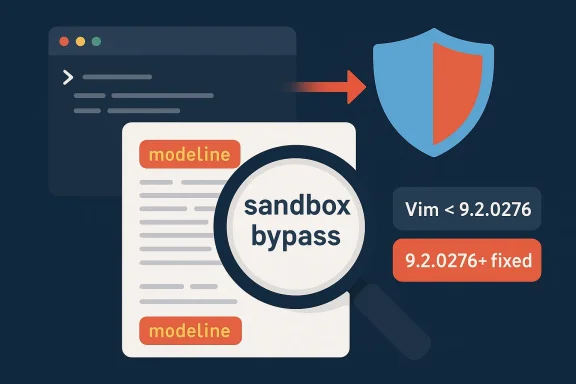
When a text editor becomes a code execution vector, the problem is no longer just a nuisance for developers; it becomes a supply-chain-style trust issue for every workstation that opens unvetted files. CVE-2026-34982 is a Vim modeline bypass that affects Vim versions earlier than 9.2.0276, and the practical consequence is grim: a crafted file can push the editor past its intended sandbox and into arbitrary OS command execution. The vulnerability is especially important because modelines are designed to make files portable and self-configuring, which means the attack surface is built into an everyday workflow rather than an obscure advanced feature.
Vim’s modeline system has always walked a delicate line between convenience and risk. It lets a file declare a small set of editor settings near the top or bottom of the document, so that indentation, wrapping, folding, or similar preferences travel with the file itself. That convenience is one reason the feature exists in the first place, but it also means attackers only need to persuade someone to open a weaponized file in a vulnerable editor.
The new issue is not the existence of modelines, but the fact that several option-processing paths were not constrained strongly enough. Public reporting around the advisory points to a sandbox bypass in which options such as complete, guitabtooltip, and printheader could be abused because security flags were missing or incomplete, and in one path
This is also a reminder that editor security bugs do not need network exposure to be dangerous. A local user opening a file from email, a repository, a shared drive, or a build artifact may be enough to trigger the flaw. In enterprise environments, that pattern is all too familiar: a trusted tool ingests an untrusted object, and the result is a privilege boundary collapse that is easy to overlook until incident response is already underway.
Vim fixed the issue in 9.2.0276, and the advisory chain now places that version as the relevant remediation point. That version number matters because patch guidance in package managers, distro backports, and vulnerability scanners often uses it as the practical cutoff for compliance checks. For many teams, the immediate question is not whether Vim is affected in theory, but whether their packaged build has picked up the fix or still reports a vulnerable upstream lineage.
The attack chain appears to rely on the modeline parser reaching an option-handling branch that should have been treated as secure but wasn’t. If an option can steer Vim into expression evaluation, mapping logic, or other behavior that interacts with shell commands or unsafe callbacks, the sandbox no longer protects the user. That is why the “bypass” label is so important: the flaw is not that modelines were never supposed to exist, but that their protective gate failed in certain paths.
That distinction has real operational impact. Security teams may already have controls that tolerate modelines because they are considered limited and familiar, but a bypass invalidates that trust. Once a feature is seen as a policy boundary, every exception becomes a potential exploit path.
The danger is amplified by the fact that the vulnerable content looks like ordinary text. Unlike a macro-enabled document or a binary payload, a malicious modeline can be buried in a file that otherwise appears harmless. That makes detection harder for humans and leaves more responsibility on the editor itself, which is exactly where the bug lived.
There is also a subtle but important ecosystem effect. Some distributions ship their own packages and may backport fixes without changing the upstream version string in obvious ways. Others may lag, especially in long-term-support repositories. So while 9.2.0276 is the upstream fix point, enterprise teams still need to verify what their package manager actually deployed on endpoints and servers.
The advisory also fits into a broader 2026 pattern: security teams have been issuing more editor, parser, and document-format advisories that trigger from single-file interactions. That matters because these are not classic remote exploits against internet-facing services; they are “open the thing” attacks that piggyback on human curiosity and routine developer behavior. That human factor is the real attack surface.
The patch guidance should also be read through the lens of workflow risk. Developers often trust files from repositories they clone, review, or build from, yet the malicious file can come from a contributor, a dependency archive, or even a generated artifact. That means the “just open it” scenario is not hypothetical; it is exactly how a lot of real-world developer interaction happens.
The risk profile is even worse when admin accounts are involved. An attacker who can get code execution in the context of a privileged user may be able to access configuration files, credentials, deployment scripts, or infrastructure keys. The real danger is not merely the editor process itself, but everything that account can reach once the shell command runs.
