARM-only branding.
- Scanners should inspect application directories, not just system packages.
- Vendor patch timelines may vary widely. (nvd.nist.gov)
Strengths and Opportunities
The upside of a bug like this is that it is relatively straightforward to understand, classify, and remediate once identified. It also reinforces the value of upstream security work in mature open-source projects, where maintainers can push a fixed release and let downstreams consume it. If handled quickly, organizations can turn the event into a routine maintenance win rather than an incident. That is the best-case outcome. (nvd.nist.gov)- The fix is available in libpng 1.6.56.
- The flaw is well-scoped to a specific code path.
- CVE records, NVD, and vendor advisories align on the basics.
- Security teams can target AArch64 deployments first.
- The issue is suitable for inventory-based remediation.
- It encourages better SIMD path testing in CI.
- It highlights the value of upstream patch velocity. (nvd.nist.gov)
Risks and Concerns
The main concern is that seemingly narrow bugs in shared libraries can propagate into large, hard-to-observe service failures. If the library is embedded in a high-volume image workflow, the crash surface becomes a reliability problem rather than a one-off exploit question. The other concern is that the vulnerable path may be hidden in static builds or packaged applications, making it harder for defenders to know where they are exposed. (nvd.nist.gov)- Attackers can feed malicious PNGs through normal workflows.
- Repeated crashes can create a denial-of-service condition.
- Static or vendored builds can obscure exposure.
- SIMD boundary bugs are often hard to reproduce consistently.
- Monitoring tools may miss the library version actually in use.
- Automated image pipelines can amplify a small flaw into a larger outage.
- Partial mitigations may leave the vulnerable path reachable. (nvd.nist.gov)
Looking Ahead
The next phase to watch is downstream adoption of the patched release. Security issues in foundational libraries usually create a staggered response: upstream fixes first, then distribution packages, then application vendors, then embedded and appliance vendors. That stagger can be especially long in products that only refresh dependencies during major releases, which is why version tracking will matter over the coming weeks. (nvd.nist.gov)The other thing to watch is whether additional libpng issues appear around the same release family. The presence of multiple recent libpng advisories is not proof of systemic failure, but it does show that the code base is under active security pressure. For defenders, that means more attention to maintenance cadence, fuzz coverage, and architecture-specific testing, particularly on ARM and AArch64 systems. (nvd.nist.gov)
Key items to monitor
- Vendor packages that move to 1.6.56 or later.
- Products that silently bundle libpng in their installers.
- ARM/AArch64 systems that process untrusted images at scale.
- Reports of crashes in preview, thumbnail, or ingest pipelines.
- Follow-on advisories involving neighboring libpng code paths. (nvd.nist.gov)
Source: MSRC Security Update Guide - Microsoft Security Response Center