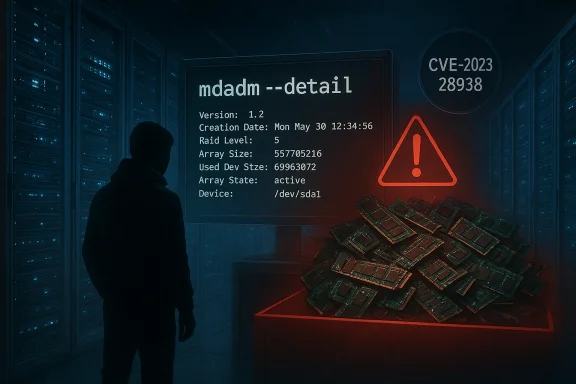
Intel’s security advisory last year quietly tied a confusingly named component to a simple but real availability risk: an uncontrolled resource consumption bug in certain Intel® SSD Tools distributions — specifically those shipping an upstream mdadm build older than mdadm-4.2-rc2 — can allow a privileged local user to cause a denial‑of‑service (DoS) by exhausting memory or other process resources. Intel’s advisory and several vulnerability databases record the issue as CVE‑2023‑28938 and recommend upgrading to mdadm‑4.2‑rc2 or later to remove exposure. (intel.com) (nvd.nist.gov)
The problem is straightforward in principle: a component used in Intel’s SSD Tools package — which bundles utilities, tools and wrappers around common storage management code such as the Linux md (multiple device) tooling — contained code paths that failed to bound or free certain resource allocations. In practice that manifested as a memory leak or other resource exhaustion triggered by local execution of mdadm operations (notably, mdadm --detail in distribution reports). Because the affected code path runs when a privileged user or process queries or manipulates RAID/SSD state, a user with sufficient privileges could repeatedly trigger the leak until the host’s memory or other limits are consumed, producing sustained or persistent unavailability. (intel.com)
Two important contextual facts shape the real-world risk assessment:
Actionable next steps for administrators: inventory your systems for mdadm and Intel SSD Tools packages, prioritize patching or vendor updates where mdadm < 4.2‑rc2 is present, and — until patched — restrict who and what can run storage management commands. Combine the patch with defensive measures (resource bounds, monitoring, privilege audits) to reduce the blast radius of similar resource‑consumption bugs in future. For systems where Intel or a third‑party vendor supplies an integrated toolset, coordinate directly with the vendor to ensure you apply the correct, tested package for your product.
Finally, remember this is a remediated issue: upstream and distribution fixes exist. Use your environment’s change control and patching processes to validate and deploy the appropriate package versions, and monitor for any anomalous mdadm usage during the rollout. (intel.com)
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
The problem is straightforward in principle: a component used in Intel’s SSD Tools package — which bundles utilities, tools and wrappers around common storage management code such as the Linux md (multiple device) tooling — contained code paths that failed to bound or free certain resource allocations. In practice that manifested as a memory leak or other resource exhaustion triggered by local execution of mdadm operations (notably, mdadm --detail in distribution reports). Because the affected code path runs when a privileged user or process queries or manipulates RAID/SSD state, a user with sufficient privileges could repeatedly trigger the leak until the host’s memory or other limits are consumed, producing sustained or persistent unavailability. (intel.com)Two important contextual facts shape the real-world risk assessment:
- The flaw is local and requires high privileges to trigger in most documented cases; it is not a remote, unauthenticated network exploit.
- The impact is availability‑focused (CWE‑400: uncontrolled resource consumption). It does not directly yield confidentiality or integrity compromises in documented analyses, although availability loss in storage subsystems can produce secondary operational consequences. (intel.com)
What exactly is vulnerable?
