Microsoft has quietly pushed KB5077241 into the Windows 11 preview channel and, while it’s not a headline-grabbing feature update, it is one of the more consequential quality-and-security releases in months — bundling a practical taskbar speed test, a curated Emoji 16 roll‑in, in‑box Sysmon (System Monitor) as an optional feature, WebP wallpaper support, camera pan/tilt controls, RSAT for Arm64, and critical groundwork for the upcoming Secure Boot certificate rotation that could affect thousands of devices if overlooked.
Microsoft published KB5077241 as a non‑security preview update on February 24, 2026, covering Windows 11 versions 24H2 and 25H2 and producing OS builds 26100.7922 and 26200.7922 respectively. The update is distributed as a preview (optional) servicing wave and uses a phased rollout model, so when you see the changes can vary by device and configuration.
The timing for KB5077241 matters. 2026 started poorly for Windows update reliability — a string of January fixes and emergency out‑of‑band patches raised doubts among IT teams about update testing and rollout behavior, and administrators are more cautious than usual about accepting cumulative and preview releases without validating them in controlled environments first. That context colors how organizations should approach KB5077241: treat it as a functional preview with important platform implications, but validate critical behaviors in a test ring before broad deployment.
Practical enablement examples are straightforward:
Why this is worth noting:
That said, the update must be handled with discipline:
Prepare your test plan now: verify Secure Boot CA status with the PowerShell checks, validate Sysmon behavior in a controlled ring, and script telemetry to monitor both installation success and any unintended service disruptions. KB5077241 is small in scope but substantial in consequence — treat it as an operational milestone, not just another optional preview.
Source: Windows Report https://windowsreport.com/kb5077241...i-sysmon-integration-and-secure-boot-updates/
 Background
Background
Microsoft published KB5077241 as a non‑security preview update on February 24, 2026, covering Windows 11 versions 24H2 and 25H2 and producing OS builds 26100.7922 and 26200.7922 respectively. The update is distributed as a preview (optional) servicing wave and uses a phased rollout model, so when you see the changes can vary by device and configuration.The timing for KB5077241 matters. 2026 started poorly for Windows update reliability — a string of January fixes and emergency out‑of‑band patches raised doubts among IT teams about update testing and rollout behavior, and administrators are more cautious than usual about accepting cumulative and preview releases without validating them in controlled environments first. That context colors how organizations should approach KB5077241: treat it as a functional preview with important platform implications, but validate critical behaviors in a test ring before broad deployment.
What’s in KB5077241 — Quick overview
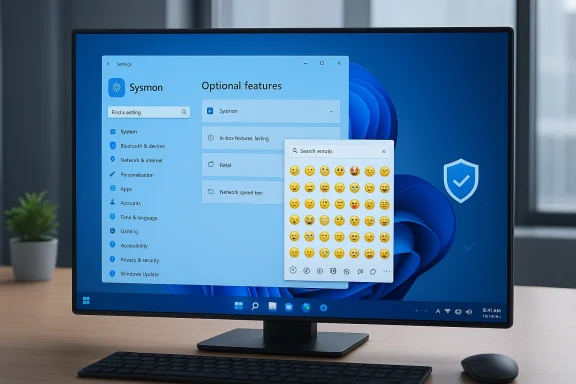
This is not a rework of the OS, but a focused bundle of platform, manageability and security changes:- Built‑in Sysmon (optional inbox feature) — Sysmon is now packaged with Windows and integrates with Event Log (disabled by default).
- Taskbar network speed test — a one‑click launcher exposed from the network icon or Wi‑Fi Quick Settings that runs a browser‑based speed check.
- Emoji 16.0 glyphs — a small, curated set of new emoji now available in the emoji panel (Win + .).
- Camera pan/tilt controls exposed in Settings for supported webcams.
- WebP as desktop background support.
- RSAT on Arm64, various File Explorer and printing fixes, Widgets settings improvements, and a BitLocker reliability fix.
- Secure Boot certificate updates: KB5077241 contains targeting data and mechanisms that expand device eligibility for receiving new Secure Boot certificates rolled out by Microsoft and OEMs ahead of certificate expirations beginning June 2026. This part of the update is operationally significant.
Sysmon, in‑box: what changed and why it matters
The practical change
Sysmon (System Monitor), long distributed as part of the Sysinternals toolkit, is now included in Windows as an optional, disabled‑by‑default feature. Enabling the feature installs Sysmon as a native component and writes its output to the Windows Event Log so existing SIEM and EDR pipelines can consume system‑level telemetry without deploying the separate Sysinternals package. Microsoft documents the enablement paths in KB5077241 (Settings > System > Optional features > More Windows features, or via DISM/PowerShell) and explicitly warns administrators to uninstall any previously installed Sysmon from Sysinternals before enabling the inbox version to avoid conflicts.Practical enablement examples are straightforward:
- Settings route: Settings > System > Optional features > More Windows features > select Sysmon and enable.
- CLI route: DISM or Add‑WindowsPackage to add the KB package, then run the Sysmon installer command to complete setup (the KB notes running sysmon -i after feature install).
