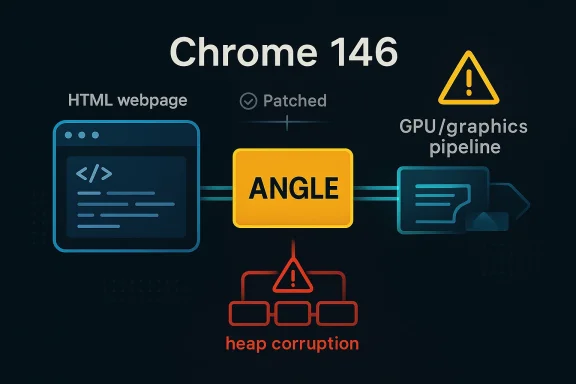
Google has now patched a fresh Chromium security issue in the browser’s graphics stack, and the details matter for anyone who treats Chrome as a routine utility instead of a high-value attack surface. CVE-2026-4464 is an integer overflow in ANGLE, the graphics translation layer used by Chromium, and Google says it affected Chrome versions prior to 146.0.7680.153. The bug could let a remote attacker abuse a crafted HTML page to trigger heap corruption, which is exactly the sort of memory-safety failure that can become a serious browser exploit chain if it is paired with other weaknesses or reliable exploit primitives. The Chromium project has classed the issue as Medium, but the technical shape of the flaw means enterprises should still treat it as a meaningful patching priority. r security in 2026 continues to be defined by a familiar pattern: attackers do not need to break the whole browser at once, only one reachable component with enough memory-unsafe behavior to get a foothold. ANGLE sits in a particularly sensitive place because it bridges browser rendering to platform graphics APIs, and that puts it on the path of content that started as ordinary web input. When an HTML page can drive the bug, the attack surface is broad, which is why this CVE deserves attention even before all downstream scoring metadata is fully populated.
The underlying prob it remains dangerous. Integer overflows are notorious for transforming a seemingly bounded calculation into a smaller-than-expected allocation, length, or index, and that can cascade into heap corruption when later writes or reads assume the calculation was correct. In browser code, that often turns into a crash first and a exploitability question second, but it is the second part that security teams worry about most. The fact that the issue is described as remote and page-triggerable raises the stakes immediately.
Google’s Chrome release cadence shows the March 2026 stable cycle, with Chrome 146 promoted to stable on March 10, 2026 and a later stable update on March 12, 2026. The March 10 release already carried a long list of security fixes, and by March 12 Google had issued another stable-channel build while also correcting its notes to remove a previously listed item that would arrive later. That sequence is a reminder that browser patching is increasingly incremental, with security fixes arriving in waves rather than in one neat monthly bundle. (chromereleases.googleblog.com)
For Microsoft Edge users, the story is the same in a different channel. Microsoft’s Security Update Guide is often the place where downstream consumers learn that a Chromium fix has been incorporated into Edge, even when Microsoft did not author the bug itself. The presence of this CVE in Microsoft’s guidance confirms that the issue is relevant to the broader Chromium ecosystem, not juse notes.
ANGLE, short for Almost Native Graphics Layer Engine, exists to translate OpenGL ES calls into platform-native graphics back ends. In practical terms, that means it is a compatibility bridge, one that allows browser content to lean on hardware acceleration without forcing every platform to expose the same graphics stack natively. That compatibility layer is invaluable for performance, but it also widens the blast radius when memory arithmetic gohy graphics bugs in browsers are often more consequential than their labels suggest. A flaw in a rendering bridge may appear to be “just” a graphics issue, but browsers use graphics components to process a huge range of attacker-controlled content, from simple pages to animated elements and GPU-adjacent code paths. If the vulnerable code is reachable through HTML, then the attack surface is not limited to niche applications or advanced users. It is the open web.
