Microsoft’s short public attestation that “Azure Linux includes this open‑source library and is therefore potentially affected” is accurate — but it is an inventory statement for one product, not a blanket claim that no other Microsoft product could contain the same vulnerable Linux kernel code. //archive.ph/2025.12.07-214203/https%3A/msrc.microsoft.com/update-guide/vulnerability/CVE-2025-39762)
On July 4, 2025 the Linux kernel community and downstream trackers recorded a bug described as “smb: client: add NULL check in automount_fullpath” and assigned CVE‑2025‑38208. The defect is a missing NULL pointer check in the SMB client code path (automount_fullpath) that can produce a NULL pointer dereference under particular execution conditions, i.e., a local robustness/availability vulnerability that can lead to kernel OOPS or crash. Upstream maintainers merged a small defensive fix to add the missing check, and the change was backported or packaged by multiple distributors.
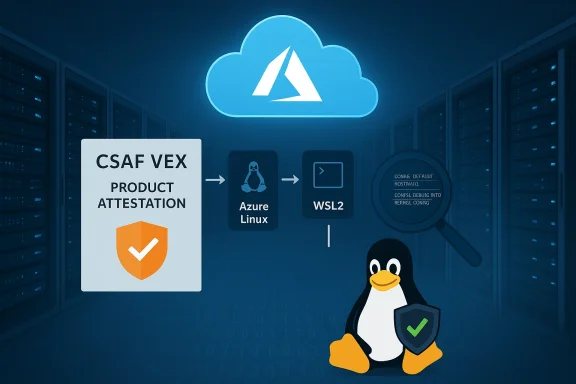
Microsoft’s MSRC entry for this CVE (the short FAQ item many administrators quote) explicitly states that Azure Linux includes the open‑source component and is therefore potentially affected, and then adds that Microsoft began publishing machine‑readable CSAF/VEX attestations in October 2025 and will update CVEuld additional Microsoft products be found to ship the affected component. That wording is important because it reflects a product‑by‑product inventory approach, not an exhaustive statement about Microsoft’s entire product portfolio.
This article explains what that MSRC phrasing means in practical terms, summarizes the technical nature and impact of CVE‑2025‑38208, and — critically for defenders — shows how to decide which Microsoft artifacts you must verify and patch. The guidance is deliberately operational: where Microsoft’s attestation leaves an “unknown” we show how to close that gap quickly and with high confidence.
However, this phrasing should not be read as meaning Azure Linux is the only Microsoft product that could include the affected kernel code. Microsoft’s inventory and CSAF/VEX rollout are phased and product‑by‑product; absence of a product name onsence of attestation**, not proof of absence of the vulnerable code. Other Microsoft artifacts may ship kernels built from upstream commits that predate the fix and may therefore include the same code unless explicitly attested as Not Affected or patched.
If you manage Microsoft‑provided images, Azure VMs, WSL endpoints, or mixed estates, follow this prioritized checklist. Treat Azure Linux as patch‑first; then apply artifact‑level discovery for everything else.
However, do not read that sentence as a declaration that no other Microsoft product could be affected. Any Microsoft artifact that ships or runs a Linux kernel build compiled from the vulnerable commit range and with the SMB client code enabled is potentially a carrier until verified. Prioritize patching Azure Linux images first, then inventory and verify WSL2 kernels, Azure VM/Marketplace images, AKS node images and any other Microsoft‑distributed artifacts you operate. Use vendor VEX/CSAF feeds as they arrive, but complement them with artifact‑level checks, kernel config inspections, and package metadata verification.