That makes policy the first line of defense. If teams do not need modelines, they should consider disabling them centrally. If they do need them, then they should pair that choice with strict patch management and tighter trust controls around what files can be opened in privileged sessions.
That history makes the latest advisory more instructive than alarming. It shows that hardening work is iterative, not one-and-done. A security boundary that blocks 99 paths but misses one option flag or one function call is still a broken boundary. The more flexible the feature, the more exacting the security review has to be.
For defenders, the takeaway is not to panic about every modeline. It is to understand that “safe by design” features still need continuous testing whenever they touch expressions, mappings, callbacks, or any other mechanism that can indirectly invoke the system shell. In security engineering, indirection is often where the exploit hides.
The impact is highest for people who work with code, logs, configuration files, or downloaded text artifacts. Those users are far more likely to encounter modelines and more likely to trust the files they open. The vulnerability therefore sits right in the middle of a common developer convenience pattern, which is exactly what makes it credible as an initial-access vector.
There is also a social engineering angle. A malicious file can be disguised as a patch, a configuration example, a log snippet, or a contribution from a colleague. Because Vim modelines are legitimate syntax, suspicious content may not stand out during quick review. That plausibility is part of the threat.
The competitive implication is less about one editor beating another and more about trust. Users who see repeated parser- or modeline-related issues may reevaluate how much untrusted automation they allow inside their editor sessions. Alternatives like disabling risky features, hardening default configs, or relying on stricter filetype detection may gain appeal even if the editor itself remains popular.
This also reinforces why packagers often backport fixes rather than wholesale rebasing. A targeted patch is easier to ship widely, easier to test, and less disruptive to users. In security terms, that is the ideal outcome: a quiet fix that closes the hole without forcing a major version jump.
There is also a broader lesson for toolmakers: features that parse attacker-controlled text must be treated as mini-interpreters, not simple preferences. Whenever a preference can influence mappings, callbacks, or expression evaluation, the code should be reviewed as if it were a scripting surface. That is the only realistic way to keep convenience from becoming code execution.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Overview
Overview
Vim’s modeline system has always walked a delicate line between convenience and risk. It lets a file declare a small set of editor settings near the top or bottom of the document, so that indentation, wrapping, folding, or similar preferences travel with the file itself. That convenience is one reason the feature exists in the first place, but it also means attackers only need to persuade someone to open a weaponized file in a vulnerable editor.The new issue is not the existence of modelines, but the fact that several option-processing paths were not constrained strongly enough. Public reporting around the advisory points to a sandbox bypass in which options such as complete, guitabtooltip, and printheader could be abused because security flags were missing or incomplete, and in one path
mapset() lacked a check_secure() call. That matters because Vim’s security model assumes expression-like features are heavily fenced off when a file is merely being viewed or opened.This is also a reminder that editor security bugs do not need network exposure to be dangerous. A local user opening a file from email, a repository, a shared drive, or a build artifact may be enough to trigger the flaw. In enterprise environments, that pattern is all too familiar: a trusted tool ingests an untrusted object, and the result is a privilege boundary collapse that is easy to overlook until incident response is already underway.
Vim fixed the issue in 9.2.0276, and the advisory chain now places that version as the relevant remediation point. That version number matters because patch guidance in package managers, distro backports, and vulnerability scanners often uses it as the practical cutoff for compliance checks. For many teams, the immediate question is not whether Vim is affected in theory, but whether their packaged build has picked up the fix or still reports a vulnerable upstream lineage.
How the Modeline Attack Surface Works
Modelines are a long-standing Vim feature, and by design they only allow a narrow class of settings. That restriction was introduced precisely because unrestricted command execution through file metadata would be unacceptable. Yet CVE-2026-34982 shows how security bugs can still emerge when an option is technically “just a setting” but internally reaches deeper code paths than intended.The attack chain appears to rely on the modeline parser reaching an option-handling branch that should have been treated as secure but wasn’t. If an option can steer Vim into expression evaluation, mapping logic, or other behavior that interacts with shell commands or unsafe callbacks, the sandbox no longer protects the user. That is why the “bypass” label is so important: the flaw is not that modelines were never supposed to exist, but that their protective gate failed in certain paths.
Why a Bypass Is Worse Than a Simple Bug
A straightforward crash is bad, but a bypass is more strategically valuable to an attacker. It means the defenders already have a mental model of the risk, and the attacker’s job is to find the seam in that model. In this case, the seam is the assumption that modeline-initiated changes stay safely boxed inside a restricted option set.That distinction has real operational impact. Security teams may already have controls that tolerate modelines because they are considered limited and familiar, but a bypass invalidates that trust. Once a feature is seen as a policy boundary, every exception becomes a potential exploit path.
