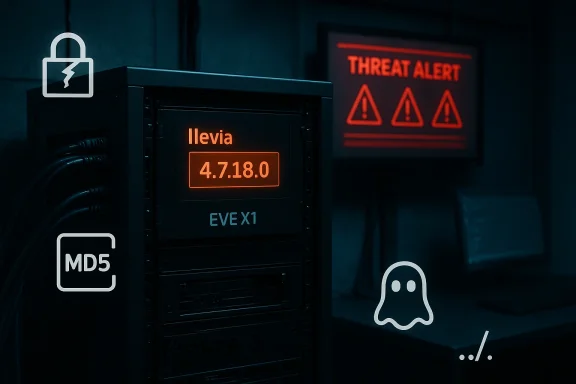
The Ilevia EVE X1 Server family has been the subject of a coordinated advisory that lists multiple high‑severity vulnerabilities in firmware versions up to and including 4.7.18.0. These flaws—ranging from pre‑auth file disclosure and path traversal to unauthenticated OS command injection, insecure password hashing, and reflected XSS—create a realistic, high‑impact attack surface for adversaries with network access to affected devices. Public vulnerability records and independent advisories confirm proof‑of‑concept material exists for several issues, and defenders should treat exposed EVE X1 endpoints as urgent priorities for containment, detection, and remediation.
Background
Ilevia Srl.’s EVE X1 Server is an embedded platform commonly used in industrial and building automation contexts. The vendor’s firmware branch identified in multiple advisories—referred to as 4.7.18.0 (sometimes shown as 4.7.18.0.eden)—is the version cutoff for a cluster of reported vulnerabilities. The researcher credited for discovery is Gjoko Krstic of Zero Science Lab; independent aggregators (VulnCheck and others) and national vulnerability databases have published CVE records and technical summaries for the issues.The advisory bundle names a set of CVEs that map to classic web/embedded weaknesses:
- Path traversal (absolute and relative) enabling arbitrary file reads.
- OS command injection in login/update endpoints that accept unsanitized input, including pre‑authentication command injection vectors.
- Insecure hashing/storage of credentials (MD5, unsalted), increasing the impact of any credentials disclosure.
- Cross‑site scripting (reflected XSS) in web UI components.
- Log and informatses that can reveal system configuration and secrets.
What the vulnerabilities actually allow attackers to do
Pre‑auth file disclosure & path traversal (high confidentiality impact)
Several CVEs describe pre‑authentication file read capabilities via endpoints that accept file‑path parameters or database logging parameters. In practical terms this means an unauthenticated remote actor can request arbitrary files (for example configuration files, credential stores, or system logs) if the web endpoint canonicalizes file paths incorrectly or fails to restrict reads to a safe directory. Public tracking pages and NVD summaries list these as high‑impact information disclosure issues.Why this matters: if an attacker can retrieve configuration blobs or password databases, they can harvest credentials, secrets, and device internals that materially lower the bar for full system takeover.
Unauthenticated OS command injection (remote code execution)
At least one KPI in the advisory set is an unauthenticated command injection that accepts attacker‑controlled input and forwards it into a shell or command context (for example, a 'passwd' POST parameter in a login script). Where a device executes shell commands on user input without proper sanitization or safe parameterization, the result is remote code execution (RCE) at the privileges of the affected service. Public CVE records and vendor/third‑party advisories indicate the injection is network‑accessible and low complexity to abuse.Why this matters: remote unauthenticated command execution is one of the most dangerous failure modes for embedded devices—attackers can drop backdoors, pivot, manipulate telemetry, or use the device as a foothold into management and corporate networks.
Insecure hashing and sensitive information leakage
The product stores password material using MD5 with no per‑password salt in at least one documented advisory. MD5 is a fast, broken hash that enables rapid offline cracking with modern GPU‑assisted tooling. When combined with file disclosure or config file leaks, hashed credentials quickly become convertible into real account access.Why this matters: credential recovery increases the window of exploitation and may allow privileged (authenticated) actions even if the initial vector was read‑only.
