CVE-2026-3633 is a reminder that the most dangerous bugs are not always memory corruptions or flashy remote code execution chains; sometimes they are one malformed string away from letting an attacker reshape an HTTP request. In libsoup, a remote attacker who controls the
This is not the fir* ecosystem has been in the security spotlight. The library is a long-standing HTTP client and server component used by GNOME and other software, and Red Hat’s advisories repeatedly describe it as the HTTP layer that many higher-level products depend on. That matters because a vulnerability in a foundational networking library often propagates far beyond the library’s own name. It can end up affecting desktop software, middleware, container images, and enterprise appliances that quietly embed the code.
The NVD record shows that Red Hat’s inited the issue with several enterprise Linux CPEs, including Red Hat Enterprise Linux 6 through 10, plus
There is also an important operational detail in the descriptgered by control over the
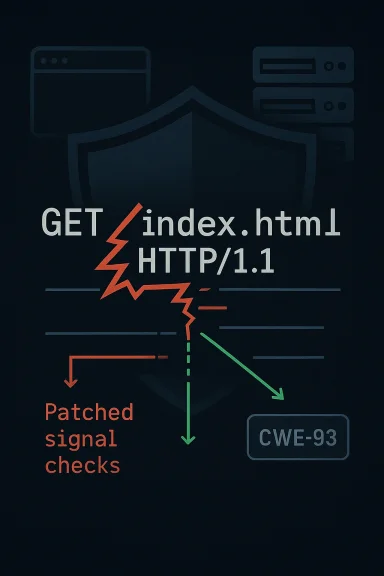
CRLF injection has been a recurring problem across HTTP stacks for ill relies on textual framing semantics. If an attacker can get carriage return and line feed characters into a place the library assumes is inert, they may be able to terminate a line early and start a new header, or even append extra request material that the application never intended to send. That is why the weakness is cataloged as CWE-93 and why it is often treated as a protocol boundary failure rather than a mere formatting bug.
In libraries like libsoup, request construction sits at a sensitive point in the stack. The code islication intent—target URL, method, headers, body—and turn it into a compliant HTTP message. When that translation step fails to sanitize control characters properly, the library becomes the attacker’s protocol authoring tool. That is a particularly ugly failure mode because it can affect outbound requests, upstream proxies, authentication gateways, or anything else that consumes the crafted traffic.
The broader history of libsoup vulnerabilities shows a pattern familiar to anyone who tracks middleware and protocol librari does the heavy lifting for a large ecosystem, so any flaw in parsing, framing, or validation can ripple widely. Red Hat’s advisories identify libsoup as an HTTP client and server library for GNOME, and other security entries in the same family show how often the package appears in enterprise maintenance streams. In other words, this is a small code path with an outsized footprint.
Microsoft’s Security Update Guide also lists CVE-2026-3633, which is notable even though the page content is sparse in the material provided. Thassue has crossed from upstream project concern into downstream ecosystem relevance. For Windows admins and mixed-environment teams, that matters because Linux-derived containers, WSL-based tools, and cross-platform dependencies can surface the library in places that are easy to forget during patch planning.
The most important lesson from the background is not that libsoup has a bug; it is that protocol libraries are only as safe as the assumptions they enforce. If a methRLF sequences into a request line, then the library is not merely mishandling input—it is failing to preserve the semantic integrity of HTTP itself. That is why these issues attract security attention quickly and why they often require both upstream fixes and downstream backports.
A practical exploitation path would likely rely on an application that accepts or derives the method from external input without canonicalization. That might sound unusual, but real-world systems often do odd things with method orations, tunneling helpers, or custom request builders. The risk is highest when developers believe the method is a safe enum-like value but fail to enforce that assumption at the boundary.
In security terms, that is why CRLF injection is especially nasty: it is not always about stealing data directly. Sometimes it is about making a system speak with a forged voice, and that can be enough to undermine trust in the request chain. For enterprise operators, thtextual, which makes detection harder than with a straightforward crash or memory fault.
This is particularly relevant for organizations that build appliances or platform images on top of Linux distributions. A custom image may inherit libsoup through a dependency chain that nobody notices until a security scanner or advisory flags it. At that point, remediation can take longer because teams have to rebuild images, rerun tests, and redeploytiple environments.
The most likely real-world pattern is not a dramatic public exploit but a chain of subtle failures: malformed request construction, a confused proxy, a rejected upstream call, and a hard-to-trace application error. That is why such issues are often underappreciated until they show up in incident reports or targeted abuse. Silent protocol corruption can be harder to diagnose than a crash becau like normal network weirdness.
