The Linux kernel patch for CVE-2025-37973 fixes a bounds-calculation error in the wifi subsystem’s cfg80211 code that could produce an out‑of‑bounds access during multi‑link element defragmentation — and Microsoft’s public advisory names Azure Linux as the Microsoft product the company has inspected and attested as potentially affected, but that attestation is explicitly product‑scoped and does not by itself guarantee that no other Microsoft artifact contains the vulnerable upstream code.
Background / Overview
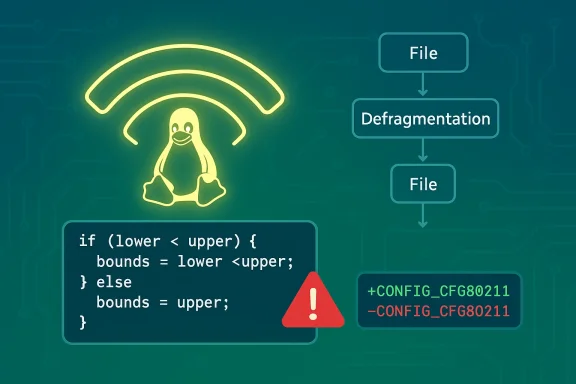
The vulnerability tracked as CVE‑2025‑37973 appears in the Linux kernel wireless configuration layer, cfg80211, during processing of Information Elements (IEs) used in multi‑link (ML) Wi‑Fi operations. In short, when the kernel code attempts to defragment multi‑link elements it incorrectly computes the length of the remaining IEs after the multi‑link element; the multi‑link element length was added to the total IEs length rather than using the proper end offset. If the multi‑link element (or its fragments) appear at the end of the IEs buffer, that calculation error can lead to an out‑of‑bounds access — a form of memory corruption that can crash the kernel or (in some exploit scenarios) be escalated to code execution.Two important, verifiable technical points:
- The bug is in the upstream kernel wireless code (cfg80211), which is part of the standard Linux kernel tree and can be enabled or disabled by kernel configuration (CONFIG_CFG80211). The cfg80211 subsystem acts as the canonical kernel interface for wireless drivers and is present in upstream kernel sources and in most distro kernels when wireless support is required.
- The upstream fix was committed into the kernel tree and distributed via vendor advisories and distro CVE trackers; multiple independent vulnerability databases (NVD, Ubuntu, Red Hat/Rapid7 and others) have indexed CVE‑2025‑37973 and list the corrected code as merged upstream. Those sources assign medium–high severity in their assessments and point to the kernel commit(s) carrying the fix.
What Microsoft actually said — reading the advisory closely
Microsoft’s Security Response Center (MSRC) CVE entry for CVE‑2025‑37973 contains an FAQ‑style line that has become standard across a number of Linux‑CVE pages: “Azure Linux includes this open‑source library and is therefore potentially affected by this vulnerability.” The page also explains that Microsoft began publishing machine‑readable CSAF/VEX attestations in October 2025 and that the company will update the CVE mapping if it identifies impact to additional Microsoft products. This is a deliberate, procedural statement: it documents Microsoft’s inventory for Azure Linux at the time of the advisory, and signals the start of a phased, artifact‑by‑artifact attestation process.Two clarifications readers must understand from that wording:
- Microsoft’s statement is an authoritative yes for Azure Linux: Microsoft inspected the Azure Linux distribution (the distro formerly known as CBL‑Mariner and the Microsoft‑maintained Azure images) and confirmed it includes the upstream component in question. Customers running Azure Linux should treat that product as in scope and follow Microsoft’s remediation guidance.
- That wording is not an explicit no for other Microsoft products. Microsoft is not asserting other Microsoft artifacts are unaffected; rather, the company is saying it has verified Azure Linux and will extend VEX/CSAF attestations to other products as inventories complete. Until Microsoft publishes those artifact‑level attestations or issues additional advisories, other Microsoft‑distributed kernel artifacts remain unverified, not necessarily immune. Independent community analysis has repeatedly emphasized this distinction.