Chrome’s so show how crowded the security landscape has become. The March 10 stable release listed 29 security fixes, including multiple high-severity memory-safety issues across WebML, WebSpeech, WebMIDI, WindowDialog, Extensions, and other subsystems. That breadth matters because it demonstrates that Chrome’s attack surface is distributed across many specialized components, and ANGLE is only one of several places where memory safety continues to be a recurring challenge. (chromereleases.googleblog.com)
ANGLE has also become a recurring reminder that browser engines are really collections of mini-runtime systems. They include parsers, JITs, graphics bridges, media stacks, and policy layers, all of which are reachable through content that looks ordinary to a user. That makes a vulnerability like CVE-2026-4464 structurally important even if the initial sn is not the highest possible.
The attacker model is equally important. This is not a local-only flaw and not one that requires privileged access or social engineering beyond getting the victim to render a malicious page. In browser security, the “crafted HTML page” detail is often a sign that the issue can be delivered over the web, embedded in ad traffic, or hidden behind a link. That makes the operational risk much broader than the wording “Medium” might imply to a casuainteger overflow buys an attacker
An overflow does not automatically equal remote code execution, but it can create the conditions that make exploitation possible. If a length calculation wraps or truncates, subsequent allocations can be too small, and the program may later write as though the allocation were larger. The outcome can be corrupted heap state, controlled overwrite opportunities, or a crash that reveals exploitation potential.
The browser layer. Many modern exploit chains begin with a memory-corruption primitive in a content-facing component and then move toward sandbox escape or privilege escalation through a second bug. That is why defenders should not dismiss an overflow just because the advisory does not claim instant code execution. In the real world, exploitability is often compositional.
This is especially relevant in mixed Windows estates. Chrome often updates quickly on consumer endpoints, but enterprise-managed desktops, VDI hosts, and locked-down workstations frequently lag behind the public channel. The result is a risk window that is smaller for individual users than for centralized fleets, which is exactly where administrators need cleaner visibility.
ility and Real-World Impact
The most important question is not whether the bug exists, but whether it can be turned into something worse than a crash. For a browser vulnerability, the answer almost always depends on whether the memory corruption is stable, whether a reliable trigger exists, and whether the affected code can be reached in common browsing flows. The fact that Google treats the issue as a security fix at all tells us the code path was serious enough to warrant public remediation.
Heap corruption in b have several outcomes. At the mild end, users see tab crashes or GPU process failures. At the severe end, the bug becomes part of a multi-stage chain that compromises renderer integrity or assists in sandbox escape. Security teams should therefore evaluate the patch as a preventive control, not merely as a crash fix.
The practical concern is amplified in enterprise environments tied to business workflows. Internal portals, SaaS dashboards, and document viewers all rely on browsers as universal renderers, which means a graphics-layer bug can ride in on what appears to be normal work. That is the hidden cost of browser ubiquity: the same code path serves entertainment, work, and attack delivery.
For enterprises, the issue is broader and more procedural. Endpoint compliance tools need to verify browt just browser presence, and patch teams need to reconcile Chrome release timing with internal change windows. If browser updates are delayed for stability testing, the organization should treat this CVE as a reason to compress that window, not stretch it.
The safer posture is simple: verify the installed version, restart the browser if necessary, and let the updater finish its work. Browser restarts because many patches do not become effective until the old process is gone. That is an old lesson, but it keeps paying dividends.
Patch validation should also include endpoint telemetry. A security ticket is not closed because a vendor published a fix; it is closed when the fleet has actually adopted it. That distincimportant in environments with slow ring deployments or branch-based approval workflows.
That pattern is important for rivals too. Edge, Brave, Opera, and other Chromium-based products must absorb upstream fixes quickly or risk inheriting the same exposure window. For administrators, that means browser policy should be measured by patch freshness and build provenance, not just by brand name. The upstream project may move first, but downstream vendors determine when your endpoint is actually safe.
This also explains why browser security advisories have become a supply-chain event. A fix in Chromium can alter the risk posture for enterprises lly chose Chrome, because a downstream browser, webview, or embedded shell may still consume the same vulnerable code. That reality is one of the big operational stories in modern desktop security.
That matters because many Windows enterprises standardize on Edge while still encountering Chrome-based compatibility requirements. The browser estate may appear simple at the policy layerit is often mixed, with multiple Chromium consumers moving at slightly different speeds. A clean Chrome patch does not automatically guarantee a clean Edge patch at the same moment.