If you want a compact, runnable checklist or a short script that automates the kernel checks described above across a fleet (WSL endpoints, Azure VMs, AKS nodes), provide me the scope (cloud-only, enterprise endpoints, or both) and I will produce that runbook ready for your patching and remediation teams.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
On July 4, 2025 the Linux kernel community and downstream trackers recorded a bug described as “smb: client: add NULL check in automount_fullpath” and assigned CVE‑2025‑38208. The defect is a missing NULL pointer check in the SMB client code path (automount_fullpath) that can produce a NULL pointer dereference under particular execution conditions, i.e., a local robustness/availability vulnerability that can lead to kernel OOPS or crash. Upstream maintainers merged a small defensive fix to add the missing check, and the change was backported or packaged by multiple distributors.Microsoft’s MSRC entry for this CVE (the short FAQ item many administrators quote) explicitly states that Azure Linux includes the open‑source component and is therefore potentially affected, and then adds that Microsoft began publishing machine‑readable CSAF/VEX attestations in October 2025 and will update CVEuld additional Microsoft products be found to ship the affected component. That wording is important because it reflects a product‑by‑product inventory approach, not an exhaustive statement about Microsoft’s entire product portfolio.
This article explains what that MSRC phrasing means in practical terms, summarizes the technical nature and impact of CVE‑2025‑38208, and — critically for defenders — shows how to decide which Microsoft artifacts you must verify and patch. The guidance is deliberately operational: where Microsoft’s attestation leaves an “unknown” we show how to close that gap quickly and with high confidence.
What the CVE is — technical summary
The bug in plain terms
- The vulnerability exists in the Linux kernel SMB client code path: the function that builds an automount full path (automount_fullpath) used by the kernel SMB client does not always check for NULL in one control path.
- That missing check can allow a NULL pointer to be dereferenced under specific conditions, which typically causes a kernel OOPS or panic (availability impact). The issue is not a remote, unauthenticated RCE; it is a local robustness defect that can be triggered by someone with local access or by code executing in the guest that exercises the SMB client path.
Downstream impact and fixes
- Upstream kernel maintainers produced a minimal patch to add the missing NULL check; the fix landed in the kernel stable trees and was backported by several vendors and distributions.
- Multiple vendors and cloud Linux images cataloged the CVE and published fixed package versions or advisories (Debian/Ubuntu/SUSE/Amazon Linux etc.). If you run any Linux kernel build that predates those fixes and whose configuration exposes the SMB client code, you should treat that host as potentially vulnerable.
What Microsoft’s wording actually means
Product-level attestation, not global exclusion
When MSRC says “Azure Linux includes this open‑source library and is therefore potentially affected” it is declaring that Microsoft has completed inventory work for the Azure Linux product family and found the upstream kernel component that maps to the CVE. That is an authoritative, actuatch or update the Azure Linux kernel packages according to Microsoft’s guidance.However, this phrasing should not be read as meaning Azure Linux is the only Microsoft product that could include the affected kernel code. Microsoft’s inventory and CSAF/VEX rollout are phased and product‑by‑product; absence of a product name onsence of attestation**, not proof of absence of the vulnerable code. Other Microsoft artifacts may ship kernels built from upstream commits that predate the fix and may therefore include the same code unless explicitly attested as Not Affected or patched.
Why Microsoft named Azure Linux first
Azure Linux is Microsoft’s cloud‑focused, Microsoft‑maintained Linux image lineage. It is a natural starting point for Microsoft’s VEX/CSAF rollout because Azure customers consume Microsoft‑maintained kernels and images directly. Attesting Azuiate, high‑value remediation guidance for a large user base. But the attestation does not replace per‑artifact verification for other Microsoft products or images.Is Azure Linux the only Microsoft product that could be affected?
Short answer: No — not necessarily. Azure Linux is the only Microsoft product Microsoft has publicly attested so far for this particular CVE, and that attestation makes Azure Linux a confirmed remediation priority. But technically, any Microsoft product or service that ships, distributes, or runs a Linux kernel build (or supplies virtual machine imarnel) could include the vulnerable source code until inventory and attestations show otherwise.Microsoft artifacts you should consider and why
- Azure Linux images / linux‑azure kernels — Confirmed attestation; highest priority for remediation. Azurely called out by MSRC.system for Linux) kernel builds** — Microsoft ships and maintains a WSL2 kernel binary and source tree; depending on the kernel version and build configuration the WSL2 kernel could include the same code. WSL kernels are built beam trees and can differ by configuration. Do not assume WSL is safe without verification.