Is Azure Linux the only Microsoft product that includes the library and is therefore potentially affected?
Short answer: No — not necessarily. Microsoft’s public attestation names Azure Linux because that product was inspected and inventoried; it is the only Microsoft product Microsoft has publicly confirmed carries the implicated open‑source component for this CVE so far. But that inventory statement is product‑scoped and time‑boxed: any Microsoft product, image, or service that ships a Linux kernel built with the wireless stack enabled (or that supplies kernel modules derived from upstream trees that include cfg80211) could contain the vulnerable code until the artifact is verified or patched.To restate precisely:
- Definitive: Microsoft has verified that Azure Linux includes the upstream code path implicated by CVE‑2025‑37973. Treat Azure Linux as in‑scope for remediation.
- Non‑definitive: Microsoft has not (yet) published a blanket statement that no other Microsoft product includes the vulnerable code. Other Microsoft artifacts must be treated as unverified until Microsoft’s VEX program or independent inspection demonstrates otherwise.
Which Microsoft products and artifacts could include cfg80211? (and why you should check them)
Because cfg80211 is an upstream kernel subsystem, it can appear in any Linux kernel binary built from kernel trees containing the code and configured to include wireless support. The practical Microsoft artifacts administrators should evaluate include:- Azure Linux images and linux-azure kernel packages — these are the direct targets of Microsoft’s attestation (so treat them as in scope). Microsoft maintains kernel artifacts used by Azure VM SKUs and these have historically included wireless subsystem components in their upstream merges.
- WSL2 (Windows Subsystem for Linux) kernel builds — Microsoft publishes the WSL2 kernel source and the kernel configuration used to build the WSL kernel. Whether a given WSL kernel includes cfg80211 depends on the particular Microsoft WSL build and config; some WSL published kernel configs include numerous drivers and platform support modules, so WSL cannot be categorically excluded without inspecting the specific WSL kernel build and its .config. In short: WSL2 is a plausible carrier until you verify the shipped kernel config.
- Azure Marketplace images and partner images — many Marketplace images include vendor‑provided or Microsoft‑curated kernel packages (e.g., “linux‑azure” or vendor kernels). The image publisher is responsible for patching those kernels; Microsoft’s attestation for Azure Linux does not automatically cover third‑party marketplace images. Check each image’s CVE advisories and kernel package changelogs.
- AKS node images and managed container hosts — while containers generally rely on the host kernel, AKS and other managed Kubernetes offerings run on host images that may use Microsoft‑maintained kernels or vendor kernels. If a host image runs a kernel with cfg80211 enabled, the host (and workloads with privileged kernel access) could be affected. Verify the node image kernel packages.
- Custom VM images, appliances, or IoT images provided by Microsoft partners — any image that ships a Linux kernel with wireless support compiled in can include cfg80211 and therefore must be inventoried individually.
For community and operational analysis, see corroborating threads and technical commentary from independent sources and community auditors who have reviewed Microsoft’s FAQ phrasing and recommended artifact checks.
How to verify whether your Microsoft artifacts are affected — practical checks
If you manage systems on Azure, WSL2, or other Microsoft artifacts, use the following deterministic checks to establish whether a particular artifact includes cfg80211 or the wireless drivers in question.- Inspect the running kernel configuration:
- zcat /proc/config.gz | grep -E 'CONFIG_CFG80211|CONFIG_MAC80211|CONFIG_IEEE80211'
- grep -E 'CONFIG_CFG80211|CONFIG_MAC80211' /boot/config-$(uname -r)
These commands will show whether cfg80211 (and related mac80211) were built into the kernel or as modules. If CONFIG_CFG80211 is set to "y" or "m" the subsystem is present.