The danger is increased when developers wos and assume the library is doing all necessary validation for them. Convenience functions are attractive because they reduce boilerplate, but they also hide the exact boundary between input and protocol output. If that boundary is not clearly documented and enforced, misuse becomes almost inevitable in larger codebases.
That is why request smuggling-adjacent bugs are treated seriously even when the initial report sounds narrow. A malformed be the beginning of a much wider misinterpretation cascade. Depending on the architecture, that can create a security issue, an availability issue, or both.
The fact that the NVD page includes Red Hat’s own CVSS assessment, along with its own CPE mapping, is also revealing. It suggests that the ans on the vendor’s understanding of how the flaw manifests in packaged environments. That tends to be more actionable than a generic score because it reflects actual deployment realities.
For Windows-centric teams, the lesson is straightforward: if your environment touches Linuxpelines, or cross-platform clients, do not assume a “Linux library” stays on the Linux side of the fence. Security ownership in 2026 is increasingly ecosystem-wide, and patch responsibilities follow the software graph, not just the OS brand.
This is also a reminder that availability and integrity often travel together in library bugs. A maliciously shaped request can cause downstream rejections, retries, cache weirdness, or failed authenticatioirect impact is not a crash. Security teams should therefore watch not only for compromise indicators but also for unexplained request anomalies after patching.
For WindowsForum readers managing026-3633 is a good example of why Linux library CVEs still belong on the Windows admin radar. The software supply chain no longer respects platform silos, and neither do attackers. If your environment runs containers, gateways, desktop tooling, or cross-platform services that touch libsoup, this is one of those vulnerabilities that should move from “interesting” to “actionable” immediately.
CVE-2026-3633 is, at heart, a lesson in how protocol integrity fails when a library trusts a string it should have treated as hostile. The fix will likely be straightforward compared with the downstream cleanup, but the real work is broader: confirming where libsoup lives, how method values flow through your applications, and whether any component in your stack can still be persuaded to emit a malformed HTthat kind of discipline is not optional; it is what keeps small parsing flaws from becoming large operational problems.
Source: NVD Security Update Guide - Microsoft Security Response Center
method parameter passed to soup_message_new() can inject arbitrary headers and additional request data because the method value is not properly escaped during request-line construction, creating a classic CRLF injection condition. The vulnerability is tracked as CWE-93, and the initial NVD entry ties the issue to Red Hat’s disclosure and to downstream package exposure across multiple enterprise Linux generations. re problem with CVE-2026-3633 is deceptively simple: HTTP request construction is supposed to treat control characters as toxic, but in this case the method string can influence the request line in a way that permits header smuggling and extra request material. That means the bug is not just about malformed formatting; it is about breaking the trust boundary between application input and wire-level protocol structure. The result can range from request manipulation to unintended backend behavior, depending on how the library is used.This is not the fir* ecosystem has been in the security spotlight. The library is a long-standing HTTP client and server component used by GNOME and other software, and Red Hat’s advisories repeatedly describe it as the HTTP layer that many higher-level products depend on. That matters because a vulnerability in a foundational networking library often propagates far beyond the library’s own name. It can end up affecting desktop software, middleware, container images, and enterprise appliances that quietly embed the code.
The NVD record shows that Red Hat’s inited the issue with several enterprise Linux CPEs, including Red Hat Enterprise Linux 6 through 10, plus
cpe:2.3:a:gnome:libsoup:-:*:*:*:*:*:*:*. That is a broad signal, not a narrow one. It tells defenders to think in terms of packaged dependencies, backports, and transitive exposure rather than just source-level version numbers.There is also an important operational detail in the descriptgered by control over the
method parameter, not necessarily by a full compromise of the application. In practice, that means developers who assume a method string is always harmless or constrained to a small set of HTTP verbs may be in trouble if they pass user-controlled values through convenience wrappers without validation. That is a design-level trap*, and it is exactly the kind of subtle input mistake that gets missed until a security advisory forces the issue.
 Background
Background
CRLF injection has been a recurring problem across HTTP stacks for ill relies on textual framing semantics. If an attacker can get carriage return and line feed characters into a place the library assumes is inert, they may be able to terminate a line early and start a new header, or even append extra request material that the application never intended to send. That is why the weakness is cataloged as CWE-93 and why it is often treated as a protocol boundary failure rather than a mere formatting bug.In libraries like libsoup, request construction sits at a sensitive point in the stack. The code islication intent—target URL, method, headers, body—and turn it into a compliant HTTP message. When that translation step fails to sanitize control characters properly, the library becomes the attacker’s protocol authoring tool. That is a particularly ugly failure mode because it can affect outbound requests, upstream proxies, authentication gateways, or anything else that consumes the crafted traffic.
