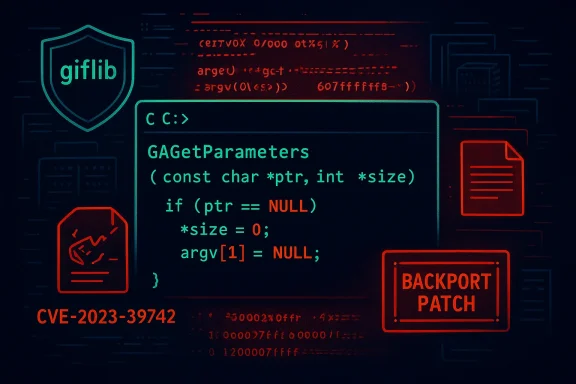
The giflib library shipped in version 5.2.1 contains a flaw that can cause a local segmentation fault in the command-line utilities — a denial‑of‑service condition traced to the getarg.c argument‑parsing code and tracked as CVE‑2023‑39742.
giflib is a long‑standing, small C library and toolset used to read, write, and manipulate GIF images and to provide utilities such as gif2rgb. It is packaged across many Linux distributions and embedded toolchains, and it is frequently present on developer machines and in build images where basic image tooling is required. The vulnerability was publicly recorded in August 2023 and has been catalogued across major vulnerability databases.
The immediate technical symptom reported is a segmentation fault that occurs inside the argument‑parsing routines implemented in getarg.c when the affected tools are invoked with malformed or unexpected inputs. Upstream metadata and vendor advisories characterize the issue as a crash (availability impact) rather than an information disclosure or privilege escalation.
Across the vulnerability ecosystem, multiple scanners and databases reproduced (or at least ingested) the same description: segmentation fault in getarg.c, availability impact, and a CVSS 3.1 base score reported around 5.5 (Medium) in many entries. These independent catalog entries (NVD, OpenCVE, Recorded Future and vendor advisories) cross‑confirm the basic technical facts.
If you maintain downstream packages, consider contributing the regression tests and the smallest possible patch upstream so that future upstream releases include the fix and downstream consumers can rely on a canonical point release.
Furthermore, the giflib example demonstrates broader lessons:
By treating even a local CLI crash as an operational and supply‑chain risk, teams can prevent small parsing bugs from becoming larger outages or pivot points in complex infrastructures.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
giflib is a long‑standing, small C library and toolset used to read, write, and manipulate GIF images and to provide utilities such as gif2rgb. It is packaged across many Linux distributions and embedded toolchains, and it is frequently present on developer machines and in build images where basic image tooling is required. The vulnerability was publicly recorded in August 2023 and has been catalogued across major vulnerability databases.The immediate technical symptom reported is a segmentation fault that occurs inside the argument‑parsing routines implemented in getarg.c when the affected tools are invoked with malformed or unexpected inputs. Upstream metadata and vendor advisories characterize the issue as a crash (availability impact) rather than an information disclosure or privilege escalation.
What exactly goes wrong: a technical overview
The vulnerable surface: getarg.c and gif2rgb
The fault is triggered in the library's command‑line argument parsing path (the getarg.c component), which is used by utilities such as gif2rgb. AddressSanitizer output posted to the upstream bug tracker shows the crash occurring when GAGetParameters / GAGetArgs (the library's argument routines) call formatted input functions and end up reading from a null/zero page or otherwise dereferencing invalid memory. That crash path produces a typical local segmentation fault and can also expose memory‑leak conditions in associated utilities.Why this is an availability issue
Because the fault manifests as a reliable segmentation fault in the userspace utility, an attacker or local user who can run the fluent tooling (or the contexts where it’s invoked) can cause repeated crashes, effectively denying service for that utility or any appliance that relies on it. The vulnerability has been assessed as producing no confidentiality or integrity loss, but high availability impact in the vulnerable component. Many vulnerability trackers therefore rate the flaw as a local-denial‑of‑service with a medium CVSS base score.Local vs remote: the practical attack vector
A key fact for defenders: the majority of public advisories describe the attack vector as local — an attacker needs the ability to run the affected binary (or cause it to be run on their behalf) to trigger the crash. That means remote, unauthenticated attacks against network stacks are not the typical path — but any service or pipeline that executes giflib tools on untrusted inputs (for example, an upload‑processing job on a server) may expose a remote‑triggerable vector if user‑provided files or input cause the affected codepath to run. Treating this as a supply‑chain and execution‑context risk is critical.Evidence and reproducibility
A public bug report filed on the giflib SourceForge tracker includes an AddressSanitizer trace and a minimal repro pattern showing a crash when invoking gif2rgb with malformed arguments (for example, invoking gif2rgb -s under certain conditions). The bug report contains explicit sanitizer output that ties the crash back to the getarg.c call stack and documents accompanying memory leaks observed under ASan. That repro demonstrates the reliability of the crash and underpins the DoS classification.Across the vulnerability ecosystem, multiple scanners and databases reproduced (or at least ingested) the same description: segmentation fault in getarg.c, availability impact, and a CVSS 3.1 base score reported around 5.5 (Medium) in many entries. These independent catalog entries (NVD, OpenCVE, Recorded Future and vendor advisories) cross‑confirm the basic technical facts.