Why this matters to defenders
Organizations that depend on endpoint telemetry — SOCs, IR teams, and threat hunters — will welcome the simpler provisioning. Making Sysmon available in the image (as an optional feature) lowers the friction for baseline telemetry on freshly imaged endpoints, Cloud PCs, and non‑persistent configurations where installing Sysinternals manually is inconvenient. It also aligns Windows with a “batteries‑included” security posture that makes threat detection easier to standardize.Caveats and operational risks
- Configuration still matters. Sysmon’s value comes from a quality configuration file (filters, event IDs toggled, exclusions). Shipping a default, aggressive configuration can produce enormous event volumes and false positives; shipping an overly restrictive one reduces detection fidelity. Plan a configuration lifecycle: test templates, vet exclusions for common enterprise software, and tune retention policies.
- Event Log volume and storage — enabling Sysmon without retention planning can fill event stores or overload SIEM ingestion budgets. Validate logging rates in a lab before rolling out at scale.
- Compatibility with existing Sysmon installs — Microsoft explicitly asks teams to uninstall the older Sysinternals Sysmon before enabling the inbox feature. Failing to remove the legacy package can produce unpredictable behavior.
Recommended actions for IT/SecOps teams
- Validate the Sysmon inbox feature in a dedicated test ring and collect realistic event volumes using your standard configuration.
- Convert your canonical Sysmon configuration and test it against the inbox implementation; confirm Event Log paths and retention behavior.
- Add Sysmon enablement/disablement to your imaging automation and group policy workflows; ensure rollback is possible.
- Update runbooks to include the explicit uninstall step for legacy Sysmon prior to enabling the inbox feature.
Taskbar network speed test — tiny convenience, big signal
KB5077241 surfaces a one‑click network speed test from the system tray network icon and the Wi‑Fi/Cellular Quick Settings. Selecting the entry opens a browser‑based speed test to measure latency, download, and upload on Ethernet, Wi‑Fi or cellular connections. This is a lightweight, diagnostic convenience aimed at end users and helpdesk staff to reduce time‑to‑diagnosis on connectivity complaints.Why this is worth noting:
- It signals Microsoft’s preference for small, integrated diagnostics in UX surfaces rather than pushing users to third‑party sites or tools.
- It’s low risk functionally, but because it launches the default browser it’s dependent on the browser environment and any enterprise proxy or monitoring that might affect test results. Test in your environment before relying on the number as evidence when troubleshooting.
Emoji 16 and WebP wallpaper support — quality of life and creator friendliness
KB5077241 adds a curated subset of Emoji 16.0 to the emoji panel and enables WebP images as desktop backgrounds from Settings or File Explorer. These are consumer‑visible polish items that improve creator and communication workflows and reduce the friction of modern image formats on the desktop. While minor in absolute importance, they represent Microsoft’s continued incremental investments in user experience and cross‑platform consistency.Camera pan/tilt controls, RSAT Arm64, and other incremental improvements
The update exposes basic pan and tilt controls for supported cameras in Settings > Bluetooth & devices > Cameras, and it ships Remote Server Administration Tools (RSAT) support for Arm64 devices. These changes are modest individually but meaningful in aggregate: improved camera controls help hybrid workers, and RSAT on Arm64 closes a long‑standing tooling gap for administrators managing Arm64 servers and endpoints. The release also includes numerous File Explorer, sleep/resume, printing spooler and Windows Update UI reliability fixes.Secure Boot certificate rotation — the operational imperative
Arguably the most critical reason to pay attention to KB5077241 is its role in the larger Secure Boot certificate refresh that Microsoft and OEMs have been coordinating for months. The certificates Microsoft originally shipped in 2011 (KEK/DB CA certificates) start to expire in June 2026 (and cumulatively through October 2026). Microsoft has published guidance and is rolling 2023 CA certificates to replace the expiring 2011 authorities; KB5077241 carries additional device targeting and rollout signals to increase the set of devices eligible to automatically receive the new certificates.What happens if devices do not receive the new certificates?
- Devices that do not receive updated CA entries will continue to boot, but they will not be able to receive new Secure Boot updates after the old CAs expire. That means firmware‑level and boot‑time security updates (DB/DBX, Windows Boot Manager updates) may not be applicable, exposing those devices to future boot‑level threats or leaving them unable to accept new signed loaders or option ROMs. Over time this degrades device security posture and could block platform upgrades.
Who needs to act?
- Most modern Windows 11 devices will receive the new certificates automatically through Windows Update and OEM firmware updates, but some fleets — particularly older hardware, specialized appliances, some VMs, and certain servers or IoT devices — may require firmware updates or manual steps from OEMs. OEM support pages (HP, ASUS and others) and Microsoft recommend checking your fleet and applying BIOS/UEFI updates where applicable.
How to check certificate state (quick verification cheatsheet)
Before rolling any changes, verify Secure Boot and the presence of the 2023 certificates:- Confirm Secure Boot is enabled:
- Run PowerShell as Administrator and execute:
- Confirm-SecureBootUEFI
- A result of True indicates Secure Boot is active.
