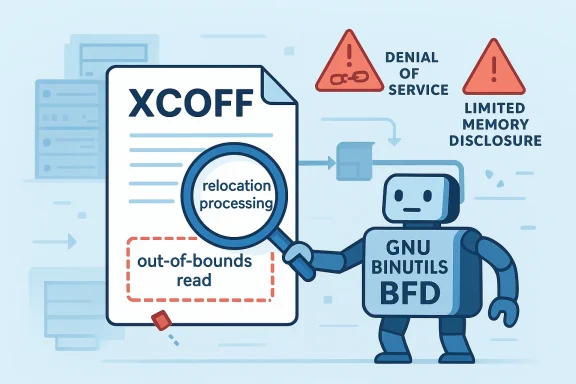
CVE-2026-4647 is a GNU Binutils flaw in the BFD library that can be triggered when parsing specially crafted XCOFF object files, and the security impact is best understood as a mix of service disruption and limited memory disclosure rather than code execution. Microsoft’s advisory frames the issue as a denial-of-service condition with the potential for an attacker to repeatedly drive the impacted component into an unavailable state, which is why the vulnerability has attracted attention well beyond the traditional Unix toolchain audience. (app.opencve.io)
Binutils sits at the heart of many development and reverse-engineering workflows, and BFD is the library inside that stack that understands a wide range of binary formats. That matters because BFD is not just a niche parser; it is a compatibility engine for compilers, linkers, disassemblers, debuggers, and conversion tools that need to inspect object files from different platforms and eras. When a vulnerability lands here, the blast radius can extend from build systems to analysis environments and, in some cases, packaging pipelines.
The format at issue, XCOFF, is especially relevant to IBM AIX and related toolchains. It is less common than ELF on Linux, but it remains important in enterprise environments that support legacy or specialized workloads. That rarity can cut both ways: fewer systems are exposed, but those that are often process untrusted third-party artifacts in automated ways, which increases the practical risk of parser bugs.
The current public record indicates that CVE-2026-4647 was published on March 23, 2026, with later metadata updates following on April 9, 2026. The CNA record attributes the issue to Red Hat, and the acknowledgment credits the reporter as Chen Zhengzhe of Hangzhou Dianzi University. That combination is a reminder that many critical toolchain bugs are found by researchers looking at robustness, not only by attackers in the wild. (app.opencve.io)
The core defect is described as an out-of-bounds read during XCOFF relocation processing. In plain terms, the parser trusts a relocation type value more than it should, then uses that value in a way that can cause reads outside the expected memory bounds. The immediate consequence is typically a crash or an error condition, but the same class of flaw can also reveal data already resident in memory, which is why the vulnerability is scored with low confidentiality impact alongside high availability impact. (app.opencve.io)
A useful way to read this CVE is as part of a broader pattern: binary parsers are endlessly attractive targets because they sit on the boundary between data and code. Every time a toolchain component opens a file, it is effectively making a trust decision about a blob that could have been crafted to stress edge cases in format handling. That is why parser bugs in compilers, linkers, debuggers, and archive tools remain a recurring security theme year after year.
That makes this a classic parser trust-boundary failure. The file is not “running” in the usual sense, but it is still influencing program control flow by shaping how memory gets interpreted. In a large codebase like Binutils, the danger is not only the immediate bug, but the fact that the same design pattern can appear in multiple format handlers. (app.opencve.io)
This is important because the phrase “local” can be misleading. In vulnerability scoring, “local” often means the attacker needs the victim to process a file on the local system, not that the attacker must already be physically present. In practical terms, a malicious XCOFF file sent through a repository, mail attachment, download, or artifact exchange could still trigger the bug when a developer, analyst, or automated tool touches it. (app.opencve.io)
Relocations are among the most sensitive pieces of any object-file format because they determine how references are adjusted before final output or analysis. If a relocation type value is checked too late, too loosely, or against the wrong table, the parser can be driven into code paths that assume the input is sane. In a library like BFD, that can translate directly into memory safety issues.
Another subtle point is that XCOFF support often exists because compatibility is demanded by downstream users, not because the format is fashionable. That can slow modernization, since maintainers are balancing correctness, compatibility, and portability at once. The result is an attack surface that may receive fewer everyday test cases than ELF paths, even though the code still ships in widely used toolchains.
