A federal jury’s conviction and a subsequent 22‑month prison sentence for a Florida software reseller has thrown a spotlight on a long‑running and under‑reported weakness in the Windows and Office supply chain: genuine Microsoft Certificate of Authenticity (COA) labels, when separated from their original packaging or hardware, can be converted into usable product keys and sold on a global grey market — and that market has now produced a criminal prosecution with prison time and a fine.
Heidi Richards, 52, the operator of an e‑commerce business called Trinity Software Distribution, was convicted by a federal jury of conspiring to traffic in illicit Microsoft COA labels after a multi‑year investigation and trial. The conviction followed an investigation by Homeland Security Investigations and prosecution by the U.S. Attorney’s Office for the Middle District of Florida and the Department of Justice Computer Crime & Intellectual Property Section (CCIPS). Richards purchased thousands of genuine COA labels, removed or revealed the product activation codes written on them, and sold the codes in bulk to buyers who could redeem them — a practice that federal law and Microsoft’s distribution rules prohibit.
Officials say Richards wired millions of dollars to suppliers between 2018 and 2023 and personally profited from the resale of extracted keys. The prosecution characterized the labels as having “no independent commercial value” when separated from the software or hardware they were meant to authenticate — which is precisely why federal law targets trafficking in stand‑alone COAs.
This case progressed from indictment to conviction in late 2025, with sentencing carried out in early 2026: Richards was ordered to serve 22 months in federal prison and pay a $50,000 fine — a meaningful penalty that signals the Department of Justice’s position on large‑scale exploitation of software authentication mechanisms.
Most modern COAs implement a small clear label with a silver scratch‑off material that conceals the 25‑character product key so the key cannot be read without removing the scratch‑off. Microsoft expanded this concealment approach to products using the 25‑character keys in mid‑decade, and OEM activations have increasingly shifted toward digital or firmware‑embedded methods. The security features are designed to make standalone COAs unattractive and impractical for legitimate resale.
The Congress‑level record compiled when the Anti‑Counterfeiting Amendments Act was considered underscores the scale: past enforcement actions documented hundreds of thousands of missing or stolen COAs and the large black market value placed on otherwise worthless labels. The critical point is legal: COAs have no independent commercial value when sold apart from the licensed product, and trafficking them can qualify as federal criminal activity.
The Department of Justice’s public statement following the 2025 trial emphasized that Richards purchased genuine, standalone COA labels at prices far below retail and distributed keys harvested from them — conduct that the indictment described as illegal trafficking in COAs. The Homeland Security Investigations Kansas City Field Office led the investigation, with prosecutors from the Middle District of Florida and CCIPS taking the lead at trial.
Source: theregister.com Windows, Office software scalper jailed for 22 months
 Background / Overview
Background / Overview
Heidi Richards, 52, the operator of an e‑commerce business called Trinity Software Distribution, was convicted by a federal jury of conspiring to traffic in illicit Microsoft COA labels after a multi‑year investigation and trial. The conviction followed an investigation by Homeland Security Investigations and prosecution by the U.S. Attorney’s Office for the Middle District of Florida and the Department of Justice Computer Crime & Intellectual Property Section (CCIPS). Richards purchased thousands of genuine COA labels, removed or revealed the product activation codes written on them, and sold the codes in bulk to buyers who could redeem them — a practice that federal law and Microsoft’s distribution rules prohibit.Officials say Richards wired millions of dollars to suppliers between 2018 and 2023 and personally profited from the resale of extracted keys. The prosecution characterized the labels as having “no independent commercial value” when separated from the software or hardware they were meant to authenticate — which is precisely why federal law targets trafficking in stand‑alone COAs.
This case progressed from indictment to conviction in late 2025, with sentencing carried out in early 2026: Richards was ordered to serve 22 months in federal prison and pay a $50,000 fine — a meaningful penalty that signals the Department of Justice’s position on large‑scale exploitation of software authentication mechanisms.
