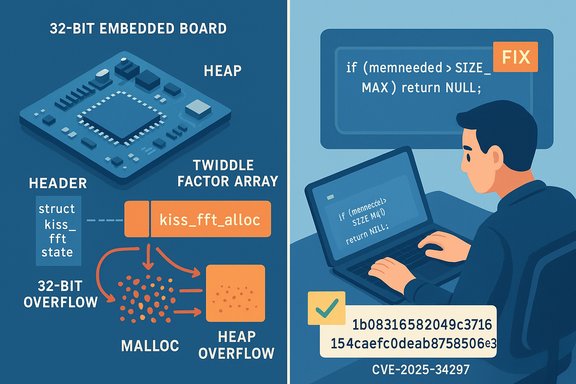
KissFFT maintainers fixed a dangerous integer‑overflow‑turned‑heap‑overflow in the library’s allocator that can crash or corrupt processes on 32‑bit builds — a flaw tracked as CVE‑2025‑34297 affecting KissFFT versions before the commit that checks for overflow in
KissFFT is a compact, permissively licensed FFT library widely embedded in audio tools, signal‑processing toolchains, scientific software, and many firmware images where small, portable C libraries are preferred. The vulnerability CVE‑2025‑34297 stems from improper arithmetic when computing the allocation size inside
Operational checklist (summary)
Source: MSRC Security Update Guide - Microsoft Security Response Center
kiss_fft_alloc.
 Background / Overview
Background / Overview
KissFFT is a compact, permissively licensed FFT library widely embedded in audio tools, signal‑processing toolchains, scientific software, and many firmware images where small, portable C libraries are preferred. The vulnerability CVE‑2025‑34297 stems from improper arithmetic when computing the allocation size inside kiss_fft_alloc; on 32‑bit platforms where size_t is limited, the expression used to compute memory requirements can wrap, causing malloc to allocate too little memory and a later initialization loop to write past the allocated buffer. The issue was fixed upstream with a defensive bounds check in commit 1b08316 that explicitly aborts the allocation for dangerously large nfft values. Multiple public vulnerability databases and advisories reproduced the same technical summary and assigned a high severity (CVSS v4.0 ≈ 8.6) in vendor/third‑party assessments; NVD’s record is present but marked as awaiting enrichment while other trackers list the published details. Technical analysis
What exactly goes wrong
- The vulnerable code computes the required memory as a sum of a fixed header (
struct kiss_fft_state) plus space for the twiddle factors, using an expression that multipliessizeof(kiss_fft_cpx)by(nfft - 1). - On platforms where
size_tis 32 bits, a largenfftvalue can make that multiplication overflow (wrap to a small value).malloctherefore returns a buffer smaller than the code expects. - The library then initializes
nffttwiddle entries in a loop, writing past the undersized allocation and creating a heap buffer overflow. This is an instance of an integer overflow → buffer overflow chain (CWE‑190 → CWE‑122).
The upstream fix
The maintainer added a size check before computing/allocating memory. In effect:- If
nfftis large enough thatmemneededwould exceedSIZE_MAX(i.e., the multiplication could overflow), the function returnsNULLto signal allocation failure rather than continuing to an unsafe allocation and initialization. - The specific commit adds the conditional test and returns early when a potentially overflowing
nfftis detected. This is a small, safe, and targeted fix that prevents the arithmetic wrap and subsequent out‑of‑bounds writes.
Why this is platform‑specific
- The overflow depends on the width of
size_t. On modern 64‑bit builds wheresize_tis 64 bits, the multiplication does not wrap for practical FFT sizes; the vulnerability therefore only affects 32‑bit builds (including many embedded targets and legacy x86 systems). Public trackers make this platform distinction explicit.
Affected systems and real‑world impact
Who should care
- Embedded and IoT vendors that build KissFFT into firmware images using 32‑bit toolchains (ARMv7, MIPS, older x86) are the highest‑risk group.
- Desktop or server applications that statically link a 32‑bit build of KissFFT or ship 32‑bit binaries.
- Any downstream project that exposes FFT sizes derived from untrusted inputs (for example, networked audio processing servers, file parsers that accept FFT parameters, or plugins accepting user‑supplied configuration) can be fed a large
nfftvalue to trigger the condition.
Attack vector and prerequisites
- The vulnerability is local in the sense that exploitation requires calling into the vulnerable
kiss_fft_allocwith a craftednfftvalue; whether that is remotely exploitable depends entirely on how the host application exposes that functionality. - Typical vectors:
- An application that accepts FFT size over a network protocol or file format without validation.
- A plugin interface in a sequencer/DAW or audio server that parses user input.
- A firmware API callable by local parties (or code running in a guest container on the device).
- Privileges: no explicit special privileges are needed if the host process exposes the call to untrusted inputs; otherwise the requirement is whatever privileges the calling context already has.
Realistic impacts
- Primary immediate impact: denial of service and process crashes (heap corruption leading to aborts, aborting the process, or causing undefined behavior).
- Secondary impact: depending on the host environment and mitigations (ASLR, heap hardening, control flow integrity), heap corruption may be exploitable for code execution or privilege escalation, though reliably converting a heap overflow into RCE typically requires additional memory‑corruption or information‑leak primitives in the surrounding application.
- Score & urgency: vendor/third‑party quantitative assessments place the issue at high severity (CVSS ≈ 8.6) because integrity and availability impacts are high when untrusted inputs are accepted and the environment is 32‑bit. NVD’s page exists but is awaiting full enrichment at time of writing.
Verification and sources
All technical claims in this article were checked against multiple independent sources:- The KissFFT upstream commit that implements the overflow check and returns early is publicly visible in the repository (commit
1b08316). The commit message and diff show the exact check added tokiss_fft_alloc. - Vulnerability aggregators and trackers document the issue description, platform scope (32‑bit only), and the same root cause (integer overflow leading to heap overflow). These include NVD and independent CVE aggregators. Note that NVD lists the CVE but was marked as awaiting analysis at the time of capture; some commercial aggregators have published a CVSSv4 assessment.
- Vendor/third‑party advisory mirrors and vulnerability indexing sites provide corroborating writeups and timelines; where vendor scoring differs, treat NVD and the upstream commit as canonical for technical details.
Mitigation and remediation (practical playbook)
The single correct remediation is to update to a KissFFT source tree that contains the fix (the commit referenced above) and rebuild any artifacts that embed KissFFT. For integrators who cannot immediately upgrade, adopt compensating controls.Immediate steps for integrators and developers
- Identify any builds that contain KissFFT.
- Check project dependencies, submodules, and static library linkages.
- For firmware and embedded images, inspect build artifacts and toolchain outputs.
- Verify whether your build targets are 32‑bit. If your distribution or product uses 64‑bit builds exclusively, the risk from this specific flaw is low, but you should still track updates.
- Update KissFFT to the fixed commit or to the downstream release that includes it, and rebuild all binaries and firmware images that statically link the library.
- If you vendor a copy of the source, apply the same early‑return check in
kiss_fft_allocor merge the maintainer’s patch. - Run functional tests covering FFT initialization and edge cases to ensure your integration handles allocation failures gracefully (i.e., check for
NULLreturns and fail safely). - Reproduce and harden: add unit tests that call
kiss_fft_allocwith very largenfftvalues to ensure the patched library returnsNULLrather than performing unsafe writes.
Short‑term compensations if patching is delayed
- Validate inputs: enforce sane upper bounds on
nfftvalues in application code before calling into KissFFT. Reject or clamp values that exceed application‑defined maximums. - Sandbox and restrict: run processes that call into vulnerable builds with reduced privileges and process isolation (containers with limited interfaces, hardened user accounts).
- Monitoring: enable application telemetry and process‑crash alerts. Heap corruptions can manifest as frequent crashes or abnormal termination — instrumenting these signals helps detect attempts to trigger the flaw.
For distribution and vendor teams
- Backport the upstream check into maintenance branches if you ship a stable vendor kernel or firmware line—but test across embedded toolchains because size and alignment semantics can vary between compilers.
- Reissue firmware updates with proper change logs; for devices that cannot be updated, flag the devices as at‑risk and apply network/hardening mitigations (limit access to configuration channels, restrict input sources that can influence FFT parameters).
