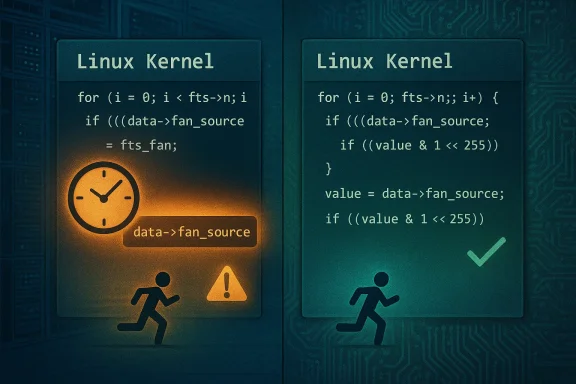
The Linux kernel received a targeted fix addressing a subtle but real Time‑of‑Check to Time‑of‑Use (TOCTOU) race in the hwmon driver ftsteutates: the fts_read() path could read a shared fan source index twice without synchronization, opening a narrow window where a concurrent update changes the value and leads to undefined behavior, including kernel crashes or incorrect userland readings.
The hwmon subsystem exposes hardware monitoring sensors (temperatures, fan speeds, PWM controls) to user-space. Drivers in this space routinely share small state structures between threads and interrupt contexts; correctness depends on careful ordering or locking when those fields are read and updated. In fts_read(), used to report or compute fan-related values, the code previously tested data->fan_source[channel] against FTS_FAN_SOURCE_INVALID and then later reused data->fan_source[channel] as an argument to BIT() without re-reading it into a local, stable variable. A concurrent fts_update_device() could change that field to 0xff (FTS_FAN_SOURCE_INVALID) in between, causing BIT(255) — a shift beyond the type width — and the resulting undefined behavior can crash the kernel or return bogus values to user-space. The upstream remediation reads the shared value once into a local variable and uses that, eliminating the TOCTOU window.
Practical steps for Microsoft-distributed artifacts:
Actionable priorities for teams responsible for Linux estates:
Conclusion: prioritize remediation now for shared and embedded systems, verify vendor advisories and package changelogs, and treat hwmon‑related TOCTOU fixes as part of routine kernel hardening rather than isolated trivia.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
The hwmon subsystem exposes hardware monitoring sensors (temperatures, fan speeds, PWM controls) to user-space. Drivers in this space routinely share small state structures between threads and interrupt contexts; correctness depends on careful ordering or locking when those fields are read and updated. In fts_read(), used to report or compute fan-related values, the code previously tested data->fan_source[channel] against FTS_FAN_SOURCE_INVALID and then later reused data->fan_source[channel] as an argument to BIT() without re-reading it into a local, stable variable. A concurrent fts_update_device() could change that field to 0xff (FTS_FAN_SOURCE_INVALID) in between, causing BIT(255) — a shift beyond the type width — and the resulting undefined behavior can crash the kernel or return bogus values to user-space. The upstream remediation reads the shared value once into a local variable and uses that, eliminating the TOCTOU window.Why this matters now
- The immediate impact is availability: the bug manifests as unexpected kernel behavior — crashes, hangs, or corrupted readings — which are service‑affecting on servers, appliances, or developer machines that expose these hwmon interfaces.
- The vector is local: an unprivileged user or process that can interact with the hwmon sysfs or driver interfaces may be able to trigger the condition, especially on multi‑tenant infrastructure where untrusted local workloads are present.
- Fixes were merged into upstream stable trees and backported into distribution kernels; operators must verify their vendor packages include the patch.
Technical anatomy: what broke and how the patch fixes it
The faulty pattern
In concurrent systems the classic TOCTOU pattern is:- Check a shared value (time-of-check).
- Assume that value is still valid later and use it (time-of-use).
The practical exploit primitive
The exploit primitive is not a remote over‑the‑internet worm. Instead, it's exploitable via local interaction with hwmon interfaces:- A process that can read or write hwmon attributes (sysfs or device-specific ioctls) triggers fts_read().
- Another actor — possibly the same process or a concurrent system thread performing fts_update_device() — updates the shared fan_source value at a precisely timed moment.
- The race produces an invalid shift and undefined behavior, potentially crashing the kernel or producing incorrect sensor results in user-space.
The upstream fix — small, surgical, and low risk
Upstream maintainers applied a minimal, idiomatic fix: read data->fan_source[channel] into a local variable and use that local for the subsequent check and for BIT(). This removes the TOCTOU window without adding heavy locking or altering API semantics. The patch is tiny, easily reviewable, and straightforward to backport. Multiple security trackers and advisories referenced the exact stable commits and listed the fixed stable kernel ranges.Evidence, corroboration, and exploitability status
Multiple independent trackers confirm the technical details and remediation:- The NVD entry documents the root cause and the precise code path, describing the double read of data->fan_source and the resulting undefined behavior from a large BIT() shift.
- Independent vulnerability aggregators and bulletin sites reproduce the same summary and list stable-branch patches and vendor backports; none reported an available public exploit or proof‑of‑concept at the time of publication.
Who is affected
- Any Linux system that includes the ftsteutates hwmon driver is potentially affected until patched. Not every distribution or install will have that driver built-in or exposed as a module; embedded vendors and appliance builders are especially likely to ship kernels with hwmon drivers enabled.
