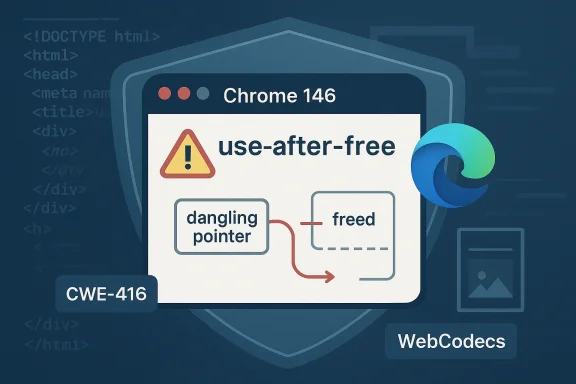
Chromium’s CVE-2026-5280 is another reminder that browser security is still dominated by memory-safety failures in code paths most users never think about. The flaw is a use-after-free in WebCodecs affecting Google Chrome prior to 146.0.7680.178, and Google says a remote attacker could exploit it through a crafted HTML page to execute arbitrary code inside the browser sandbox. Microsoft has also surfaced the issue in its security guidance, which matters because Edge and other Chromium-based products inherit the same upstream fix path and the same operational urgency. w CVE lands in a familiar place: the intersection of rich web media, complex object lifecycles, and browser sandboxing. WebCodecs is one of those modern platform features that looks innocuous to users but sits deep in a browser’s media pipeline, where timing, memory ownership, and decoding state can all interact in subtle ways. When a flaw in that kind of code becomes remotely reachable from HTML, defenders immediately have to treat it as a potentially high-impact issue, even if exploitation still has to cross the sandbox boundary. Google’s own description calls the issue High severity, and the downstream advisory context in Microsoft’s Security Update Guide confirms the patch relevance for Windows environments that rely on Chromium-based browsers.
This is not an isol early April 2026 have already shown how quickly Chromium bugs can cascade across the ecosystem, from Chrome to Edge to enterprise patch-management tools. The broader pattern is important: Google fixes the upstream browser, Microsoft mirrors the status for Edge customers, and security teams have to map both the browser version and the device’s rollout state before they can say a fleet is safe. That pattern is visible in Microsoft’s own guidance and in the way Chromium issues are tracked as they move from vendor disclosure to downstream visibility.
The practical lesson for administrators is straightforward, even if the underlying engineering is not. If you are running Chrome, Edge, or another Chromium-derived browser on Windows, Linux, or macOS, you should assume that this CVE belongs in the same urgent patch queue as any other browser memory-corruption issue. Microsoft’s advisory record explicitly ties the vulnerability to affected Chromium versions prior to the fixed build, while the Chrome release notes are the canonical upstream signal that the fix has shipped.
Chromium is the shared browser engine that powers Google Chrome and a wide range of downstream products, including Microsoft Edge. That architecture is a strength because it concentrates security engineering and accelerates fixes, but it also means a single upstream flaw can affect a large slice of the desktop web. When a Chromium CVE is published, the first question for enterprises is rarely “Is Chrome vulnerable?” It is more often “Which downstream products have ingested the patch, and on which dates?” That is why Microsoft maintains a Security Update Guide presence for Chromium-origin bugs: it gives IT teams a downstream verification point rather than forcing them to infer safety from upstream release notes alone.
WebCodecs itself is part of the browser’s modern media stack. It lets websites work with encoded audio and video more directly, which can improve performance and unlock new web applications. The tradeoff is that media pipelines are hard to harden: objects are created, passed around, and freed quickly, often on different threads or under different state transitions. A use-after-free in that context usually means one component still believes an object is valid after another has already released it, creating a window for memory corruption. In a browser, that can become code execution, information disclosure, or a foothold for broader exploitation depending on the primitive achieved.
The timing also matters. Chrome 146 is already a busy release line, with multiple March 2026 security fixes across graphics, media, JavaScript, and Uncentration is typical of major browser branches: once a release train is underway, several unrelated memory-safety bugs often surface together. In the March 2026 Chrome Release notes, Google shipped multiple security fixes and later additional stable updates, which is exactly the sort of cadence that forces defenders to watch build numbers rather than rely on general “patched this month” assumptions.
