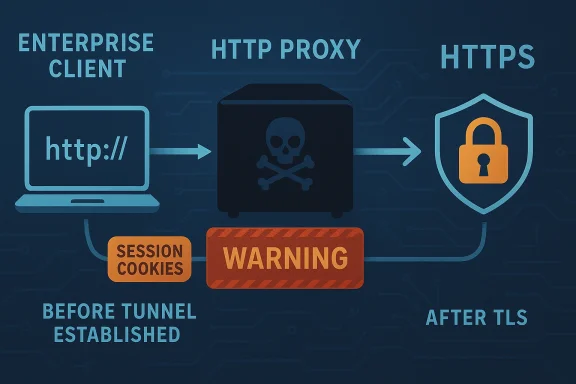
When a vulnerability lives in a network library rather than an end-user app, the blast radius is often much larger than the CVSS score alone suggests. That is the case with CVE-2026-5119, a libsoup flaw that can leak session cookies in cleartext during HTTPS tunnel establishment through an HTTP proxy, creating a realistic path to session hijacking or user impersonation. The issue sits at the intersection of proxy handling, cookie propagation, and encrypted transport setup, which makes it especially dangerous in enterprise environments that rely on outbound proxies for policy, monitoring, or egress control. Red Hat’s CNA record and the NVD entry both describe the bug as an information-disclosure problem rooted in cleartext transmission of sensitive data, with CWE-319 assigned to the flaw
Libsoup is not a niche component. It is a long-running GNOME HTTP library used by desktops, services, and middleware stacks that need client-side HTTP behavior, server-side request handling, or proxy support. Red Hat’s advisories repeatedly describe libsoup as an HTTP client and server library for GNOME, and the NVD record for CVE-2026-5119 places it alongside Red Hat Enterprise Linux platforms and the upstream GNOME package, underscoring how far the affected code can travel into production systems
The security story around libsoup in 2025 and 2026 shows a pattern: the project keeps running into bugs at protocol boundaries where developers assume one layer has already guaranteed safety. That has included cookie handling, redirect logic, host header construction, HTTP/2 processing, and proxy-related behaviors. In that context, CVE-2026-5119 is not an isolated oddity; it is another reminder that stateful network plumbing is where subtle privacy failures are born
The specific weakness here is especially unsettling because it does not require code execution, memory corruption, or exotic exploit development. Instead, a malicious proxy or a network-positioned attacker can simply observe a CONNECT request that contains sensitive session cookies in the clear before the TLS tunnel is fully established. In practical terms, that means the attacker may inherit the user’s authenticated session without needing to break encryption at all; the mistake occurs before encryption begins
Microsoft’s Security Update Guide entry for the CVE points readers to the same upstream and vendor references, which is a good reminder that downstream product teams are tracking the issue as a real supply-chain exposure, not just an academic upstream note. The record is also a useful signal that defenders should think beyond “Linux package update” and consider which Microsoft-adjacent or enterprise Linux images embed libsoup in their software bill of materials
The danger is magnified in environments that centrally route traffic through HTTP proxies for inspection or compliance. A malicious proxy, a compromised proxy appliance, or a network attacker in the right position can exploit the fact that the sensitive data leaves the client before the tunnel exists. That makes this vulnerability structurally different from a flaw inside an established TLS session.
That distinction matters because many security teams focus on encrypted traffic payloads while underweighting the bootstrap phase. Yet bootstrap mistakes can be just as serious as post-handshake TLS problems. If the authentication secret leaks before the tunnel is up, the fact that the destination connection will later be encrypted does not help.
Red Hat’s associated entries point to issue tracking and vendor guidance, which suggests the bug is already recognized upstream and in downstream security workflows. That matters because a CVE with issue tracker references tends to move from abstract disclosure into actual remediation and backport work faster than a vague warning ever would. The same pattern appeared in other recent libsoup CVEs, where Red Hat tied advisories to GNOME issue IDs and affected-package lists
That disagreement does not make the issue less important. It means the operational question is not “Can this be abused?” but rather “Under what deployment conditions does abuse become practical?” For organizations with explicit HTTP proxy configuration, the answer may be much easier than the lower score implies.
For security teams, that means the most prudent posture is not to wait for a polished exploit proof-of-concept. The combination of a sensitive credential type, a cleartext transmission window, and a proxy-mediated path is enough to justify immediate inventory and patch review.