It also reduces ambiguity for patch teams. Rather than treating “Chromium fixed it” as the end of the story, teams can check whether their browser vendor has rolled the fix into the build they deploy. That workflow is slower than it is also safer. Security is a state, not a press release.
This is where defenders need to resist score-chasing. The NVD record in the uploaded material shows that public scoring may still be catching up, while other enrichment sources can suggest a higher-risk vector. That discrepancy is exactly why teams should look at the vuln, the affected version range, and the reachable attack path before deciding how quickly to patch.
Administrators should therefore triage by shape, not just by score. A remote browser flaw that can be triggered from a crafted page and that involves heap corruption belongs near the front of the queue even if the formal rating is still in motion. That is the kind of judgment good patch management requires.
Security teams should also look for corroborating indicators in their environment. Crash telemetry, renderer faults, or GPU-process anomalies are not proof of exploitation, but they can help determine whether the vulnerable code path is being exercised in unexpected ways. That is useful both for immediate response and for validating that the fix does nots.
It will also be worth watching whether Google or independent researchers publish more detail on the underlying ANGLE arithmetic failure. If more technical analysis appears, it may reveal whether the bug is isolated or part of a broader class of graphics-layer overflow issues. The broader lesson is familiar but still urgent: the web’s performance stack remains one of its most fragile security surfaces.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center
The underlying prob it remains dangerous. Integer overflows are notorious for transforming a seemingly bounded calculation into a smaller-than-expected allocation, length, or index, and that can cascade into heap corruption when later writes or reads assume the calculation was correct. In browser code, that often turns into a crash first and a exploitability question second, but it is the second part that security teams worry about most. The fact that the issue is described as remote and page-triggerable raises the stakes immediately.
Google’s Chrome release cadence shows the March 2026 stable cycle, with Chrome 146 promoted to stable on March 10, 2026 and a later stable update on March 12, 2026. The March 10 release already carried a long list of security fixes, and by March 12 Google had issued another stable-channel build while also correcting its notes to remove a previously listed item that would arrive later. That sequence is a reminder that browser patching is increasingly incremental, with security fixes arriving in waves rather than in one neat monthly bundle. (chromereleases.googleblog.com)
For Microsoft Edge users, the story is the same in a different channel. Microsoft’s Security Update Guide is often the place where downstream consumers learn that a Chromium fix has been incorporated into Edge, even when Microsoft did not author the bug itself. The presence of this CVE in Microsoft’s guidance confirms that the issue is relevant to the broader Chromium ecosystem, not juse notes.
 Background
Background
ANGLE, short for Almost Native Graphics Layer Engine, exists to translate OpenGL ES calls into platform-native graphics back ends. In practical terms, that means it is a compatibility bridge, one that allows browser content to lean on hardware acceleration without forcing every platform to expose the same graphics stack natively. That compatibility layer is invaluable for performance, but it also widens the blast radius when memory arithmetic gohy graphics bugs in browsers are often more consequential than their labels suggest. A flaw in a rendering bridge may appear to be “just” a graphics issue, but browsers use graphics components to process a huge range of attacker-controlled content, from simple pages to animated elements and GPU-adjacent code paths. If the vulnerable code is reachable through HTML, then the attack surface is not limited to niche applications or advanced users. It is the open web.Chrome’s so show how crowded the security landscape has become. The March 10 stable release listed 29 security fixes, including multiple high-severity memory-safety issues across WebML, WebSpeech, WebMIDI, WindowDialog, Extensions, and other subsystems. That breadth matters because it demonstrates that Chrome’s attack surface is distributed across many specialized components, and ANGLE is only one of several places where memory safety continues to be a recurring challenge. (chromereleases.googleblog.com)
Why ANGLE keeps showing up
Graphics translation layers are inherently complex because they must reconcile different driver expectations, data models, and API semantics. In a browser, that complexity is compounded by untrusted web content and by the requirement that rendering remain fast enough for everyday use. The result is a subsystem where a single arithmetic error can become a memory-safetto reason about and even harder to fuzz completely.ANGLE has also become a recurring reminder that browser engines are really collections of mini-runtime systems. They include parsers, JITs, graphics bridges, media stacks, and policy layers, all of which are reachable through content that looks ordinary to a user. That makes a vulnerability like CVE-2026-4464 structurally important even if the initial sn is not the highest possible.