Affected components and versions
- The vulnerability is present in Intel® SSD Tools software packages that include a version of mdadm earlier than 4.2‑rc2. Intel’s advisory calls out “Intel® SSD Tools software before version mdadm‑4.2‑rc2” as the affected product set and recommends upgrading the tools to include mdadm‑4.2‑rc2 or later. (intel.com)
- Distribution-level trackers (Debian security tracker and other Linux packaging advisories) list the same mdadm upstream cutoff: vulnerable upstream mdadm versions prior to 4.2‑rc2, with fixes shipped into distribution packages (for example, Debian’s Bookworm and later include the patched mdadm release).
How the issue is triggered (technical summary)
Available public descriptions and distribution notes indicate the issue is an uncontrolled resource consumption bug, commonly manifested as a memory leak, that occurs when mdadm performs certain metadata or detail queries (documented examples include mdadm --detail). The offending code path allocates resources that are not reliably freed on every control-flow exit; invoked repeatedly, the allocation accumulates until process or system memory is exhausted. The practical effect is that an attacker with local privileged access can cause an mdadm process (or the system) to consume excessive memory and either crash services, force an OOM (out‑of‑memory) condition, or otherwise prevent normal operation.Why the vendor lists “mdadm” in an Intel advisory
Intel’s SSD Tools bundles and redistributes certain storage management utilities and may ship an mdadm build as part of its toolchain for SSD/RAID management. In this case Intel’s internal review found the vulnerability in the bundled tooling and coordinated disclosure with upstream and downstream maintainers, resulting in the recommendation to upgrade the mdadm component. This kind of cross‑project packaging is common for vendor toolsets that provide storage‑management functionality. (intel.com)Cross‑checking the facts (what we verified)
I cross‑checked vendor and independent sources to ensure the technical summary and remediation guidance are accurate:- Intel’s official advisory (INTEL‑SA‑00690) explains both CVE‑2023‑28736 (a buffer overflow) and CVE‑2023‑28938 (uncontrolled resource consumption) in the same advisory and explicitly names mdadm‑4.2‑rc2 as the fix point. That advisory also lists the recommended remediation (update to mdadm‑4.2‑rc2 or later). (intel.com)
- The National Vulnerability Database (NVD) entry for CVE‑2023‑28938 contains the same descriptive text and records the availability impact, and provides the consolidated canonical CVE description used by many organizations. Differences in scoring across tracks were noted; NVD’s entry is a primary record for the vulnerability’s canonical description. (nvd.nist.gov)
- Distribution security trackers (Debian’s security tracker) record the same vulnerability and show the fixed versions shipped in Debian Bookworm (mdadm 4.2~rc2‑2 packaged and subsequent distribution updates). Those trackers also capture the practical detail that the leak appears tied to one‑shot operations such as mdadm --detail, which reduces operational severity in most server setups where the command is run interactively or by trusted scripts.
- Several security aggregators and scanning services (Snyk, Wiz and others) list the vulnerability as CWE‑400 and describe the potential for DoS via resource exhaustion, reinforcing the NVD/Intel descriptions.
Operational impact — realistic scenarios and risk model
Where this is high‑risk
- Multi‑tenant servers, hosting nodes, or managed‑service hosts where multiple users/operators have local privileged accounts. In those environments an attacker who gains elevated, local privileges could weaponize the leak to affect other tenants or services.
- Orchestration hosts with automated tooling that repeatedly invokes mdadm queries from privileged contexts; an automation loop could accidentally exacerbate the problem or allow a compromised automation token to repeatedly trigger the leak.
- Edge or appliance systems that run vendor‑provided Intel SSD Tools continuously as a monitoring agent: if the tool routinely runs the vulnerable mdadm path on a schedule, the environment could accumulate resource consumption over time.
Where this is low‑risk
- Single‑user desktops or workstations where only trusted administrators can run mdadm and the tool is invoked infrequently; many distributions note the practical impact is limited because the vulnerable path is triggered by a one‑shot operation (for example, mdadm --detail), and the security tracker describes the impact as “negligible” for interactive use cases.
Attack complexity and prerequisites
- Privileges required: High (local privileged user). This is not a remote, unauthenticated bug.