For Microsoft customers, the important distinction is not whether Microsoft authored the bug. It is whether the fix has made it into the Edge branch that their devices actually run. Microsoft’s Security Update Guide exists precisely for that downstream question, and prior Chromium CVEs in Edge have followed the same logic: the advisory is a tracker, a verification point, and a signal that a specific browser build has absorbed the upstream repair. That is why the appearance of CVE-2026-5280 in Microsoft’s guide is operationally useful even when the root cause lives entirely in Google’s codebase.
The version boundary is especially useful. Version-based remediation is how most enterprise browser security gets managed in the real world, because it is a measurable state that can be checked through software inventory, endpoint management, or browser telemetry. If a device is below **1hould be treated as exposed until proven otherwise. That makes the guidance more actionable than a generic “update your browser” notice, because it gives teams a concrete compliance target.
Google’s own Chrome release notes remain the upstream source of truth for the fix. Microsoft’s guide points back to the Chrome releases page and the Chromium issue tracker, which is consistent with the normal workflow for Chromium vulnerabilities: disclosure, fix, downstream ingestion, and then enterprise visjust paperwork; it is the mechanism that lets defenders confirm whether their products are still on the vulnerable side of the branch boundary.
The file search results show the same general pattern across multiple Chromium CVEs: Microsoft records upstream issues to help Edge users confirm ingestion of the fix, and the downstream advisory often mirrors the core description, severity, and version floor from the Chrome side. That pattern has become a practical convention for enterprise patching. It reduces ambiguity, particularly in large fleets where Chrome and Edge may coexist and where version drift can create a false sense of security.
For the Windows ecosystem, this matters even more because browser choice is often not a pure user preference. Endpoint managers may need to standardize a particular Chromium build, apply compliance baselines, and verify that update channels have converged. A vulnerability like CVE-2026-5280 becomes a fleet-management problem as much as a browser bug. That is the real enterprise cost of modern browser security: every upstream fix is also a downstream coordination exercise.
The long-term security story here is not unique to Chromium. Across browsers, media, graphics, and JavaScript subsystems tend to attract the majority of serious memory-corruption bugs because they combine performance pressure with enormous input diversity. Google’s release cadence in March 2026 underscores that reality: Chrome’s stable branch has already seen security fixes in WebCodecs, WebAudio, Skia, and other areas in a relatively short span. That breadth tells you where the real attack surface lives.
There is also a subtle strategic point here. Attackers value WebCodecs because ned to make the browser more capable, which often means making it more trusting of user-supplied content. Trusted flexibility is what modern web platforms are built on, but every new capability widens the path count into native code. If the lifetime rules are imperfect, the bug can be the capability itself.
There is also a channel-management issue. Organizations often pin browsers to approved branches, control automatic updates, or stage changes through rings that intentionally delay deployment. Those controls are sensible, but they can also a high-severity browser CVE is released. If a patch is available but not deployed, the organization is effectively choosing exposure in exchange for change management stability. That may be acceptable in some contexts, but it should be a conscious decision, not an accident.
The Microsoft guidance makes this especially relevant to hybrid estates where Chrome and Edge coexist. Security teams need to inventory both browsers, because a device running an up-to-date Edge build but an outdated Chrome installation is still exposed. Likewise, an update to one browser does not imply the other has inherited the fix. That simple fact is easy to overlook and costly to ignore.
The threat model for consumers is straightforward. A malicious link, a compromised ad slot, a phishing page, or a booby-trapped website can all deliver a crafted HTML payload. You do not need to be an obvious high-value target to benefit from prompt patching; wide web reach means ordinary users can be caught in the blast radius of an opportunistic campaign. Thates should be treated with the same seriousness as operating system security updates.
Consumers also benefit from paying attention to the browser they actually use, not the one they assume they use. Edge, Chrome, and other Chromium-based browsers are not interchangeable from a patching perspective, even if they share the same engine lineage. A patch in one product family does not automatically repair every installed browser binary on the machine.
