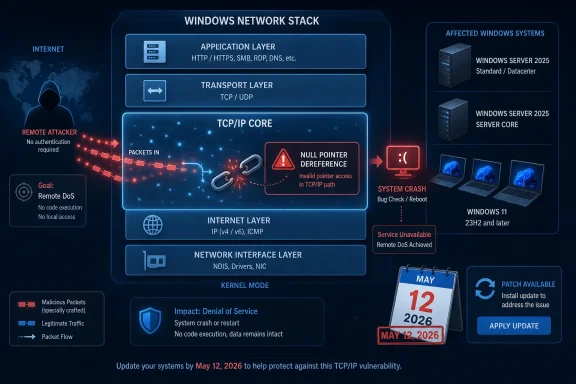
Microsoft disclosed CVE-2026-40405 on May 12, 2026, as an Important-rated Windows TCP/IP denial-of-service vulnerability caused by a null pointer dereference that lets an unauthenticated attacker deny service over the network on affected Windows 11 and Windows Server 2025 systems. The plain-English version is less dramatic than a wormable remote-code-execution bug, but more operationally relevant than the word “Important” can make it sound. This is a network-stack crash-class issue, and network-stack bugs do not need phishing, macros, or user mistakes to matter. The real story is not that attackers get code execution; it is that Microsoft is telling administrators a confirmed flaw exists in one of the few Windows components every machine trusts by default.
CVE-2026-40405 lands in the familiar but uncomfortable category of Windows TCP/IP vulnerabilities: low-friction exposure, high availability impact, and limited public technical detail at launch. Microsoft’s description is short, but it says enough. A null pointer dereference in Windows TCP/IP can allow an unauthorized attacker to deny service over a network.
That phrasing does not imply data theft, privilege escalation, or remote shell access. It implies interruption. In the CVSS vector, the attack is network-based, requires low attack complexity, needs no privileges, requires no user interaction, and affects availability at a high level while leaving confidentiality and integrity untouched.
That combination is why this bug deserves attention even without a “Critical” badge. A denial-of-service flaw in a desktop app is one thing; a denial-of-service flaw in the TCP/IP stack is another. The vulnerable component sits beneath most higher-level defenses, before the operating system has handed traffic to the services administrators usually monitor and harden.
Microsoft’s temporal scoring tempers the panic. The company lists exploit code maturity as unproven, remediation as official fix, and report confidence as confirmed. In other words, Microsoft says the bug is real, a patch exists, but there is no public proof-of-concept or observed exploitation at the time of publication.
That is the operational sweet spot where patch discipline matters most. The internet has not yet turned the vulnerability into a commodity nuisance, but the vendor has confirmed enough that waiting for public exploit code is the wrong trigger.
That matters because exploitability is not only about whether code exists on GitHub. It is also about how much ground truth attackers can infer from the advisory, the patch, and the affected binaries. Once a vendor ships a fix, the delta between old and new code can become a map for researchers and adversaries alike.
The “confirmed” metric does not mean exploitation is happening. Microsoft separately says the vulnerability was not publicly disclosed and not exploited at original publication. But “confirmed” does mean defenders should stop treating the issue as hypothetical.
This is the difference between “someone thinks Windows TCP/IP may behave badly” and “the vendor has acknowledged a reproducible vulnerability in the network stack.” In vulnerability management, that distinction should affect priority. A confirmed, unauthenticated, network-reachable availability bug deserves a place near the front of the monthly Windows queue, especially for systems that cannot tolerate unplanned downtime.
The advisory’s exploitability assessment, “exploitation less likely,” should be read as a probability signal, not a permission slip. Microsoft uses that language when it believes practical exploitation is not the most likely near-term outcome. It does not say “impossible,” and it does not say “ignore until next maintenance window.”
A successful exploit against CVE-2026-40405 would not hand an attacker the keys to a server. It could, however, make a vulnerable system unavailable. For domain controllers, VPN gateways, remote desktop hosts, management jump boxes, file servers, or heavily used workstations, availability is not a soft requirement.
The advisory’s CVSS base score of 7.5 reflects that tension. The vulnerability is not a confidentiality or integrity disaster, but its availability impact is high. The temporal score drops to 6.5 because Microsoft has shipped an official fix and exploit maturity is unproven.