The Vulnerability Shape
The vulnerability description is concise but revealing: integer overflow in ANGLE leading to potential heap corruption via a crafted HTML page. That combination is a classic exploit-friendly pattern because arithmetic mistakes can desynchronize intended object sizes from actual allocations. Once memory layout is wrong, subsequent writes can land in adjacent objects or metadata, which is the sort of condihunt for.The attacker model is equally important. This is not a local-only flaw and not one that requires privileged access or social engineering beyond getting the victim to render a malicious page. In browser security, the “crafted HTML page” detail is often a sign that the issue can be delivered over the web, embedded in ad traffic, or hidden behind a link. That makes the operational risk much broader than the wording “Medium” might imply to a casuainteger overflow buys an attacker
An overflow does not automatically equal remote code execution, but it can create the conditions that make exploitation possible. If a length calculation wraps or truncates, subsequent allocations can be too small, and the program may later write as though the allocation were larger. The outcome can be corrupted heap state, controlled overwrite opportunities, or a crash that reveals exploitation potential.
The browser layer. Many modern exploit chains begin with a memory-corruption primitive in a content-facing component and then move toward sandbox escape or privilege escalation through a second bug. That is why defenders should not dismiss an overflow just because the advisory does not claim instant code execution. In the real world, exploitability is often compositional.
Patch Timing and Release Cortant operational fact is the version floor: Chrome versions prior to 146.0.7680.153 are the affected builds named in the advisory data. In practice, that means organizations running 146 branch builds need to confirm they are at or beyond the patched revision, especially on devices that do not auto-update promptly. The advisory’s language makes clear that the issue is tied to a specific release boundary rather than to an open-ended set of older versions.
The second important fact is timing. Chrome 146 reah 10, 2026**, with the March 12 stable-channel note showing the release train continuing to move forward. Google’s cadence suggests the fix is part of the broader March security response, even if the public records around the CVE continue to evolve. That matters because organizations often rely on the release notes rather than the CVE page itself when making patch decisions. (chromereleases.googleblog.com)Why the release train matters for defenders
Browser updates are no longer a “set it and forget it” event. Some fleets update in hours, others in days or weeks, and managed environments may have their own approval gate before an auto-update can be deployed. A flaw like this should therefore be tracked by version, not by hope. If your Chrome or Edge versioning policy is loose, you may think you are safe while still sitting on thThis is especially relevant in mixed Windows estates. Chrome often updates quickly on consumer endpoints, but enterprise-managed desktops, VDI hosts, and locked-down workstations frequently lag behind the public channel. The result is a risk window that is smaller for individual users than for centralized fleets, which is exactly where administrators need cleaner visibility.
ility and Real-World Impact
The most important question is not whether the bug exists, but whether it can be turned into something worse than a crash. For a browser vulnerability, the answer almost always depends on whether the memory corruption is stable, whether a reliable trigger exists, and whether the affected code can be reached in common browsing flows. The fact that Google treats the issue as a security fix at all tells us the code path was serious enough to warrant public remediation.
Heap corruption in b have several outcomes. At the mild end, users see tab crashes or GPU process failures. At the severe end, the bug becomes part of a multi-stage chain that compromises renderer integrity or assists in sandbox escape. Security teams should therefore evaluate the patch as a preventive control, not merely as a crash fix.
Why “crafted HTML” is a red flag
Whe from HTML, the attacker’s delivery problem is dramatically easier. No special file type is needed, no local admin is required, and no unusual software environment is assumed. In many cases, the victim only needs to visit a page, load an ad, or open content embedded in a site they already trust. That is why web-exposed flaws deserve fast remediation even when they do not initially sound dramatic.The practical concern is amplified in enterprise environments tied to business workflows. Internal portals, SaaS dashboards, and document viewers all rely on browsers as universal renderers, which means a graphics-layer bug can ride in on what appears to be normal work. That is the hidden cost of browser ubiquity: the same code path serves entertainment, work, and attack delivery.