The broader history of libsoup vulnerabilities shows a pattern familiar to anyone who tracks middleware and protocol librari does the heavy lifting for a large ecosystem, so any flaw in parsing, framing, or validation can ripple widely. Red Hat’s advisories identify libsoup as an HTTP client and server library for GNOME, and other security entries in the same family show how often the package appears in enterprise maintenance streams. In other words, this is a small code path with an outsized footprint.
Microsoft’s Security Update Guide also lists CVE-2026-3633, which is notable even though the page content is sparse in the material provided. Thassue has crossed from upstream project concern into downstream ecosystem relevance. For Windows admins and mixed-environment teams, that matters because Linux-derived containers, WSL-based tools, and cross-platform dependencies can surface the library in places that are easy to forget during patch planning.
The most important lesson from the background is not that libsoup has a bug; it is that protocol libraries are only as safe as the assumptions they enforce. If a methRLF sequences into a request line, then the library is not merely mishandling input—it is failing to preserve the semantic integrity of HTTP itself. That is why these issues attract security attention quickly and why they often require both upstream fixes and downstream backports.
How the Vulnerability Works
At a technical level, the issue centers on howsoup_message_new() turns its arguments into the first line of an HTTP request. If the method argumente concatenation, embedded carriage returns and line feeds can alter the structure of the generated request. The attacker then gains leverage over the headers or the body that follow, which is the essence of HTTP request injection.The request-line problem
The request line is supposed to be predictable: method, target, protocol version. If the method can contain control characters, it stops being a method and becomes a payload carr is critical, because downstream components generally trust the request line to delimit message semantics. Once those delimiters are broken, the bug can cross from input validation into request smuggling territory.A practical exploitation path would likely rely on an application that accepts or derives the method from external input without canonicalization. That might sound unusual, but real-world systems often do odd things with method orations, tunneling helpers, or custom request builders. The risk is highest when developers believe the method is a safe enum-like value but fail to enforce that assumption at the boundary.
What attackers can inject
The vulnerability description explicitly mentions arbitrary headers and additional request data. That means an attacker may be able to influence not just a single field but the shape of the entire outbound request. In te adversary, that can alter authentication context, confuse logging, poison upstream caches, or create unexpected interactions with proxy layers.In security terms, that is why CRLF injection is especially nasty: it is not always about stealing data directly. Sometimes it is about making a system speak with a forged voice, and that can be enough to undermine trust in the request chain. For enterprise operators, thtextual, which makes detection harder than with a straightforward crash or memory fault.
- Method control can become request control if the string is not escaped.
- Header injection can change downstream authorization or routing behavior.
- Additional request data can confuse parsers and proxies.
- Logging systems may record a forged request shape, complicatiy this is more than a formatting bug
Affected Exposure
The published material points to broad enterprise Linux coverage, which implies downstream packages and rebuilds may be exposed even when the upstream source has already been fixed. Red Hat’s change history associates the issue with RHEL 6, 7, 8, 9, and 10 CPEs, plus the GNOME libsoup is a classic sign that security teams need to check vendor advisories rather than rely on version strings alone.Enterprise packaging matters
In modern enterprise environments, the same vulnerable library can appear in multiple forms: base OS packages, container layers, SDK images, middleware bundles, and application runtimes. A patch in one place does not guarantee protection everywhere else. The NVD record’s broad CPE listing is a warnihould be inventory-driven, not assumption-driven.This is particularly relevant for organizations that build appliances or platform images on top of Linux distributions. A custom image may inherit libsoup through a dependency chain that nobody notices until a security scanner or advisory flags it. At that point, remediation can take longer because teams have to rebuild images, rerun tests, and redeploytiple environments.
Consumer impact is indirect but real
Consumers are less likely to see “libsoup” in a changelog, but they may still feel the impact through desktop apps, update tools, or client software that embeds the library. In those cases, the symptom may be broken connectivity, unusual request behavior, or a feature that fails in response to a hostile endpoint. The bug is still thnever sees the name of the component.The most likely real-world pattern is not a dramatic public exploit but a chain of subtle failures: malformed request construction, a confused proxy, a rejected upstream call, and a hard-to-trace application error. That is why such issues are often underappreciated until they show up in incident reports or targeted abuse. Silent protocol corruption can be harder to diagnose than a crash becau like normal network weirdness.