That scoring can make the issue look like routine Patch Tuesday background noise. It is not. The meaningful question for administrators is whether an unauthenticated network packet path can disrupt a machine that users, services, or recovery processes depend on.
For home users, the practical risk is narrower but still real. Most consumer PCs sit behind NAT routers and host firewalls, reducing unsolicited inbound exposure. But laptops move between networks, gaming PCs run unusual services, and small-office machines often double as file shares, remote access endpoints, or ad hoc servers.
The advisory identifies CWE-476, the common weakness category for null pointer dereference. The rough idea is simple: software attempts to use a memory reference that points to nothing. If the vulnerable path is reachable from network traffic, the result can be a repeatable crash or service failure.
Microsoft does not publish packet-level details in the advisory, and that restraint is deliberate. The less the company says about the exact trigger, the harder it is for opportunistic attackers to reproduce quickly. But defenders do not need the trigger to understand the patching priority.
The important detail is the combination of network reachability and no authentication. An attacker does not need an account on the target, and no user needs to click anything. The vulnerability lives in the kind of code path administrators cannot meaningfully disable without disabling the machine’s role on the network.
That is also why mitigation advice is thinner than usual. You can block unsolicited traffic. You can segment networks. You can reduce exposure. But you cannot run Windows without TCP/IP, and most organizations cannot wall off every affected host from every untrusted packet source.
For Windows 11 24H2 and 25H2, Microsoft lists updates under the May 12, 2026 release. For Windows 11 26H1, the advisory points to a separate build line. For Windows Server 2025, both full and Server Core installations are included, with conventional security updates and hotpatch-related entries appearing in the table.
The server inclusion is the more consequential part. A desktop crash is disruptive; a server crash can cascade into authentication failures, application outages, and incident-response noise. Server Core being listed also undercuts the common assumption that trimming the GUI meaningfully reduces exposure to this class of bug.
This is not a vulnerability in a desktop shell component or a bundled app. It is in Windows TCP/IP. If the system is listening, routing, responding, or simply processing network traffic in the vulnerable path, the minimalism of Server Core is not a shield.
The May 2026 Patch Tuesday release is also broad, with community tracking showing 137 Microsoft CVEs in the release set. CVE-2026-40405 is one entry among many, and that is precisely why it can be missed. Patch Tuesday overload has become a vulnerability management problem of its own.
For most Windows 11 users, this means installing the May 2026 cumulative update through Windows Update, Windows Update for Business, WSUS, Intune, or the Microsoft Update Catalog. For Windows Server 2025, it means validating the normal security update path and, where hotpatching is in use, ensuring the hotpatch baseline and servicing model are actually current.
The absence of public exploitation should shape sequencing, not justify delay. Internet-facing servers, systems in semi-trusted networks, and machines that provide authentication, remote access, management, or business-critical services should move first. Low-risk desktops behind strong perimeter controls can follow normal rings, but they should not be deferred indefinitely.
There is also a testing trap here. Because the bug affects the network stack, administrators will naturally worry about regressions in VPN clients, endpoint detection drivers, packet filters, virtual switches, and NIC offload features. That caution is fair, but it argues for fast pilot rings rather than waiting for the internet to do the testing for you.
Organizations that run heavy network inspection or host-based firewall software should watch for update interactions. Kernel networking changes can expose assumptions in third-party filter drivers. A clean pilot across laptops, servers, Hyper-V hosts, VPN-connected systems, and security-tool-heavy endpoints is more useful than a tiny test on one pristine VM.
For CVE-2026-40405, the presence of a hotpatch path for Server 2025 should be treated as an opportunity to shorten exposure, not as a reason to relax validation. The machines that benefit most from hotpatching are often the same machines where a denial-of-service crash would be most painful.
There is an irony here. The vulnerability threatens availability, and the fix may itself require availability planning. That tension is the daily reality of Windows operations: leave the system unpatched and risk an attacker-induced outage, or patch quickly and manage the possibility of update-induced disruption.
