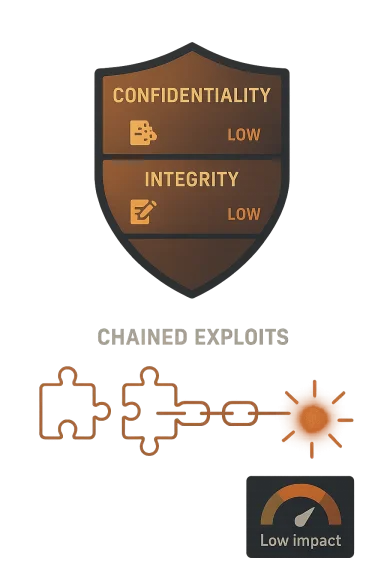
For a vulnerability like this, C:L / I:L / A:L means the expected impact is low in each of the three security areas: confidentiality, integrity, and availability. In CVSS terms, “Low” is used when a successful exploit would likely cause only a limited adverse effect, not a broad or catastrophic one.
In practical terms, that usually means an attacker could cause some harm — for example, expose a small amount of information, alter something in a limited way, or interrupt the app in a limited or temporary fashion — but not fully compromise the device or completely take it over. The CVSS “Low” designation is specifically meant to capture that kind of constrained impact.
Microsoft’s note is important: it says the vulnerability’s standalone exploitability is limited, and that an attacker would need to combine it with other vulnerabilities to mount a more serious attack. That means this CVE is not necessarily a complete attack path by itself; it is more likely to be one piece in a chained exploit scenario.
So, the bottom line is:
- Confidentiality low: limited information exposure is possible.
- Integrity low: limited tampering or spoofing effects are possible.
- Availability low: limited disruption or service degradation is possible.
- Not a full compromise on its own: additional flaws are likely needed for a meaningful real-world attack.
Source: MSRC Security Update Guide - Microsoft Security Response Center