Microsoft’s own explanation of its Security Update Guide emphasizes that CVSS dimensions help map real-world consequence, not just theoretical exploitability. In this case, the high availability rating is the central signal, and the rest of the vector explains why the issue is serious without being treated as remote code execution or a broad integrity compromise.
For defenders, this is exactly the sort of flaw that slips through the cracks between “developer issue” and “security issue.” If a CI pipeline, signing service, or file-analysis appliance consumes untrusted object files, the vulnerability becomes a reliability and availability concern for the organization, not just a workstation annoyance. (app.opencve.io)
The most exposed organizations are those that treat object files as routine data. Build systems, code-signing workflows, malware analysis sandboxes, and archival conversion tools may all touch binary artifacts generated elsewhere. If the toolchain component is embedded in a service, the availability impact can ripple outward to release engineering, developer productivity, and incident response queues.
The other enterprise-specific issue is inventory blindness. Many organizations know where their web servers are, but not where
Developers are also the people most likely to encounter the bug accidentally because they routinely unpack, inspect, and rebuild artifacts from many sources. A malformed object file from a vendor drop, a research corpus, or a fuzzing set can exercise code paths that ordinary end users never touch. That makes the vulnerability a classic “specialist exposure” issue: narrow in population, broad in consequences for those who live in the path.
The CVE record already links to vendor advisories and a Sourceware bug, which is the usual pattern for coordination across the GNU toolchain ecosystem. The open record also shows that the issue was public quickly and then annotated over time, reflecting the normal cadence of post-disclosure enrichment and vendor mapping. (app.opencve.io)
This is also why vulnerability management teams need to map software capabilities, not just package names. If a product can parse XCOFF, it inherits the risk even if the administrator never consciously installed an “XCOFF tool.” Security teams that rely only on top-level package inventories will miss a surprising amount of parser exposure. (app.opencve.io)
For vendors that package Binutils or incorporate its logic into larger platforms, the lesson is double-edged. Broad compatibility helps win enterprise adoption, but it also increases the maintenance and security burden. In a market where customers increasingly ask for secure-by-default toolchains, parser robustness becomes part of product differentiation. (app.opencve.io)
At the same time, too aggressive a fix can break compatibility with obscure but legitimate files. That creates a familiar tension: vendors want safer parsers, but their customers still expect old archives and legacy object files to keep working. The competitive winner is usually the vendor that can thread that needle without surprising users.
The broader lesson is that open-source toolchains are now a security surface in their own right, not merely a plumbing layer beneath the “real” product. As build systems become more automated and as supply-chain scrutiny increases, the line between developer tools and production infrastructure keeps fading. That means a bug in BFD can matter not just to compiler engineers, but to security teams, platform teams, and operations leaders as well.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
Binutils sits at the heart of many development and reverse-engineering workflows, and BFD is the library inside that stack that understands a wide range of binary formats. That matters because BFD is not just a niche parser; it is a compatibility engine for compilers, linkers, disassemblers, debuggers, and conversion tools that need to inspect object files from different platforms and eras. When a vulnerability lands here, the blast radius can extend from build systems to analysis environments and, in some cases, packaging pipelines.The format at issue, XCOFF, is especially relevant to IBM AIX and related toolchains. It is less common than ELF on Linux, but it remains important in enterprise environments that support legacy or specialized workloads. That rarity can cut both ways: fewer systems are exposed, but those that are often process untrusted third-party artifacts in automated ways, which increases the practical risk of parser bugs.
The current public record indicates that CVE-2026-4647 was published on March 23, 2026, with later metadata updates following on April 9, 2026. The CNA record attributes the issue to Red Hat, and the acknowledgment credits the reporter as Chen Zhengzhe of Hangzhou Dianzi University. That combination is a reminder that many critical toolchain bugs are found by researchers looking at robustness, not only by attackers in the wild. (app.opencve.io)
The core defect is described as an out-of-bounds read during XCOFF relocation processing. In plain terms, the parser trusts a relocation type value more than it should, then uses that value in a way that can cause reads outside the expected memory bounds. The immediate consequence is typically a crash or an error condition, but the same class of flaw can also reveal data already resident in memory, which is why the vulnerability is scored with low confidentiality impact alongside high availability impact. (app.opencve.io)
A useful way to read this CVE is as part of a broader pattern: binary parsers are endlessly attractive targets because they sit on the boundary between data and code. Every time a toolchain component opens a file, it is effectively making a trust decision about a blob that could have been crafted to stress edge cases in format handling. That is why parser bugs in compilers, linkers, debuggers, and archive tools remain a recurring security theme year after year.