- Azure VM marketplace images and curated kernels — Microsoft publishes many Marketplace imaed by Microsoft and include Microsoft‑tuned kernels. Those images are discrete artifacts and must be checked individually.
- AKS (Kubernetes) node images and managed node kernels — Node images that rely on Microsoft‑maintained kernels (or the Azure Linux lineage) may be carriers.
- Other Microsoft-supplied container base images and appliances — These typically rely on the host kernel, but any image that bundles a kernel or kernel modules for specialized ain the vulnerable code.
- Third-party images Microsoft distributes or supports — Some Marketplace images are third‑party — they may be updated by external vendors, and Microsoft’s Azure Linux attestation does not apply to them. Validate provider patches or assume unknown until verified.
Evidence / cross‑che on a single source, this analysis cross‑checked multiple independent trackers and vendor pages:
- Security trackers and distributors documented the technical fix (NULL check in automount_fullpath) and published advisories and package fixes (Rapid7, AWS ALAS, Wiz, Snyk/SUSE listings). These show the patch landed in ndors.
- Microsoft’s MSRC pages (and archived captures of those pages) show the standard FAQ wording making a product‑specific attestation for Azure Linux and announcing the CSAF/VEX rollout beginning October 2025. That wording appears consistently across multiple MSRC CVE pages.
- Community analysis and forurum threads and other independent writeups) explain the operational meaning of Microsoft’s attestation: Azure Linux = confirmed carrier; other Microsoft artifacts = unverified until attested. Those independent writeups converge on the same practical interpretation.
If you manage Microsoft‑provided images, Azure VMs, WSL endpoints, or mixed estates, follow this prioritized checklist. Treat Azure Linux as patch‑first; then apply artifact‑level discovery for everything else.
1) Immediate priority: Azure Linux (confirmed attested carrier)
- Identify Azure Linux hosts (inventory query, cloud tagging, CMDB).
- Apply Microsoft’s Azure Linux kernel updates as publi versions against MSRC / vendor advisories.
- Verify by checking kernel package changelog or installed kernel version maps to a fixed release (many distributors list fixed package numbers).
2) High priority: WSL2 endpoints in your environment
- If you allow WSL2 in your environmenrsion shipped with each WSL2 installation. On a WSL2 instance: uname -r
- Inspect the WSL2 kernel config if available (Microsoft publishes kernel config for WSL builds) or compare the kernel version to the fixed kernel ranges published by vendors. Do not assume the WSL2 kernel is unaffecre Linux was called out; WSL2 kernels are independently maintained and may include different upstream commits.
3) Medium priority: Azure VM images, AKS node images, Marketplace images
- Inventory which Marketplace or Azure VM images you run (image name, publisher, SKU).
- For Microsoft‑published images, request or check the SBOM/VEX attestation for that image; Microsoft is rolling CSAF/VEX out product‑by‑product and may publish attestations for additional images over time. If no attestation exists, treat the artifact as unverified.
- If feasible, boot a test instance and run:
- uname -a
- grep -E 'CONFIG_KSMBD|CONFIG_SMB|automount' /boot/config-$(uname -r) (or extract kernel config from the image)
- lsmod | grep -E 'smb|cifs|ksmbd' to see if related modules are present
- If the kernel shows presence of SMB client/server drivers a predates fixes, plan for patching or instance replacement.
4) Lower priority but necessary: container infra and appliance images
- Containers typically rely on the host kernel, so the main focus should be the host image. However, appliance images or marketplace appliances that bundle a kernel or kernel modules must be inspected similion commands (practical, low‑risk checks)
- Check running kernel and config:
- uname -a
- grep -E 'CONFIG_KSMBD|CONFIG_CIFS|CONFIG_SMB' /boot/config-$(uname -r) || zgrep -E 'CONFIG_KSMBD|CONFIG_CIFS|CONFIG_SMB' /proc/config.gz
- Look for modules:
- lsmod | egrep 'smb|cifs|ksmbd'
- modinfo ksmbd || true
- Inspect package metadata:
- On Debian/Ubuntu: dpkg -l | egrep 'linux-image|linux-azure'
- On RHEL/SUSE: rpm -qa | egrep 'kernel|azure'
- For WSL: use wsl --list --verbose on Windows host, then inspect the WSL instance’s uname -r and kernel config files.