People often hear “sandbox” and assume the problem is contained. In reality, the sandbox is a layer of defense, not a magic shield. A sandboxed exploit can still exfiltrate sensitive data, access authenticated sessions, or position the attacker for additional exploitation. That is why a high-severity browser memory bug deserves immediate attention even when the vendor says the code executes inside a sandbox.
That dynamic also explains why patch transparency matters as a competitive differentiator. Browsers are no longer judged only on speed or standards support; they are judged on how quickly they absorb upstream security fixes and how clearly they communicate exposure. Microsoft’s visible downstream mapping gives it a credibility advantage with enterprise administrators who need to know not just that a bug exists, but whether their specific browser channel has cer market implication is that browser vendors increasingly compete on operational trust. If a vendor can show that its update guidance is clear, its version numbers are easy to verify, and its patch cadence is reliable, it wins points with IT departments even if the underlying vulnerability was introduced upstream. That is why downstream security documentation has become a strategic asset, not just a support artifact.
A second opportunity is process improvement. Each browser CVE is a chance to reduce lag between upstream release and endpoint deployment. Organizations that automate browser inventory, enforce restart compliance, and validate version thresholds can turn a security incident into a measurable operational win. In security terms, patching is one of the few controls that gets better with practice.
A second concern is patch drift. Browser updates are fast, but not ev the same pace, especially in environments with offline endpoints, enterprise proxies, or deferred restarts. The gap between “patched upstream” and “patched everywhere” is where most real-world risk lives. That gap is easy to underestimate and expensive to ignore.
There is also the risk of normalizing browser CVEs as routine background noise. That would be a mistake. Repeated memory-corruption bugs in high-value subsystems suggest that browser attack surfaces are still too large and too complex for comfort. If anything, the steady stream of Chromium fixes should be a reminder that modern browser security remains a live engineering problem, not a solved one.
Security teams should also watch for any follow-on disclosures involving WebCodecs or adjacent media components. When one media bug appears, it often leads researchers to review similar lifetime handling in related code paths. That does not mean another issue is guaranteed, but it does mean the subsystem deserves more scrutiny than usual.
Finally, this CVE will likely be remembered less for its name than for what it says about browser operations in 2026: the fastest patch is only useful if it reaches every endpoint. The organizations that win here will be the ones that treat browser security as a continuous inventory-and-enforcement problem, not a one-time software update event. That is where modern risk management really lives.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center
This is not an isol early April 2026 have already shown how quickly Chromium bugs can cascade across the ecosystem, from Chrome to Edge to enterprise patch-management tools. The broader pattern is important: Google fixes the upstream browser, Microsoft mirrors the status for Edge customers, and security teams have to map both the browser version and the device’s rollout state before they can say a fleet is safe. That pattern is visible in Microsoft’s own guidance and in the way Chromium issues are tracked as they move from vendor disclosure to downstream visibility.
The practical lesson for administrators is straightforward, even if the underlying engineering is not. If you are running Chrome, Edge, or another Chromium-derived browser on Windows, Linux, or macOS, you should assume that this CVE belongs in the same urgent patch queue as any other browser memory-corruption issue. Microsoft’s advisory record explicitly ties the vulnerability to affected Chromium versions prior to the fixed build, while the Chrome release notes are the canonical upstream signal that the fix has shipped.
 Background
Background
Chromium is the shared browser engine that powers Google Chrome and a wide range of downstream products, including Microsoft Edge. That architecture is a strength because it concentrates security engineering and accelerates fixes, but it also means a single upstream flaw can affect a large slice of the desktop web. When a Chromium CVE is published, the first question for enterprises is rarely “Is Chrome vulnerable?” It is more often “Which downstream products have ingested the patch, and on which dates?” That is why Microsoft maintains a Security Update Guide presence for Chromium-origin bugs: it gives IT teams a downstream verification point rather than forcing them to infer safety from upstream release notes alone.WebCodecs itself is part of the browser’s modern media stack. It lets websites work with encoded audio and video more directly, which can improve performance and unlock new web applications. The tradeoff is that media pipelines are hard to harden: objects are created, passed around, and freed quickly, often on different threads or under different state transitions. A use-after-free in that context usually means one component still believes an object is valid after another has already released it, creating a window for memory corruption. In a browser, that can become code execution, information disclosure, or a foothold for broader exploitation depending on the primitive achieved.
