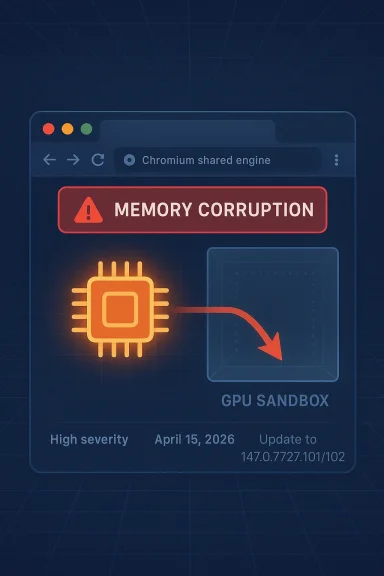
The latest Chrome security cycle has landed with a high-severity GPU memory corruption bug that matters well beyond the browser tab where it originated. Google’s April 15, 2026 Stable Channel update for desktop includes CVE-2026-6314, described as an out-of-bounds write in GPU, and the fixed version is 147.0.7727.101/102 depending on platform. Microsoft’s Security Update Guide is tracking the same Chromium issue for Edge users, which is a reminder that browser-engine vulnerabilities rarely stay confined to one product for long. gleblog.com](Stable Channel Update for Desktop))
Browser security news tends to get flattened into “update now” shorthand, but CVE-2026-6314 deserves a more careful reading. The flaw sits in the GPU process, one of the most sensitive and performance-critical parts of a modern browser, and Google says a remote attacker who already compromised that process could potentially use the bug to escape the sandbox via a crafted HTML page. That is a serious escalation path because the browser sandbox st meaningful barrier between web content and the host system. (chromereleases.googleblog.com)
The timing also matters. Google shipped the fix as part of a broad April 15 desktop update that addressed 31 security issues, many of them in components that repeatedly show up in browser exploit chains: ANGLE, Skia, WebRTC, V8, and PDFium among them. That pattern is familiar for a reason. Attackers usually do not rely on a single bug class; they look for whichever renderer, graphics, codec, or utility path gives them a foothold, then chain another flaw to cross the trust boundary. (chromereleases.googleblog.com)
Microsoft’s entry for the same CVE is important not because it changes the technical details, but because it confirms the downstream impact on **Microsoft Edgers cadence. For enterprise teams, that means patch tracking is not just a Chrome exercise. It is a browser-platform exercise, one that reaches browsers, embedded web views, and any product that consumes Chromium security updates.
This is also a useful case study in how Google stages disclosure. Chrome’s release notes explicitly say that some bug details may remain restricted until most users are updated, especially when the issue involves a third-party library or a vulnerability that could still be abused before adoption is broad. That policy is a balancing act: enough information for defenders to act, but not so much that exploit developers get a free roadmap. (chromereleases.googleblog.com)
The GPU process deserves special attention because browsers isolate it precisely to reduce the blast radius of graphics and rendering bugs. That process still has privileged responsibilities, though, and it operates in a space where complex input, hardware variability, and performance constraints collide. Those conditions make GPU code a perennial favorite for exploit chains because the code must be fast, interoperable, and tolerant of huge amounts of attacker-controlled data. (chromereleases.googleblog.com)
Google’s April 15 bulletin shows that the release was not a narrow patch but a broad hardening pass across the browser stack. The list includes severe issues in ANGLE, Skia, Proxy, Prerender, Video, CSS, Codecs, PDFium, and more. That breadth reinforces the idea that Chrome’s security model is only as strong as its least safe subsystem, especially where web content meets graphics and media pipelines. (chromereleases.googleblog.com)
That tension is why the GPU process receives intense scrutiny from both Google and external researchers. It is an obvious target for memory safety bugs, and memory safety bugs in this subsystem can be especially valuable because they often connect to rich data flowsm. A malformed page, a bad shader path, or an unexpected object lifetime can create the conditions for exploitation without ever looking suspicious to a normal user. (chromereleases.googleblog.com)
This matters because the browser’s job is not just to block outright code execution from a web page. It is to make chained exploitation expensive, unreliable, and noisy. CVE-2026-6314 chips away at that defense-in-depth model by giving an attacker a post-compromise escape route inside the GPU sandbox boundary.