Enterprise and Consumer Exposure
For consumers, the immediate advice is straighme, and by extension any Chromium-based browser that inherits the fix, as soon as the patched build is available. Automatic updates reduce exposure, but they do not eliminate the interval during which a vulnerable build remains in use. In security terms, that interval is the gap attackers try to exploit.For enterprises, the issue is broader and more procedural. Endpoint compliance tools need to verify browt just browser presence, and patch teams need to reconcile Chrome release timing with internal change windows. If browser updates are delayed for stability testing, the organization should treat this CVE as a reason to compress that window, not stretch it.
Consumer guidance
Consumers usually benefit from browser auto-update mechanisms, but only if those mechanisms are functi by policy or stale installations. On personal devices, the risk is often more about exposure time than about lack of remediation altogether. If the browser is not updating, the user has a problem that goes beyond this specific CVE.The safer posture is simple: verify the installed version, restart the browser if necessary, and let the updater finish its work. Browser restarts because many patches do not become effective until the old process is gone. That is an old lesson, but it keeps paying dividends.
Enterprise guidance
Enterprises should inventory all Chromium-based browsers, not just Google Chrome. Microsoft Edge, embedded browser runtimes, and managed deskt be checked because Chromium fixes often propagate downstream. The operational mistake is assuming that a Chrome patch automatically means every Chromium consumer is safe on the same day.Patch validation should also include endpoint telemetry. A security ticket is not closed because a vendor published a fix; it is closed when the fleet has actually adopted it. That distincimportant in environments with slow ring deployments or branch-based approval workflows.
How This Fits the Broader Chromium Pattern
This CVE is another entry in the long Chromium memory-safety story. Chrome’s March 2026 stable branch included a wide set of issues, many of them memory corruptiont bugs across discrete subsystems. The release notes show that browser security today is not about one monolithic problem; it is about a constant stream of narrowly scoped fixes across many code paths. (chromereleases.googleblog.com)That pattern is important for rivals too. Edge, Brave, Opera, and other Chromium-based products must absorb upstream fixes quickly or risk inheriting the same exposure window. For administrators, that means browser policy should be measured by patch freshness and build provenance, not just by brand name. The upstream project may move first, but downstream vendors determine when your endpoint is actually safe.
Chromium as an ecosystem, not a browser
Chromium is now closer to a platform than a product. Its rendering engine, extenbridge, and policy system are all reused or adapted across a broad market of browsers and embedded applications. That scale is one reason a single CVE can have consequences far beyond the original vendor’s user base.This also explains why browser security advisories have become a supply-chain event. A fix in Chromium can alter the risk posture for enterprises lly chose Chrome, because a downstream browser, webview, or embedded shell may still consume the same vulnerable code. That reality is one of the big operational stories in modern desktop security.
The Microsoft Edge Angle
Microsoft’s Security Update Guide is not the original source of this CVE, but it is an important downstream signal for Windows environmenty surfaces Chromium-origin vulnerabilities to tell Edge customers when their installed builds have incorporated the upstream fix. In other words, MSRC is often the place where Windows admins confirm whether Edge has closed the loop on a Chromium issue.That matters because many Windows enterprises standardize on Edge while still encountering Chrome-based compatibility requirements. The browser estate may appear simple at the policy layerit is often mixed, with multiple Chromium consumers moving at slightly different speeds. A clean Chrome patch does not automatically guarantee a clean Edge patch at the same moment.
Why downstream tracking matters
Downstream tracking is useful precisely because it is operational, not theoretical. It tells administrators when a vendor has actually consumed the upstream fix and shippeds. That is a critical distinction in environments where the browser is a mandatory enterprise application rather than a discretionary consumer app.It also reduces ambiguity for patch teams. Rather than treating “Chromium fixed it” as the end of the story, teams can check whether their browser vendor has rolled the fix into the build they deploy. That workflow is slower than it is also safer. Security is a state, not a press release.