The danger is amplified by the fact that the vulnerable content looks like ordinary text. Unlike a macro-enabled document or a binary payload, a malicious modeline can be buried in a file that otherwise appears harmless. That makes detection harder for humans and leaves more responsibility on the editor itself, which is exactly where the bug lived.
What the New Advisory Adds
The most important contribution of the CVE-2026-34982 disclosure is specificity. Rather than treating this as a vague “Vim security issue,” the advisory ties the flaw to a precise affected range: Vim < 9.2.0276. That gives administrators a clean remediation target and helps vulnerability management tools distinguish patched builds from older ones.There is also a subtle but important ecosystem effect. Some distributions ship their own packages and may backport fixes without changing the upstream version string in obvious ways. Others may lag, especially in long-term-support repositories. So while 9.2.0276 is the upstream fix point, enterprise teams still need to verify what their package manager actually deployed on endpoints and servers.
The advisory also fits into a broader 2026 pattern: security teams have been issuing more editor, parser, and document-format advisories that trigger from single-file interactions. That matters because these are not classic remote exploits against internet-facing services; they are “open the thing” attacks that piggyback on human curiosity and routine developer behavior. That human factor is the real attack surface.
Patch Priority and Upgrade Signal
For affected users, the remediation message is simple: upgrade to Vim 9.2.0276 or later. If patching is not immediately possible, the most conservative temporary measure is to disable modelines entirely withset nomodeline in local configuration, though that trades away functionality for safety. That workaround is blunt, but in the short term it cuts off the attack path described in the advisory.The patch guidance should also be read through the lens of workflow risk. Developers often trust files from repositories they clone, review, or build from, yet the malicious file can come from a contributor, a dependency archive, or even a generated artifact. That means the “just open it” scenario is not hypothetical; it is exactly how a lot of real-world developer interaction happens.
Why This Matters for Enterprise Environments
Enterprises should care about this vulnerability even if they think Vim is “just a terminal tool.” Many engineering, operations, and security teams still use Vim directly on production jump hosts, admin boxes, container shells, and remote maintenance sessions. In those contexts, a successful file-open exploit can land in a very sensitive workspace with elevated trust and broad reach.The risk profile is even worse when admin accounts are involved. An attacker who can get code execution in the context of a privileged user may be able to access configuration files, credentials, deployment scripts, or infrastructure keys. The real danger is not merely the editor process itself, but everything that account can reach once the shell command runs.
Operational Consequences
This sort of issue is difficult for defenders because it sits between software inventory and behavior monitoring. Asset management may show that Vim is installed, but it does not show which users regularly open untrusted files or which automation jobs invoke it. Meanwhile, endpoint detection may not have enough context to decide whether a spawned shell from Vim is legitimate or malicious.That makes policy the first line of defense. If teams do not need modelines, they should consider disabling them centrally. If they do need them, then they should pair that choice with strict patch management and tighter trust controls around what files can be opened in privileged sessions.
The Historical Context of Vim Modeline Bugs
This is not the first time Vim’s modeline machinery has been implicated in a security issue. The editor has a long history of hardening around expression handling, secure mode, and restricted settings because the design goal is inherently risky: allow file-local customization without allowing file-local code execution. The recurring lesson is that the edge cases are where attackers win.That history makes the latest advisory more instructive than alarming. It shows that hardening work is iterative, not one-and-done. A security boundary that blocks 99 paths but misses one option flag or one function call is still a broken boundary. The more flexible the feature, the more exacting the security review has to be.
Comparing This with Earlier Modeline Issues
Earlier modeline-related flaws helped establish the pattern: attacker-controlled text, parser confusion, and a route from “editor preference” to “action execution.” CVE-2026-34982 follows that same logic, but with a newer and more nuanced twist in the option-handling internals. That suggests the upstream project has improved the obvious attack paths, while the long tail of configuration and option semantics still deserves scrutiny.For defenders, the takeaway is not to panic about every modeline. It is to understand that “safe by design” features still need continuous testing whenever they touch expressions, mappings, callbacks, or any other mechanism that can indirectly invoke the system shell. In security engineering, indirection is often where the exploit hides.
Consumer Impact and Developer Workflow
For individual users, the risk is easiest to understand in plain terms: opening the wrong file in an old Vim build could run commands on your machine. That is enough to justify updating even if you only use Vim occasionally. Consumer users may not think of themselves as high-value targets, but malicious documents and code samples often circulate widely and opportunistically.The impact is highest for people who work with code, logs, configuration files, or downloaded text artifacts. Those users are far more likely to encounter modelines and more likely to trust the files they open. The vulnerability therefore sits right in the middle of a common developer convenience pattern, which is exactly what makes it credible as an initial-access vector.