In practice, that means defenders should treat the vulnerability as part of a multi-stage attack story, not as an isolated crash bug. The more complex the browser subsystem, the more likely a small memory corruption flaw is to become an exploit enabler.
That downstream model creates an awkward reality for enterprise patching. Security teams cannot simply watch Google’s release blog and call the problem solved. They must also confirm whether their browser channel, build ring, and managed update settings have pullger organizations, that can mean different timelines for consumer Chrome, corporate Chrome, and enterprise-managed Edge. (chromereleases.googleblog.com)
That means the vulnerability is strategically important even if the initial exploit conditions are constrained. Attackers love bugs that help them move from one protection layer to the next. Once they can cross that boundary, the rest of the system becomes much easier to attack. In other words, a flaw like this may not be the whole compromise, but it can be the step that makes the compromise feasible.
One useful way to think about it is:
The browser ecosystem has been conditioned by years of vulnerability releases, so it is easy to become numb to the language. But memory corruption in a sandboxed process is exactly where real-world exploit work begins. Even when the vulnerability is not directly remote code execution in the public-facing sense, it may be the key that unlocks everything else.
The label should also be read in context with Google’s own release notes and Microsoft’s downstream tracking. When both vendors surface the same issue in a security update cycle, it is rarely because the defect is cosmetic. It is because the bug affects a layer that matters for both stability and trust. (chromereleases.googleblog.com)
There is also a behavioral issue. Many organizations assume browser updates are low frictio automatically. In reality, browsers can remain behind for surprisingly mundane reasons: long-lived sessions, deferred reboot behavior, update rings, offline laptops, virtual desktops, or local policy restrictions. Those operational delays are exactly the kind of thing exploit developers hope to find.
The second thing to watch is downstream timing. Chrome’s April 15 release is not the end of the story; it is the beginning of the propagation phase. If Edge, managed Chrome channels, or embedded Chromium consumers lag significantly, the practical exposure window will stay open longer than the upstream patch date implies. (chromereleases.googleblog.com)
Finally, watch for whether this flaw turns out to be part of a broader GPU or graphics hardening wave. Chromium has spent years improving its security posture with sanitizers, fuzzing, and process isolation, and Google’s release notes repeatedly show that graphics and media subsystems remain productive hunting grounds for researchers. If CVE-2026-6314 is any indication, that pressure is not easing. (chromereleases.googleblog.com)
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center
 Overview
Overview
Browser security news tends to get flattened into “update now” shorthand, but CVE-2026-6314 deserves a more careful reading. The flaw sits in the GPU process, one of the most sensitive and performance-critical parts of a modern browser, and Google says a remote attacker who already compromised that process could potentially use the bug to escape the sandbox via a crafted HTML page. That is a serious escalation path because the browser sandbox st meaningful barrier between web content and the host system. (chromereleases.googleblog.com)The timing also matters. Google shipped the fix as part of a broad April 15 desktop update that addressed 31 security issues, many of them in components that repeatedly show up in browser exploit chains: ANGLE, Skia, WebRTC, V8, and PDFium among them. That pattern is familiar for a reason. Attackers usually do not rely on a single bug class; they look for whichever renderer, graphics, codec, or utility path gives them a foothold, then chain another flaw to cross the trust boundary. (chromereleases.googleblog.com)
Microsoft’s entry for the same CVE is important not because it changes the technical details, but because it confirms the downstream impact on **Microsoft Edgers cadence. For enterprise teams, that means patch tracking is not just a Chrome exercise. It is a browser-platform exercise, one that reaches browsers, embedded web views, and any product that consumes Chromium security updates.
