A subtle parsing bug in Go’s build tooling quietly opened a door for attackers to run code during compilation — and the fallout is wider than you might expect if your environment uses gccgo or builds untrusted modules. CVE-2023-29405 exposes an improper sanitization of LDFLAGS with embedded spaces in the go command when cgo is in play, allowing an attacker to smuggle disallowed linker flags through sanitization and achieve arbitrary code execution at build time. This is a supply-chain problem: the vulnerability is triggered while fetching or building code, not while the resulting binary runs, and it can be exploited by supplying crafted #cgo LDFLAGS in a malicious module or dependency.
The Go toolchain supports interfacing with C through cgo, which lets Go programs include C code and pass flags to the C compiler and linker using directives such as
This issue is limited to workflows that use the gccgo compiler front end. The default Go compiler — often referred to as gc — parses and handles flags differently and was not affected by this specific bug. That distinction matters for whether your systems are exposed; many systems and CI environments use the default gc toolchain and were not vulnerable, but a notable number of Linux distributions and some developer toolchains use gccgo either by preference or packaging choices.
The Go project addressed this issue in security fixes, and patched releases were published. The vulnerable ranges include older 1.19 series releases and early 1.20 releases; the short remediation path is to upgrade to the fixed releases or later. The vulnerability carries a high severity rating because it grants code execution at build time, which is often an immediate route to full system compromise when build machines or CI runners are involved.
The sanitization is intended to strip or reject flags that are not on an approved list. That filtering relies on predictable tokenization of flags: each flag appears as a distinct token. The trouble comes when a token itself contains embedded space characters; if the tokenization layer or the file format used to persist flags collapses or rearranges flags that contain internal whitespace, then a malicious author can "hide" a dangerous flag inside the argument of another flag.
A representative example (sanitized and simplified) shows the pattern:
Note: the vulnerability disclosures and advisories also grouped related cgo/parser issues that affect other edge cases; treat those as individual CVEs with their own patches and mitigations.
This is a textbook case where canonicalization — enforcing a single, unambiguous representation of data — prevents injection and smuggling attacks. It’s also a reminder that build tooling needs the same threat modeling and input validation scrutiny we apply to runtime code.
If you run Go toolchains:
CVE-2023-29405 belongs to a pattern of vulnerabilities that weaponize development infrastructure. Fixing the code is only the first step — the larger work is building safer, auditable, and resilient build systems that reduce the blast radius when a single malicious module appears.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background and overview
Background and overview
The Go toolchain supports interfacing with C through cgo, which lets Go programs include C code and pass flags to the C compiler and linker using directives such as // #cgo LDFLAGS: .... To reduce risk, the go command performs sanitization on flags exposed by imported packages before invoking compilers or linkers. CVE-2023-29405 arises when those LDFLAGS contain embedded spaces: the sanitization logic mishandles such flags and can be bypassed by hiding disallowed arguments inside what looks like a valid flag’s argument. The result: dangerous linker arguments can be passed to the toolchain and executed during the build.This issue is limited to workflows that use the gccgo compiler front end. The default Go compiler — often referred to as gc — parses and handles flags differently and was not affected by this specific bug. That distinction matters for whether your systems are exposed; many systems and CI environments use the default gc toolchain and were not vulnerable, but a notable number of Linux distributions and some developer toolchains use gccgo either by preference or packaging choices.
The Go project addressed this issue in security fixes, and patched releases were published. The vulnerable ranges include older 1.19 series releases and early 1.20 releases; the short remediation path is to upgrade to the fixed releases or later. The vulnerability carries a high severity rating because it grants code execution at build time, which is often an immediate route to full system compromise when build machines or CI runners are involved.
How the bug works (technical analysis)
What the go tool does with #cgo LDFLAGS
When a package includes cgo directives, it may list compilation and linking flags that should be applied when that package is built. The go command parses those#cgo directives and, before passing things to a system linker, performs checks and sanitization to block obviously dangerous flags — for example, flags that would cause an arbitrary shell command to execute or that pass unexpected inputs to the linker.The sanitization is intended to strip or reject flags that are not on an approved list. That filtering relies on predictable tokenization of flags: each flag appears as a distinct token. The trouble comes when a token itself contains embedded space characters; if the tokenization layer or the file format used to persist flags collapses or rearranges flags that contain internal whitespace, then a malicious author can "hide" a dangerous flag inside the argument of another flag.