Why Developers Should Pay Extra Attention
Developers sometimes run editors in shells with broad permissions, shared mounts, or access to source trees and secrets. That makes the blast radius of a malicious file much larger than a casual consumer desktop scenario. Even if the exploit only executes as the current user, the current user in a dev workflow can already be very powerful.There is also a social engineering angle. A malicious file can be disguised as a patch, a configuration example, a log snippet, or a contribution from a colleague. Because Vim modelines are legitimate syntax, suspicious content may not stand out during quick review. That plausibility is part of the threat.
The Broader Competitive and Ecosystem Implications
Vim remains a foundational tool in the Unix and Linux ecosystem despite the rise of modern editors and IDEs. That means a security flaw in Vim has a ripple effect across distros, appliance images, developer environments, containers, and remote administration workflows. Once a vulnerability like this lands, downstream maintainers have to decide whether to fast-track packages, backport fixes, or leave older releases exposed for longer than they’d like.The competitive implication is less about one editor beating another and more about trust. Users who see repeated parser- or modeline-related issues may reevaluate how much untrusted automation they allow inside their editor sessions. Alternatives like disabling risky features, hardening default configs, or relying on stricter filetype detection may gain appeal even if the editor itself remains popular.
Implications for Linux Distros and Packagers
Distribution maintainers are now on the hook to communicate not just that a Vim package is “updated,” but that the security-relevant patch is present. That can be surprisingly hard when the underlying source tree is stable and only a small subset of builds are vulnerable. As a result, vulnerability databases and package metadata become operational tools, not just documentation.This also reinforces why packagers often backport fixes rather than wholesale rebasing. A targeted patch is easier to ship widely, easier to test, and less disruptive to users. In security terms, that is the ideal outcome: a quiet fix that closes the hole without forcing a major version jump.
Strengths and Opportunities
The upside of this disclosure is that it comes with a clear fix and a clear mitigation path. That is the best-case scenario for defenders because it turns a subtle exploit chain into an actionable patch-management task. It also gives organizations a chance to review broader editor-hardening policies before the next issue appears.- Clear fixed version: Vim 9.2.0276 provides a concrete remediation target.
- Easy temporary mitigation:
set nomodelinecan break the attack chain quickly. - Low-friction update path: Most users can patch through normal package channels.
- Policy review opportunity: Teams can reassess whether modelines are needed at all.
- Security tooling improvement: Scanners can flag pre-9.2.0276 builds more reliably.
- Hardening lesson: The issue encourages stricter treatment of option paths and secure flags.
- Workflow awareness: Developers may become more cautious about opening untrusted files in privileged sessions.
Risks and Concerns
The main concern is that this exploit lives inside a feature many users perceive as benign. That perception gap makes social engineering easier and increases the odds that an attacker can sneak a malicious file into routine workflows. It also means some teams may underestimate the urgency because the entry point is “just a text editor.”- User trust in text files: Malicious payloads can hide in otherwise harmless-looking content.
- Privilege amplification: Admin or power-user sessions magnify the impact.
- Patch lag: Older packaged builds may remain exposed longer than upstream versions suggest.
- Detection challenges: Security tools may not distinguish benign from malicious shell execution inside Vim.
- Feature reliance: Some teams may resist disabling modelines due to workflow disruption.
- Downstream inconsistency: Distro backports may make inventory and compliance checks messy.
- Historical repetition: Modeline-related bugs suggest a recurring hardening burden.
What to Watch Next
The key question now is not whether the bug exists, but how quickly ecosystems close the exposure window. If past Vim issues are any guide, the upstream fix will spread unevenly across distributions, appliance images, and enterprise base images. Security teams should expect a patch-management tail rather than a clean overnight resolution.There is also a broader lesson for toolmakers: features that parse attacker-controlled text must be treated as mini-interpreters, not simple preferences. Whenever a preference can influence mappings, callbacks, or expression evaluation, the code should be reviewed as if it were a scripting surface. That is the only realistic way to keep convenience from becoming code execution.
- Distro backports: Watch how quickly major Linux and BSD packages pick up the fix.
- Enterprise inventories: Check whether compliance tools recognize the patched build correctly.
- Behavioral detection: Monitor for suspicious shell spawning from editor processes.
- Modeline policy: Decide whether to disable the feature globally or selectively.
- Upstream hardening: Look for follow-up changes to option security flags and secure checks.
Source: MSRC Security Update Guide - Microsoft Security Response Center