This is also a useful case study in how Google stages disclosure. Chrome’s release notes explicitly say that some bug details may remain restricted until most users are updated, especially when the issue involves a third-party library or a vulnerability that could still be abused before adoption is broad. That policy is a balancing act: enough information for defenders to act, but not so much that exploit developers get a free roadmap. (chromereleases.googleblog.com)
What CVE-2026-6314 Means
At a technical level, an out-of-bounds write means code is writing outside the buffer it was supposed to use. In a browser GPU path, that isk; it can become a building block for memory corruption, code execution, or sandbox escape depending on the surrounding hardening and exploit quality. Google’s wording is cautious — “potentially perform a sandbox escape” — but in vulnerability terms, potentially is already enough to justify urgent remediation.The GPU process deserves special attention because browsers isolate it precisely to reduce the blast radius of graphics and rendering bugs. That process still has privileged responsibilities, though, and it operates in a space where complex input, hardware variability, and performance constraints collide. Those conditions make GPU code a perennial favorite for exploit chains because the code must be fast, interoperable, and tolerant of huge amounts of attacker-controlled data. (chromereleases.googleblog.com)
Why GPU Bugs Matter So Much
GPU-related vulnerabilities are dangerous because they sit near the junction of complex parsing and high-value privileges. The browser is constantly translating web content into graphics commands, shader operations, compositing work, and device interactions, all while trying to remain responsive. If one of those pathways writes out of bounds, the attacker may get more than a crash; they may get a primitive that lets them manipulate memory in ways the sandbox was supposed to prevent.- Attack surface is large because modern pages use acceleration routinely.
- Input is attacker-influenced because HTML and rendering data come from the web.
- Exploit value is high because GPU bugs often pair well with renderer or JIT flaws.
- Detection is difficult because crashes may look like ordinary graphics instability.
- Sandbox relevance is direct because the flaw is already inside a sandboxed process.
How the Fix Fits Into Chrome 147
CVE-2026-6314 shipped in Chrome 147.0.7727.101/102, which Google says is rolling out across Windows, macOS, and Linux over the coming days and weeks. That staggered rollout is standard for Stable Channel releases, but it creates a practical problem for defenders: the existence of a fixed build does not mean every user is protected immediately. Enterprises that rely on automatic updates still need to verify deployment state rather than assume it. (chromereleases.googleblog.com)Google’s April 15 bulletin shows that the release was not a narrow patch but a broad hardening pass across the browser stack. The list includes severe issues in ANGLE, Skia, Proxy, Prerender, Video, CSS, Codecs, PDFium, and more. That breadth reinforces the idea that Chrome’s security model is only as strong as its least safe subsystem, especially where web content meets graphics and media pipelines. (chromereleases.googleblog.com)
Release Cadence and Patch Discipline
The important operational lesson is that Chromium security is now a continuous synchronization problem. One vendor publishes the fix, another ingests it, and organizations must confirm that the downstream browser or embedded runtime has actually adopted the patched code. The lag between upstream disclosure and downstream deployment is exactly where attackers try to operate.- Google fixed the issue in the April 15 Stable Channel update. (chromereleases.googleblog.com)
- The patch is in Chrome 147.0.7727.101/102. (chromereleases.googleblog.com)
- Microsoft tracks the issue for Edge as a Chromium-derived vulnerability.
- The rollout is gradual, not instantaneous. (chromereleases.googleblog.com)
Chromium’s GPU Attack Surface
Chromium’s GPU path is one of those areas where engineering elegance and security practicality are always in tension. The browser wants accelerated graphics, smooth video, and low-latency rendering. Security wants compartmentalization, strict validation, and minimal privilege. Every time performance pressure wins a small argument, the attack surface grows a little more.That tension is why the GPU process receives intense scrutiny from both Google and external researchers. It is an obvious target for memory safety bugs, and memory safety bugs in this subsystem can be especially valuable because they often connect to rich data flowsm. A malformed page, a bad shader path, or an unexpected object lifetime can create the conditions for exploitation without ever looking suspicious to a normal user. (chromereleases.googleblog.com)
Why a Crafted HTML Page Is Enough
The phrasing in Google’s description is telling: a crafted HTML page after the attacker had already compromised the GPU process. That is a classic browser exploit-chain scenario. The first bug gets a foothold; the second bug turns that foothold into a sandbox escape or a wider compromise.This matters because the browser’s job is not just to block outright code execution from a web page. It is to make chained exploitation expensive, unreliable, and noisy. CVE-2026-6314 chips away at that defense-in-depth model by giving an attacker a post-compromise escape route inside the GPU sandbox boundary.