The timing also matters. Chrome 146 is already a busy release line, with multiple March 2026 security fixes across graphics, media, JavaScript, and Uncentration is typical of major browser branches: once a release train is underway, several unrelated memory-safety bugs often surface together. In the March 2026 Chrome Release notes, Google shipped multiple security fixes and later additional stable updates, which is exactly the sort of cadence that forces defenders to watch build numbers rather than rely on general “patched this month” assumptions.
For Microsoft customers, the important distinction is not whether Microsoft authored the bug. It is whether the fix has made it into the Edge branch that their devices actually run. Microsoft’s Security Update Guide exists precisely for that downstream question, and prior Chromium CVEs in Edge have followed the same logic: the advisory is a tracker, a verification point, and a signal that a specific browser build has absorbed the upstream repair. That is why the appearance of CVE-2026-5280 in Microsoft’s guide is operationally useful even when the root cause lives entirely in Google’s codebase.
Why use-after-free bugs still matter
Use-after-free issues remain one of the most dangerous classes of browser memory bugs because they can be surprisingly flexible in exploitation. An attacker who can reclaim freed memory with controlled data may steer program behavior in ways that are hard to predict from the source code alone. In a browser context, that flexibility is valuable because the attacker already controls a malicious page and can often re-trigger the vulnerable path repeatedly.Why WebCodecs is a high-value target
WebCodecs is attractive to attackers because it handles complex, structured input and is reachable from ordinary web content. Anything that processes rich media formats at browser scale becomes part of thebluntly, the more formats and timing states a subsystem must juggle, the more opportunities there are for lifetime mistakes. That makes media pipelines a persistent hunting ground for both researchers and exploit developers.What the advisory actually says
The core advisory language is concise but important. Microsoft’s record describes “Use after free in WebCodecs in Google Chrome prior to 146.0.7680.178” and notes that a remote attacker could execute arbitrary code inside ad HTML page. The security classification is High, and the weakness maps to CWE-416, the standard label for use-after-free memory errors.The version boundary is especially useful. Version-based remediation is how most enterprise browser security gets managed in the real world, because it is a measurable state that can be checked through software inventory, endpoint management, or browser telemetry. If a device is below **1hould be treated as exposed until proven otherwise. That makes the guidance more actionable than a generic “update your browser” notice, because it gives teams a concrete compliance target.
Google’s own Chrome release notes remain the upstream source of truth for the fix. Microsoft’s guide points back to the Chrome releases page and the Chromium issue tracker, which is consistent with the normal workflow for Chromium vulnerabilities: disclosure, fix, downstream ingestion, and then enterprise visjust paperwork; it is the mechanism that lets defenders confirm whether their products are still on the vulnerable side of the branch boundary.
Sandbox execution does not mean low risk
The phrase “inside a sandbox” can lull non-specialists into underestimating the issue. Browser sandboxes are meaningful defenses, but they are not a guarantee that exploitation is harmless. Sandboxed code execution can still lead to data theft, session hijacking, privilege escalation chains, or sandbox escape attempts if a second flaw exists. In other words, sandboxing reduces blast radius; it does not eliminate it.Crafted HTML is enough to make this a web-scale problem
The attack vector matters because it is web-native. An attacker does not need a USB drop, a plugin, or local access if a malicious page can reliably reach the vulnerable path. That means email links, drive-by downloads, embedded content, and compromised ad inventory can all become delivery vehicles. Onemotely reachable from standard HTML, the risk profile expands quickly.Why Microsoft’s guidance matters
Microsoft’s Security Update Guide is not duplicative noise; it is one of the most useful downstream signals for organizations that run Chromium-based browsers in Windows-heavy environments. The guide provides a bridge between upstream Chromium release notes and Microsoft’s own browser deployment model. For administrators, that distinction isanswers the question, “Has my managed browser build actually received the fix?” rather than merely “Has Google shipped a patch somewhere?”The file search results show the same general pattern across multiple Chromium CVEs: Microsoft records upstream issues to help Edge users confirm ingestion of the fix, and the downstream advisory often mirrors the core description, severity, and version floor from the Chrome side. That pattern has become a practical convention for enterprise patching. It reduces ambiguity, particularly in large fleets where Chrome and Edge may coexist and where version drift can create a false sense of security.