The right answer is not blind urgency. It is disciplined urgency. Build the ring, patch representative systems, monitor network behavior, then accelerate deployment to exposed servers and critical clients.
Home and small-business users have a simpler path. Install the update, reboot when prompted, and resist the temptation to pause updates for weeks because this month’s headline bug is “only” denial of service. The machines most likely to be neglected are often the least monitored when something goes wrong.
The sheer number of CVEs each month has trained many teams to rely on shortcuts: Critical before Important, exploited before unexploited, RCE before denial of service. Those shortcuts are necessary, but they are also lossy. A network-reachable, unauthenticated DoS in TCP/IP can fall below a flashier Office bug and still represent a more immediate operational concern for certain environments.
The better prioritization model starts with asset role. A domain controller, remote access server, exposed Windows Server 2025 system, or management endpoint has a different risk profile than a kiosk or single-user workstation. CVSS does not know your topology.
It also starts with attacker path. If a system can receive traffic from untrusted networks, unauthenticated network vulnerabilities rise in importance. If a system is isolated behind strict allow lists, the same CVE may be less urgent, though still worth patching in the normal cycle.
This is where vulnerability management becomes engineering rather than scorekeeping. The CVSS vector tells you what the vulnerability can do in general. Your network tells you whether that path is reachable in practice.
When a vulnerability is patched, researchers can compare binaries, infer code paths, and test malformed traffic. That process can produce defensive insight, but it can also produce exploit tooling. Denial-of-service bugs are often easier to weaponize than reliable code execution because the attacker only needs to make the target fall over, not control it gracefully.
Microsoft’s own exploitability assessment says exploitation is less likely at publication. That is useful, but it is not a durable state. The exploitability of a patched bug can change as more eyes examine the update.
Administrators should also remember that network DoS is not always about mass internet scanning. An insider, a compromised device on the same network, a malicious guest on Wi-Fi, or a foothold in a segmented environment can use availability bugs to create distraction and damage. The attacker does not need global reach if they already have local reach.
That makes segmentation and ingress filtering still relevant even when the patch is available. Good network boundaries reduce the blast radius of bugs like this. They also buy time when a patch cannot be installed immediately.
Most consumer systems will receive the fix through the usual cumulative update channel. If automatic updates are enabled, the main task is to let the installation finish and reboot. A half-installed security update sitting behind a pending restart is a familiar Windows risk multiplier.
The temptation for enthusiasts is to over-index on whether there is a public exploit. That matters, but it is not the only signal. Microsoft has already confirmed the vulnerability and shipped a fix. For a network-stack availability bug, that is enough reason to get current.
Users who routinely disable IPv6, tweak firewall rules, or rely on router NAT should not treat those habits as a substitute for patching. The advisory does not provide a specific workaround that eliminates the issue. Without a precise trigger, homegrown mitigations are guesswork.
For small offices, the better play is to patch Windows endpoints and servers, check that backups and remote access paths still work, and review which machines are reachable from guest Wi-Fi, VPN clients, or port-forwarded services. That review is useful even after the patch lands.
The most useful framing is reliability under adversarial input. Windows TCP/IP is supposed to process hostile, malformed, unexpected, and noisy traffic without collapsing. A null pointer dereference in that path means a class of input can break that promise.
That framing helps justify patch priority to stakeholders who do not care about CVSS. The issue is not that someone might “hack” a server in the cinematic sense. The issue is that a system may be remotely forced into an unavailable state, and Microsoft has confirmed the condition.
Enterprises should map the advisory against their Windows Server 2025 footprint first. Then they should check Windows 11 systems that occupy privileged or exposed positions: admin workstations, jump hosts, developer machines on shared networks, security consoles, and devices used for remote access.
After deployment, monitoring should focus on the ordinary signs of network-stack trouble: unexpected reboots, bugchecks, loss of connectivity, VPN instability, endpoint firewall events, and anomalies from network filter drivers. The patch should fix the vulnerability, but the surrounding ecosystem of drivers and security products is where update friction often appears.
The key facts are unusually clean. The vulnerability is confirmed. The attack vector is network. No privileges are required. No user interaction is required. The impact is denial of service. The affected products include current Windows client and server releases. An official fix is available. Microsoft says there is no public disclosure or observed exploitation at publication.
