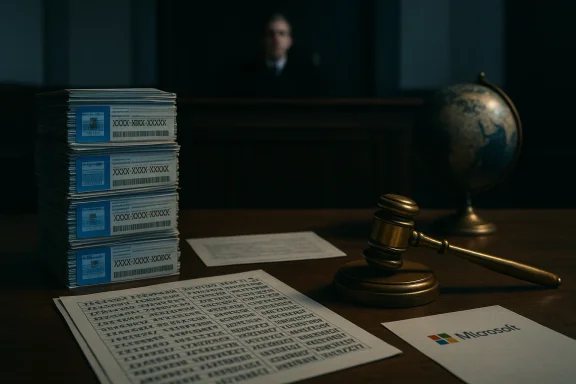
A federal jury and a U.S. district court have put a hard legal cap on a years‑long, low‑tech but high‑value operation that turned genuine Microsoft "Genuine" stickers into a multiyear, multimillion‑dollar resale business: Heidi Richards, 52, the operator of Trinity Software Distribution in Brandon, Florida, was sentenced to 22 months in federal prison and ordered to pay a $50,000 fine after being convicted for conspiring to traffic in illicit Microsoft Certificate of Authenticity (COA) labels.
COA labels — the small tamper‑resistant stickers and cards that historically accompanied Windows and Office media or OEM machines — are intended as evidence that a copy of software is genuine, not as a standalone product or transferable license. Microsoft’s own guidance says a COA “is not a software license” and should never be sold by itself; distribution of COAs separate from their intended hardware or sealed package is not authorized.
Federal prosecutors say Richards and associates purchased tens of thousands of genuine Microsoft COA labels from third parties and suppliers, removed or inspected the printed product keys on those labels, transcribed the 25‑character codes into spreadsheets, and sold the keys in bulk to customers worldwide. The Department of Justice’s Middle District of Florida described the trafficking as a deliberate scheme that transformed physical anti‑counterfeiting artifacts into a tradable commodity.
This case is the latest example of how physical security controls in software distribution — holograms, scratch‑off panels and tamper‑proof labels — can be defeated not by high‑tech hacking but by simple diversion and manual data entry. The legal response reflects an enforcement posture that treats such large‑scale diversion as criminal trafficking, not merely a civil licensing dispute.
COA labels are legitimately distributed only with the software or hardware they are meant to authenticate. The indictment quoted by prosecutors makes that clear: “The only authorized method of downstream distribution for a Windows OEM COA is affixed to the computer on which the software was installed or with the complete, sealed OEM package including the COA label and license.” That legal framing matters because it differentiates lawful resale (package + COA) from trafficking (COA alone).
This approach created a number of operational risks that would later feed the investigation: bank transfer records for bulk payments, spreadsheets and order records, and communications with suppliers and buyers. Those documentary trails supplied prosecutors with the means to quantify the scale and to tie the business activity back to a conscious decision to traffic in COA stickers separately from their intended products.
The conviction demonstrates that federal prosecutors will pursue criminal charges where the trafficking of authentication artifacts is systematic and commercial in scale. While low‑value or isolated COA diversions are typically pursued civilly or administratively, prosecutors made the case that repeated, structured purchases and resale at scale crossed into criminal conspiracy territory.
Prosecutors emphasized that COAs “bear security features intended to dissuade counterfeit duplication” and that their removal and resale undermines legitimate software distribution and intellectual property rights. That reasoning—combining criminal statutes with commercial licensing rules—has been applied in other prosecutions but is notable here because the defendant’s operation used genuine labels rather than forgeries.
Many practitioners point out that the gray market for license keys is not new; the means have changed since the early days of OEM key reselling and KMS emulation, but the same dynamics — arbitrage, lax buyer due diligence, and opaque third‑party sellers — repeat across years and product generations. The criminal case against Trinity is therefore less a unique anomaly than an intensification of enforcement against a persistent marketplace behavior.
Enforcement is one lever to deter bad actors, but it cannot fully substitute for better supply‑chain controls, clearer provenance requirements in secondary markets, and buyer education. The DOJ’s criminal prosecution signals both deterrence and a recognition that large‑scale exploitation of COAs is not merely a commercial violation but a law enforcement priority when it becomes organized and repetitive.
In short: a sticker is not a license, and this prosecution makes clear that treating it as such can carry severe consequences.
Source: Neowin Florida woman jailed over massive Microsoft "Genuine" Windows & Office activation key fraud
 Background
Background
COA labels — the small tamper‑resistant stickers and cards that historically accompanied Windows and Office media or OEM machines — are intended as evidence that a copy of software is genuine, not as a standalone product or transferable license. Microsoft’s own guidance says a COA “is not a software license” and should never be sold by itself; distribution of COAs separate from their intended hardware or sealed package is not authorized.Federal prosecutors say Richards and associates purchased tens of thousands of genuine Microsoft COA labels from third parties and suppliers, removed or inspected the printed product keys on those labels, transcribed the 25‑character codes into spreadsheets, and sold the keys in bulk to customers worldwide. The Department of Justice’s Middle District of Florida described the trafficking as a deliberate scheme that transformed physical anti‑counterfeiting artifacts into a tradable commodity.