What the vulnerability changes
The headline detail is that the flaw is not about malformed executable code, but about malformed relocation metadata inside XCOFF content. Relocations tell the linker or object-file consumer how to adjust addresses and references, so they are deeply structural rather than decorative. If a relocation type is not validated before it is consumed, the parser can be led into reading the wrong table entry or dereferencing an unexpected offset. (app.opencve.io)That makes this a classic parser trust-boundary failure. The file is not “running” in the usual sense, but it is still influencing program control flow by shaping how memory gets interpreted. In a large codebase like Binutils, the danger is not only the immediate bug, but the fact that the same design pattern can appear in multiple format handlers. (app.opencve.io)
Why availability takes the lead
The CVSS vector attached to the issue is CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:L/I:N/A:H, which points to local attack vector, low attack complexity, no privileges required, user interaction required, and high availability impact. The emphasis on availability reflects how parser crashes often surface in build, extraction, inspection, or conversion workflows where the user must open or process the malicious file. (app.opencve.io)This is important because the phrase “local” can be misleading. In vulnerability scoring, “local” often means the attacker needs the victim to process a file on the local system, not that the attacker must already be physically present. In practical terms, a malicious XCOFF file sent through a repository, mail attachment, download, or artifact exchange could still trigger the bug when a developer, analyst, or automated tool touches it. (app.opencve.io)
Why confidentiality is only low
The record shows low confidentiality impact, which suggests an out-of-bounds read could expose a limited amount of memory, but not in a way that is expected to yield broad or reliable data theft. That distinction matters because it shapes triage: this is more likely to be a crash-and-signal issue than a full memory-extraction primitive. Still, even a small read past bounds can matter if the parser processes secrets, pointers, or internal addresses. (app.opencve.io)- The flaw is triggered during relocation parsing, not normal file execution.
- The most obvious outcome is denial of service.
- Limited memory disclosure remains possible because the bug is an out-of-bounds read.
- The file must generally be user-supplied or user-processed.
- The issue is most relevant to XCOFF-aware workflows. (app.opencve.io)
How XCOFF relocations fit into Binutils
XCOFF is one of those formats that many Windows and Linux users barely notice, yet it persists because enterprise toolchains do not disappear just because the mainstream has moved on. BFD’s value proposition has always been breadth: it can understand many binary formats and present a unified API to the rest of Binutils. That breadth creates a maintenance burden, because every format has its own rules, edge cases, and historical quirks.Relocations are among the most sensitive pieces of any object-file format because they determine how references are adjusted before final output or analysis. If a relocation type value is checked too late, too loosely, or against the wrong table, the parser can be driven into code paths that assume the input is sane. In a library like BFD, that can translate directly into memory safety issues.
The practical parser problem
The immediate engineering lesson is straightforward: format handlers must validate both the type and range of relocation metadata before using it as an index or selector. That sounds banal, but in parser code, it is easy to drift into assumptions that were true for “normal” files and false for adversarial ones. Defensive parsing is not optional in this layer; it is the product. (app.opencve.io)Another subtle point is that XCOFF support often exists because compatibility is demanded by downstream users, not because the format is fashionable. That can slow modernization, since maintainers are balancing correctness, compatibility, and portability at once. The result is an attack surface that may receive fewer everyday test cases than ELF paths, even though the code still ships in widely used toolchains.
Severity and scoring
The publicly visible CVSS score of 6.1 Medium is easy to dismiss, but that would be a mistake. Medium severity in a file parser often means “highly annoying in practice,” especially when the bug is easy to trigger and lands inside an automated workflow. A crash in a developer tool can stop builds, break packaging, and disrupt analysis pipelines in ways that are operationally expensive even if the direct technical impact is limited. (app.opencve.io)Microsoft’s own explanation of its Security Update Guide emphasizes that CVSS dimensions help map real-world consequence, not just theoretical exploitability. In this case, the high availability rating is the central signal, and the rest of the vector explains why the issue is serious without being treated as remote code execution or a broad integrity compromise.