Cross‑site scripting (XSS) and log injection
Reflected XSS in the web GUI and improper neutralization of log content can be abused by attackers to target operators who use the device’s web console. An attacker can weaponize XSS to steal session tokens, induce an operator to perform privileged actions, or deliver payloads that alter device state. Similarly, log injection that places attacker data into monitoring artifacts can obfuscate activity or manipulate forensic evidence.Why this matters: XSS and log manipulation are lower‑barrier attack paths that become dangerous in combination with device administrative workflows and operator consoles—particularly when those consoles run on Windows engineering workstations and are used to manage many OT endpoints.
Cross‑validation: what independent sources say
At least two independent vulnerability aggregators and the National Vulnerability Database (NVD) maintain entries for the most critical CVEs in this cluster. NVD lists a detailed description for the file disclosure issue and the unauthenticated command injection; VulnCheck and other trackers provide corroborating technical summaries and note public proofs‑of‑concept for several CVEs. Multiple sources credit the same researcher (Gjoko Krstic / Zero Science Lab), strengthening confidence in the technical fidelity of the reports.Caveats: a small number of public trackers carry vendor statements that the vendor “declined to service” or recommended that customers not expose administrative ports to the Internet. Those statements originate from third‑party aggregators and should be verified against vendor advisories or official CISA/National CERT postings for accuracy before taking irreversible action (like device replacement). Still, the presence of public PoCsical descriptions across independent trackers is enough to treat these flaws as actionable and urgent.
Operational risk for Windows‑centric environments
Industrial and building automation devices do not sit in a vacuum. They are often managed from Windows‑based engineering consoles, jump hosts, or domain‑joined workstations. A compromised EVE X1 Server can be used to:- Harvest credentials stored in configuration files that grant access to supervisory Windows systems.
- Stage lateral movement from OT to IT, leveraging weak segmentation to reach Windows server infrastructure.
- Use the appliance as a command-and-control relay or dropper for payloads that target Windows endpoints (for example, deploying a Windows‑compatible backdoor on management hosts).
Immediate actions (first 24–72 hours)
If you manage or operate EVE X1 Servers, apply this prioritized checklist immediately:- Inventory and isolate
- Identify every EVE X1 instance and confirm firmware version. Prioritize any running version ≤ 4.7.18.0.
- Remove direct Internet exposure. Block external access to device bly port 8080 where documented).
- Network containment
- Place affected devices behind a firewall and restrict access to a small set of trusted management hosts (whitelist IPs).
- Move devices to a segmented OT network or VLAN that limits east‑west and north‑south traffic.
- Temporary access controls
- Require access through hardened jump hosts with MFA. Disable direct RDP/SMB exposure from the public Internet to engineering consoles that can reach OT.
- Monitor and preserve evidence
- Increase logging and forward OT logs to a secure SIEM. Preserve existing device logs and configuration snapshots for forensic review.
- Communicate and escalate
- Notify vendor support, internal incident response, and national CERT/CISA if you observe suspicious activity. Follow established reporting guidelines when sharing indicators.
Medium‑tdays)
- Patch and verify: apply vendor firmware updates if Ilevia publishes fixed releases. If an official patch exists, validate checksums and test in a staging environment before wide deployment. Where a vendor patch is not available, implement compensating network controls and monitor for public proof‑of‑concept exploitation attempts.
- Rotate credentials: assume any exposed credential material (including MD5 hashes) may be cracked—rotate service and operator passwords, and replace keys where feasible. Move authentication to centralized or vaulting solutions for better rotation and auditing.
- Harden management hosts: enforce full patching, EDR/AV controls, application whitelisting, and least privilege on Windows jump boxes that connect to OT devices. Ensure jump hosts use dedicated accounts and are not used for general browsing or email.