- RHEL backports may carry the fix even when the upstream version number looks old.
- Container images may remain vulnerable after host patching.
- Desktop applications can inherit the bug transitively.
- Proxy chains can amplify the consequences of injected request structure.
Why CRLF Injection Still Matters
It is tempting to think of CRLF injection as an old bug class that modern framewosince eliminated. The reality is more frustrating: any place that transforms user-controlled strings into protocol syntax remains vulnerable if escaping is incomplete. HTTP is full of such seams, which is why this class of vulnerability keeps reappearing in different forms.Protocol semantics are fragile
HTTP depends on line-oriented separators, and that makes its syntax unusually sensitive to control characters. If a library gets the escaping rules wrong, the attacker can alter structure rather than content. That is a major difference, because content bugs are usually confined to a field, while structure bugs can redefine the meaning of an entire message.The danger is increased when developers wos and assume the library is doing all necessary validation for them. Convenience functions are attractive because they reduce boilerplate, but they also hide the exact boundary between input and protocol output. If that boundary is not clearly documented and enforced, misuse becomes almost inevitable in larger codebases.
The attack surface in modern applications
Modern apps rarely speak e. They talk to APIs, reverse proxies, gateways, microservices, monitoring systems, and third-party services. A request injection flaw in one library can therefore affect authentication flows, audit trails, retries, or even service-to-service trust assumptions.That is why request smuggling-adjacent bugs are treated seriously even when the initial report sounds narrow. A malformed be the beginning of a much wider misinterpretation cascade. Depending on the architecture, that can create a security issue, an availability issue, or both.
- HTTP’s syntax makes control characters especially dangerous.
- Convenience APIs can hide unsafe concatenation.
- Proxy and gateway layers may magnify the effect.
- Audit logs can bhe wire format itself is attacker-shaped.
Red Hat, NVD, and Microsoft: What the Metadata Signals
The NVD record for CVE-2026-3633 is still in an enrichment phase, but the associated references already tell a useful story. Red Hat is the source of the primary disclosure, Bugzilla tracks the isse GNOME libsoup GitLab issue points to the upstream project’s handling of the bug. Those three anchors together are enough to establish this as a real, multi-layered supply-chain concern rather than an isolated report.Why vendor advisories matter
Vendor advisories matter because they define the patchable reality that most administrators actually live in. Upstream may fix a bug in source code, but downstream distros frequently backport the correction into older branches with different version numbers. That makes the vendor advisory, not the raw version label, the authoritative guide for many operations teams.The fact that the NVD page includes Red Hat’s own CVSS assessment, along with its own CPE mapping, is also revealing. It suggests that the ans on the vendor’s understanding of how the flaw manifests in packaged environments. That tends to be more actionable than a generic score because it reflects actual deployment realities.
The Microsoft listing is a clue, not the whole answer
Microsoft’s update guide entry indicates that the CVE is relevant enough to appear in its security ecosystem, but the page itself does not provide the sameream exploit write-up or a detailed vendor advisory. That means operators should treat it as a signal to verify packaging, not as a complete remediation guide. In practice, cross-referencing sources is what turns a CVE identifier into a useful patch plan.For Windows-centric teams, the lesson is straightforward: if your environment touches Linuxpelines, or cross-platform clients, do not assume a “Linux library” stays on the Linux side of the fence. Security ownership in 2026 is increasingly ecosystem-wide, and patch responsibilities follow the software graph, not just the OS brand.
- Red Hat provides the most operationally relevant disclosure context here.
- NVD confirms broad CPE mapping across enterprise releases.
- GNOME’s upstream issue tracker anchors the technical root cause.
- Microsoft’s listing shows thewnstream relevance beyond the original package ecosystem.
Practical Risk to Administrators
Administrators should think about CVE-2026-3633 as a request integrity issue first and a vulnerability label second. If any internal application accepts user influence over HTTP method creation, that path should be reviewed immediately. The safest assumpted method parameter, method override, or request-builder hook is potentially dangerous until proven otherwise.Where to look first
The highest-risk code is anything that builds outbound HTTP requests from dynamic inputs. That includes proxy adapters, custom API clients, integration services, automated test harnesses, and middleware that normalizes request verbs. If the application uses libsoup directly or indirectly, the security team should confirm whether the fixed build has actually been deployed to the runtime image or host package.This is also a reminder that availability and integrity often travel together in library bugs. A maliciously shaped request can cause downstream rejections, retries, cache weirdness, or failed authenticatioirect impact is not a crash. Security teams should therefore watch not only for compromise indicators but also for unexplained request anomalies after patching.