In practice, that means defenders should treat the vulnerability as part of a multi-stage attack story, not as an isolated crash bug. The more complex the browser subsystem, the more likely a small memory corruption flaw is to become an exploit enabler.
Edge, Enterprise Browsers, and Downstream Risk
Microsoft’s Security Update Guide exists for a reason: Edge is Chromium-based, so many Chrome vulnerabilities automatically become Edge security issues once the upstream fix is known and integrated. The CVE-2026-6314 entry on MSRC is therefore not a separate product bug, but it is a critical signal for Windows fleets that standardize on Edge.That downstream model creates an awkward reality for enterprise patching. Security teams cannot simply watch Google’s release blog and call the problem solved. They must also confirm whether their browser channel, build ring, and managed update settings have pullger organizations, that can mean different timelines for consumer Chrome, corporate Chrome, and enterprise-managed Edge. (chromereleases.googleblog.com)
What Enterprises Should Pay Attention To
The enterprise risk is not just “a browser bug exists.” It is “a browser bug exists in a component that many organizations allow employees to use t portals, and productivity tools.” Browsers are no longer passive windows onto the internet; they are runtime platforms that touch identity, file handling, conferencing, SaaS dashboards, and remote work portals.- Managed Chrome channels may lag behind Google’s public release.
- Edge deployment rings may lag behind Chromium upstream fixes.
- VDI and kiosk environments often have their own update friction.
- Web apps can amplify browser exploit impact by concentrating usage.
- Security tooling may underestimate browser update latency in fleets.
Why This Looks Like a Sandbox-Escape Class Bug
Sandbox escapes are not the same as initial code execution, and that distinction matters. A browser exploit chain often starts with a renderer or graphics bug, then uses a second flaw to break out of the process boundary. CVE-2026-6314 fits that model neatly because Google’s own description places the flaw inside the GPU process and frames the impact as a potential sandbox escape.That means the vulnerability is strategically important even if the initial exploit conditions are constrained. Attackers love bugs that help them move from one protection layer to the next. Once they can cross that boundary, the rest of the system becomes much easier to attack. In other words, a flaw like this may not be the whole compromise, but it can be the step that makes the compromise feasible.
Chaining Logic in Modern Browser Exploits
Modern browser exploitation is usually about sequencing, not single-bug theatrics. A first bug gains execution in a restricted context. A second bug breaks process isolation. A third step might then target privilege escalation, data theft, or persistence. This is why memory corruption in high-value sandboxes draws immediate attention from both attackers and defenders.One useful way to think about it is:
- The attacker delivers or loads a crafted page.
- A separate flaw compromises the GPU or related process.
- CVE-2026-6314 is used to cross the sandbox boundary.
- Additional post-exploitation steps expand control of the system.
What Makes This Different From a Typical Browser Crash
Not every browser memory bug deserves the same level of urgency. Some are nuisance crashity problems, and some are exploit-chain components. CVE-2026-6314 belongs firmly in the third category because Google assigned it High severity and tied it to GPU sandbox escape potential. That combination is much more serious than a generic rendering crash or a low-impact web compatibility issue. (chromereleases.googleblog.com)The browser ecosystem has been conditioned by years of vulnerability releases, so it is easy to become numb to the language. But memory corruption in a sandboxed process is exactly where real-world exploit work begins. Even when the vulnerability is not directly remote code execution in the public-facing sense, it may be the key that unlocks everything else.