Why user interaction matters
The UI:R component means the attacker cannot usually fire this off in the background without any victim action. Someone has to open, import, inspect, convert, or otherwise process the malicious file. That makes the bug less wormable, but not benign, because many build and validation systems are intentionally configured to auto-process inbound artifacts. (app.opencve.io)For defenders, this is exactly the sort of flaw that slips through the cracks between “developer issue” and “security issue.” If a CI pipeline, signing service, or file-analysis appliance consumes untrusted object files, the vulnerability becomes a reliability and availability concern for the organization, not just a workstation annoyance. (app.opencve.io)
- Medium does not mean trivial in a parser.
- High availability impact is the key operational concern.
- User interaction reduces reach but not business impact.
- No privileges required makes initial access simpler.
- The flaw is still serious even without integrity loss. (app.opencve.io)
Impact on enterprises
Enterprises are the most likely to care about this CVE if they maintain cross-platform build farms, legacy AIX support, artifact inspection systems, or security tooling that ingests object files. Those environments often automate file processing at scale, which makes a crash-causing parser bug more consequential than it would be on an isolated desktop. That is the hidden multiplier: one malformed input can interrupt many jobs or wedge a service that is assumed to be trusted. (app.opencve.io)The most exposed organizations are those that treat object files as routine data. Build systems, code-signing workflows, malware analysis sandboxes, and archival conversion tools may all touch binary artifacts generated elsewhere. If the toolchain component is embedded in a service, the availability impact can ripple outward to release engineering, developer productivity, and incident response queues.
Enterprise exposure patterns
A useful way to think about enterprise risk is to separate ingestion from execution. The vulnerable component is not the application logic that consumes business data, but the binary parser that sits earlier in the workflow and may be invoked by trusted automation. That means traditional perimeter defenses can miss the issue because the input already looks like an internal file by the time it arrives. (app.opencve.io)The other enterprise-specific issue is inventory blindness. Many organizations know where their web servers are, but not where
binutils, gdb, or downstream packages derived from BFD are installed. When the vulnerable library is bundled into a larger distribution or appliance, the apparent surface area may be much larger than the visible package count suggests. (app.opencve.io)Impact on consumers and developers
For individual developers and power users, the risk is less about mass compromise and more about workflow interruption and trust erosion. If an object file from a third party can crash an inspection tool, that undermines confidence in the analysis chain. In practical terms, the user loses time, the tool loses reliability, and the format parser becomes a chokepoint. (app.opencve.io)Developers are also the people most likely to encounter the bug accidentally because they routinely unpack, inspect, and rebuild artifacts from many sources. A malformed object file from a vendor drop, a research corpus, or a fuzzing set can exercise code paths that ordinary end users never touch. That makes the vulnerability a classic “specialist exposure” issue: narrow in population, broad in consequences for those who live in the path.
Tooling trust and developer fatigue
There is also a softer but important effect: repeated parser crashes create fatigue. When developers start to assume that a file-format tool might fail unpredictably, they build workarounds, disable checks, or stop trusting automated output. That erosion of trust is an underappreciated cost of vulnerabilities like this one, especially in release engineering and security-analysis teams. (app.opencve.io)- Builds may fail on malformed third-party inputs.
- Analysis pipelines may need extra quarantine steps.
- Developers may lose trust in inspection tooling.
- Error handling becomes part of the security posture.