For the Windows ecosystem, this matters even more because browser choice is often not a pure user preference. Endpoint managers may need to standardize a particular Chromium build, apply compliance baselines, and verify that update channels have converged. A vulnerability like CVE-2026-5280 becomes a fleet-management problem as much as a browser bug. That is the real enterprise cost of modern browser security: every upstream fix is also a downstream coordination exercise.
Edge inherits Chromium risk by design
Edge’s Chromium base gives Microsoft users compatibility and fast access to web standards, but it also means Edge users ride the same security wave as Chrome. When an upstream Chromium bug is fixed, Edge is only safe once the corresponding Edge build includes that code. That creates a brief but important window where patch awareness, not just patch availability, determines exposure.Update guides are more than compliance paperwork
Security update guides are often dismissed as administrative clutter. In practice, they are the record that tells SOC teams and endpoint admins whether a browser CVE is still relevant to their estate. Without that downstream mapping, defenders would have to correlate every browser release manually, which is slow and error-prone. For a high-severity browser bug, minutes matter and manual guesswork is a poor substitute for a maintained advisory.WebCodecs as an attack surface
WebCodecs sits in a particularly sensitive part of the browser architecture because it processes data that is both complex and attacker-controllable. Unlike a simple text parser, media code must manage buffer lifetimes, codec state, format transitions, and asynchronous operations. That complexity increases the odds that a freed object might still be referenced later in the pipeline, which is the essence of a use-after-free.The long-term security story here is not unique to Chromium. Across browsers, media, graphics, and JavaScript subsystems tend to attract the majority of serious memory-corruption bugs because they combine performance pressure with enormous input diversity. Google’s release cadence in March 2026 underscores that reality: Chrome’s stable branch has already seen security fixes in WebCodecs, WebAudio, Skia, and other areas in a relatively short span. That breadth tells you where the real attack surface lives.
There is also a subtle strategic point here. Attackers value WebCodecs because ned to make the browser more capable, which often means making it more trusting of user-supplied content. Trusted flexibility is what modern web platforms are built on, but every new capability widens the path count into native code. If the lifetime rules are imperfect, the bug can be the capability itself.
Why memory safety is still the core issue
The persistent problem is not just “browser code is complicated.” It is that large portions of the browser stack remain written in memory-unsafe languages or use unsafe patterns in performance-critical code. A use-after-free means the code has lost track of ownership at the exact moment an attacker wants that confusion to exist. That is why even routine-seeming browser features can generate high-severity advisories.Why the browser sandbox is only part of the defense
The sandbox is still important, and browser vendors have made major progress hardening it. But once an attacker has code execution related sandboxed process, the next step is often chaining bugs, not stopping there. That is why Google and Microsoft both treat a sandboxed RCE primitive as serious even if the initial impact looks contained.Enterprise impact
For enterprises, the key question is not whether CVE-2026-5280 is real. It is how quickly the fleet can be brought above the fixed version and how confidently that state can be verified. On Windows, that means checking whether Chrnts have moved to a build at or beyond the patched release, and whether any managed systems are lagging because of update rings, deferred restarts, or software distribution issues.There is also a channel-management issue. Organizations often pin browsers to approved branches, control automatic updates, or stage changes through rings that intentionally delay deployment. Those controls are sensible, but they can also a high-severity browser CVE is released. If a patch is available but not deployed, the organization is effectively choosing exposure in exchange for change management stability. That may be acceptable in some contexts, but it should be a conscious decision, not an accident.
The Microsoft guidance makes this especially relevant to hybrid estates where Chrome and Edge coexist. Security teams need to inventory both browsers, because a device running an up-to-date Edge build but an outdated Chrome installation is still exposed. Likewise, an update to one browser does not imply the other has inherited the fix. That simple fact is easy to overlook and costly to ignore.