This is also why the issue is so hard to reason about from a distance. A developer may correctly assume that “HTTPS traffic is encrypted,” while forgetting that proxy negotiation is an HTTP transaction first. If cookies are attached to that transaction, they can leave the client in plaintext even though the eventual destination is TLS-protected.
This is especially problematic because many enterprises trust proxies as enforcement points rather than as adversarial actors. That trust may be operationally reasonable, but it becomes a liability if the proxy is compromised, misconfigured, or run by a third party. A malicious proxy only needs one successful capture to turn an otherwise routine browsing session into an account takeover opportunity.
In the enterprise, the issue can have downstream effects beyond a single user. If an admin browses internal dashboards through a libsoup-based client behind a proxy and their cookie is intercepted, an attacker may gain access to internal resources, ticketing systems, monitoring panels, or browser-based administration consoles. The risk is not theoretical; it follows directly from the security role cookies play in modern web authentication.
That matters because it changes how defenders should view the project. This is not a one-off coding mistake in an obscure corner. It is a sustained maintenance challenge in a library that sits on the perimeter between application logic and network reality. The more central the library, the more damage each small mistake can do.
CVE-2026-5119 fits neatly into that history. Instead of leaking a proxy password or allowing a bad redirect to expose credentials, it leaks session cookies during proxy tunnel setup. The surface has changed, but the lesson has not: in a network library, every header decision is a security decision.
This is why CVEs in foundational libraries should trigger asset inventory work, not just patch ticketing. If a fleet uses mixed Linux images, desktop clients, or containerized services with proxy settings, the exposure surface can be wider than the package maintainer’s own product list suggests.
For enterprises, the story is more serious. Many companies route outbound traffic through explicit proxies, security gateways, or content filtering systems. In that kind of topology, a flawed CONNECT implementation can turn a policy control into a credential sink, and a compromised proxy can harvest session cookies from privileged users at scale. That is a high-leverage failure because one intercepted session may unlock multiple internal systems.
The key point is that the flaw does not need a mass-market worm to be valuable. A targeted attacker who can position themselves as a proxy or on-path observer only needs to catch the right cookie once. For many account targets, one cookie is enough.
The most concerning enterprise scenarios include:
The better mental model is that confidentiality can fail at multiple layers. A request may be encrypted on the wire to the destination, but still disclose secrets to an intermediary during setup. Layered security only works if each layer is actually aware of the others.
That is why bugs like CVE-2026-5119 are often best understood as boundary violations. The application thought it was speaking only to a tunnel broker. In reality, it was disclosing session state to a separate party that should not have been in the loop.
A simple validation regimen should include:
That broad mapping is important because many organizations do not patch “libraries” in isolation. They patch distributions, container bases, or vendor bundles. The actual remediation step may therefore arrive through OS errata, application updates, or image refreshes rather than a direct libsoup package install.
This matters operationally because a security team can no longer say, “We don’t use libsoup directly.” If a product team ships a Linux-based appliance, desktop image, or container that embeds the library, the issue becomes theirs too. That is the modern supply-chain reality.
A practical response sequence is:
The other concern is patch latency. Because the issue sits in a dependency, not a headline application, organizations may delay remediation while waiting for downstream packaging. That delay can leave a surprisingly broad window of exposure.
A second thing to watch is whether additional disclosure or replay-style bugs emerge in adjacent proxy-handling code. libsoup has already seen multiple security issues in cookie, redirect, and header logic, and that pattern suggests the maintainers are cleaning up an area that has accumulated technical debt over time. The good news is that maintenance attention is focused there; the bad news is that the area clearly deserves it.