- List loaded wireless modules:
- lsmod | grep -E 'cfg80211|mac80211|iwlwifi|ath|brcmfmac'
If cfg80211 is loaded as a module and driver modules (e.g. iwlwifi for Intel) are present, that kernel has the wireless stack active.
- lsmod | grep -E 'cfg80211|mac80211|iwlwifi|ath|brcmfmac'
- Check kernel package changelogs and distro CVE trackers:
- For Debian/Ubuntu: apt changelog linux-image-$(uname -r)
- For RHEL/SUSE: rpm -q --changelog kernel | grep CVE-2025-37973
Distribution changelogs and vendor advisories will often reveal whether upstream fixes have been backported.
- Inspect WSL kernel config (if you run WSL2):
- Microsoft publishes the WSL2 kernel config in the WSL2-Linux-Kernel repository (or via the kernel release tag). Review that .config against the CVE window to determine if cfg80211 was enabled in the WSL build used by your systems. If you run a custom WSL kernel (via .wslconfig), check that kernel’s .config directly.
- Centralize findings in asset inventory:
- Ingest results into a CMDB or asset inventory and map kernel versions/builds to your CVE inventory. Automated host scanning and configuration management (Ansible/Chef/Puppet) make this process repeatable at scale. Community guidance also encourages grep‑based checks across images and a focus on kernel packages rather than solely on userland packages.
Mitigation and remediation guidance
The operational goal for defenders is straightforward: identify all kernels (and kernel modules) that include the vulnerable cfg80211 code path, and apply the appropriate kernel updates or mitigations.- Apply vendor patches: distributions and kernel vendors have merged the upstream fix and are publishing packages. Rely on your distribution’s security advisories (Ubuntu, Red Hat, SUSE, etc.) or Microsoft’s Azure Linux updates for the official, tested kernel packages. Confirm the CVE mapping in the package changelog and apply updates according to your change control cycle.
- For WSL2 users: if Microsoft’s WSL kernel used in your environment has the vulnerable code, update to the latest Microsoft WSL kernel release (or install a patched custom kernel if you manage .wslconfig custom kernels). Inspect the WSL kernel config and changes and apply the recommended kernel update. Community repos and build tooling make it straightforward to build and test patched kernels for WSL when necessary.
- For Azure VM and Marketplace images: patch the VM’s kernel package and, if you manage golden images, rebuild and re‑publish patched images. If you consume third‑party marketplace images, consult the image vendor’s advisory. Microsoft’s attestation for Azure Linux covers Microsoft‑maintained Azure Linux images, but not third‑party marketplace images — each image publisher must be polled or checked.
- Short‑term mitigations: if an immediate kernel update is not possible, disable or unload the relevant kernel modules where feasible (e.g., prevent cfg80211 or specific wireless drivers from loading) — but recognize this may disable wireless functionality and is not a long‑term substitute for applying fixes. Use module blacklisting or kernel boot options in controlled environments. Confirm the mitigation’s impact in test before wide deployment.
- Monitor VEX/CSAF attestations: Microsoft’s move to publish machine‑readable VEX/CSAF attestations is intended to make product‑level mapping between CVEs and Microsoft artifacts deterministic. Use those attestations (and subscribe to vendor feeds) to reduce uncertainty as Microsoft expands its artifact coverage beyond Azure Linux. Until additional attestations appear, perform artifact verification as recommended above.
Threat and exploitability assessment
CVE‑2025‑37973 is an upstream bounds‑calculation bug that can produce an out‑of‑bounds kernel memory access. The immediate, common impact of such bugs is kernel instability and crashes (availability loss). Whether a local or remote attacker can escalate such a defect into code execution depends on a combination of factors: the specific kernel version and architecture, exploit techniques available to attackers for the target platform, presence or absence of exploit mitigations (kASLR, SMEP, KPTI variants, hardened compilers), and whether an attacker has an accessible channel to feed crafted multi‑link IEs into the vulnerable code path.Operational reality for cloud customers:
- In many cloud VM deployments Wi‑Fi hardware is not present or not exposed to guests, which reduces attack surface for remote network‑based triggers. However, a kernel vulnerability in a VM image still matters because the kernel code is present; privileged attackers or local users with access to crafted buffers may be able to trigger the defect. Inventory and patching remain the correct defense.
