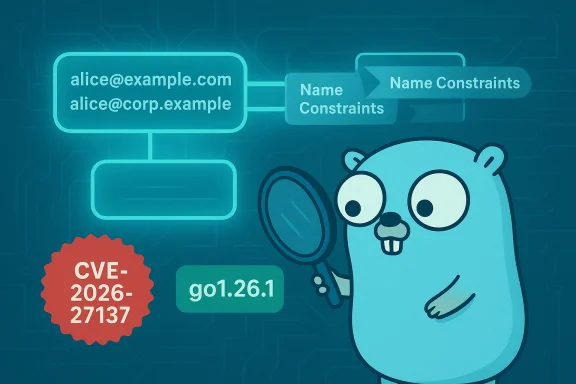
A subtle correctness bug in Go’s X.509 verification code — tracked as CVE-2026-27137 — can cause certificate chains to ignore multiple email-address name constraints when those constraints share the same local-part but differ by domain. The practical upshot: under specific conditions a certificate chain that should have been rejected because of name constraints may be accepted by crypto/x509’s Certificate.Verify, potentially allowing a trusted chain to vouch for email identities that were intended to be prohibited. The flaw was reported to the Go team and fixed in the point release that closes out the 1.26 line; operators and developers should treat this as a targeted correctness issue with material risk for any code that relies on email-address name constraints enforced by the Go standard library. (go.dev)
Certificate name constraints are a defensive control in X.509 that let a CA restrict where certificates it issues may be used. Name constraints can apply to DNS names, IP ranges, email addresses, RFC822Name entries, and other identifier types. They are used in hierarchical PKI setups to limit delegated issuance — for example, to prevent a subordinate CA from issuing certs for high-risk domains or email addresses outside of a designated scope.
Go’s crypto/x509 implements those checks as part of the chain verification routine. During Certificate.Verify the package builds candidate chains, then checks name constraints and other restrictions. CVE-2026-27137 is a correctness problem in the email-specific name-constraint code path: when a certificate contains multiple full email-address constraints that share a common local part (the part before the ‘@’) but different domains (the part after the ‘@’), crypto/x509 was failing to enforce all constraints and only considered the last constraint seen. That means an excluded or not-permitted email address could escape enforcement if an earlier constraint was silently ignored. (go.dev)
This is a logic bug rather than, say, a memory-safety vulnerability or panic-on-malformed-input issue. It’s rated as an improper certificate validation weakness (CWE-295) because failing to apply name constraints correctly weakens the guarantees that PKI policy is supposed to provide. The vulnerability was reported by Jakub Ciolek and tracked in the Go project’s security issue record.
In the buggy crypto/x509 path, the constraints are parsed and stored in a way that collapses or overwrites earlier entries that share the same local-part, leaving only the last constraint in the internal table. As a consequence, the check routine looks up constraints by local-part and only applies the final constraint value, ignoring previous entries that would have denied the leaf address. That single-step logic error produces a gap in enforcement. (go.dev)
The Go project published security releases (including go1.26.1) that incorporate the fix; community security announcements and downstream advisories have catalogued the release. Security scanners and vendors (for example Tenable and several Linux distributions) are recommending upgrades to go1.26.1 or to vendor-patched packages. If you use pre-built Go packages from your operating system or a language/runtime distribution, check your vendor’s security tracker and apply the update they provide.
The fix is straightforward: upgrade to go1.26.1 (or apply the patched distro packages) and rebuild Go-built artifacts. The harder work is operational: discovering every binary that needs rebuilding, verifying vendor-supplied images, and remediating systems that implicitly trust certificates for authorization. Organizations that use certificate-based email identity or operate internal CAs should prioritize this CVE accordingly.