What are COA labels and why they matter
COA labels: a physical authentication control
A Certificate of Authenticity (COA) is a tamper‑resistant label that accompanies physical Microsoft software packages or OEM installations and is intended to help customers and vendors determine whether the software was legitimately distributed. Historically COAs included holograms, color‑shifting inks, and other anti‑counterfeit features. Since the 2010s Microsoft has updated the COA design and added concealment panels to protect the printed product key from casual inspection or theft.Most modern COAs implement a small clear label with a silver scratch‑off material that conceals the 25‑character product key so the key cannot be read without removing the scratch‑off. Microsoft expanded this concealment approach to products using the 25‑character keys in mid‑decade, and OEM activations have increasingly shifted toward digital or firmware‑embedded methods. The security features are designed to make standalone COAs unattractive and impractical for legitimate resale.
Why COAs still have value to illicit markets
Despite the anti‑tamper measures, a persistent secondary market exists because a genuine COA with an intact underlying key can be used to activate full Microsoft products. Fraudsters and resellers who obtain legitimate COAs separately from the intended equipment or sealed retail package can harvest the underlying activation codes and sell them as low‑cost licenses, undercutting authorized channels and enabling widespread software activation without proper licensing. The anti‑counterfeit hardware cannot fully prevent exploitation when genuine COAs are diverted earlier in the supply chain.The Congress‑level record compiled when the Anti‑Counterfeiting Amendments Act was considered underscores the scale: past enforcement actions documented hundreds of thousands of missing or stolen COAs and the large black market value placed on otherwise worthless labels. The critical point is legal: COAs have no independent commercial value when sold apart from the licensed product, and trafficking them can qualify as federal criminal activity.
The Richards case: facts, charges, and evidence
Timeline and the prosecution’s theory
Prosecutors say Richards, operating as Trinity Software Distribution, purchased COA labels from a Texas‑based supplier between July 2018 and January 2023, wiring more than five million dollars to the supplier over that period. Employees were instructed to transcribe the codes from the COAs into spreadsheets; those extracted codes were then sold in bulk to buyers. That sequence — purchase, extraction, and resale — formed the core of the conspiracy charge.The Department of Justice’s public statement following the 2025 trial emphasized that Richards purchased genuine, standalone COA labels at prices far below retail and distributed keys harvested from them — conduct that the indictment described as illegal trafficking in COAs. The Homeland Security Investigations Kansas City Field Office led the investigation, with prosecutors from the Middle District of Florida and CCIPS taking the lead at trial.
Evidence cited at trial
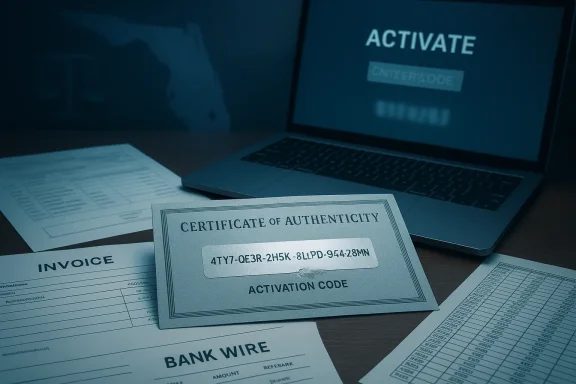
The government relied on transactional records, bank wiring evidence, purchase invoices, the spreadsheets containing transcribed keys, and witness testimony showing employees engaging in key extraction and data entry. Indictments in such cases typically focus on the pattern of commercial behavior (quantity of COAs, frequency of purchases, the pricing disparity with legitimate retail channels) and documentary trails that show the defendant profited from the operation. While not all granular trial exhibits are publicly released, the prosecution’s press release and industry reporting make clear the case rested on both physical evidence and financial flows.Why this case matters to IT teams, resellers, and buyers
Real‑world consequences
- End users who buy cheap keys from grey markets risk having the license revoked or rendered invalid if Microsoft detects the activation was derived from a misused COA.