Source: NVD Security Update Guide - Microsoft Security Response Center
 Overview
Overview
Libsoup is not a niche component. It is a long-running GNOME HTTP library used by desktops, services, and middleware stacks that need client-side HTTP behavior, server-side request handling, or proxy support. Red Hat’s advisories repeatedly describe libsoup as an HTTP client and server library for GNOME, and the NVD record for CVE-2026-5119 places it alongside Red Hat Enterprise Linux platforms and the upstream GNOME package, underscoring how far the affected code can travel into production systemsThe security story around libsoup in 2025 and 2026 shows a pattern: the project keeps running into bugs at protocol boundaries where developers assume one layer has already guaranteed safety. That has included cookie handling, redirect logic, host header construction, HTTP/2 processing, and proxy-related behaviors. In that context, CVE-2026-5119 is not an isolated oddity; it is another reminder that stateful network plumbing is where subtle privacy failures are born
The specific weakness here is especially unsettling because it does not require code execution, memory corruption, or exotic exploit development. Instead, a malicious proxy or a network-positioned attacker can simply observe a CONNECT request that contains sensitive session cookies in the clear before the TLS tunnel is fully established. In practical terms, that means the attacker may inherit the user’s authenticated session without needing to break encryption at all; the mistake occurs before encryption begins
Microsoft’s Security Update Guide entry for the CVE points readers to the same upstream and vendor references, which is a good reminder that downstream product teams are tracking the issue as a real supply-chain exposure, not just an academic upstream note. The record is also a useful signal that defenders should think beyond “Linux package update” and consider which Microsoft-adjacent or enterprise Linux images embed libsoup in their software bill of materials
Why cleartext cookies matter
Cookies are not just session convenience data. In many systems, they are the primary bearer token that proves a browser or client is already authenticated. If an attacker can capture them in transit, they may be able to replay the session, access protected resources, or impersonate the user until the cookie expires or the server invalidates it. That is why a disclosure bug in the CONNECT phase is more than a cosmetic privacy issue.The danger is magnified in environments that centrally route traffic through HTTP proxies for inspection or compliance. A malicious proxy, a compromised proxy appliance, or a network attacker in the right position can exploit the fact that the sensitive data leaves the client before the tunnel exists. That makes this vulnerability structurally different from a flaw inside an established TLS session.
Why the proxy path is the real attack surface
The CONNECT method exists specifically to bootstrap a tunnel through an intermediary. It is a legitimate and widely used design, but it also creates a tiny window in which applications can accidentally reveal metadata and credentials to the proxy itself. In this case, libsoup apparently sends session cookies too early, turning a proxy negotiation into an unintended credential leak.That distinction matters because many security teams focus on encrypted traffic payloads while underweighting the bootstrap phase. Yet bootstrap mistakes can be just as serious as post-handshake TLS problems. If the authentication secret leaks before the tunnel is up, the fact that the destination connection will later be encrypted does not help.
What the public record says
The NVD description for CVE-2026-5119 is straightforward: when establishing HTTPS tunnels through a configured HTTP proxy, sensitive session cookies are sent in cleartext within the initial HTTP CONNECT request. NVD attributes the initial technical report to Red Hat, lists CWE-319, and flags the issue as an information disclosure weakness. The publicly visible NVD page also records the NIST analysis status as still pending, which means defenders should treat the vendor description as the most concrete technical statement currently availableRed Hat’s associated entries point to issue tracking and vendor guidance, which suggests the bug is already recognized upstream and in downstream security workflows. That matters because a CVE with issue tracker references tends to move from abstract disclosure into actual remediation and backport work faster than a vague warning ever would. The same pattern appeared in other recent libsoup CVEs, where Red Hat tied advisories to GNOME issue IDs and affected-package lists
How to interpret the CVSS split
The public record shows a noticeable difference between the NVD’s provisional score and Red Hat’s CNA score. NVD’s preliminary vector is more severe because it treats the issue as network-reachable with no privileges and no user interaction, while Red Hat’s lower score reflects higher attack complexity and user interaction requirements. That spread is a useful warning sign: the exploit path is not fully settled, and the real-world risk may depend heavily on whether the target environment forces proxy use and cookie-bearing requests through the vulnerable pathThat disagreement does not make the issue less important. It means the operational question is not “Can this be abused?” but rather “Under what deployment conditions does abuse become practical?” For organizations with explicit HTTP proxy configuration, the answer may be much easier than the lower score implies.
The role of issue tracking and upstream validation
CVE records that include upstream issue references usually tell defenders two things. First, the bug is likely reproducible or at least believed credible by the maintainer community. Second, patches or mitigation discussions are probably already underway, even if they are not yet widely shipped. In the case of libsoup, recent CVEs have followed exactly that arc, from GNOME issue references to Red Hat advisories and then to package-level fixes in downstream productsFor security teams, that means the most prudent posture is not to wait for a polished exploit proof-of-concept. The combination of a sensitive credential type, a cleartext transmission window, and a proxy-mediated path is enough to justify immediate inventory and patch review.