If you run Go-built services, treat this as a rebuild-and-deploy task with high priority for all systems that use certificate-based email SAN authorization. The vulnerability’s constraints reduce the immediacy of mass exploitation, but its ability to silently undermine name-constraint enforcement makes it a practical concern for PKI-reliant environments. (go.dev)
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
Certificate name constraints are a defensive control in X.509 that let a CA restrict where certificates it issues may be used. Name constraints can apply to DNS names, IP ranges, email addresses, RFC822Name entries, and other identifier types. They are used in hierarchical PKI setups to limit delegated issuance — for example, to prevent a subordinate CA from issuing certs for high-risk domains or email addresses outside of a designated scope.Go’s crypto/x509 implements those checks as part of the chain verification routine. During Certificate.Verify the package builds candidate chains, then checks name constraints and other restrictions. CVE-2026-27137 is a correctness problem in the email-specific name-constraint code path: when a certificate contains multiple full email-address constraints that share a common local part (the part before the ‘@’) but different domains (the part after the ‘@’), crypto/x509 was failing to enforce all constraints and only considered the last constraint seen. That means an excluded or not-permitted email address could escape enforcement if an earlier constraint was silently ignored. (go.dev)
This is a logic bug rather than, say, a memory-safety vulnerability or panic-on-malformed-input issue. It’s rated as an improper certificate validation weakness (CWE-295) because failing to apply name constraints correctly weakens the guarantees that PKI policy is supposed to provide. The vulnerability was reported by Jakub Ciolek and tracked in the Go project’s security issue record.
Technical anatomy: what exactly goes wrong
Where the bug lives
The fault appears inside crypto/x509’s email-constraint parsing and checking machinery — specifically the code paths that:- parse and normalise mailbox constraints,
- build internal "emailConstraints" structures (functions named like newEmailConstraints and parseMailboxes),
- and query those constraints during the chain‑level check (emailConstraints.query, checkConstraints, checkChainConstraints).
The failing case, in plain language
Imagine a CA certificate contains multiple email name constraints that look like:- alice@example.com (constraint #1)
- alice@corp.example (constraint #2)
In the buggy crypto/x509 path, the constraints are parsed and stored in a way that collapses or overwrites earlier entries that share the same local-part, leaving only the last constraint in the internal table. As a consequence, the check routine looks up constraints by local-part and only applies the final constraint value, ignoring previous entries that would have denied the leaf address. That single-step logic error produces a gap in enforcement. (go.dev)
Why the post-chain check matters
Name-constraint verification runs after the library has built candidate chains to trusted roots. Because library behavior only affects chains that ultimately end in a root trusted by the verifier, exploitation requires a CA trusted by the verifier to issue a cert that contains the relevant (malformed-for-policy) constraints or for an attacker to coerce a trusted CA into issuing such a cert. In practical terms, this restricts exploitation scenarios compared to a fully remote attack that required no trusted CA involvement — but it does not eliminate the attack surface. Internal PKI, misissued subordinate CAs, or a compromised CA are plausible avenues to abuse the bug. (go.dev)Who’s affected
- The issue is specific to the Go standard library's crypto/x509 implementation in the Go 1.26 series prior to the fix. The official vulnerability metadata marks versions earlier than go1.26.1 as affected. If you are compiling programs with a Go 1.26 toolchain that embeds the standard library, or you are using OS packages that distribute the Go runtime from that line, your binaries may carry the vulnerable behavior.
- Downstream packages and OS distributions that vendor or ship a copy of the Go standard library should be considered at risk until their maintainers publish patched builds. Several distributors and security trackers (Ubuntu, SUSE, Debian trackers, Tenable) have catalogued the CVE as relevant to packages derived from go1.26 and advise updating to patched builds.
- Not affected: earlier and later major releases outside of the impacted 1.26 window are not listed as vulnerable by the Go team’s advisory metadata; in particular, the problem was identified as being introduced or present in the 1.26 line, and the fix is packaged into go1.26.1. Always verify the exact versions shipped by your OS vendor.