Vendor and distribution responses (what is fixed, where)
- Ubuntu’s security tracker marked the issue and indicates fixes in distribution packages — for example, the Ubuntu packages that ship giflib have been updated in affected releases to versions that mitigate the crash in practice; Ubuntu treat this as low priority in many images because it is a CLI‑tool crash rather than an escalative remote exploit. If you run Ubuntu or a derived image, check the distro advisory for the exact package version number for your release.
- SUSE lists the issue and shows it resolved in packaged builds (their advisory lists specific package updates). This demonstrates that vendor maintainers have provided distribution‑level fixes or mitigations in those product trees.
- Amazon Linux’s advisory (ALAS) indicates fixes for affected Amazon Linux images. Red Hat and other vendor trackers also recorded the CVE; however, some vendor pages reported that no upstream fix in the canonical giflib source was available at the time their packages were updated. That pattern — distribution patching without an upstream point release — is common for small projects where distributors backport patches into packaging trees.
- Several vulnerability management services and upstream scanners (Snyk, GitLab dependency advisories, and others) indicate that as of their last updates no fixed upstream giflib version had been published at the time the advisories were assembled; instead, distributions backported patches into their packaging. This matters: if you maintain bespoke builds or vendors embed the raw upstream source, you may not receive the distribution‑level fixes and must either apply the upstream patch yourself or upgrade when a fixed upstream release is published.
Risk analysis for WindowsForum readers
Not an immediate remote code‑execution worm but a real availability risk
The technical consensus is that CVE‑2023‑39742 causes a reliable crash in an argument‑parsing code path rather than a wide‑reaching memory‑corruption primitive that was trivially weaponizable into remote code execution. That is meaningful: the severity is primarily Denial‑of‑Service for the affected utility or the process that embeds the library. Still, for environments that automatically process untrusted files (CI pipelines, web upload services, image conversion servers, container build systems), a local crash becomes a remote attack vector if the attacker can feed inputs that cause the vulnerable utility to be executed.Supply‑chain and device implications
Even if an OS distribution has issued a fix, many laptops, appliances, or embedded devices ship their own giflib copy or bundle it statically. Those embedded instances will not automatically inherit distribution fixes. Enterprises should treat giflib as a small but not insignificant supply‑chain risk: scanning your artifacts for giflib 5.2.1 or older and verifying whether your images contain the problematic binary is important. Distribution advisories and package changelogs will be the authoritative way to know whether your deployed images are fixed.Likelihood of exploitation
Public EPSS and exploit telemetry show a very low probability of active exploitation for this CVE, and public advisories do not indicate a verified remote exploit in the wild at the time of writing. That does not remove the need to remediate: the vulnerability is trivially reproducible locally and therefore attractive to attackers who can run or invoke the tool. Prioritize remediation according to exposure: public servers and media‑processing pipelines come first.Detection, validation, and testing guidance
How to detect affected instances
- Inventory your images and packages for giflib version 5.2.1 or earlier. Use your package manager’s query tools (dpkg, rpm, apk) to list installed versions and build images. Distribution CVE pages list package names and fixed package versions you can match against.
- Search binaries and containers for the gif2rgb or other giflib utilities: many automated scanners and container CVE scanners will flag giflib 5.2.1. For bespoke builds, inspect the source tree for getarg.c and review commit histories.
- Monitor crash and application logs for repeated segmentation faults in giflib utilities; set up alerts for core dumps or for elevated exit codes from image‑conversion jobs. Unexpected repeated process crashes in image pipelines are a strong detection signal.
How to validate a remediation
- Confirm the installed package version is a distribution‑sanctioned fixed build (for example, the Ubuntu fixed package version noted in the Ubuntu tracker).
- Reproduce the previously failing argument invocation under a safe, isolated test environment (do not run untrusted inputs on production). The upstream bug page shows minimal repro patterns that cause gif2rgb to crash; use sanitized, local test inputs for confirmation rather than public PoC payloads.
- Verify that the invocation no longer produces a segmentation fault and that memory‑sanitizer runs (ASan/Valgrind) do not show the same failure. If you maintain a CI pipeline, add the regression case as a test.