What patching should include
The answer is not merely “update libsoup.” It is also “rebuild the image,” “redeploy the container,” “restart the service,” and “verify the binary in memory is the fixed one.” That sounds tedious, but in library CVEs it is the only way to be ed. Old processes can continue running stale code long after package managers report success.- Inspect all code paths that pass external input into
soup_message_new(). - Confirm distro backports, not just upstream version numbers.
- Rebuild containers and appliances that bundle the library.
- Restart services to ensure the patched library is actually loaded.
- Monitor for request anent.
Operational Response Checklist
A sensible response plan starts with inventory, because you cannot patch what you do not know you run. From there, the goal is to determine whether libsoup is present directly, whether it is present transitively, and whether any code path gives an attacker influence over the HTTP method string. That triage sequence is simple, but it saves a lot ### Step-by-step triage- Identify packages, containers, and applications that include libsoup.
- Determine whether your build or runtime uses
soup_message_new()directly. - Check vendor advisories and backported package changelogs for the fixed build.
- Rebuild and redeploy any image or binary that still contains the vulnerable library.
- Validate in logs and packet captures that request structure is no longer attacker-influenced.
Logging and detection
Detection is difficult because the symptom may be subtle. Administrators should review logs for malformed request lines, unexpected header boundaries, and any sign that a request was parsed differently than it was originally constructed. In addition, if requests are generated through a service mesh or API gateway, those components may provide secondary evidence of injected structure or rejected line breaks.- Inventory first, patch second.
- Look for transitive dependencies, not just direct ones.
- Treat container rebuilds as mandatory.
- Use logging and packet inspection to confirm the fix.
- Assume old runtime processes are still vulnerable until restarted.
Strengths and Opportunities
There like CVE-2026-3633 is that it gives organizations a concrete prompt to clean up a class of brittle request-construction code that should probably have been hardened long ago. It also creates an opportunity to audit how much trust the software stack places in protocol syntax. That is useful work even outside the immediate CVE.- The bug has a clear root cause, which makes remediation easier to validate.
- The flaw is in a **wellso code review can be targeted.
- Vendor and upstream references already exist, which helps with patch correlation.
- The issue encourages teams to improve input validation for all protocol builders.
- Security tooling can look for CRLF patterns and suspicious request-line composition.
- The advisory may drive broader cleanup of legacy HTTP helper code.
- It offers a chance to document safe method handling across internal libraries.
Risks and Concerns
The biggest concern is that request injection bugs are often underestimated because they do not always cause immediate crashes. Instead, they silently alter protocol behavior, which ystems that rely on proxies, chained services, or strict request semantics. That makes the issue harder to spot and potentially easier to abuse in targeted environments.- The flaw can enable header injection and extra request data.
- Affected code may exist in transitive dependencies that teams do not track closely.
- Patches may be missed if teams rely only on upstream version numbers.
- Logging can become misleading if the attacker manipulates request structure.
- Internal apps may mistakenly assume method values are safe by design.
- Proxy chains can magnify the impact of a single malformed request.
- Legacy deployments may remain exposed if they are no longer in active maintenance.
What to Watch Next
The next things to watch are the availability of fixed packages, downstream advisories from distribution vendors, and any clarification from upstream about the exact affected release range. Because the public record currently emphasizes t than its full deployment matrix, the practical answer for operators is to verify package state rather than wait for perfect documentation. That is especially true in enterprise environments where backports are common.Watch list
- Vendor package updates for RHEL 6 through 10 and related rebuilds.
- Upstream libsoup issue updates and any linked fix commits.
- Container image rebuilds in middleware and developer toolchains.
- Security scanner signatures for CWE-93 / CRLF injection patterns.
- Internal code reviews for method parameters that can be influenced by users.
For WindowsForum readers managing026-3633 is a good example of why Linux library CVEs still belong on the Windows admin radar. The software supply chain no longer respects platform silos, and neither do attackers. If your environment runs containers, gateways, desktop tooling, or cross-platform services that touch libsoup, this is one of those vulnerabilities that should move from “interesting” to “actionable” immediately.
CVE-2026-3633 is, at heart, a lesson in how protocol integrity fails when a library trusts a string it should have treated as hostile. The fix will likely be straightforward compared with the downstream cleanup, but the real work is broader: confirming where libsoup lives, how method values flow through your applications, and whether any component in your stack can still be persuaded to emit a malformed HTthat kind of discipline is not optional; it is what keeps small parsing flaws from becoming large operational problems.
Source: NVD Security Update Guide - Microsoft Security Response Center