Realistic attack scenarios and risk model
Threat scenarios that matter
- Internal PKI abuse: Organizations with private subordinate CAs often use email constraints to limit issuance to specific addresses and domains. If a subordinate certificate contains multiple email constraints that share local parts, the bug could let an improperly constrained leaf certificate be accepted by Go-based verification code, enabling an attacker to impersonate an email identity in systems that rely on X.509 email SANs for mapping or authorization.
- Misissuance or compromised CA: If a trusted CA mistakenly or maliciously issues name constraints that, combined with the bug, allow prohibited addresses, remote services that accept certificates for email identity could be tricked into mapping the wrong user. The attacker must have the ability to obtain a certificate chained to a trusted root — a nontrivial requirement, but not impossible in supply-chain or CA-compromise scenarios.
- Cross-application impact: Any application that relies on crypto/x509.Certificate.Verify for authorization decisions using email SANs is at risk — mail gateways doing S/MIME checks, internal certificate-to-account mapping in enterprise single-sign-on, and bespoke PKI-integrated workflows. This is especially true where verification is used directly as an authorization gate rather than just for transport-layer identity.
Why this is not an artery-wide remote RCE panic
This is not a remote code execution or memory corruption issue; it is a logical validation bug. That lowers the immediate global exploitability compared to a remotely triggerable crash or code-exec flaw. However, the severity in practice hinges on how widely the affected verification behavior is used to make authorization decisions, and on whether an attacker can obtain certificates chained to a trusted CA. Privileged environments and internal PKIs are high-value targets for abuse of this exact class of flaw.What was fixed and where to find the patch
The Go project remedied the bug in a change that adjusts how email constraints are parsed and queried so that multiple constraints with the same local part are individually recorded and applied. The official tracking points to a change list and to the Go issue that documents the problem; the CVE entry and the Go vulnerability tracker list the program routines involved and mark go1.26.1 as the safe release boundary.The Go project published security releases (including go1.26.1) that incorporate the fix; community security announcements and downstream advisories have catalogued the release. Security scanners and vendors (for example Tenable and several Linux distributions) are recommending upgrades to go1.26.1 or to vendor-patched packages. If you use pre-built Go packages from your operating system or a language/runtime distribution, check your vendor’s security tracker and apply the update they provide.
Practical mitigation and remediation guidance
If your environment uses Go or runs Go-built binaries, follow these steps as a prioritized checklist:- Inventory:
- Identify services and binaries built with Go 1.26. Focus on servers that perform X.509 certificate verification for email SANs or that use Certificate.Verify as part of identity/authorization logic.
- Check containers and base images; many container images include Go-built binaries or the Go toolchain. Use package manifests and build logs to confirm the toolchain version.
- Upgrade the toolchain and rebuild:
- Update development toolchains to Go 1.26.1 (or later stable releases) and rebuild all static/standalone binaries. This is the most reliable fix because crypto/x509 is part of the statically linked standard library that ships into compiled Go programs.
- If you use a distribution’s Go packages, apply the vendor patches or updated packages released by your OS vendor (Ubuntu, SUSE, Debian, etc.).
- Vendor or pin standard library (if rebuilding is not immediately possible):
- If you cannot rebuild immediately, consider adding compensating checks at the application layer where Certificate.Verify is used — e.g., manually re-check email constraints for SANs when you perform authorization decisions. This is hard and error-prone; prefer rebuilding.
- For CI/CD and supply-chain hygiene:
- Ensure CI images and build containers update their Go toolchain to the patched version.
- If you run reproducible builds, confirm the build recipe uses a patched SDK.
- Detection and monitoring:
- Audit logs for certificate acceptance patterns that are unusual — look for S/MIME or certificate-mapped authentications involving suspect domains or newly used subordinate CAs.
- Where possible, check certificate chains against your internal CA policies to ensure subordinate CAs do not include unexpected or multiple conflicting name constraints.
- Communicate with CAs:
- If you operate a CA, review how email name constraints are issued in subordinate certificates. Avoid multi-entry constraints that could interact poorly with parsers; and if you rely on strict enforcement by clients, coordinate policy expectations with downstream consumers.