This case is the latest example of how physical security controls in software distribution — holograms, scratch‑off panels and tamper‑proof labels — can be defeated not by high‑tech hacking but by simple diversion and manual data entry. The legal response reflects an enforcement posture that treats such large‑scale diversion as criminal trafficking, not merely a civil licensing dispute.
How the scheme worked
Acquisition and the supply chain gap
Prosecutors’ evidence showed the defendant sourced COA labels from a Texas‑based supplier and wired more than $5.14 million to that supplier between mid‑2018 and early 2023. Those purchases reportedly amounted to tens of thousands of individual COA stickers for Windows 10 and Microsoft Office product families. The operation relied on a simple arbitrage: obtain genuine COA labels cheaply, extract the embedded product keys, and resell those keys at a markup to buyers seeking low‑cost activations.COA labels are legitimately distributed only with the software or hardware they are meant to authenticate. The indictment quoted by prosecutors makes that clear: “The only authorized method of downstream distribution for a Windows OEM COA is affixed to the computer on which the software was installed or with the complete, sealed OEM package including the COA label and license.” That legal framing matters because it differentiates lawful resale (package + COA) from trafficking (COA alone).
Harvesting keys and inventorying them
Rather than repackaging COAs with associated software or hardware, employees at Trinity allegedly manually transcribed the printed activation codes from the labels into spreadsheets — an irony that has not been lost on reporters and prosecutors alike. The spreadsheet became inventory: rows of 25‑character keys ready for bulk sale. Federal filings and reporting show simple human labor, not sophisticated automation, scaled the operation.This approach created a number of operational risks that would later feed the investigation: bank transfer records for bulk payments, spreadsheets and order records, and communications with suppliers and buyers. Those documentary trails supplied prosecutors with the means to quantify the scale and to tie the business activity back to a conscious decision to traffic in COA stickers separately from their intended products.
Distribution channels and buyers
Court records and reporting indicate the harvested keys were sold in bulk to customers worldwide. The downstream buyers were not necessarily large enterprises enrolled in Microsoft volume licensing; many of the buyers purchasing low‑cost bulk activations are smaller resellers and end users who prioritize price over provenance — making them the natural demand side for keys harvested from COAs. That demand is what sustains a grey market where stickers with no independent legal value in fact become currency.The legal and enforcement picture
Charges, trial and sentence
Richards was convicted by a jury and later sentenced to 22 months in prison, in addition to a $50,000 fine, a penalty that federal prosecutors portrayed as proportionate to the scale of the trafficking operation. The U.S. Attorney’s Office for the Middle District of Florida prosecuted the case, with assistance from Homeland Security Investigations (HSI) and attorneys from the Department of Justice’s Computer Crime & Intellectual Property Section (CCIPS).The conviction demonstrates that federal prosecutors will pursue criminal charges where the trafficking of authentication artifacts is systematic and commercial in scale. While low‑value or isolated COA diversions are typically pursued civilly or administratively, prosecutors made the case that repeated, structured purchases and resale at scale crossed into criminal conspiracy territory.
Statutory and policy framework
Two distinct legal forces intersect in this case. First, intellectual property and anti‑counterfeiting statutes — and precedent around the unauthorized trafficking of authenticating devices or labels — create a statutory basis for criminal prosecution when actors knowingly traffic in standalone COAs. Second, Microsoft’s distribution policies, licensing agreements and channel rules make explicit that COAs do not constitute transferable licenses and must not be sold separately. Those policies, while civil in nature, buttress criminal prosecutions by clarifying that commercial resale of COAs as independent items is outside authorized channels.Prosecutors emphasized that COAs “bear security features intended to dissuade counterfeit duplication” and that their removal and resale undermines legitimate software distribution and intellectual property rights. That reasoning—combining criminal statutes with commercial licensing rules—has been applied in other prosecutions but is notable here because the defendant’s operation used genuine labels rather than forgeries.
Why COAs still have value — and why that value is illegal
COA value is strictly contextual: by themselves a COA label is not a license, but within the Windows/Office activation ecosysteduct key embedded in a genuine COA can often perform the technical act of activation. Buyers who want inexpensive activations therefore face a temptation: if a legitimate COA’s printed key works, it can activate Windows or Office for a machine, at least until Microsoft detects misuse. That technological reality creates an illicit market even though, legally and contractually, the COA carries no transferable value. ([devicepartner.microsoft.com](Communication page | Licensing FAQ of a COA — from OEM packing to end user — is intended to keep the key tethered to specific hardware or sealed packaging. When that tether is cut, the key converts from a physical validation control into a simple code string that can be reused and resold. That conversion is what converts an otherwise inert sticker into contraband.Impact on buyers, channels and IT procurement
- Risk of invalid activation or blocking: Keys harvested and resold at scale are susceptible to mass‑use detection, blacklisting, or revocation by Microsoft if misused patterns emerge.