Why this flaw is different from ordinary HTTPS bugs
Most HTTPS-related flaws are discussed in terms of TLS downgrade, certificate validation, or transport-layer interception. CVE-2026-5119 is subtler. The actual encryption protocol may be functioning correctly, while the application leaks secrets before the secure tunnel is negotiated. That is a classic example of a protocol stack bug living one layer above where most teams expect the danger to be.This is also why the issue is so hard to reason about from a distance. A developer may correctly assume that “HTTPS traffic is encrypted,” while forgetting that proxy negotiation is an HTTP transaction first. If cookies are attached to that transaction, they can leave the client in plaintext even though the eventual destination is TLS-protected.
CONNECT versus end-to-end confidentiality
The CONNECT method is intended to create an opaque pipe from the client to the final origin server. But before that pipe exists, the proxy sees the setup chatter, and the application decides what to include in it. If the app mistakenly attaches cookies meant for the final secure origin, the proxy becomes a privileged witness to data it should never see.This is especially problematic because many enterprises trust proxies as enforcement points rather than as adversarial actors. That trust may be operationally reasonable, but it becomes a liability if the proxy is compromised, misconfigured, or run by a third party. A malicious proxy only needs one successful capture to turn an otherwise routine browsing session into an account takeover opportunity.
Why session cookies are a high-value target
Session cookies are often more valuable than passwords in active compromise scenarios because they bypass authentication entirely. They can also evade password rotation and sometimes multi-factor authentication, depending on how long the session remains valid and what actions the application allows after login. That makes cookie leakage a high-impact confidentiality problem even if the underlying service continues to function normally.In the enterprise, the issue can have downstream effects beyond a single user. If an admin browses internal dashboards through a libsoup-based client behind a proxy and their cookie is intercepted, an attacker may gain access to internal resources, ticketing systems, monitoring panels, or browser-based administration consoles. The risk is not theoretical; it follows directly from the security role cookies play in modern web authentication.
Historical context: libsoup’s recent security pattern
Recent libsoup disclosures show a library under sustained pressure from edge-case protocol handling. NVD entries in 2025 and early 2026 described bugs involving cookies, redirects, header construction, HTTP/2 behavior, and host parsing. Seen together, they form a pattern: the library is repeatedly being asked to make policy decisions across ambiguous transport boundaries, and each of those boundaries can expose confidential data if the logic is slightly offThat matters because it changes how defenders should view the project. This is not a one-off coding mistake in an obscure corner. It is a sustained maintenance challenge in a library that sits on the perimeter between application logic and network reality. The more central the library, the more damage each small mistake can do.
What the 2025 cookie and redirect bugs taught us
Earlier libsoup vulnerabilities showed that cookies and proxy-related metadata are unusually easy to mishandle. One issue affected cookie date parsing, another allowed proxy authentication credentials to leak on redirect, and others touched host-header construction and caching semantics. The repeated theme is that headers are not just text—they are policy carriers, and a small bug can accidentally widen the audience for secrets that should stay scoped to one origin or one connectionCVE-2026-5119 fits neatly into that history. Instead of leaking a proxy password or allowing a bad redirect to expose credentials, it leaks session cookies during proxy tunnel setup. The surface has changed, but the lesson has not: in a network library, every header decision is a security decision.
Why recurring libsoup bugs matter to ecosystem risk
Because libsoup is used by GNOME-adjacent and other Linux software, each bug has the potential to ripple outward into desktops, agents, management tools, and middleware. That means organizations may be affected without consciously choosing to deploy “libsoup” as a product. They may simply inherit it as a transitive dependency from a browser engine, desktop component, or enterprise package.This is why CVEs in foundational libraries should trigger asset inventory work, not just patch ticketing. If a fleet uses mixed Linux images, desktop clients, or containerized services with proxy settings, the exposure surface can be wider than the package maintainer’s own product list suggests.