That set of facts argues for a measured but prompt response. It does not argue for emergency shutdowns, mass firewall panic, or disabling core networking features. It does argue against burying the update under less relevant but scarier-sounding CVEs.
The advisory also illustrates the limits of public vulnerability data. We know the weakness class, the affected products, the score, and Microsoft’s exploitability view. We do not know the packet pattern, the crash mode, or whether real-world configurations reduce or expand reachability.
That uncertainty is not a failure of reporting. It is part of coordinated disclosure. Defenders should fill the gap with asset knowledge, exposure analysis, and patch telemetry rather than speculation.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Microsoft’s “Important” Label Hides a Very Direct Attack Path
Microsoft’s “Important” Label Hides a Very Direct Attack Path
CVE-2026-40405 lands in the familiar but uncomfortable category of Windows TCP/IP vulnerabilities: low-friction exposure, high availability impact, and limited public technical detail at launch. Microsoft’s description is short, but it says enough. A null pointer dereference in Windows TCP/IP can allow an unauthorized attacker to deny service over a network.That phrasing does not imply data theft, privilege escalation, or remote shell access. It implies interruption. In the CVSS vector, the attack is network-based, requires low attack complexity, needs no privileges, requires no user interaction, and affects availability at a high level while leaving confidentiality and integrity untouched.
That combination is why this bug deserves attention even without a “Critical” badge. A denial-of-service flaw in a desktop app is one thing; a denial-of-service flaw in the TCP/IP stack is another. The vulnerable component sits beneath most higher-level defenses, before the operating system has handed traffic to the services administrators usually monitor and harden.
Microsoft’s temporal scoring tempers the panic. The company lists exploit code maturity as unproven, remediation as official fix, and report confidence as confirmed. In other words, Microsoft says the bug is real, a patch exists, but there is no public proof-of-concept or observed exploitation at the time of publication.
That is the operational sweet spot where patch discipline matters most. The internet has not yet turned the vulnerability into a commodity nuisance, but the vendor has confirmed enough that waiting for public exploit code is the wrong trigger.
“Confirmed” Is the Quiet Word That Changes the Risk Model
The user-supplied MSRC metric text points to the most important nuance in this advisory: report confidence. This is not a rumor, not a vague undesirable behavior, and not a speculative research note. Microsoft marks the report confidence as confirmed.That matters because exploitability is not only about whether code exists on GitHub. It is also about how much ground truth attackers can infer from the advisory, the patch, and the affected binaries. Once a vendor ships a fix, the delta between old and new code can become a map for researchers and adversaries alike.
The “confirmed” metric does not mean exploitation is happening. Microsoft separately says the vulnerability was not publicly disclosed and not exploited at original publication. But “confirmed” does mean defenders should stop treating the issue as hypothetical.
This is the difference between “someone thinks Windows TCP/IP may behave badly” and “the vendor has acknowledged a reproducible vulnerability in the network stack.” In vulnerability management, that distinction should affect priority. A confirmed, unauthenticated, network-reachable availability bug deserves a place near the front of the monthly Windows queue, especially for systems that cannot tolerate unplanned downtime.
The advisory’s exploitability assessment, “exploitation less likely,” should be read as a probability signal, not a permission slip. Microsoft uses that language when it believes practical exploitation is not the most likely near-term outcome. It does not say “impossible,” and it does not say “ignore until next maintenance window.”
Denial of Service Is Not a Lesser Category When the Target Is the Network Stack
Security teams naturally prioritize remote code execution, elevation of privilege, and authentication bypass. That instinct is correct most of the time. But denial of service has a different kind of business impact, particularly when it can be triggered remotely and without credentials.A successful exploit against CVE-2026-40405 would not hand an attacker the keys to a server. It could, however, make a vulnerable system unavailable. For domain controllers, VPN gateways, remote desktop hosts, management jump boxes, file servers, or heavily used workstations, availability is not a soft requirement.
The advisory’s CVSS base score of 7.5 reflects that tension. The vulnerability is not a confidentiality or integrity disaster, but its availability impact is high. The temporal score drops to 6.5 because Microsoft has shipped an official fix and exploit maturity is unproven.