- Complexity: Low to moderate — the vulnerability generally requires repeated or programmatic triggering to reach a system‑level denial of service in typical systems.
- Exploit maturity: No widely reported remote exploits; this is an availability-focused local bug rather than a code‑execution vector. Public descriptions show remediation upstream and in major distributions. (intel.com)
Patching and mitigation — concrete steps for sysadmins
If you manage systems that include Intel SSD Tools or that ship mdadm from upstream, follow these prioritized steps immediately:- Identify affected systems
- Run mdadm --version or query your package manager:
- Debian/Ubuntu: dpkg -l mdadm
- RHEL/CentOS/Fedora: rpm -q mdadm
- For vendor bundles, identify whether your vendor or appliance shipped a bundled Intel SSD Tools package that includes mdadm. If you’re unsure, treat the system as potentially affected until verified.
- Apply the vendor‑recommended update
- Upgrade the mdadm component to mdadm‑4.2‑rc2 or later as recommended by Intel. For Debian users, the patched package appears in Bookworm and later; for other distributions, pick the distribution’s security update that includes the upstream fix. (intel.com)
- If immediate patching is not possible, reduce exposure
- Restrict local privileged access: limit who can invoke mdadm‑level operations, and audit sudoers and automation roles.
- Disable or sandbox any automated processes that run mdadm queries on a schedule until patched.
- Use OS-level resource controls (systemd slices, cgroups) to bound memory consumption for the relevant process to reduce the likelihood of system-wide OOM.
- Monitor for signs of exploitation
- Look for repeated mdadm invocations in logs, spikes in memory usage attributed to mdadm processes, and OOM killer activity. Search syslogs and audit trails for frequent calls to storage‑management tools.
- Add alerting for anomalous process memory growth on storage management agents.
- Validate the fix
- After patching, re-run any failing or previously faulting mdadm commands and confirm that memory use does not steadily increase over repeated invocations.
- Run your regression tests for storage tooling and monitor for service stability before returning systems to production workflows.
- Document and communicate
- Inform change control and operations teams of the patch windows and mitigation steps.
- Where appliances or vendor bundles are in play, coordinate with the appliance vendor for formal patches if the vendor supplies their own integrated packages.
Detection, forensics and indicators
- The clearest indicator is a process (or processes) showing steady, unbounded memory growth after repeated mdadm actions; in many cases this was observed when running storage detail or metadata queries.
- Audit trails showing repeated execution of mdadm --detail or similar commands by a single account are worth investigating.
- System-level symptoms include unusual OOM killer invocations, system performance drops, and storage‑related service failures that correlate with elevated mdadm activity.
- For forensic retention, preserve:
- The mdadm binary and its exact version.
- System logs around the time of resource spikes.
- Memory dumps if systems crashed and that is permissible in your operational and regulatory context.
Why the scoring differs across sources (a short explainer)
You’ll see small differences in CVSS scoring across Intel, NVD and third‑party aggregators. That happens because scoring requires assumptions about attacker privileges, frequency of triggering, whether the condition is sustained or one‑shot, and the expected ability to cause system‑wide disruption.- Intel’s advisory applies a vendor risk posture and lists CVSS 3.1 = 3.4 (Low) for CVE‑2023‑28938, reflecting the requirement for local privileged access and the one‑shot nature in many configurations. (intel.com)
- The NVD and some third‑party trackers sometimes place higher weight on the availability impact in constrained or multi‑tenant systems, resulting in medium severity assessments on some databases. These differences are not contradictory; they reflect different operational assumptions about exposure and impact. (nvd.nist.gov)
Deeper technical notes and the upstream fix
- The upstream fix that closed CVE‑2023‑28938 was incorporated into mdadm upstream around the 4.2‑rc2 release. Distribution trackers reference the upstream commit used to remediate the leak in mdadm; distributions have repackaged that fix and shipped it in security updates. Administrators should rely on the distribution’s security packages rather than attempting to patch in place unless they are comfortable building and testing upstream code.