- Businesses that inadvertently deploy such keys can face compliance gaps, potential audit liabilities, and remediation costs.
- OEMs and authorized channel partners can suffer brand and revenue damage when illegitimate keys circulate, complicating warranty and support relationships.
Supply‑chain and procurement vulnerabilities
The Richards prosecution highlights several recurring weaknesses:- Fragile custody controls at intermediate suppliers: loose inventory controls make genuine COAs removable and tradable outside intended flows.
- Disaggregated resale channels: third‑party liquidators, refurbishers, and small distributors create opacity that can be exploited.
- Demand for low‑cost licenses: buyers often prioritize price over provenance, fueling the market that makes exploitation financially attractive.
Legal framework and enforcement
The statutory angle
Trafficking in COAs intersects intellectual property and anti‑counterfeiting statutes as well as federal mail and wire fraud statutes when deceptive commercial conduct is involved. Congress and law enforcement agencies have treated the illicit trade in COAs seriously for decades, documenting large externalities and pursuing both counterfeit COAs and criminal diversion of genuine labels. The Anticounterfeiting Amendments and related enforcement resources give prosecutors tools to pursue multi‑million‑dollar schemes.Recent enforcement posture
The DOJ’s Computer Crime & Intellectual Property Section (CCIPS) has made the prosecution and conviction of large COA trafficking operations an explicit priority as part of broader efforts to curb cyber and intellectual property crime. The Richards case was prosecuted by CCIPS trial counsel in coordination with the U.S. Attorney’s Office in Florida and HSI investigators — a standard enforcement pattern for transnational and supply‑chain crimes. The 22‑month sentence and $50,000 fine demonstrate that, where the evidence shows large‑scale, profit‑driven trafficking, federal sentences will follow.Technical controls, Microsoft’s role, and why the problem persists
Microsoft’s anti‑counterfeit measures
Microsoft’s COA designs evolved over many years — from color‑shifting inks to holographic elements — and more recently to concealment panels designed to prevent casual reading of product keys. OEM activations have shifted toward firmware‑embedded or Microsoft account‑linked licensing in many cases, reducing the practical usefulness of loose COAs for newer devices. However, each packaging and distribution model leaves windows of opportunity early in the channel where labels can be separated and diverted.Why those protections don’t eliminate the market
- Where physical COAs still accompany product shipments, poor custody can let them be removed and aggregated for resale.
- Older product families and regions that still rely on physical COAs remain a target-rich environment.
- Criminal syndicates or opportunistic actors can outpace technical protections with logistics: it’s cheaper to buy diverted genuine COAs than to counterfeit quality labels convincingly.
Practical guidance: buying, vetting, and remediating
For IT buyers and administrators
- Always prefer authorized channels. Buy licenses directly from Microsoft, OEMs, or certified resellers. If a reseller offers volume discounts that look too good to be true, demand documentation tying keys to hardware shipments or sealed retail SKUs.
- Require provenance documentation. For bulk purchases, require supplier affidavits, purchase orders that match physical shipments, and the right to audit supply‑chain records.
- Use central activation and telemetry. Manage licensing from centralized consoles tied to Microsoft accounts or enterprise agreements so that anomalous activations are detected quickly and can be traced.
- Have a remediation plan. Budget for the cost of replacing suspect licenses and forensics in the event keys are revoked.
For resellers and refurbishers
- Tighten inventory controls. Implement chain‑of‑custody procedures and mark COA affixations as part of shipment checklists.
- Train staff on legal constraints. Many personnel may not understand COAs’ legal status; internal compliance training reduces accidental noncompliance.
- Be transparent with customers. If you sell refurbished systems, use OEM‑authorized refurbisher COAs or the Microsoft‑approved processes for transferring licenses.
If you’ve already purchased cheap keys
- Verify the license status in your organization’s Microsoft admin center.
- Contact the seller and demand proof of legitimate provenance.
- If keys are revoked or services disrupted, prepare to replace the licenses from authorized channels and document your vendor interactions for potential recourse.