That scoring can make the issue look like routine Patch Tuesday background noise. It is not. The meaningful question for administrators is whether an unauthenticated network packet path can disrupt a machine that users, services, or recovery processes depend on.
For home users, the practical risk is narrower but still real. Most consumer PCs sit behind NAT routers and host firewalls, reducing unsolicited inbound exposure. But laptops move between networks, gaming PCs run unusual services, and small-office machines often double as file shares, remote access endpoints, or ad hoc servers.
A Null Pointer Dereference Is Boring Until It Is Remote
Null pointer dereference sounds like a memory-safety footnote. In ordinary application code, it often means a crash. In kernel-adjacent or network-stack code, the consequences become more serious because the crash happens inside foundational plumbing.The advisory identifies CWE-476, the common weakness category for null pointer dereference. The rough idea is simple: software attempts to use a memory reference that points to nothing. If the vulnerable path is reachable from network traffic, the result can be a repeatable crash or service failure.
Microsoft does not publish packet-level details in the advisory, and that restraint is deliberate. The less the company says about the exact trigger, the harder it is for opportunistic attackers to reproduce quickly. But defenders do not need the trigger to understand the patching priority.
The important detail is the combination of network reachability and no authentication. An attacker does not need an account on the target, and no user needs to click anything. The vulnerability lives in the kind of code path administrators cannot meaningfully disable without disabling the machine’s role on the network.
That is also why mitigation advice is thinner than usual. You can block unsolicited traffic. You can segment networks. You can reduce exposure. But you cannot run Windows without TCP/IP, and most organizations cannot wall off every affected host from every untrusted packet source.
The Affected List Points to Microsoft’s Newest Windows Estate
The security update table for CVE-2026-40405 covers Windows 11 versions 24H2, 25H2, and 26H1, along with Windows Server 2025 and Server Core installation. That product list is notable because it centers the modern Windows estate rather than legacy releases.For Windows 11 24H2 and 25H2, Microsoft lists updates under the May 12, 2026 release. For Windows 11 26H1, the advisory points to a separate build line. For Windows Server 2025, both full and Server Core installations are included, with conventional security updates and hotpatch-related entries appearing in the table.
The server inclusion is the more consequential part. A desktop crash is disruptive; a server crash can cascade into authentication failures, application outages, and incident-response noise. Server Core being listed also undercuts the common assumption that trimming the GUI meaningfully reduces exposure to this class of bug.
This is not a vulnerability in a desktop shell component or a bundled app. It is in Windows TCP/IP. If the system is listening, routing, responding, or simply processing network traffic in the vulnerable path, the minimalism of Server Core is not a shield.
The May 2026 Patch Tuesday release is also broad, with community tracking showing 137 Microsoft CVEs in the release set. CVE-2026-40405 is one entry among many, and that is precisely why it can be missed. Patch Tuesday overload has become a vulnerability management problem of its own.
The Patch Is the Mitigation, but Exposure Still Determines Urgency
Microsoft marks customer action as required for the affected products. That is bureaucratic language for the only practical fix: apply the relevant cumulative security update or hotpatch where applicable.For most Windows 11 users, this means installing the May 2026 cumulative update through Windows Update, Windows Update for Business, WSUS, Intune, or the Microsoft Update Catalog. For Windows Server 2025, it means validating the normal security update path and, where hotpatching is in use, ensuring the hotpatch baseline and servicing model are actually current.
The absence of public exploitation should shape sequencing, not justify delay. Internet-facing servers, systems in semi-trusted networks, and machines that provide authentication, remote access, management, or business-critical services should move first. Low-risk desktops behind strong perimeter controls can follow normal rings, but they should not be deferred indefinitely.
There is also a testing trap here. Because the bug affects the network stack, administrators will naturally worry about regressions in VPN clients, endpoint detection drivers, packet filters, virtual switches, and NIC offload features. That caution is fair, but it argues for fast pilot rings rather than waiting for the internet to do the testing for you.
Organizations that run heavy network inspection or host-based firewall software should watch for update interactions. Kernel networking changes can expose assumptions in third-party filter drivers. A clean pilot across laptops, servers, Hyper-V hosts, VPN-connected systems, and security-tool-heavy endpoints is more useful than a tiny test on one pristine VM.