Downstream and ecosystem considerations
- OS vendors and language packagers have publicly catalogued the CVE and started shipping patched packages. However, the Go ecosystem also includes many container images, serverless functions, and third-party binaries that may be built once and widely distributed. Effective remediation therefore requires tracking built artifacts as well as package managers.
- Public cloud or appliance vendors that ship precompiled Go binaries must be monitored for vendor attestations. Historically, Microsoft and other large vendors publish product-level attestations about included open-source components; those attestations are product-scoped and should be read carefully — presence of a component in a product does not automatically mean every product instance is vulnerable, and absence of a published attestation is not proof of absence in other artifacts. Community threads around prior Go CVEs underscore this point: product attestations are helpful but not exhaustive.
- Applications that treat X.509 email SANs as authoritative identity tokens (for S/MIME, certificate-to-account mapping, or automatic mailbox-to-account provisioning) are the highest-risk class. If you are running such software, prioritize rebuilds and out-of-band verification for critical paths.
Strengths of the Go response — and the remaining risks
The Go project’s response demonstrates some best practices:- The issue was tracked in the public issue tracker (with private bug details where needed) and assigned a CVE through the normal coordinator process.
- A targeted fix was produced and included in a point release (go1.26.1), and the vulnerability metadata documents the affected functions and the fix boundary. Multiple distribution and security trackers have already catalogued the CVE and issued guidance. (go.dev)
- Rebuild requirement: Because Go compiles the standard library into static binaries, already-deployed artifacts remain vulnerable until rebuilt. Operators with long-lived binaries or appliances may find patching operationally nontrivial.
- Visibility gap: Not every vendor publishes clear, timely attestations of which product artifacts include a given Go standard-library version. That means organizations must maintain accurate software inventories to know where rebuilds are required. Prior community discussions about vendor attestations illustrate how product-scoped notices can create a false sense of completeness.
- PKI complexity: The vulnerability’s real-world exploitability depends on whether a trusted CA will issue a certificate with the right combination of constraints or whether an attacker can coerce such issuance. Those threat scenarios are higher-impact and realistic for enterprise/internal PKI environments, where subordinate CAs and automated issuance systems exist.
Audit checklist for security teams (quick reference)
- Locate all Go-built artifacts in your estate and record their Go toolchain version (focus on 1.26).
- Prioritize rebuilds for services that:
- Use X.509 email SANs for identity mapping, and
- Rely on Certificate.Verify for policy/authorization decisions.
- Apply vendor patches for OS-packaged Go runtime where applicable, but plan to rebuild and redeploy application binaries.
- Add log alerts for unusual certificate acceptance patterns or for certificates signed by subordinate CAs that include unexpected name constraints.
- Engage internal CA operators to confirm subordinate issuance policies and to avoid multi-entry email constraints that might interact poorly with client parsers.
- If immediate rebuilds are impossible, implement compensating application-level checks with caution and plan a roadmap to full remediation.
Final assessment
CVE-2026-27137 is a high-quality example of a correctness bug that matters because of where cryptographic checks are used: not for low-level transport safety, but as gates in authorization and identity flows. The code-level error — conflating constraints that share a local-part — is elegant in its subtlety and consequential in its practical impact for enterprise PKI and certificate-based identity.The fix is straightforward: upgrade to go1.26.1 (or apply the patched distro packages) and rebuild Go-built artifacts. The harder work is operational: discovering every binary that needs rebuilding, verifying vendor-supplied images, and remediating systems that implicitly trust certificates for authorization. Organizations that use certificate-based email identity or operate internal CAs should prioritize this CVE accordingly.
If you run Go-built services, treat this as a rebuild-and-deploy task with high priority for all systems that use certificate-based email SAN authorization. The vulnerability’s constraints reduce the immediacy of mass exploitation, but its ability to silently undermine name-constraint enforcement makes it a practical concern for PKI-reliant environments. (go.dev)
Source: MSRC Security Update Guide - Microsoft Security Response Center