Mitigations while you confirm and patch
- Uninstall or blacklist modules (temporary): If an image exposes SMB modules you do not need, consider removing or blacklisting them (e.g., echo "blacklist ksmbd" > /etc/modprobe.d/blacklist-ksmbd.conf) until you can patch. This is a stopgap only — kernelterm fix.
- Reduce local attack surface: Restrict shell access, containers or workload privileges that could exercise the SMB client code path.
- Isolate multi‑tenant workloads: For cloud hypervisors or multi‑tenant hosts, reduce untrusted workload co‑location until the host fleet is patched.
- Use tested vendor packages or kernel backports: Where vendor packages are available, prefer thoy‑picked patches. Backporting kernel fixes is nontrivial; use vendor guidance where possible.
- Monitor kernel logs: Watch for recurring OOPS/panic traces referencing automount_fullpath or SMB client stack traces; these indicate exploitation attempts or accidental triggers.
Supply‑chain and policy implications
- Treat vendor attestations (CSAF/VEX) as helpful automation inputs, not as sole proof that everything from that vendor is safe. Microsoft’s product‑scoped attestations provide high‑value signals for products they name, but Microsoft — like other large vendors — cannot instantly attest thousands of artifacts. Microsoft’s MSRC out are deliberately phased to deliver the most immediate customer value first.
- For enterprise vulnerability management, the practical requirement is twofold:
- Ingest vendor VEX/CSAF feeds to automate remediation where the vendor has attested a product is affected.
- Maintain an independent artifact inventory (images, kernels, WSL instances, AKS nodes, marketplace appliances) so you can verify or contest a vendor‑level attestation for your deployed artifacts.
Risks and caveats
- The CVE’s primary impact is availability (DoS via kernel OOPS/panic). Local exploitation is the realistic vector; remote, unauthenticated exploitation is not the expected threat model for this bug. That lowersality relative to remote code execution CVEs but does not make the issue unimportant — availability issues in kernels can undermine multi‑tenant or production platform stability quickly.
- Kernel image diversity matters: two kernels built from the same upstream tree can diverge in feature selection and backports; therefore a vendor‑attested kernel in Image A does not prove an un‑attested image B is safe. Verify artifact metadata and kernel configs for each artifact you run.
- Where public attestations are missing, yademand SBOM/VEX attestations from the vendor. Microsoft has publicly promised to update CVE pages if additional Microsoft products are identified as affected — but that is backward‑looking. If you need deterministic assurance today, perform artifact verification.
Conclusion — practical takeaway for defenders
Microsoft’s public message is correct and constructive: Azure Linux includes the implicated open‑source kernel component and is therefore potentially affected, and Microsoft has begun publishing CSAF/VEX attestations (a program that started in October 2025) and will publish attestations for additional products if they are found to be affected. That line is an authoritative call to action for Azure Linux customers.However, do not read that sentence as a declaration that no other Microsoft product could be affected. Any Microsoft artifact that ships or runs a Linux kernel build compiled from the vulnerable commit range and with the SMB client code enabled is potentially a carrier until verified. Prioritize patching Azure Linux images first, then inventory and verify WSL2 kernels, Azure VM/Marketplace images, AKS node images and any other Microsoft‑distributed artifacts you operate. Use vendor VEX/CSAF feeds as they arrive, but complement them with artifact‑level checks, kernel config inspections, and package metadata verification.
If you want a compact, runnable checklist or a short script that automates the kernel checks described above across a fleet (WSL endpoints, Azure VMs, AKS nodes), provide me the scope (cloud-only, enterprise endpoints, or both) and I will produce that runbook ready for your patching and remediation teams.
Source: MSRC Security Update Guide - Microsoft Security Response Center