Enterprise impact versus consumer impact
For consumers, the immediate concern is theft of logged-in sessions in apps that rely on HTTP proxy settings and libsoup-backed network functions. That could mean browser-adjacent tools, desktop software, or lightweight clients whose users never realized the proxy layer could see more than expected. The practical risk is highest where users are on hostile networks, rely on corporate Wi-Fi with intermediary proxies, or use third-party proxy services.For enterprises, the story is more serious. Many companies route outbound traffic through explicit proxies, security gateways, or content filtering systems. In that kind of topology, a flawed CONNECT implementation can turn a policy control into a credential sink, and a compromised proxy can harvest session cookies from privileged users at scale. That is a high-leverage failure because one intercepted session may unlock multiple internal systems.
Consumer exposure is more situational
Consumer exposure depends on whether the affected application actually uses libsoup and whether the user is configured to go through a proxy. Most home users are not running complex enterprise proxies, which may reduce the average case. But public Wi-Fi, ISP-provided proxies, privacy proxies, and corporate remote-access setups all create plausible exposure paths.The key point is that the flaw does not need a mass-market worm to be valuable. A targeted attacker who can position themselves as a proxy or on-path observer only needs to catch the right cookie once. For many account targets, one cookie is enough.
Enterprise exposure can be systemic
In an enterprise, the same bug can affect many endpoints at once if the application stack is standardized. If the affected client or service is deployed widely, and if corporate policy requires proxying, then the attack surface is not one user—it is every user session that transits the vulnerable code path. That is why proxy-specific flaws often become incident-response problems rather than routine patch cycles.The most concerning enterprise scenarios include:
- fleets with mandatory outbound HTTP proxies,
- Linux desktops using libsoup-backed applications,
- service accounts that authenticate to web dashboards,
- third-party proxy appliances that log or inspect traffic,
- contractors or remote workers on managed endpoints,
- kiosk or shared systems where session reuse is common.
How defenders should think about the bug class
This vulnerability belongs to a broader class of issues where encryption is undermined by metadata handling rather than cipher failure. The attacker does not need to crack TLS. They simply exploit the sequence of operations around TLS, HTTP, and proxy bootstrapping. That distinction is important because many security programs still organize their controls around the assumption that “encrypted equals safe.”The better mental model is that confidentiality can fail at multiple layers. A request may be encrypted on the wire to the destination, but still disclose secrets to an intermediary during setup. Layered security only works if each layer is actually aware of the others.
The trust boundary problem
HTTP proxies are a trust boundary by design. They see enough of the traffic path to route and inspect it, but not always enough to justify receiving origin-authentication secrets. If a library places cookies into the CONNECT request, it quietly shifts data across that boundary.That is why bugs like CVE-2026-5119 are often best understood as boundary violations. The application thought it was speaking only to a tunnel broker. In reality, it was disclosing session state to a separate party that should not have been in the loop.
The importance of proxy-aware testing
One practical lesson for engineering teams is to test applications behind real proxies, not just direct TLS endpoints. Bugs like this can sit dormant in direct-connect labs and only appear when the client is forced through an HTTP proxy. That makes proxy simulation a necessary part of secure QA, especially for applications that depend on upstream libraries for transport behavior.A simple validation regimen should include:
- forcing traffic through an explicit HTTP proxy,
- capturing the initial CONNECT exchange,
- checking whether cookies or auth headers appear before tunnel establishment,
- confirming whether fixes suppress sensitive metadata,
- repeating tests across both desktop and containerized deployments.
Patch management and ecosystem response
Red Hat’s involvement in the CVE record suggests that the fix path will likely follow the now-familiar model of upstream issue, downstream advisories, and package updates across supported Linux releases. The NVD entry lists affected CPEs for Red Hat Enterprise Linux 7, 8, 9, and 10, as well as the generic GNOME libsoup package, which indicates broad downstream relevance rather than a narrow application-specific bugThat broad mapping is important because many organizations do not patch “libraries” in isolation. They patch distributions, container bases, or vendor bundles. The actual remediation step may therefore arrive through OS errata, application updates, or image refreshes rather than a direct libsoup package install.
Why supply-chain visibility matters
Microsoft’s Security Update Guide has increasingly served as a downstream visibility layer for open-source components embedded in Microsoft-managed or Microsoft-adjacent products. While the page for CVE-2026-5119 is JS-rendered and difficult to scrape directly, the vendor-linked record itself confirms that Microsoft is tracking the issue in its update guide ecosystem. That is a reminder that open-source library bugs are now part of the mainstream enterprise patch and inventory conversation, not a separate siloThis matters operationally because a security team can no longer say, “We don’t use libsoup directly.” If a product team ships a Linux-based appliance, desktop image, or container that embeds the library, the issue becomes theirs too. That is the modern supply-chain reality.