Why Severity Labels Still Matter
Severity labels are imperfect, but they are still useful for prioritization when interpreted correctly. In this case, High means the issue sits in the upper tier of browser risk because it can contribute to meaningful compromise paths. It does not necessarily mean already underway, but it does mean the bug is technically serious enough that delaying updates is a bad bet.The label should also be read in context with Google’s own release notes and Microsoft’s downstream tracking. When both vendors surface the same issue in a security update cycle, it is rarely because the defect is cosmetic. It is because the bug affects a layer that matters for both stability and trust. (chromereleases.googleblog.com)
Patch Implications for Windows Users
For Windows users, the practical question is whether the browser installed on the machine has crossed the fixed version threshold. Chrome and Edge can both be updated on their own schedules, and enterprise policy can slow that cadence. That makon more important than announcement monitoring. (chromereleases.googleblog.com)There is also a behavioral issue. Many organizations assume browser updates are low frictio automatically. In reality, browsers can remain behind for surprisingly mundane reasons: long-lived sessions, deferred reboot behavior, update rings, offline laptops, virtual desktops, or local policy restrictions. Those operational delays are exactly the kind of thing exploit developers hope to find.
Practical Priorities
- Confirm installed browser versions against the fixed 147.0.7727.101/102 build. (chromereleases.googleblog.com)
- Check whether enterprise policies are delaying Chromium update ingestion.
- Review whether Edge is managed separately from Chrome in your environment.
- Pay attention to kiosk, VDI, and shared-device deployments.
- Watch for browser restarts that may be needed before the patch is active.
Strengths and Opportunities
The good news is that this is the kinvendor response was fast, specific, and operationally actionable. Google identified the flaw, pushed a fixed build, and exposed enough information for defenders to prioritize patching without handing exploit developers a full blueprint. Microsoft’s downstream tracking also makes it easier for Edge customers to see whether their environment is covered. (chromereleases.googleblog.com)- Fast upstream remediation reduces the open window.
- Clear fixed-version information makes verification easier. (chromereleases.googleblog.com)
- Downstream Edge tracking helps Windows administrators.
- Sandbox framing gives defenders a concrete risk model.
- Chromium’s layered security model still contains the impact if patched promptly.
- Release notes breadth suggests active hardening of multiple risky subsystems. (chromereleases.googleblog.com)
- Centralized browser management can reduce exposure when policies are aligned.
Risks and Concerns
The obvious concern is that GPU-process memory corruption can be chained into more serious exploitation if attackers already have a foothold in the browser. The less obvious concern is that browser patching often looks complete on paper before it is complete in practice. That gap between release and endpoint adoption is where risk lives. (clog.com)- Sandbox escape potential raises the stakes beyond a simple crash.
- Gradual rollout means not every system is fixed immediately. (chromereleases.googleblog.com)
- Enterprise policy delays can leave managed devices behind.
- Edge/Chrome split management can create blind spots.
- Attack chaining makes a narrow bug strategically valuable.
- User behavior may delay browser restarts and patch activation.
- Visibility gaps in VDI and kiosk fleets can hide vulnerable builds.
What to Watch Next
The next thing to watch is whether exploit researchers publish technical analysis of the GPU bug once disclosure restrictions loosen. Google’s note about withholding some details until a majority of users are updated suggests the company is aware that the issue could be attractive to attackers if left too exposed too soon. That is often the signal that a deeper technical write-up may arrive later, after the patch window has had time to close. (chromereleases.googleblog.com)The second thing to watch is downstream timing. Chrome’s April 15 release is not the end of the story; it is the beginning of the propagation phase. If Edge, managed Chrome channels, or embedded Chromium consumers lag significantly, the practical exposure window will stay open longer than the upstream patch date implies. (chromereleases.googleblog.com)
Finally, watch for whether this flaw turns out to be part of a broader GPU or graphics hardening wave. Chromium has spent years improving its security posture with sanitizers, fuzzing, and process isolation, and Google’s release notes repeatedly show that graphics and media subsystems remain productive hunting grounds for researchers. If CVE-2026-6314 is any indication, that pressure is not easing. (chromereleases.googleblog.com)
- Track whether Edge picks up the fix in your managed channel.
- Verify that endpoints are actually on 147.0.7727.101/102. (chromereleases.googleblog.com)
- Watch for exploit-analysis posts once bug-detail restrictions loosen. (chromereleases.googleblog.com)
- Review whether your browser management process includes restart enforcement.
- Monitor other GPU- and graphics-adjacent Chromium advisories for pattern clustering.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center