What the Severity Label Really Means
The Chromium project’s Medium label should not be misread as “low importance.” Severity labels are useful triage tools, but they are not a substitute for exploitability analysis or deployment context. A mederable memory-corruption bug in a browser component can still be more urgent than a high-rated issue in a rarely used internal tool.This is where defenders need to resist score-chasing. The NVD record in the uploaded material shows that public scoring may still be catching up, while other enrichment sources can suggest a higher-risk vector. That discrepancy is exactly why teams should look at the vuln, the affected version range, and the reachable attack path before deciding how quickly to patch.
Scoring, enrichment, and the real-world queue
The NVD enrichment process often lags vendor disclosure, especially in the first days after publication. That lag can leave defenders with incomplete data even when the technical description already points clearly toward a memory-corruption cthe absence of a final score should not be treated as reassurance.Administrators should therefore triage by shape, not just by score. A remote browser flaw that can be triggered from a crafted page and that involves heap corruption belongs near the front of the queue even if the formal rating is still in motion. That is the kind of judgment good patch management requires.
e
The response path should be simple: verify version, confirm auto-update health, and accelerate deployment to the fixed Chrome branch or the downstream browser build that contains the patch. In enterprise settings, it may also be wise to review browser hardening settings and ensure that update policies are notying security adoption. Small misconfigurations in fleet policy can create outsized exposure windows.Security teams should also look for corroborating indicators in their environment. Crash telemetry, renderer faults, or GPU-process anomalies are not proof of exploitation, but they can help determine whether the vulnerable code path is being exercised in unexpected ways. That is useful both for immediate response and for validating that the fix does nots.
A practical patch checklist
- Confirm Chrome is at or beyond 146.0.7680.153 on all supported endpoints.
- Check whether any Chromium-based browser in the fleet is on a build that has ingested the upstream fix.
- Verify that browser restarts have completed so the old vulnerable process is no longer active.
- Audit endpoint management policies that could delupdates.
- Watch crash telemetry for suspicious graphics-process instability after patch rollout.
Strengths and Opportunities
The positive side of this disclosure is that the fix is clear, bounded, and tied to a specific version threshold, which gives administrators a concrete target. It also reinforces the value of upstream security engineering: the same component that broadens browser capability can be hardened through timely remediation when the bug is found.- The vulnerable build bnd easy to verify.
- The issue is reachable from web content, so remediation has direct security value.
- The patch can be rolled out through normal browser update channels.
- Downstream vendors can align their own remediation with the upstream fix.
- The disclosure gives security teams a chance to audit Chromium update health.
- The incident underscores the importance of memory-safe coding in graphics bridges.
- Enterprises can use the event to tighten browser patch compliance reporting.
Risks and Concerns
The risk profile here is shaped by the fact that this is a browser-facing memory-corruption bug, not a theoretical logic flaw in a little-used module. Even with a Medium label, the combination of remote reachability and heap corruption means defenders should assume practical exploit interest, especially if delayed patching leaves a meaningful population on the vulnerable build.- Heap corruption can sometimes be chained into more serious exploitation.
- Crafted HTML lowers the delivery barrier for attackers.
- Downstream browsers may lag behind Chrome in patch adoption.
- Managed desktops can remain vulnerable longer than consumer devices.
- NVD enrichment may lag, complicating immediate prioritization.
- Graphics bugs can be hard to reproduce and easy to underestimate.
- Browser restarts are required before some patches fully take effect.
Looking Ahead
The next thing to watch is how quickly Chromium’s downstream ecosystem converges on the fixed build. Chrome users will likely move first, but the more interesting story is how fast Edge and other Chromium-based browsers close the gap. In 2026, browser security is measured less by release announcements than by fleet adoption, and that gap is where risk lives.It will also be worth watching whether Google or independent researchers publish more detail on the underlying ANGLE arithmetic failure. If more technical analysis appears, it may reveal whether the bug is isolated or part of a broader class of graphics-layer overflow issues. The broader lesson is familiar but still urgent: the web’s performance stack remains one of its most fragile security surfaces.
- Confirm fleet-wide adoption of the fixed Chromium branch.
- Watch Microsoft’s downstream tracking for Edge-specific build confirmation.
- Review whether browser auto-update policies are slowing remediation.
- Monitor for follow-on ANGLE or graphics-stack advisories.
- Treat heap corruption in page-reachable code as a high-priority security event.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center