What to do first
Organizations should start with exposure mapping rather than blind patching panic. Determine which systems use libsoup, which of those systems are configured for HTTP proxies, and which applications transmit authenticated sessions through those proxies. Then prioritize environments where session cookies correspond to administrative, support, or remote-access roles.A practical response sequence is:
- inventory libsoup usage across endpoints, images, and appliances,
- identify proxy-dependent workflows,
- locate products that use cookie-based sessions over CONNECT,
- apply vendor fixes or package updates as they land,
- rotate high-value sessions if interception is suspected.
Strengths and Opportunities
The good news is that CVE-2026-5119 is the kind of issue for which clear architecture changes can meaningfully reduce risk. It does not require new hardware, major redesign, or deep cryptographic intervention. It needs better boundary enforcement, better proxy handling, and better validation that secrets never leave the client before the tunnel is established.- The flaw is conceptually simple to understand, which should help defenders prioritize it quickly.
- Vendors and upstream maintainers already have a well-established advisory path for libsoup.
- The bug class is patchable without changing application business logic.
- Proxy-aware regression tests can catch similar problems in the future.
- Enterprises can reduce exposure by segmenting high-value sessions away from proxy-mediated paths where feasible.
- Security teams can use the event to improve asset inventory for embedded open-source components.
- The disclosure reinforces the value of dependency-aware SBOM practices.
A chance to improve transport-layer hygiene
The broader opportunity here is to harden client libraries against accidental metadata leakage. If maintainers use this incident to audit how cookies, authorization headers, and proxy credentials are handled across CONNECT and redirect paths, the long-term benefit will extend beyond a single CVE. That is the right kind of defensive housekeeping.Risks and Concerns
The obvious risk is cookie theft, but the larger concern is how quietly this bug could blend into normal traffic. A user may never see an error, a proxy may never fail, and the intercepted cookie may never be detected until after the session has been abused. That makes this a stealthy confidentiality failure rather than an immediate outage problem.- Session hijacking may occur without additional malware on the endpoint.
- Malicious or compromised proxies can harvest credentials silently.
- High-value admin sessions are especially attractive targets.
- Proxy-heavy enterprise environments increase exposure breadth.
- Detection may be hard if logs do not record CONNECT request contents.
- Users may assume HTTPS protects them when the leak occurs before TLS begins.
- Downstream products may inherit the issue without obvious branding of libsoup.
The danger of false confidence
One concern is that teams may underestimate the bug because it is “only” information disclosure. But information disclosure often becomes the first step in a larger attack chain. Once an attacker has a valid session cookie, they may move laterally, escalate access through the web UI, or extract additional data from trusted portals.The other concern is patch latency. Because the issue sits in a dependency, not a headline application, organizations may delay remediation while waiting for downstream packaging. That delay can leave a surprisingly broad window of exposure.
Looking Ahead
The next meaningful milestone will be the appearance of concrete upstream fixes and downstream package advisories, followed by confirmation of which product lines actually ship the vulnerable libsoup build. Once that happens, defenders can move from exposure assessment to targeted remediation. Until then, the safest assumption is that any system using libsoup through an HTTP proxy deserves review.A second thing to watch is whether additional disclosure or replay-style bugs emerge in adjacent proxy-handling code. libsoup has already seen multiple security issues in cookie, redirect, and header logic, and that pattern suggests the maintainers are cleaning up an area that has accumulated technical debt over time. The good news is that maintenance attention is focused there; the bad news is that the area clearly deserves it.
What to watch next
- upstream patch publication and changelog details,
- downstream advisories for Linux distributions and vendor bundles,
- whether browsers or desktop apps inherit the fix through system libraries,
- any proof-of-concept demonstrating cookie capture during CONNECT,
- whether proxy-aware logging guidance is updated by vendors,
- whether Microsoft’s Security Update Guide adds broader product mappings,
- whether additional libsoup CVEs cluster around the same proxy and header paths.
Source: NVD Security Update Guide - Microsoft Security Response Center