Mitigation and remediation recommendations
Immediate actions (0–24 hours)
- If you operate public servers or automated pipelines that call giflib utilities on untrusted input, stop or isolate those pipelines until you can apply package‑level fixes or mitigations. A temporary mitigation is to refuse user‑supplied GIFs or to run the conversion step in an isolated, sandboxed environment (container, restricted user account, seccomp, AppArmor/SELinux policy).
- If your workloads are exclusively on distributions that already published fixed packages (Ubuntu, SUSE, Amazon Linux states), update those packages immediately to the vendor‑published fixed versions. Confirm the package upgrades removed the vulnerable binary or patched the code path.
Short term (24–72 hours)
- For environments where you build giflib from upstream sources, either:
- Apply the distro backport patch if you can obtain it from your distribution’s source‑package change log, or
- Rebuild the tool(s) with hardened compiler flags (e.g., -fstack-protector-strong, -D_FORTIFY_SOURCE=2) and enable stack canaries and PIE to make exploitation of memory faults harder until an upstream fixed release is available. Note that hardening mitigations are not a replacement for a correct functional fix but can raise the bar.
- Containerize or sandbox any image‑processing toolchains and restrict access rights on the conversion tools so that even if an attacker can trigger a crash, the blast radius is small.
Longer term (weeks)
- Add giflib to your SBOM and scanning roster if it is not already included. Ensure that any third‑party binary you ship or embed is built from a patched source or a vetted distribution package.
- If you maintain embedded appliances that include giflib statically, schedule a firmware/software update to replace the static library with a patched build or a safer image‑handling library.
Responsible disclosure and upstream status
Upstream issue tracking and community notes (SourceForge bug #166) contain the initial repro and discussion; however, at the time of initial reporting many third‑party scanners and advisories noted that no upstream release had yet been published to resolve the bug and that distributions applied backports in their packaging. This uneven upstream vs distribution picture is common for smaller OSS projects: distributions sometimes patch and ship fixes faster than the upstream project can issue a formal point release. If your environment depends on upstream tarballs or third‑party vendor builds, verify the origin of the patch (distribution backport vs upstream release).If you maintain downstream packages, consider contributing the regression tests and the smallest possible patch upstream so that future upstream releases include the fix and downstream consumers can rely on a canonical point release.
Practical hardening checklist (for sysadmins and devops)
- Inventory: Identify all hosts, containers, and build systems that contain giflib version 5.2.1 or earlier. Use package queries and SBOMs.
- Update: Apply distribution patches from your OS vendor (Ubuntu, SUSE, Amazon Linux advisories list fixed packages). Prioritize public servers and media‑processing hosts.
- Isolate: Run any image‑conversion or gif utility within containers, sandboxes, or limited‑privilege user accounts. Use seccomp/AppArmor/SELinux policies to restrict syscalls and limit damage from crashes.
- Monitor: Alert on repeated gif2rgb/giflib process crashes, core dumps, and failed conversions. Track incident tickets for repeated, correlated failures.
- Test: Add the known invalid argument/ASan repro as a test‑case to CI pipelines to avoid regressions.
- Build hardening: For self‑built packages, enable stack canaries, PIE, RELRO, and compiler sanitizers in debug builds.
- Supply‑chain: If you embed giflib statically in appliances, treat this as a firmware update item and schedule patches with appropriate QA windows.
Why this matters beyond a single CLI crash
A segmentation fault in a utility can be a trivial reliability bug in many contexts — but in modern continuous and automated environments the same crash can be triggered remotely via file uploads, automated builds, or image‑processing microservices. Unattended pipelines and headless conversion services are common in web hosting, content delivery, and CI — environments where a local CLI crash turns into an operational outage or can be chained as part of a larger supply‑chain or lateral‑movement play.Furthermore, the giflib example demonstrates broader lessons:
- Small, old libraries remain a real attack surface.
- Distribution patching strategies vary: a fix in your chosen distro does not mean the upstream project has an official release.
- Inventory/packaging discipline (SBOM, container image scanning) is essential to safely manage transitive dependencies.
Conclusion
CVE‑2023‑39742 is a reliable, local segmentation‑fault vulnerability in giflib 5.2.1’s getarg.c that results in denial‑of‑service for the affected utilities and any pipeline that runs them on untrusted input. The defect is reproducible (SourceForge bug report includes ASan traces), catalogued by major CVE/NVD entries, and has been addressed at the distribution level in several vendor package trees while upstream release status has been uneven. Administrators should prioritize patching distribution packages where available, isolate and sandbox affected tools, and inventory their environments for embedded or static giflib copies that may not inherit distro fixes.By treating even a local CLI crash as an operational and supply‑chain risk, teams can prevent small parsing bugs from becoming larger outages or pivot points in complex infrastructures.
Source: MSRC Security Update Guide - Microsoft Security Response Center