- Inspect the DB (Allowed Signature Database) for the 2023 CA:
- Use (run elevated):
[System.Text.Encoding]::ASCII.GetString((Get‑SecureBootUEFI db).bytes) -match 'Windows UEFI CA 2023' - If the command returns True, the updated CA is present in the DB.
- Check KEK similarly:
[System.Text.Encoding]::ASCII.GetString((Get‑SecureBootUEFI kek).bytes) -match 'Microsoft Corporation KEK 2K CA 2023' - True indicates the new KEK entry exists.
- Registry deployment status and event logs:
- Inspect HKLM:\SYSTEM\CurrentControlSet\Control\SecureBoot\Servicing for rollout state keys (NotStarted, InProgress, Updated) and watch System log Event ID 1808 for certificate application success.
Recommended Secure Boot workplan for IT teams
- Inventory — identify devices with Secure Boot enabled and capture current DB/KEK contents using the PowerShell checks above. Flag hardware that lacks OEM firmware updates or is out of vendor support.
- Test — apply the certificate update and any BIOS/UEFI firmware update to a pilot cohort. Confirm BitLocker behavior is preserved and note if BitLocker recovery prompts appear after firmware upgrades. OEM documentation warns BitLocker recovery key prompts are possible and provide steps to minimize user impact.
- Automate — script the PowerShell verification steps and integrate them into patch orchestration tools to monitor rollout progress and surface devices that require manual intervention.
- Coordinate with procurement/OEMs — for older or specialized hardware, request firmware updates or documented procedures from OEMs. Many vendors (HP, ASUS) already published guidance and BIOS updates to help devices receive the new CAs.
- Communicate — inform helpdesk and end‑user support teams about possible BitLocker recovery prompts after firmware changes and ensure recovery keys are escrowed in your identity or management platform.
Deployment guidance and risk mitigation for KB5077241
KB5077241 is a preview (optional) update that contains both convenience features and important platform targeting adjustments. Approach deployment with the following practical checklist:- Test ring first — validate Sysmon enablement, event volume, SIEM ingestion and correlation; test the taskbar speed test workflow and confirm WebP wallpaper handling; validate camera PTZ controls for commonly used webcams.
- Secure Boot readiness — run the PowerShell checks above across your estate and escalate devices that lack the 2023 CAs. Create a remediation queue and prioritize server and critical endpoints for firmware updates.
- Backup and recovery — ensure BitLocker keys are accessible and preserved before applying BIOS/UEFI updates. Expect some endpoints to prompt for recovery keys after firmware updates, so surface recovery keys in advance for high‑risk devices.
- Monitor Microsoft’s release notes and health dashboard — follow the Windows release health and KB pages for any post‑release corrections or known issues tied to KB5077241. Microsoft lists no known issues at publication, but the January experience underlines the need to monitor closely after rollout.
What to watch for in the coming weeks
- Phased availability — feature availability for the taskbar speed test, Sysmon, and Emoji 16 may be gated by Controlled Feature Rollout logic and device targeting, so don’t assume uniform availability immediately after installing the KB.
- Sysmon configuration drift — as organizations enable Sysmon via group policy or images, mismatched configurations across environments will create blind spots or overload SIEM pipelines. Standardize and version control Sysmon configs.
- Certificate rollout telemetry — monitor event logs (Event ID 1808 and related Secure Boot events) and the registry servicing keys to verify certificate application status at scale. Automate remediation for devices stuck “NotStarted” or “InProgress.”
- OEM firmware cadence — some OEMs publish firmware updates quickly while others lag. Maintain a prioritized list of models that require manual firmware updates and track vendor advisories.
Final analysis: strengths, risks, and the path forward
KB5077241 bundles sensible, low‑risk productivity and manageability improvements with a quietly significant operational element: the Secure Boot CA lifecycle. The inclusion of Sysmon as an optional inbox feature is a pragmatic win for defenders and image builders — it reduces friction for delivering baseline telemetry across modern Windows 11 fleets. The speed test, WebP wallpaper support, camera PTZ controls and Emoji 16 upgrades are practical, user‑facing polish that will be appreciated by helpdesk teams and creators alike.That said, the update must be handled with discipline:
- Do not enable Sysmon at scale without configuration and ingestion planning. Event volume and retention are the tactical blockers here. Test with representative workloads and ensure SIEM filters and retention policies are sized appropriately.
- Secure Boot certificate rotation is a cross‑team problem. It requires firmware updates, validation scripts, and clear recovery procedures for BitLocker. Treat the certificate work as an infrastructure lifecycle program, not an incidental patch. Missing the migration window could reduce device security posture and complicate future boot‑time protections.
- Continue to watch Microsoft’s update hygiene. Given January’s emergency updates and fixes earlier in the year, conservative rollout and robust rollback-runbooks remain prudent. Validate in test rings and have recovery plans for impacted productivity apps or drivers.
Prepare your test plan now: verify Secure Boot CA status with the PowerShell checks, validate Sysmon behavior in a controlled ring, and script telemetry to monitor both installation success and any unintended service disruptions. KB5077241 is small in scope but substantial in consequence — treat it as an operational milestone, not just another optional preview.
Source: Windows Report https://windowsreport.com/kb5077241...i-sysmon-integration-and-secure-boot-updates/