What enterprises should check first
- Confirm whether Chrome is at 146.0.7680.178 or later on all endpoints.
- Verify the corresponding Edge version on managed Windows devices.
- Check whether browser updates are blocked by policy, maintenance windows, or stale update services.
- Review whether exposed systems routinely open untrusted HTML content or browse high-risk sites.
- Ensure security monitoring is tuned for suspicious browser crashes, renderer restarts, or exploit indicators.
Why patch urgency is different for browsers
Browsers are not ordinary desktop apps. They are the primary interface to email, documents, authentication portals, SaaS tools, and internal line-of-business systems. That means a browser CVE can become the first step in a compromise even if it is not the final step. In enterprise risk terms, the browser is both a productivity tool and a universal attack surface.Consumer impact
For consumers, the message is less about architecture and more about hygiene: update the browser immediately and make sure the auto-update mechanism has actually completed. Many users assume Chrome or Edge updates themselves seamlessly, but browser processes are sometimes delayed by open tabs, suspended sessions, or a machine that has not been restarted in days. If you are below the fixed version, you are effectively carrying the bug until the update lands.The threat model for consumers is straightforward. A malicious link, a compromised ad slot, a phishing page, or a booby-trapped website can all deliver a crafted HTML payload. You do not need to be an obvious high-value target to benefit from prompt patching; wide web reach means ordinary users can be caught in the blast radius of an opportunistic campaign. Thates should be treated with the same seriousness as operating system security updates.
Consumers also benefit from paying attention to the browser they actually use, not the one they assume they use. Edge, Chrome, and other Chromium-based browsers are not interchangeable from a patching perspective, even if they share the same engine lineage. A patch in one product family does not automatically repair every installed browser binary on the machine.
Practical consumer habits thaKeep automatic browser updates enabled.
- Restart the browser regularly so downloaded patches can fully activate.
- Avoid opening unfamiliar HTML files or links from untrusted senders.
- Treat browser update prompts as urgent, not optional.
- Use password managers and MFA so a browser exploit alone is less useful to an attacker.
People often hear “sandbox” and assume the problem is contained. In reality, the sandbox is a layer of defense, not a magic shield. A sandboxed exploit can still exfiltrate sensitive data, access authenticated sessions, or position the attacker for additional exploitation. That is why a high-severity browser memory bug deserves immediate attention even when the vendor says the code executes inside a sandbox.
Competitive and market implications
Every Chromium vulnerability has a ripple effect beyond Google. Microsoft Edge, enterprise Chromium forks, and embedded browsers in software products all depend on the same code lineage. That means a single upstream bug can trigger a scramble across multiple vendors to ingest the fix, validate their builds, and communicate status to users. In practical terms, Chromium’s security posture sets the baseline for a large chunk of market.That dynamic also explains why patch transparency matters as a competitive differentiator. Browsers are no longer judged only on speed or standards support; they are judged on how quickly they absorb upstream security fixes and how clearly they communicate exposure. Microsoft’s visible downstream mapping gives it a credibility advantage with enterprise administrators who need to know not just that a bug exists, but whether their specific browser channel has cer market implication is that browser vendors increasingly compete on operational trust. If a vendor can show that its update guidance is clear, its version numbers are easy to verify, and its patch cadence is reliable, it wins points with IT departments even if the underlying vulnerability was introduced upstream. That is why downstream security documentation has become a strategic asset, not just a support artifact.