Strengths and weaknesses of the enforcement approach
Notable strengths
- Prosecuting a prominent reseller sends a deterrent signal and compensates victims by disrupting criminal supply networks.
- Interagency cooperation — HSI, CCIPS, and U.S. Attorney offices — provides operational reach to investigate cross‑jurisdictional procurement and money flows.
- Public prosecutions educate the market about the legal and compliance risks of grey‑market licenses.
Potential weaknesses and limits
- Enforcement is reactive: it addresses actors once they’ve scaled, but it does not inherently fix upstream custody or packaging vulnerabilities that allow COAs to be separated in the first place.
- Criminal penalties deter but do not fully eliminate demand: as long as buyers prioritize lower prices and vendors tolerate opacity, new actors will emerge to fill the market.
- Technical evolution (embedded keys, Microsoft account activations) reduces the attack surface over time, but long tail devices and legacy licensing keep the market alive for years.
Broader implications for software licensing and supply‑chain integrity
This prosecution is more than a single‑defendant story: it is a cautionary chapter in a larger tale about how physical authentication tokens and legacy distribution models interact with modern online activation systems and global commerce. Two broader lessons stand out:- The shift to digital‑first activations (firmware, Microsoft account bindings, volume licensing portals) reduces reliance on physical artifacts and thereby shrinks the market for diverted COAs, but migration is gradual and uneven. Enterprises and OEMs must accelerate migration where possible.
- Supply‑chain integrity matters for digital goods as much as it does for hardware. Physical stickers, labels, or packaging elements can be as important to IP enforcement as cryptographic keys or DRM. Process discipline — documented handoffs, sealed packaging, and auditable resale channels — are part of the solution.
What Microsoft and the industry can (and should) do next
- Harden physical security and tamper evidence. Improve COA materials and design for forensic traceability and make tampering more visible and damaging to keys.
- Close coverage gaps for older product lines. Offer migration paths or replacement policies for legacy devices to reduce the number of active, redeemable physical COAs in circulation.
- Push for stronger distributor accountability. Encourage or require audits and provenance guarantees for large resellers and wholesalers.
- Public education. Work with industry media and regulators to warn buyers about the downstream costs of cheap keys, including revocation and compliance risk.
Caveats, open questions, and what we could not verify
- Some published reports quote a precise wired amount — $5,148,181.50 — that Richards allegedly sent to suppliers between 2018 and 2023. That figure appears in investigative reporting and seems to originate from the indictment or trial exhibits; Department of Justice summary language typically uses broader phrases like “millions of dollars.” The exact figure is reported by media outlets that covered the trial, but readers should treat specific transaction totals as drawn from trial documents rather than the DOJ’s standardized press release language.
- Public reporting does not always include the full indictment exhibits or a forensic breakdown of where the COAs originated in the supply chain. The prosecution demonstrates criminal liability for trafficking, but public sources do not provide exhaustive detail on the upstream custody failures that permitted the diversion. That means some operational remedies will require cooperation from OEMs, distributors, and investigators whose internal records are not public.
- Finally, this article relies on DOJ public notices, court calendar entries, and reputable technology reporting. Where those sources differ in phrasing or detail, I have noted such discrepancies and indicated where numbers or claims reflect investigative reporting rather than a standardized government press release.
Conclusion: a market, a crime, and a roadmap
The Richards case is a clarifying moment: it shows that the unauthorized trafficking of genuine COA labels is not a victimless act and that federal prosecutors are willing to seek prison time for those who build profitable businesses from diverted software authentication artifacts. For technologists, IT procurement leads, and channel partners, the case should be read as an urgent compliance and supply‑chain management lesson.- If you buy licenses, buy from authorized channels and demand provenance.
- If you resell or refurbish, tighten custody controls and document every handoff.
- If you design licensing systems, accelerate digital activation modes that reduce physical artifacts’ exploitability.
Source: theregister.com Windows, Office software scalper jailed for 22 months