The Linux kernel has received a targeted fix for CVE-2025-38131 — a race-condition in the CoreSight configfs handling that could allow an active trace configuration to be deactivated while it is being enabled, producing a reliable use‑after‑free (UAF) and a local denial‑of‑service condition; vendors and distributions have backported small, surgical patches and operators should treat this as a priority for any hosts that expose CoreSight trace device nodes or run customized/OEM kernels.
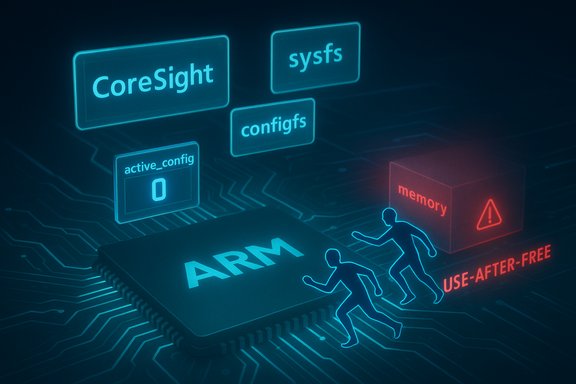
CoreSight is the Linux kernel’s framework for SoC tracing and debug on ARM platforms. It exposes configuration interfaces through configfs and sysfs that let userland enable, disable, and manage trace configurations. A subtle ordering and reference‑counting bug in the CoreSight configfs code allowed a race where one CPU could be enabling an active configuration while another CPU — via the sysfs interface — deactivated and unloaded it. That interleaving could free a configuration descriptor while the original enabling path continued to use it, producing a kernel use‑after‑free that commonly manifests as oopses and host instability. The vulnerability was cataloged as CVE‑2025‑38131 and published in early July 2025; maintainers addressed it with narrow changes that convert the active configuration counter into a reliable reference count and ensure the module reference is held until the configuration is no longer active. The fix is small but important because it closes a deterministic lifetime window that allowed access to freed memory from kernel code.
The vulnerable sequence mixes:
Recommended immediate steps (operations‑ready):
For administrators the orders of business are clear: inventory hosts that expose CoreSight/configfs, map vendor kernel packages to the upstream commit, apply distributor or vendor kernel updates, and reboot in a staged way. Where patching cannot be immediate, restrict access to configfs/sysfs and remove device exposure from untrusted containers or VMs. Embedded and OEM kernels represent the largest residual risk; engage vendors for explicit backport timelines.
Operators should treat the absence of public exploitation as a temporary reassurance only — a deterministic kernel UAF is an operationally significant failure mode in multi‑tenant and CI/VDI environments and merits rapid remediation to maintain system reliability and security.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
CoreSight is the Linux kernel’s framework for SoC tracing and debug on ARM platforms. It exposes configuration interfaces through configfs and sysfs that let userland enable, disable, and manage trace configurations. A subtle ordering and reference‑counting bug in the CoreSight configfs code allowed a race where one CPU could be enabling an active configuration while another CPU — via the sysfs interface — deactivated and unloaded it. That interleaving could free a configuration descriptor while the original enabling path continued to use it, producing a kernel use‑after‑free that commonly manifests as oopses and host instability. The vulnerability was cataloged as CVE‑2025‑38131 and published in early July 2025; maintainers addressed it with narrow changes that convert the active configuration counter into a reliable reference count and ensure the module reference is held until the configuration is no longer active. The fix is small but important because it closes a deterministic lifetime window that allowed access to freed memory from kernel code. Why this matters: impact and attack surface
- Primary impact — Availability (DoS): The defect produces deterministic kernel crashes or oopses when the driver dereferences freed configuration data. In production or multi‑tenant hosts this can force reboots, break tracing, or destabilize the system.
- Attack vector — Local: Exploitation requires the ability to trigger configfs/sysfs operations and module load/unload sequences. That is a local vector: untrusted containers, CI runners, or low‑privileged local users with access to /sys or /dev nodes may be sufficient depending on configuration.
- Privilege requirements: In many setups only low privileges are needed if configfs or trace device nodes are exposed; in better‑hardened systems root or CAP_SYS_ADMIN may be required. However, in cloud, CI, or VDI setups where device nodes are intentionally exposed to guests or containers for GPU/SoC access, the practical risk is real.
- Exploitability: At disclosure there were no public exploit campaigns converting this UAF into privilege escalation; the clearest outcome is a reliable host crash. Still, UAFs in kernel space are red flags — complex exploit chains have historically reused such primitives when combined with allocator‑shaping and other local primitives. Treat the absence of public PoCs as reassurance, not proof of safety.