Chrome’s release train still sets the pace
Google’s March 2026 Chrome updates show that the Chrome team can ship fixes quickly and repeatedly, which remains a core strength of the Chromium model. The downside is that the pace can create a perception gap: users may believe “Chrome updated recently” means “everything is safe,” when in fact specific fixes can land in later point releases. CVE-2026-5280 reinforces the need to check the exact build, not the broad release family.Why downstream browsers must move in lockstep
Edge, Brave, Opera, and other Chromium-based browsers all inherit parts of the same security story. If one of them lags behind upstream Chrome, it can briefly become the softest target in a broadly shared ecosystem. That is the strategic cost of a common engine: everyone benefits from shared fixes, but everyone also shares the same patch race.Strengths and Opportunities
The immediate strength of the response to CVE-2026-5280 is that the ecosystem already knows how to handle this class of issue. Google has a mature release process, Microsoft maintains downstream visibility, and version numbers provide a clear compliance target. That combination makes remediation achievable, even if it still demands discipline. It also gives defenders a chance to tighten update workflows that should already be mature by 2026.A second opportunity is process improvement. Each browser CVE is a chance to reduce lag between upstream release and endpoint deployment. Organizations that automate browser inventory, enforce restart compliance, and validate version thresholds can turn a security incident into a measurable operational win. In security terms, patching is one of the few controls that gets better with practice.
- Strong upstream/downstream disclosure chain
- Clear fixed-version boundary for remediation
- Mature enterprise patch tooling on Windows
- High user reach makes updates broadly effective
- Good opportunity to tighten compliance baselines
- Use-after-free class is well understood by defenders
- Sandboxing still contains some exploitation attempts
Why this is a good test case for patch discipline
CVE-2026-5280 is the kind of issue that exposes whether an organization has a real update process or just a policy on paper. If inventory is accurate, deployment rings are healthy, and restarts happen on schedule, the exposure window can be short. If not, even a well-documented fix can linger uninstalled long enough to matter.Risks and Concerns
The biggest concern is the obvious one: a remote attacker can potentially reach the flaw with a crafted HTML page. That means the vulnerability is exploitable at Internet scale, not just by local actors or privileged insiders. Once a browser flaw becomes web-reachable, defenders must assume opportunistic scanning, phishing, and malicious advertising will all be in play.A second concern is patch drift. Browser updates are fast, but not ev the same pace, especially in environments with offline endpoints, enterprise proxies, or deferred restarts. The gap between “patched upstream” and “patched everywhere” is where most real-world risk lives. That gap is easy to underestimate and expensive to ignore.
There is also the risk of normalizing browser CVEs as routine background noise. That would be a mistake. Repeated memory-corruption bugs in high-value subsystems suggest that browser attack surfaces are still too large and too complex for comfort. If anything, the steady stream of Chromium fixes should be a reminder that modern browser security remains a live engineering problem, not a solved one.
- Exposure can be triggered by ordinary web content
- Sandboxed execution still enables meaningful compromise
- Delayed updates leave fleets vulnerable longer than expected
- Multiple Chromium-based browsers may be unevenly patched
- Users may assume “recent update” means “fully protected”
- Browser crashes can be missed as exploit telemetry
- Media subsystems remain a fertile area for memory bugs
The hidden risk of false confidence
When a vendor says an exploit runs in a sandbox, people soh. That is dangerous because many attackers do not need full system compromise on the first try; they only need a foothold. Once that foothold exists, the rest of the chain becomes an exercise in privilege escalation, token theft, or lateral movement. A sandboxed bug is still a bug worth urgent attention.Looking Ahead
The next thing to watch is how quickly downstream Chromium browsers close the gap on the fixed Chrome build. For Microsoft Edge users, the practical question is whether managed channels have already absorbed the patch or whether some environments are still lagging on pre-fix versions. The answer will determine whether this remains a short-lived advisory or turns into a longer enterprise cleanup cycle.Security teams should also watch for any follow-on disclosures involving WebCodecs or adjacent media components. When one media bug appears, it often leads researchers to review similar lifetime handling in related code paths. That does not mean another issue is guaranteed, but it does mean the subsystem deserves more scrutiny than usual.
Finally, this CVE will likely be remembered less for its name than for what it says about browser operations in 2026: the fastest patch is only useful if it reaches every endpoint. The organizations that win here will be the ones that treat browser security as a continuous inventory-and-enforcement problem, not a one-time software update event. That is where modern risk management really lives.
- Verify browser versions against the fixed build
- Confirm Edge and Chrome are both updated where present
- Check restart compliance across managed devices
- Review telemetry for bralous renderer behavior
- Keep an eye on related WebCodecs and media-stack advisories
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center
Last edited: