A kernel-level fix landed this week to close a subtle eBPF map bug that could make kernel-held objects persist longer than intended: CVE-2025-68744 patches a missing cleanup in the BPF percpu hash and LRU-percpu hash update path so that special fields (notably kptr reference/per-CPU pointer fields) are freed when a map value is updated — preventing the kernel from retaining memory referenced by BPFKPTR{REF,PERCPU} until the entire map is destroyed.
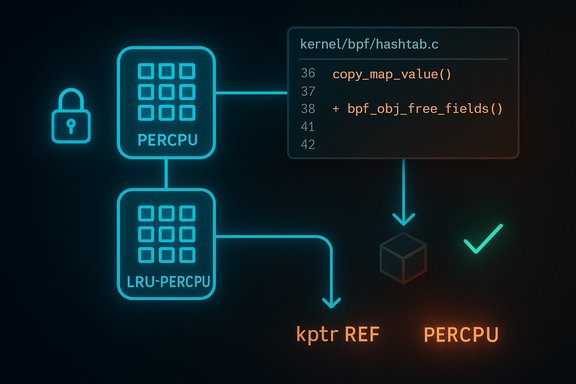
eBPF maps are kernel-side storage primitives used by eBPF programs and userland to share state. Percpu maps store per-CPU values for performance; LRU-percpu hash maps add eviction semantics. In late October a patch series authored by Leon Hwang identified that certain update paths for these map types failed to release special fields when copying values — specifically omission of a call to the kernel helper that frees object fields. The result was a memory hold: objects referenced by kptr fields could remain reachable from the map value and thereby remain allocated until the map itself was freed. This is not a classic code-execution or arbitrary-read flaw; it is a lifecycle/cleanup bug that causes memory referenced by BPF special fields to be held (leaked) longer than expected. The upstream fix inserts a call to bpf_obj_free_fields immediately after copy_map_value/copy_map_value_long in the percpu copy path (pcpu_copy_value so that reference counts are decremented and per-object resources are released on update. The change is small in code size but important in correctness.
Operators should prioritize updates according to their threat model: systems that allow untrusted workloads or that grant broad BPF capabilities deserve faster action. The upstream patch and test additions improve kernel robustness; applying them and continuing to harden BPF capability exposure remain the practical defenses.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
eBPF maps are kernel-side storage primitives used by eBPF programs and userland to share state. Percpu maps store per-CPU values for performance; LRU-percpu hash maps add eviction semantics. In late October a patch series authored by Leon Hwang identified that certain update paths for these map types failed to release special fields when copying values — specifically omission of a call to the kernel helper that frees object fields. The result was a memory hold: objects referenced by kptr fields could remain reachable from the map value and thereby remain allocated until the map itself was freed. This is not a classic code-execution or arbitrary-read flaw; it is a lifecycle/cleanup bug that causes memory referenced by BPF special fields to be held (leaked) longer than expected. The upstream fix inserts a call to bpf_obj_free_fields immediately after copy_map_value/copy_map_value_long in the percpu copy path (pcpu_copy_value so that reference counts are decremented and per-object resources are released on update. The change is small in code size but important in correctness. What exactly was wrong (technical overview)
Anatomy of the problem
- BPF maps can contain special fields that are not plain POD data: the kernel models certain fields as BPFKPTR{REF,PERCPU}, which represent kernel pointers with reference semantics or per-CPU pointer containers.
- When a user updates a percpu map entry, the kernel uses helper routines such as copy_map_value or copy_map_value_long to copy bytes into per-cpu storage.
- For map types that support these special fields, the kernel must call a cleanup routine — bpf_obj_free_fields — to release or decrement references for any previously-held object fields in the destination before overwriting them.
- In the percpu update path (pcpu_copy_value, this call was missing after the copy operation in certain code paths. As a result, the memory referenced by BPFKPTR{REF,PERCPU} fields could remain referenced and therefore not freed until the entire map was destroyed.
Scope of affected code
- The fix targets the percpu hash family and percpu LRU hash maps — the bpf hashtab code. Patch notes and the small diff show the insertion of the missing bpf_obj_free_fields call in kernel/bpf/hashtab.c immediately after the copy. The upstream discussion and series also point to related locations (local storage maps and update paths involving BPF_F_LOCK) that required careful handling; the initial series covers the non-locking cases and adds selftests to validate refcount behavior.
Confirmed facts and cross-checks
- The CVE record for CVE-2025-68744 was published and contains the same description: missing bpf_obj_free_fields in pcpu_copy_value leading to memory being held until map free. This is reflected in the official NVD entry and mirrored vulnerability databases.
- The upstream kernel patch series proposing the change, the discussion on LKML and public patchwork/patchew archives, and spinics mirror posts show the exact edit (two-line insertion) and the rationale; those patch messages include diffs and test plans.
- Multiple vulnerability trackers (Tenable, SUSE advisory pages, OSV, and others) have aggregated the CVE information; they differ slightly in how they rate or label severity, but all reference the kernel patch and the same underlying behavioral bug.
Risk assessment — what this means for systems
Technical impact
- The issue causes memory referenced by BPFKPTR{REF,PERCPU} fields to remain referenced and thus remain allocated longer than intended. Practically this manifests as a memory leak tied to map updates: repeatedly updating certain percpu map entries could cause the kernel to retain potentially unbounded memory if the old references are never released until the entire map is torn down.
- This is primarily a resource-management defect, not a direct memory-corruption or remote code-execution primitive. No public proof-of-concept exploit demonstrating privilege escalation or remote compromise was available at the time the CVE was published. Public vulnerability aggregators report no known public PoC for this CVE as of the initial disclosure.
Attack surface and exploitation requirements
- Creating or updating BPF maps requires the ability to use the bpf syscall and, depending on kernel configuration and program type, appropriate capabilities such as CAP_BPF, CAP_SYS_ADMIN, or other capability combinations. The kernel has been evolving to permit more granular capabilities (CAP_BPF) for certain operations while still limiting higher-risk actions to CAP_SYS_ADMIN or combinations of capabilities. Running unprivileged BPF is also gated by sysctl knobs such as kernel.unprivileged_bpf_disabled. Given these constraints, an attacker would typically need to be local and have elevated capabilities or exploit a separate privilege-escalation path to gain the necessary permissions to create/update the affected maps.
- Because the flaw causes retention of references rather than immediate corruption, exploitation to cause anything beyond increased memory use would be more complex and likely require chaining with other bugs (e.g., reference-count abuse or use-after-free elsewhere). No evidence yet shows such chaining in the wild for this CVE.
Severity — why vendors differ
- Vendor trackers differ in severity labeling. Some tools and scanners (e.g., Tenable/Nessus) have assigned a higher effective severity based on potential for denial-of-service/resource exhaustion and a conservative mapping to CVSS-like vectors, while other vendors and distributions describe the issue as informational or leave severity unset pending distro impact analysis. NVD initially listed the record without a CVSS score at publication. This divergence happens frequently with correctness/resource bugs — they can be rated anywhere from informational to high depending on assumptions about exploitability, required privileges, and whether memory retention can be monetized into a service disruption in customer environments.
Who should care, and how urgent is patching?
- Kernel maintainers, cloud providers, and large-scale Linux hosts that run untrusted code, multi-tenant containers, or have heavy use of eBPF for observability or networking should treat this as a relevant fix. In multi-tenant environments the risk of resource exhaustion from a misbehaving BPF program is a valid operational concern.
- Systems that do not run eBPF programs that use percpu hash or LRU-percpu hash maps — or where user processes do not have CAP_BPF/CAP_SYS_ADMIN — are at lower immediate risk. Nevertheless, because kernel bpf interfaces can be used by toolchains and auto-loaded by libbpf-based tooling, the conservative recommendation is to apply the kernel patch via your vendor kernel update when available.
Mitigation and remediation guidance
Immediate steps (operational)
- Inventory: Identify hosts that are running eBPF workloads — tracing agents, network dataplane components (XDP, TC), observability stacks that use libbpf, and any custom tooling that might create percpu hash or LRU-percpu hash maps.
- Privilege review: Confirm which processes hold CAP_BPF, CAP_SYS_ADMIN, or run with unprivileged_bpf enabled. Restrict CAP_BPF and related capabilities to trusted system components. Review systemd unit files and container runtimes for capability grants.
- Patch promptly: Apply the kernel update that contains the upstream fix. Upstream commit discussion and the kernel patch series make clear where the change was inserted; distribution vendors will fold the change into their kernel packages and publish advisories. Where vendor patches are not yet available, consider backporting the small patch if you maintain custom kernels (only if comfortable doing so) or limiting BPF capabilities until the vendor update is applied.
- Reboot: Kernel fixes require a kernel upgrade and subsequent reboot or kexec. Plan reboots for the affected hosts after patching.
- Monitoring: Watch memory usage patterns tied to BPF maps. Repeated, unbounded increments in kernel memory associated with eBPF workloads should be investigated and may indicate the leak pattern this CVE addresses.
Detection guidance
- Look for processes that repeatedly create/update percpu map entries and note kernel memory (kmalloc/rcu) that increases over time tied to those workloads.
- Use kernel eBPF selftest infrastructure (the upstream patch added selftests) and vendor-supplied regression tests to validate that updates no longer leak references. If vendor kernels include the test suite, run it in CI to verify remediation.
Practical notes for administrators and developers
- The code change is intentionally small: calling bpf_obj_free_fields after the copy ensures the object fields are freed or reference-count decremented promptly. The minimal scope of the fix makes it an easy backport candidate for distribution maintainers. That said, any backport must be applied carefully and validated because BPF code paths are performance-sensitive and core to many networking and observability subsystems.
- Developers using libbpf, bpftool, or any eBPF loader should ensure that map types in use are appropriate and that code paths handling updates consider object lifetime semantics. Wherever possible, pin maps deliberately, and avoid accidental global maps created in ephemeral test code that could persist in production images.
- Cloud and container operators: ensure container runtimes do not grant CAP_BPF broadly to untrusted workloads. Locking down capabilities reduces the attack surface and the ability of tenant workloads to create or update map types that could trigger such leaks. The kernel has options and knobs (e.g., kernel.unprivileged_bpf_disabled) to further restrict unprivileged BPF usage.
Why this matters beyond a small patch
- eBPF is now central to many Linux subsystems: networking datapaths, observability pipelines, and security tooling rely on maps and programs. Correctness issues in map lifecycle management can escalate from a local resource leak to systemic resource exhaustion in high-volume production clusters.
- The bug illustrates a class of errors where missing cleanup for non-trivial object fields leads to long-lived leaks — a subtle correctness issue that tests can miss without explicit negative tests for refcount and resource release behavior. The upstream patch series added selftests to detect the regression and ensure repeatable validation, which is an important step for future robustness.
Divergences and open questions (transparency and verification)
- Severity: At the time of publication the NVD record does not yet carry a canonical CVSS vector; third-party scanners and vendors have mapped the issue to a variety of severity levels (ranging from informational to high). That discrepancy reflects differing risk models: whether the bug can be weaponized locally in a particular environment vs. being a correctness/resource management issue. Administrators should interpret severity in light of their specific risk profile (multi-tenant services, cloud workloads, privileged tooling).
- Exploitability: No public PoC or exploit chain was available at disclosure; public trackers list no PoC repositories for CVE-2025-68744. That absence reduces the immediate urgency for emergency incident response (no known active exploitation), but it is not a reason to postpone patching — memory/resource bugs can be escalated or combined with other weaknesses in the future.
- Vendor uptake: Some distros will classify and patch faster than others. Where a distribution declares a kernel class as “won’t fix” for certain bug classes, operators must decide whether to backport the upstream fix themselves or migrate to a vendor kernel that includes the change. Check your vendor advisories for distribution-specific instructions.
Recommended checklist (practical remediation steps — quick reference)
- Confirm whether any workloads on the host create or update percpu hash / LRU-percpu hash eBPF maps.
- Confirm which processes hold CAP_BPF or CAP_SYS_ADMIN; reduce privileges where possible.
- Apply vendor kernel updates that include the upstream patch (or backport the upstream one-line fix if you manage custom kernels).
- Reboot hosts after kernel updates.
- Monitor kernel memory, BPF map counts, and application behavior for anomalous growth.
- Run eBPF selftests where available to verify refcount behavior after updates.
Conclusion
CVE-2025-68744 is an instructive example of how small omissions in resource lifecycle handling in the kernel can produce real operational hazards. The upstream fix is straightforward and corrects lifecycle behavior in percpu hash update paths so that special BPF fields (kptr reference and per-CPU pointer types) are freed when a map entry is overwritten. While this vulnerability looks like a leak rather than an immediate code-execution vector, environments that depend on eBPF at scale — multi-tenant systems, cloud infrastructure, observability stacks — should treat the issue seriously: inventory, reduce unnecessary BPF privileges, apply vendor patches quickly, and monitor for anomalous memory growth until vendors have shipped and you have validated the updates.Operators should prioritize updates according to their threat model: systems that allow untrusted workloads or that grant broad BPF capabilities deserve faster action. The upstream patch and test additions improve kernel robustness; applying them and continuing to harden BPF capability exposure remain the practical defenses.
Source: MSRC Security Update Guide - Microsoft Security Response Center