- CPU0: sysfs path increments a system active counter (sys_active_cnt).
- CPU1: a module load triggers cscfg_load_config_sets and begins to activate a config.
- CPU1 calls cscfg_csdev_enable_active_config and takes csdev->cscfg_csdev_lock to enable the config.
- CPU0, via sysfs, deactivates the config (sys_active_cnt returns to 0).
- If the module unload path runs, cscfg_unload_config_sets can free the config_desc while CPU1 still holds a reference to it — a classic UAF.
Technical details: root cause and the patch
The root cause (race + lifetime error)
At a high level, the flaw is a reference-counting and ordering error: code paths that activate or enable a configuration did not reliably hold a reference adequate to prevent another CPU from deactivating and triggering module unload while the first CPU still used the config descriptor.The vulnerable sequence mixes:
- sysfs-driven active counts (sys_active_cnt),
- per‑config descriptors (config_desc),
- module load/unload lifecycles.
The fix applied upstream
Maintainers implemented a focused change: use the per‑configuration active_cnt as a proper reference count and ensure the module reference is taken when config_active_cnt transitions from 0 to 1 and held until it goes back to 0. In practice this means:- incrementing and checking config_desc->active_cnt in the enable path,
- holding the module reference while the config is active,
- ensuring the teardown/unload path cannot free the descriptor while active_cnt > 0.
Verified timeline and public trackers
- CVE‑2025‑38131 was recorded and published in early July 2025; national and open vulnerability feeds reflected the entry and mapped it to upstream stable commits and vendor advisories.
- Upstream diffs and stable commits were referenced in vulnerability mirrors and distribution advisories; maintainers merged the fixes in stable branches and maintainers encouraged distributions and vendors to backport the small patch to older kernel series used in appliances and embedded devices.
Who is affected — practical scope
- ARM/ARM64 platforms where CoreSight tracing and the cscfg driver are enabled (CONFIG_CORESIGHT* and related configfs support).
- Embedded devices, SoC images, Android/OEM kernels: these are highest risk because vendors frequently maintain divergent kernel trees and may not promptly backport small upstream fixes.
- Cloud/VDI/CI platforms that intentionally expose trace device or configfs interfaces to untrusted containers or guest images.
- Developer workstations that load tracing modules or run tracing tools that exercise the CoreSight configfs paths.
Detection, hunting, and triage
Detecting attempted exploitation or accidental hits of this code path relies on kernel telemetry:- Monitor kernel logs (dmesg, journalctl -k) for OOPS backtraces or messages from CoreSight codepaths that reference cscfg_* functions.
- If your kernel build includes KASAN or other sanitizers in a test ring, sanitizer traces will reliably highlight invalid frees or UAFs in the cscfg path.
- On modular kernels check lsmod for CoreSight-related modules and inspect /sys/bus/coresight devices to see whether configfs entries are present.
- Centralize kernel crashes and OOPS traces (kexec/kdump, vmcore) for forensic analysis if repeated failures occur.
- grep -i coresight /var/log/kern.log or journalctl -k.
- Inspect /sys/bus/coresight for configfs entries and active configs.
- In test environments enable kmemleak/KASAN for deterministic detection when reproducing activation/deactivation flows.
Mitigation and remediation guidance
The only definitive remediation is to install a kernel package that includes the upstream stable commit(s) addressing the CVE and reboot into the updated kernel.Recommended immediate steps (operations‑ready):
- Inventory: Run uname -r and capture kernel versions across your estate. List hosts where CoreSight or configfs is enabled. (Commands: uname -r; grep CONFIG_CORESIGHT /boot/config-$(uname -r); ls /sys/bus/coresight).
- Map vendor packages: Consult your distribution or vendor security tracker to identify which kernel package versions contain the upstream commit or explicit CVE mention. Do not assume package version numbering alone — confirm the commit is present in changelogs.
- Patch: Apply vendor/distribution kernel updates that contain the stable commits and plan a staged reboot rollout (pilot -> canary -> production).
- Validate: After patching, reproduce representative trace/attach/detach sequences and monitor kernel logs for 7–14 days; in high‑risk environments run sustained soak tests.
- Compensations: If immediate patching is impossible:
- Restrict access to configfs/sysfs entries and relevant device nodes via udev rules and file permissions.
- Remove device exposure from untrusted containers or guests (drop binding of /sys/bus/coresight or restrict container device mappings).
- Blacklist the CoreSight modules on hosts where tracing is not needed (modprobe.blacklist) and rebuild initramfs where necessary.