Detection, hardening, and long‑term fixes
Detection
- Static analysis and fuzzing: integer overflows that lead to allocation miscalculations are easily discovered by bounded fuzzers and integer‑wrap detectors. Incorporate these into CI and pre‑release pipelines.
- Binary SBOM and provenance scanning: maintain a software bill of materials to identify where KissFFT is present in compiled images. Many embedded supply chains miss this step—this CVE is a strong example of why SBOMs matter.
- Runtime memory safety tools: AddressSanitizer (ASan) and heap sanitizers will catch out‑of‑bounds writes during testing, but are rarely enabled in production builds due to performance/size costs; use them during development and QA.
Hardening recommendations
- Defensive coding: when computing allocation sizes, cast operands to a sufficiently wide unsigned type and check for overflow before calling
malloc; prefer checked multiply routines or helper macros. - Fail‑safe behavior: ensure callers of allocation functions properly handle
NULLand do not proceed into loops that assume memory was allocated successfully. - Prefer modern memory‑safe wrappers where practical, or add range checks at API boundaries for any parameter that controls allocation sizes.
Supply‑chain implications
This vulnerability highlights a recurring supply‑chain risk: a tiny utility library widely embedded across diverse products can create systemic exposure when used in 32‑bit firmware or poorly validated host code. The attack surface is magnified by:- Static linking: many embedded/firmware builds statically link small libraries, which means a vulnerable version may be present in many products and releases.
- Vendor lag: devices in the field, especially in control systems or consumer electronics, may not receive timely firmware updates.
- Transitive usage: downstream projects may pull KissFFT as a submodule, copy, or bundled source — scanning and SBOMs are required to find all copies.
Practical recommendations for Windows‑centric operators
- For Windows desktop/server applications: most modern Windows deployments are 64‑bit and therefore not vulnerable to this specific 32‑bit overflow. Nevertheless:
- Verify whether any shipped or bundled third‑party components include a 32‑bit build of KissFFT (legacy plugins, 32‑bit helper executables, or drivers).
- Where an application provides a scripting or plugin interface that accepts FFT sizes, ensure those inputs are validated in the application code.
- For edge devices and appliances managed from Windows consoles:
- Inventory devices with SBOMs or vendor inventories and prioritize devices using 32‑bit toolchains or older firmware.
- Coordinate firmware updates with vendors and schedule redeployments for devices in the field.
- For developers building cross‑platform audio or DSP apps on Windows:
- Pull the patched KissFFT source (commit
1b08316or later), rebuild both 32‑bit and 64‑bit targets, and run automated tests that include very largenfftinputs to ensure graceful failures.
Assessment of exploitability and residual risk
- Exploitability: the vulnerability is high‑impact in the right context because heap corruption can potentially yield code execution. In practice, exploiting this vulnerability for reliable RCE will depend on the host process’s memory layout, compile/runtime mitigations, and presence of other memory primitives. The most immediate and likely outcome is process crash or denial of service.
- Scope: limited to 32‑bit builds of KissFFT — modern 64‑bit desktop/server OSes are generally less exposed, but many IoT and embedded targets remain vulnerable.
- Current public exploitation: as of publication there is no widely published proof‑of‑concept exploit demonstrating reliable remote RCE; trackers and the upstream commit indicate an early disclosure and prompt patching by the maintainer. Treat absence of public PoC as provisional — practical, local exploit code may appear quickly once details are public.
Conclusion
CVE‑2025‑34297 is a textbook example of how integer arithmetic mistakes in allocation math can convert into heap buffer overflows with real operational impact — especially in 32‑bit builds common to embedded systems. The fix is straightforward and has already been merged upstream: check thenfft value against an overflow threshold and return early rather than risking an undersized allocation. Integrators must do the hard work: find every build that bundles KissFFT, rebuild with the patched source, and reissue firmware and binaries where necessary.Operational checklist (summary)
- Audit: locate all instances of KissFFT in your codebase and firmware images.
- Patch: update to the fixed commit (or vendor release containing it) and rebuild all affected artifacts.
- Validate: add edge‑case tests for oversized
nfftvalues; ensure callers handle allocation failures safely. - Harden: add input validation, run static analysis / fuzzing in CI, and maintain SBOMs to reduce future supply‑chain surprise.
Source: MSRC Security Update Guide - Microsoft Security Response Center