Hotpatching Helps Only If the Fleet Is Already Ready for It
The advisory’s Server 2025 entries include security hotpatch update information, which is increasingly central to Microsoft’s enterprise patching pitch. Hotpatching can reduce restart pressure, and for availability-sensitive servers that matters. But hotpatching is not magic; it works within a servicing model that administrators must already understand.For CVE-2026-40405, the presence of a hotpatch path for Server 2025 should be treated as an opportunity to shorten exposure, not as a reason to relax validation. The machines that benefit most from hotpatching are often the same machines where a denial-of-service crash would be most painful.
There is an irony here. The vulnerability threatens availability, and the fix may itself require availability planning. That tension is the daily reality of Windows operations: leave the system unpatched and risk an attacker-induced outage, or patch quickly and manage the possibility of update-induced disruption.
The right answer is not blind urgency. It is disciplined urgency. Build the ring, patch representative systems, monitor network behavior, then accelerate deployment to exposed servers and critical clients.
Home and small-business users have a simpler path. Install the update, reboot when prompted, and resist the temptation to pause updates for weeks because this month’s headline bug is “only” denial of service. The machines most likely to be neglected are often the least monitored when something goes wrong.
Patch Tuesday Volume Is Now Part of the Threat Surface
CVE-2026-40405 arrives in a month with a large Microsoft security release. That context matters because defenders are not evaluating one vulnerability in isolation. They are triaging dozens or hundreds of items across Windows, Office, Edge, Azure services, developer tools, and enterprise applications.The sheer number of CVEs each month has trained many teams to rely on shortcuts: Critical before Important, exploited before unexploited, RCE before denial of service. Those shortcuts are necessary, but they are also lossy. A network-reachable, unauthenticated DoS in TCP/IP can fall below a flashier Office bug and still represent a more immediate operational concern for certain environments.
The better prioritization model starts with asset role. A domain controller, remote access server, exposed Windows Server 2025 system, or management endpoint has a different risk profile than a kiosk or single-user workstation. CVSS does not know your topology.
It also starts with attacker path. If a system can receive traffic from untrusted networks, unauthenticated network vulnerabilities rise in importance. If a system is isolated behind strict allow lists, the same CVE may be less urgent, though still worth patching in the normal cycle.
This is where vulnerability management becomes engineering rather than scorekeeping. The CVSS vector tells you what the vulnerability can do in general. Your network tells you whether that path is reachable in practice.
The Old TCP/IP Lessons Still Apply
Windows has had serious TCP/IP issues before, including IPv6-related flaws and fragmentation-adjacent vulnerabilities that drew intense attention because they sat close to the network perimeter. The recurring lesson is not that every TCP/IP bug is catastrophic. It is that bugs in this layer age badly once exploit details circulate.When a vulnerability is patched, researchers can compare binaries, infer code paths, and test malformed traffic. That process can produce defensive insight, but it can also produce exploit tooling. Denial-of-service bugs are often easier to weaponize than reliable code execution because the attacker only needs to make the target fall over, not control it gracefully.
Microsoft’s own exploitability assessment says exploitation is less likely at publication. That is useful, but it is not a durable state. The exploitability of a patched bug can change as more eyes examine the update.
Administrators should also remember that network DoS is not always about mass internet scanning. An insider, a compromised device on the same network, a malicious guest on Wi-Fi, or a foothold in a segmented environment can use availability bugs to create distraction and damage. The attacker does not need global reach if they already have local reach.
That makes segmentation and ingress filtering still relevant even when the patch is available. Good network boundaries reduce the blast radius of bugs like this. They also buy time when a patch cannot be installed immediately.
The Consumer Advice Is Simple, but Not Trivial
For Windows 11 users, CVE-2026-40405 should not inspire packet captures at midnight. It should inspire an update check. The affected Windows 11 versions listed by Microsoft include 24H2, 25H2, and 26H1, which means this is not a legacy corner case.Most consumer systems will receive the fix through the usual cumulative update channel. If automatic updates are enabled, the main task is to let the installation finish and reboot. A half-installed security update sitting behind a pending restart is a familiar Windows risk multiplier.