Practical checklist for WindowsForum readers (concise, prioritized)
- Within 24 hours:
- Inventory hosts that run ARM-based Linux images, developer boards, or vendor appliances; collect uname -r outputs.
- Identify hosts that mount configfs or expose /sys/bus/coresight entries to untrusted users.
- Within 72 hours:
- Confirm vendor patches are available for your distro or device.
- Schedule a staged kernel rollout for affected hosts, prioritizing cloud / multi‑tenant / CI runners.
- Implement temporary access controls (udev, container device policies).
- Post‑deployment:
- Validate with workload replay and monitor kernel logs.
- If you operate embedded fleets, open vendor tickets and request explicit backport information and predicted firmware release dates.
Critical analysis — strengths of the response and residual risks
Strengths of the upstream fix- Surgical and testable: The patch is narrowly scoped to lifetime and reference counting; small diffs reduce regression risk and make backporting straightforward. That means distributions can ship security updates quickly.
- Observable failure mode: The bug produces deterministic kernel oops traces that are reproducible in instrumentation builds (KASAN/kmemleak), making verification in test rings practical.
- Long tail in embedded/OEM kernels: Appliances, vendor kernels, and SoC-specific images often lag upstream; those devices may remain vulnerable for months. This long tail is the primary exposure for real world risk.
- Other race paths: The fix covers the identified enable/disable race and module lifecycle interplay, but similar lifetime errors could exist in other CoreSight or configfs flows; comprehensive triage is recommended.
- Reboot requirement: Kernel fixes require reboots. For high‑availability fleets, scheduling reboots and performing careful staging is necessary.
- Detection gaps: Kernel oopses can be intermittent or missed without centralized kernel logging and crash collection; organizations that rely solely on userland monitoring may not see these failures quickly.
- Public trackers and vendor advisories do not report active exploitation in the wild for CVE‑2025‑38131 at time of this writing. That is a snapshot of public information and does not exclude undisclosed private exploitation; assume a credible DoS risk until patches are deployed.
Longer‑term implications and lessons for operations
- Device exposure policies matter: Exposing debug/tracing interfaces to untrusted workloads — even for convenience in CI or developer workflows — significantly raises the risk profile. Device exposure should be limited by policy and automated checks.
- Kernel patch discipline: Small, correctness fixes in drivers are frequent; organizations must establish a predictable kernel patching cadence and a test+rollback plan that covers both generic distributions and vendor‑supplied images.
- Supply chain visibility for embedded fleets: OEMs and appliance vendors must provide clear backport timelines and machine‑readable attestations (CSAF/VEX style) for kernel components embedded in their images so customers can triage quickly.
- Centralized kernel telemetry: Aggregating dmesg/journalctl and enabling kdump/vmcore collection for critical hosts changes a kernel bug from an “annoyance” into a trackable security issue that can be triaged and remediated promptly.
Recommended technical verification commands (quick copy list)
- Determine kernel version:
- uname -r
- Check whether CoreSight configfs is present:
- ls /sys/bus/coresight || echo "no coresight sysfs"
- Inspect kernel config for CoreSight:
- grep CONFIG_CORESIGHT /boot/config-$(uname -r) 2>/dev/null || zgrep CONFIG_CORESIGHT /proc/config.gz 2>/dev/null
- Look for kernel oopses after repro:
- journalctl -k -n 200 --no-pager | egrep -i 'cscfg|coresight|cscfg_csdev|cscfg_config_desc'
- Module controls if you need an emergency workaround:
- echo 'blacklist cscfg' > /etc/modprobe.d/disable-coresight.conf && update-initramfs -u (or vendor equivalent)
Conclusion
CVE‑2025‑38131 is a real, actionable kernel correctness bug in the CoreSight configfs enable/disable path that can produce deterministic use‑after‑free crashes and availability loss on affected hosts. The upstream remediation is straightforward — strengthening the per‑config active reference semantics and holding module references while a config is active — and it is suitable for fast, low‑risk backports.For administrators the orders of business are clear: inventory hosts that expose CoreSight/configfs, map vendor kernel packages to the upstream commit, apply distributor or vendor kernel updates, and reboot in a staged way. Where patching cannot be immediate, restrict access to configfs/sysfs and remove device exposure from untrusted containers or VMs. Embedded and OEM kernels represent the largest residual risk; engage vendors for explicit backport timelines.
Operators should treat the absence of public exploitation as a temporary reassurance only — a deterministic kernel UAF is an operationally significant failure mode in multi‑tenant and CI/VDI environments and merits rapid remediation to maintain system reliability and security.
Source: MSRC Security Update Guide - Microsoft Security Response Center