The smuggling trick
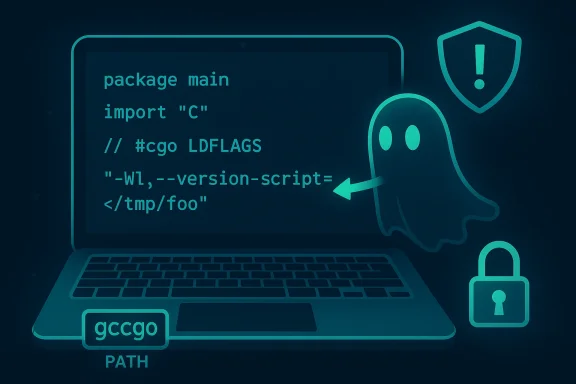
Attackers can smuggle a dangerous flag into the sanitized set by embedding it inside another flag’s quoted argument or by relying on how the flags are later reconstructed and handed to the linker. In practice, a crafted directive might look benign to a naive sanitizer but, after parsing collisions and split/join behavior, the linker sees extra arguments that the sanitizer intended to prevent.A representative example (sanitized and simplified) shows the pattern:
- Malicious #cgo entry:
// #cgo LDFLAGS: -Wl,-B /tmp; touch /tmp/pwned- What the sanitizer expects:
-Wl,-Band"/tmp; touch /tmp/pwned"as a single, safe-looking argument- What the toolchain might pass to the linker:
-Wl,-Bthen"/tmp;"and thentouchand then/tmp/pwned— turning a single directive into multiple linker/shell tokens and allowing command execution.
Scope: when the vulnerability is exploitable
- Build-time only: this is not a runtime memory corruption or logic bug in running binaries; it occurs while the go command is constructing and invoking C toolchain commands during a build that uses cgo.
- Trigger vector: fetching and building code that contains #cgo directives. Commands like
go get(or other commands that build packages) can trigger the vulnerable code path when they operate on untrusted or malicious modules. - Compiler dependency: the vulnerability is specific to environments that rely on the gccgo compiler front end. The default gc toolchain implements different parsing semantics and remains unaffected by this particular flaw. However, the broader risk remains for any environment that uses gccgo.
- Supply-chain angle: a malicious or compromised module published to a package repository can weaponize this behavior to execute code on developer laptops, build servers, or CI runners that compile the module.
Affected versions and remediation timeline
The Go project identified and patched the issue promptly after disclosure. The vulnerable version ranges are:- Affected: 1.19.x releases before the security patch (fixed in 1.19.10)
- Affected: 1.20.0 and newer up to but excluding the 1.20.5 patch release (fixed in 1.20.5)
- The fix was backported where appropriate and made available across supported release lines.
Note: the vulnerability disclosures and advisories also grouped related cgo/parser issues that affect other edge cases; treat those as individual CVEs with their own patches and mitigations.
Real-world impact and risk assessment
Why build-time code execution is high-risk
Build machines and developer workstations are attractive targets because they typically run with broad access to code repositories, signing keys, artifacts, and CI service credentials. A single malicious build step can:- Write files or tools that later persist into published artifacts.
- Steal credentials or push further lateral movement by using CI tokens and service accounts accessible to the build runner.
- Drop backdoors into compiled artifacts or distribution packages.
- Destroy or hold build infrastructure hostage (denial-of-service via persistent corruption or sabotage).
Who must care most
- Teams and organizations using gccgo as their default or alternate Go compiler (some distributions opt for gccgo).
- CI/CD environments that automatically build third-party modules without pinned modules and that allow cgo.
- Developers who run
go getor other build commands directly against external module sources without relying on a trusted module proxy or checksum verification.
Detection, mitigation and hardening steps
If you maintain Go development environments, follow this multi-layered checklist to detect exposure, mitigate immediate risk, and harden build systems.1. Quick inventory (immediate actions)
- Check your Go version on every build host and developer machine:
- Run:
go version - If output shows an older release than the fixed versions for your branch, plan to update immediately.
- Check whether gccgo is present or used:
- Test whether the
gccgobinary exists: rungccgo --versionor check forwhich gccgo. - Inspect build logs and tooling wrappers to see whether
gccgoappears. The go command will attempt to use a compiler namedgccgoif it’s present in PATH, so an unexpected PATH entry can flip which compiler is used. - If you rely on distribution-packaged Go, use your package manager’s security advisory feed and update the golang package as published by the vendor.
2. Patch and upgrade (recommended remediation)
- Upgrade the Go toolchain to at least the patched releases:
- For 1.19: upgrade to 1.19.10 or later.
- For 1.20: upgrade to 1.20.5 or later.
- Where packagers issue fixes, apply the vendor-supplied updates for your platform; vendors often produce backports for older OS images.
3. Short-term mitigations while patching
- Avoid building untrusted modules: don’t
go getor build code from unknown or new module sources on key machines. - If your projects do not require cgo, disable it in CI and build scripts:
- Set
CGO_ENABLED=0in CI job definitions for builds where cgo is not required. - Prefer the default gc toolchain for build hosts where possible; ensure
gccgois not accidentally present in PATHs used by CI runners. - Restrict network access for build runners and use dedicated, least-privilege service accounts for CI tasks.