The temptation for enthusiasts is to over-index on whether there is a public exploit. That matters, but it is not the only signal. Microsoft has already confirmed the vulnerability and shipped a fix. For a network-stack availability bug, that is enough reason to get current.
Users who routinely disable IPv6, tweak firewall rules, or rely on router NAT should not treat those habits as a substitute for patching. The advisory does not provide a specific workaround that eliminates the issue. Without a precise trigger, homegrown mitigations are guesswork.
For small offices, the better play is to patch Windows endpoints and servers, check that backups and remote access paths still work, and review which machines are reachable from guest Wi-Fi, VPN clients, or port-forwarded services. That review is useful even after the patch lands.
The Admin Playbook Should Treat CVE-2026-40405 as a Reliability Bug With Security Roots
Security teams and operations teams often talk past each other on denial-of-service vulnerabilities. Security sees a CVE. Operations sees uptime risk. CVE-2026-40405 is both.The most useful framing is reliability under adversarial input. Windows TCP/IP is supposed to process hostile, malformed, unexpected, and noisy traffic without collapsing. A null pointer dereference in that path means a class of input can break that promise.
That framing helps justify patch priority to stakeholders who do not care about CVSS. The issue is not that someone might “hack” a server in the cinematic sense. The issue is that a system may be remotely forced into an unavailable state, and Microsoft has confirmed the condition.
Enterprises should map the advisory against their Windows Server 2025 footprint first. Then they should check Windows 11 systems that occupy privileged or exposed positions: admin workstations, jump hosts, developer machines on shared networks, security consoles, and devices used for remote access.
After deployment, monitoring should focus on the ordinary signs of network-stack trouble: unexpected reboots, bugchecks, loss of connectivity, VPN instability, endpoint firewall events, and anomalies from network filter drivers. The patch should fix the vulnerability, but the surrounding ecosystem of drivers and security products is where update friction often appears.
The Signal Beneath Microsoft’s Sparse Advisory
Microsoft’s advisory is terse, and that is normal for a newly released vulnerability. The company gives defenders enough to prioritize without giving attackers a recipe. That sparsity should not be mistaken for low confidence.The key facts are unusually clean. The vulnerability is confirmed. The attack vector is network. No privileges are required. No user interaction is required. The impact is denial of service. The affected products include current Windows client and server releases. An official fix is available. Microsoft says there is no public disclosure or observed exploitation at publication.
That set of facts argues for a measured but prompt response. It does not argue for emergency shutdowns, mass firewall panic, or disabling core networking features. It does argue against burying the update under less relevant but scarier-sounding CVEs.
The advisory also illustrates the limits of public vulnerability data. We know the weakness class, the affected products, the score, and Microsoft’s exploitability view. We do not know the packet pattern, the crash mode, or whether real-world configurations reduce or expand reachability.
That uncertainty is not a failure of reporting. It is part of coordinated disclosure. Defenders should fill the gap with asset knowledge, exposure analysis, and patch telemetry rather than speculation.
The May 2026 Windows TCP/IP Fix Belongs in the First Real Patch Ring
The concrete lesson of CVE-2026-40405 is that “Important” does not mean “later” when the vulnerable component is the Windows network stack. Treat the advisory as a confirmed reliability threat with remote security implications, and prioritize accordingly.- CVE-2026-40405 is a confirmed Windows TCP/IP denial-of-service vulnerability caused by a null pointer dereference.
- The attack path is network-based, unauthenticated, low-complexity, and requires no user interaction.
- Microsoft says the vulnerability was not publicly disclosed and not exploited at the time it was published.
- The affected update set includes Windows 11 versions 24H2, 25H2, and 26H1, plus Windows Server 2025 and Server Core.
- The practical fix is to install the May 12, 2026 security update or applicable Server 2025 hotpatch update through normal Microsoft servicing channels.
- Administrators should prioritize exposed servers, remote access infrastructure, management systems, and high-value Windows 11 endpoints before broad desktop rollout.
Source: MSRC Security Update Guide - Microsoft Security Response Center