- For environments that use vendor provided Intel SSD Tools bundles (for instance appliances or OEM packages), confirm whether your vendor has published a vendor‑specific update or an advisory aligning with Intel’s advisory. Vendors may repackage upstream fixes differently, and the safest path is the vendor‑issued update for those appliances.
Practical hardening beyond the patch
Patching fixes the specific bug — but uncontrolled resource consumption vulnerabilities are a recurring class. Consider these long‑term hardening measures:- Enforce least privilege for storage management commands. If only a small set of administrators need to run mdadm, restrict sudoers entries to those users and log all such invocations.
- Use cgroups/systemd to cap memory and CPU for third‑party tools and agent processes. Even if a process leaks, bounding its resources contains the blast radius.
- Add behavioral monitoring for anomalous command frequency. A sudden spike in mdadm queries from a single account should trigger an investigation.
- For multi‑tenant or automated environments, implement service account separation and strictly control which automation roles can execute potentially dangerous management commands.
Strengths and gaps in the vendor response
What Intel did well:- Intel identified the issues internally and published a consolidated advisory (INTEL‑SA‑00690) that lists CVE‑2023‑28736 and CVE‑2023‑28938 together and points administrators to the upstream mdadm fix point. The advisory’s recommended fix — upgrade to mdadm‑4.2‑rc2 or later — is clear. (intel.com)
- Vendor advisories that reference upstream fixes can create ambiguity — the advisory recommends mdadm‑4.2‑rc2, but many administrators will need to reconcile that with their distribution packages and vendor appliance bundles. Always verify whether the vendor or distribution provides a repackaged patch and test updates in a staging environment before broad rollout. Debian’s tracker, for example, shows the fixed package versions for Debian Bookworm and newer.
- The vulnerability’s requirement for local privileged access lowers remote exploitation risk, but it remains a serious operational problem in environments where privilege separation is lax. Automated orchestration systems, container hosts, or VM images that run vendor tools with elevated privileges can amplify risk.
- Some vulnerability trackers score availability impacts differently; operations teams must map those scores into their own risk model rather than relying on the headline number alone.
Detection checklist for immediate use
- Inventory systems for Intel SSD Tools or mdadm versions < 4.2‑rc2.
- Search logs for repeated mdadm invocations and any correlation with memory spikes or OOM messages.
- Configure an alert: any mdadm process that grows beyond a preconfigured memory threshold should generate an automatic incident.
- For providers: ensure tenant isolation and privileged role audits are current and enforced.
- Confirm patch deployment in test/staging prior to production rollout and verify the leak no longer reproduces after applying upstream or vendor fixes.
Conclusion — what WindowsForum readers should take away
CVE‑2023‑28938 is an availability‑focused, local privilege‑dependent bug embedded in a vendor bundling of the mdadm tool. The fix is available upstream (mdadm‑4.2‑rc2) and in mainstream distributions; Intel published an advisory recommending the component update. While the requirement for privileged, local access limits the immediate remote risk, the vulnerability can be exploited or accidentally triggered in multi‑tenant, automated, or appliance contexts — and when abused it can cause sustained denial of service by exhausting host resources. (intel.com)Actionable next steps for administrators: inventory your systems for mdadm and Intel SSD Tools packages, prioritize patching or vendor updates where mdadm < 4.2‑rc2 is present, and — until patched — restrict who and what can run storage management commands. Combine the patch with defensive measures (resource bounds, monitoring, privilege audits) to reduce the blast radius of similar resource‑consumption bugs in future. For systems where Intel or a third‑party vendor supplies an integrated toolset, coordinate directly with the vendor to ensure you apply the correct, tested package for your product.
Finally, remember this is a remediated issue: upstream and distribution fixes exist. Use your environment’s change control and patching processes to validate and deploy the appropriate package versions, and monitor for any anomalous mdadm usage during the rollout. (intel.com)
Source: MSRC Security Update Guide - Microsoft Security Response Center