- Format parsers become a policy enforcement point. (app.opencve.io)
The upstream and downstream response
Because this is a Binutils issue, the upstream response normally matters as much as the distro response. Toolchain bugs tend to be fixed first in source form and then carried downstream by operating-system vendors, package maintainers, and SDK distributors. That means remediation can arrive at different times depending on whether you consume a base distribution package, a toolset package, or a vendor-embedded copy. (app.opencve.io)The CVE record already links to vendor advisories and a Sourceware bug, which is the usual pattern for coordination across the GNU toolchain ecosystem. The open record also shows that the issue was public quickly and then annotated over time, reflecting the normal cadence of post-disclosure enrichment and vendor mapping. (app.opencve.io)
Why distro patch cadence matters
In practice, users should not assume that “Binutils is fixed” means every package they install is fixed.binutils, gdb, gcc-toolset-*, and derivative packages may each carry their own builds and patch queues. That fragmentation is especially visible in enterprise Linux ecosystems, where the same library can appear through multiple channels. (app.opencve.io)This is also why vulnerability management teams need to map software capabilities, not just package names. If a product can parse XCOFF, it inherits the risk even if the administrator never consciously installed an “XCOFF tool.” Security teams that rely only on top-level package inventories will miss a surprising amount of parser exposure. (app.opencve.io)
Competitive implications
CVE-2026-4647 does not create a dramatic market-shifting moment, but it does highlight a persistent competitive reality: the more file formats a tool supports, the larger the attack surface becomes. That is true for GNU Binutils, but it is also true for rival disassemblers, linkers, and reverse-engineering suites. Feature breadth is still a selling point, yet every supported format adds parser risk.For vendors that package Binutils or incorporate its logic into larger platforms, the lesson is double-edged. Broad compatibility helps win enterprise adoption, but it also increases the maintenance and security burden. In a market where customers increasingly ask for secure-by-default toolchains, parser robustness becomes part of product differentiation. (app.opencve.io)
Security as a toolchain feature
Over time, there is a real competitive advantage in shipping stricter validation, clearer crash resistance, and better fuzz coverage. Teams that can say their binary-analysis stack fails safely and predictably will have an easier time convincing enterprise buyers. In that sense, each bug like this nudges the market toward more defensive parsing and better hardening.At the same time, too aggressive a fix can break compatibility with obscure but legitimate files. That creates a familiar tension: vendors want safer parsers, but their customers still expect old archives and legacy object files to keep working. The competitive winner is usually the vendor that can thread that needle without surprising users.
Strengths and Opportunities
This vulnerability has a clear remediation path, and that is one of the best things going for defenders. Because the issue is tied to a specific parser path and a specific file format, vendors can address it with targeted validation rather than sweeping architectural change. It also provides an opportunity to improve test coverage for format handling that historically receives less attention than mainstream ELF workflows. (app.opencve.io)- The bug is narrow enough to patch without redesigning BFD.
- It reinforces the value of fuzzing binary parsers.
- It can improve validation for other relocation paths.
- It gives security teams a concrete inventory question: who processes XCOFF?
- It encourages better separation between trusted and untrusted artifacts.
- It can reduce accidental crashes in build and analysis workflows.
- It is a chance to tighten defensive checks across toolchains. (app.opencve.io)
Risks and Concerns
The obvious concern is that the issue is easy to underestimate because the severity is only medium and the format is comparatively niche. That is exactly the kind of bug that can linger in enterprise environments, especially when the vulnerable package is bundled into larger products or toolsets. Another concern is that availability failures are often operationally severe even when they do not look dramatic on a CVE sheet. (app.opencve.io)- Niche formats are often overlooked in asset inventories.
- Crash-only bugs can still halt critical pipelines.
- Multiple package names can hide the same library exposure.
- Legacy environments may be slow to patch.
- Automated ingestion systems can turn a file bug into a service outage.
- Low confidentiality impact may lull teams into deprioritizing remediation.
- Parser bugs can repeat across related code paths if validation patterns are inconsistent. (app.opencve.io)
Looking Ahead
The next question is not whether this particular CVE can be exploited at scale, but whether organizations have the tooling and discipline to identify where XCOFF-capable parsing exists in their estate. In many companies, the answer will be “not yet,” because file-format risk is still under-inventoried compared with web, email, and identity exposure. That gap is where parser bugs continue to surprise defenders. (app.opencve.io)The broader lesson is that open-source toolchains are now a security surface in their own right, not merely a plumbing layer beneath the “real” product. As build systems become more automated and as supply-chain scrutiny increases, the line between developer tools and production infrastructure keeps fading. That means a bug in BFD can matter not just to compiler engineers, but to security teams, platform teams, and operations leaders as well.
- Verify whether your environments process XCOFF at all.
- Check whether
binutils,gdb, orgcc-toolsetpackages are present. - Prioritize systems that ingest untrusted object files automatically.
- Treat parser crashes as availability incidents, not just software bugs.
- Watch for downstream vendor advisories and package rebuilds.
- Reassess fuzzing and regression testing around relocation handling. (app.opencve.io)
Source: MSRC Security Update Guide - Microsoft Security Response Center