- Compliance and audit exposure: Organizations that source bulk keys from outside authorized channels risk failing licensing audits and incurring retroactive licensing fees, penalties and remediation costs.
- Operational and support gaps: Non‑genuine or improperly procured keys can leave systems out of Microsoft’s support and update streams — an outsized operational risk for enterprises and MSPs.
Community reaction and the gray market context
The story has prompted brisk discussion in IT and Windows enthusiast communities. Forum threads and community posts dissect the mechanics and the economic incentives at play, and many IT professionals treat the conviction as a corrective moment: cheap keys are seldom worth the downstream liability. Community analysis also highlights that the scheme was low‑tech and visible enough that the documentation trail (payments, spreadsheets, shipment records) made it prosecutable.Many practitioners point out that the gray market for license keys is not new; the means have changed since the early days of OEM key reselling and KMS emulation, but the same dynamics — arbitrage, lax buyer due diligence, and opaque third‑party sellers — repeat across years and product generations. The criminal case against Trinity is therefore less a unique anomaly than an intensification of enforcement against a persistent marketplace behavior.
Technical considerations for defenders and procurement teams
Practical detection signals
- Unusually low unit prices — offers that materially undercut authorized channel pricing are a red flag.
- Keys sold without accompanying media or hardware — legitimate channels supply COAs only with hardware or sealed software; standalone keys are suspect.
- Bulk sales to one buyer from a seller with weak provenance — check supplier history, tax and business registrations, and request documentation tracing keys back to OEMs or authorized distributors.
- Activation monitoring — watch for clusters of activations from disparate geographies tied to the same key series; these may indicate mass reuse and are grounds for alerting Microsoft or initiating remediation.
How to harden procurement and reduce risk
- Insist on invoices and supplier documentation that explicitly show keys were sold as part of a sealed OEM package or a volume licensing agreement.
- Use authorized Microsoft resellers and the Microsoft Volume Licensing Service Center (or equivalent regional programs) for enterprise needs.
- Implement procurement policies that require vendor due diligence for any software or key purchases outside established contracts.
- If in doubt, contact Microsoft licensing support or report suspicious sellers; the company provides channels for piracy reporting and license verification.
Broader implications: supply chain trust and enforcement
The Richards case exposes technical and governance gaps at the intersection of physical distribution and digital activation. Software licensing regimes have long relied on a blended model — digital activation plus physical proof — but when physical artifacts are diverted upstream (surplus, returns, refurbishing chains, even theft), the downstream economics change.Enforcement is one lever to deter bad actors, but it cannot fully substitute for better supply‑chain controls, clearer provenance requirements in secondary markets, and buyer education. The DOJ’s criminal prosecution signals both deterrence and a recognition that large‑scale exploitation of COAs is not merely a commercial violation but a law enforcement priority when it becomes organized and repetitive.
Caveats and unverifiable eleting aggregates figures (for example, the $5,148,181.50 wiring total and the “tens of thousands” of COAs) that are drawn from DOJ filings and press releases; while DOJ’s statement is authoritative, some secondary sources paraphrase or summarize those figures differently. Readers should treat minor numeric variance across outlets with caution and refer to the official court record for exact line items.
- Some reporting includes alternate names and addresses tied to the defendant. Court documents provide the definitive identification and are the appropriate primary reference for legal names and aliases. Where press outlets differ, the DOJ press release is the controlling public recotps://www.justice.gov/usao-mdfl/pr/software-distributor-sentenced-22-months-prison-conspiracy-traffic-illicit-microsoft)
What this means for Microsoft and software vendors
Vendors that rely on physical authenticity artifacts must continuously adapt their anti‑fraud design and supply‑chain controls. Several practical responses can help blunt the profitability of COA diversion:- Move activation to stronger, hardware‑anchored mechanisms that are not simply a printed code.
- Improve tamper‑evidence and traceability features on physical labels, including serialized tracking that is checked against vendor databases upon activation.
- Invest in monitoring and pattern detection for suspicious activation behavior tied to batches of keys.
Final analysis — lessons and risks
The Trinity Software Distribution conviction is a timely reminder that digital rights and physical artifacts are inseparably linked in software commerce. A few clear takeaways:- Legal risk is real and enforceable. Large‑scale trafficking of COA labels can be prosecuted criminally, not just litigated civilly. The 22‑month sentence and the $50,000 fine send a practical enforcement signal.
- The gray market persists because demand remains. Organizations and individuals chasing dramatic savings create the market that traffickers serve. Procurement rigor and vendor verification are essential defenses.
- Low‑tech methods can scale into high‑value fraud. Manual transcription and spreadsheet inventories may look unsophisticated, but volume amplifies impact and leaves clear forensic trails for investigators.
- Vendors must modernize provenance and activation designs. The fundamental tension is between convenience and control; stronger cryptographic binding of licenses to devices or accounts reduces the value of isolated physical labels.
In short: a sticker is not a license, and this prosecution makes clear that treating it as such can carry severe consequences.
Source: Neowin Florida woman jailed over massive Microsoft "Genuine" Windows & Office activation key fraud