Long‑term hardening (30+ days)
- Remove insecure cryptography: press the vendor or roadmap to replace insecure hashing (MD5) with modern, salted, memory‑hard password storage (e.g., Argon2, bcrypt, or PBKDF2 with appropriate parameters).
- Firmware supply chain and SBOM: require supplier SBOMs and secure update mechanisms for embedded devices to reduce the window for unknown vulnerable dependencies.
- Network design: implement zero‑trust principles between IT and OT zones, forcing mutual authentication and micro‑segmentation for maintenance access. Deploy protocol-aware IDS/IPS for OT protocols and proactive anom
Detection and hunt guidance
Use the following detection priorities to hunt for compromise or attempted abuse:- Web server logs: search for requests containing suspicious filename parameters (../ sequences) or POST requests referencing admin endpoints such as login, get_file_content.php, and other AJAX endpoints. Flag unusual 200 responses that return binary or sensitive file contents.
- Command injection indicators: monitor for unexpected process creation or shell execution initiated by the web service user context on the device, or for outbound connections from the device to unfamiliar hosts.
- Credential abuse: look for logins using recovered or guessed credentials, authentication anomalies on jump hosts, or sudden privilege escalations originating from OT‑adjacent consoles.
- Operator interaction: watch for unexpected browser-based accesses to the device GUI that include long or encoded query strings—these could be XSS triggers.
- Windows SOC correlation: correlate Windows event logs for credential use or lateral movement with OT telemetry (e.g., a Windows engineering workstation connecting to multiple EVE X1 devices outside normal working hours).
Vendor response, disclosure timeline, and verification notes
Independent trackers and the NVD record the CVEs and technical details; multiple third‑party advisories note public proofs‑of‑concept were published in mid‑October 2025. Some aggregators report that Ilevia has declined to service certain issues and recommended customers avoid exposing port 8080 to the Internet. These statements derive from third‑party advisories and should be validated directly against any official Ilevia or national CERT advisory before relying on them as a long‑term remediation strategy. The presence of public PoCs, however, is itself sufficient cause for urgent containment.Practical verification steps:
- Confirm firmware version on every EVE X1 unit; devices with versions ≤ 4.7.18.0 are in scope.
- If Ilevia releases a fixed firmware, install it in a test environment and run non‑destructive probe tests against known vulnerable endpoints to confirm behavior changes. Where possible, source PoC input (from trusted researchers) should be run only in air‑gapped testing environments.
Practical checklist for Windows administrators and SOC teams
- Immediately: Identify all Windows hosts that can reach EVE X1 devices; enforce MFA and harden jump hosts.
- Within 48 hours: Block management ports from the Internet; apply ACLs and network isolation.
- Within 7 days: Rotate credentials that were reachable from affected devices and place affected devices into monitored maintenance networks.
- Within 30 days: Complete patch testing (if vendor patches are available) and deploy updates with checksum verification.
- Ongoing: Integrate OT telemetry into the SOC, and treat ICS advisories as enterprise incidents with Windows‑side consequences (not as isolated OT problems).
Final assessment and conclusion
The Ilevia EVE X1 Server advisory represents a textbook ICS/embedded device crisis: high‑impact vulnerabilities, public proof‑of‑concept material, and a vendor footprint in critical manufacturing and industrial deployments. The most consequential exposures are the unauthenticated OS command injection and the pre‑auth file disclosure/path traversal issues—together they enable rapid escalation from recon to full compromise when the device is reachable by adversaries.For defenders, the path forward is clear and urgent:
- Contain exposed devices now—remove Internet access and restrict management to hardened, authenticated jump hosts.
- Assume leaked credential material can be cracked—rotate secrets and enforce stronger hashing and centralized credential management where possible.
- Treat OT and Windows environments as a single risk domain—control system compromises can and do lead to Windows‑side intrusions.
- Verify vendor statements and patches, and coordinate with national authorities when appropriate.
Source: CISA Ilevia EVE X1 Server | CISA