Strengths and limitations of Microsoft’s attestation approach
Microsoft’s decision to begin publishing CSAF/VEX attestations starting with Azure Linux is a meaningful transparency improvement: customers can programmatically consume attestations that explicitly declare which Microsoft artifacts include a named upstream component and thereby automate triage and prioritization. Microsoft’s advisory language — naming Azure Linux as a confirmed carrier and promising to extend VEX mappings — provides clear, actionable guidance for Azure Linux customers. This is a practical strength for Azure customers who run Microsoft‑maintained images.But the approach has inherent limitations that defenders must account for:
- Product‑scoped attestations are not ecosystem‑wide guarantees. Microsoft’s Azure Linux attestation is useful and authoritative for that product, but an absence of additional attestations is not evidence that other Microsoft images, kernels, or services are unaffected. For defenders, attestation absence equals “unverified” and should prompt artifact inspection or conservative patching.
- Inventorying every kernel artifact, marketplace image, and custom image across a large cloud environment remains operationally challenging. While VEX/CSAF helps, it does not fully replace the need for internal asset inventory and automation to detect vulnerable kernels.
Practical recommendations (operational checklist)
- For Azure Linux operators:
- Treat Microsoft’s attestation as authoritative and patch Azure Linux images per Microsoft guidance immediately. Test and deploy updated kernel packages across affected workloads.
- For WSL2 users:
- Inspect the WSL kernel config or update to the latest WSL kernel release from Microsoft. If you run a custom WSL kernel, rebuild it with the upstream fix applied.
- For all Azure customers and administrators:
- Run the kernel config and module checks described earlier across your fleet.
- Map kernel‑build artifacts to images and to VM SKUs in your CMDB.
- Patch kernel packages or replace images with patched golden images.
- If immediate patching is impossible, rely on controlled mitigations (module blacklists) and strict host isolation until fixes can be applied.
- Subscribe to vendor advisories (Microsoft MSRC VEX/CSAF feeds and your distro’s security list).
- For security teams running detection and scanning tools:
- Add rules to detect kernels with CONFIG_CFG80211 enabled and to flag images whose kernel package version falls within the vulnerable window. Automate remediation playbooks once an image or host is flagged.
Final assessment and cautionary notes
Microsoft’s advisory that “Azure Linux includes this open‑source library and is therefore potentially affected” is an important and correct inventory statement for Azure Linux — and Microsoft has committed to extending VEX/CSAF attestations to additional products as inventories complete. That means Azure Linux users should assume they are in scope and patch promptly. At the same time, defenders must resist the tempting misreading that Azure Linux’s naming constitutes an all‑clear for other Microsoft artifacts. The vulnerability lives in upstream Linux kernel code; any Microsoft product or image that ships a kernel built with the wireless stack enabled could carry the same code path until explicitly verified.Finally, a practical truth for defenders: inventory and patching are the controlling variables for how long a vulnerability remains exploitable in your environment. Use Microsoft’s VEX attestations where available, but complement them with deterministic artifact checks, automated scanning, and prioritized patching to reduce your exposure window.
Conclusion: Azure Linux is the Microsoft product Microsoft has publicly confirmed as a carrier of the upstream cfg80211 component implicated in CVE‑2025‑37973 — that attestation matters and Azure Linux customers should act immediately — but it is not a categorical statement that no other Microsoft product includes the same vulnerable library. Treat Microsoft’s statement as product‑scoped, perform artifact verification across WSL2, Marketplace images, AKS/node images and any Microsoft‑supplied kernel artifacts you run, and apply vendor patches or mitigations without delay.
Source: MSRC Security Update Guide - Microsoft Security Response Center