4. Supply-chain and module hardening (longer-term)
- Use module integrity checks:
- Ensure module checksums are enforced; rely on Go’s module checksum database behavior and do not bypass the checksum validation unless you have a specific, reviewed reason.
- Use a trusted module proxy or mirror and lock module versions in go.sum/go.mod.
- Pin and audit transitive dependencies — automated dependency scanning and SCA tools should flag packages that include cgo directives or native code.
- Apply principle of least privilege to CI tokens and credentials: prevent a single build job from pushing external changes or accessing sensitive systems.
5. Monitoring and detection
- Audit CI build logs for unexpected linker flags or third-party compilations that reference system-level linkers with unusual arguments.
- Monitor for suspicious files created as a result of builds, unexpected calls to package managers or shell commands during build steps, and newly created artifacts with strange metadata.
- Treat any anomaly in build outputs as a potential compromise until proven otherwise — a cautious, forensic-first approach is warranted after a suspected breach.
Practical steps for Windows users and admins
Many Windows developers do not use gccgo by default, but the same supply-chain risks can cross OS boundaries. Here’s a Windows-focused checklist:- Verify
go versionon your Windows developer machines and in any Windows-based CI runners. - Confirm whether
gccgoexists on your PATH. On Windows,gccgois uncommon unless you have installed a GCC toolchain or a Unix-like environment. - If you operate cross-platform build farms, ensure Linux-based runners, which are more likely to have gccgo present, follow the same patching and hardening guidance.
- In Windows CI templates and build scripts, explicitly set
CGO_ENABLED=0if your build doesn’t require cgo to reduce attack surface. - Use isolated build agents for untrusted builds and disallow them from accessing production secrets or write access to artifact repositories.
Developer and CI/CD best practices to reduce build-time risk
- Prefer pure-Go modules and avoid cgo unless you must interoperate with native libraries.
- Pin module versions and maintain a vetted internal module proxy for third-party code.
- Run builds in ephemeral, well-instrumented environments with limited privileges.
- Use deterministic, audited build steps and avoid running ad-hoc
go geton unfamiliar modules in production build jobs. - Enforce module checksum verification and do not set
GOSUMDB=offor bypass validation. - Regularly check for and apply security updates to your toolchain and build images.
Why the fix matters: the upstream correction
The Go project’s remediation corrected the root cause by changing how cgo flags are recorded and reconstructed; flags are now emitted in a canonical one-flag-per-line representation (or equivalent safe format), preventing spaces in a single token from being interpreted as multiple tokens in the later processing stages. In short, the change removes the ambiguity that allowed a malicious payload to be split into multiple linker arguments.This is a textbook case where canonicalization — enforcing a single, unambiguous representation of data — prevents injection and smuggling attacks. It’s also a reminder that build tooling needs the same threat modeling and input validation scrutiny we apply to runtime code.
Known uncertainties and caveats
- This particular CVE applies to workflows that use gccgo. If you are confident your environment uses only the default gc toolchain and you have no gccgo binary in PATH on build hosts or developer machines, your exposure to this exact flaw is lower, though other related cgo vulnerabilities may still apply.
- The exact exploitation path depends on system-specific flag parsing and the underlying C toolchain; practical exploitability in some environments may require additional conditions. That said, the potential severity is high when those conditions are met.
- Always treat a defensive posture that relies only on “we don’t use gccgo” as incomplete — attackers commonly pivot to weaker hosts in a distributed development environment, and build assets often move between machines and operating systems.
Conclusion and action plan
CVE-2023-29405 is a sharp reminder that vulnerabilities can lurk in the scaffolding around software — the compilers, linkers, and build-time tooling — not just in application source code. Because the vulnerability enables code execution during builds, the microscopy needed to find and fix it is justified: build-time compromise is a reliable route to supply-chain attacks.If you run Go toolchains:
- Immediately identify which hosts use Go and whether any of them have gccgo available.
- Patch the Go toolchain to the documented fixed releases (1.19.10, 1.20.5, or later).
- In CI and developer workflows: disable cgo where unnecessary, avoid
go geton untrusted modules, pin dependencies, and use module checksums and trusted proxies. - Audit build logs and runners for suspicious activity and harden CI agents with least privilege.
CVE-2023-29405 belongs to a pattern of vulnerabilities that weaponize development infrastructure. Fixing the code is only the first step — the larger work is building safer, auditable, and resilient build systems that reduce the blast radius when a single malicious module appears.
Source: MSRC Security Update Guide - Microsoft Security Response Center