- Multi-tenant infrastructure (cloud images, CI builders, container hosts with devices passed through) where untrusted local code can access hwmon interfaces is the highest-priority risk group. Single-user desktops are lower risk but not exempt if local processes can interact with the driver.
- Devices and appliances with vendor-pinned kernels that are slow to receive updates are a long‑tail problem; the upstream patch is small and backportable, but vendors may or may not ship a quick firmware/kernel update. Inventory and vendor engagement are required.
Detection and forensics — practical checks for SREs and incident responders
If you suspect exploitation or recurrence after patching, collect and inspect the following:- Kernel logs (dmesg, journalctl, or archived kdump output) for oops traces that include hwmon, ftsteutates, fts_read, or BIT() shift anomalies. Crashes caused by invalid bit shifts often show unusual call traces or spurious warnings about bit operations.
- The kernel version string and active kernel config (uname -r; /proc/config.gz) — confirm whether the kernel in use predates the stable patch commits.
- The presence and status of the ftsteutates driver: check /sys/bus/platform/drivers and /lib/modules/$(uname -r) for ftsteutates or its module name; confirm whether the driver is built-in or modular. If modular, list modinfo and check timestamps on package upgrades.
- Reproduction attempts in a staging lab: exercise fts_read() and fts_update_device() under controlled race conditions (only in an isolated lab). Do not attempt timing attacks in production hosts.
Mitigation and remediation — prioritized checklist
Apply the following prioritized actions to reduce exposure quickly and safely.- Inventory (Immediate)
- Enumerate kernels and artifact builds across your estate: cloud images, VM templates, developer WSL kernels, custom kernels, and firmware. Identify images that include the ftsteutates hwmon driver or kernel versions earlier than the upstream patches.
- Patch (High priority)
- Install vendor-supplied kernel updates that include the stable backports for CVE‑2025‑38217 and reboot where required. Vendors generally applied the the small patch to stable branches; consult distribution advisories for exact package names and versions.
- Livepatch (If available)
- If your vendor supplies a livepatch that includes the commit, validate and apply it. Confirm the livepatch explicitly references the upstream change or the CVE identifier before relying on it. Livepatch coverage varies by vendor and kernel branch.
- Temporary hardening (When patching is delayed)
- If the driver is modular, consider unloading or blacklisting the module and rebooting into a kernel without the module. Test hardware monitoring impact before taking this step — some motherboards rely on the driver for critical thermal control. If the driver is built into the kernel (CONFIG_* = y), unloading is not possible and patching is the only viable route.
- Operational controls
- Reduce local attack surface: restrict unprivileged device access, limit who can interact with hwmon sysfs nodes, and harden container hosts and CI runners to prevent untrusted workloads from accessing device nodes of kernel stability and oops events on sensitive hosts.
- Long-tail / embedded devices
- Contact vendors for firmware or kernel updates. Where vendors cannot provide a backport, consider isolating affected devices, replacing them on an or applying compensating network controls to reduce exposure.
Vendor mapping and artifact risk — Microsoft and the hwmon family
When Linux kernel CVEs appear in the wild, cloud and vendor artifacts complicate triage. Microsoft in recent years has adopted machine‑readable VEX/CSAF attestations to state which Microsoft‑distributed artifacts include affected open‑source components; however, those attestations are product‑scoped and do not, by themselves, confirm the absence of the vulnerable code in other artifacts. Treat Microsoft attestation as a helpful inventory signal: if Microsoft says Azure Linux includes the affected upstream component, prioritize patching those Azure Linux images; for other Microsoft artifacts (WSL2 kernels, Marketplace images, AKS node images), perform artifact‑level checks rather than assuming safety.Practical steps for Microsoft-distributed artifacts:
- For Azure Linux customers: follow Microsoft’s advisory and update images or kernel packages as directed. Microsoft’s attestation that a product “includes the open‑source library and is therefore potentially affected” should be treated as confirmation that the artifact is in scope.
- For WSL2 and Marketplace images: do not assume non‑inclusion. Verify the kernel build and driver configuration used to produce each artifact. Microsoft’s VEX/CSAF rollout began with Azure Linux and expanded over time; absence of evidence in a Microsoft attestation is not proof of absence across all artifacts.
Risk analysis: strengths of the fix and remaining operational concerns
Strengths
- The upstream patch is a textbook good‑practice fix: read once into a local, typed variable rather than re‑reading a shared field. It is minimal, easy to audit, and avoids heavy synchronization that might harm performance. This quality makes the fix safe to apply across stable branches and easy for vendors to backport.
- The scope is narrow: the change does not alter API semantics or add new kernel subsystems; it focuses on a single code site and thus has a small regression surface. That aided rapid cherry‑picks into stable trees and vendor backports.
Residual risks and operational considerations
- The long tail problem persists. Devices with vendor‑pinned kernels or appliances may not receive backports quickly; these systems remain operationally exposed until vendors ship updates or until you replace/segregate the devices. The fix’s small size helps backporting, but vendor processes and lifecycles still drive remediation timelines.
- Detection is noisy. Kernel oopses and hangs have many causes; enumerating a specific hwmon TOCTOU as the root cause requires careful log collection and correlation with driver activity. Without reproducible PoC, adjudication often depends on vendor guidance and kernel changelogs.
- The exploitability bar remains non-trivial but real on shared infrastructure. Skilled local attackers with control of timing and access to hwmon interfaces can reliably induce the fault; therefore, multi‑tenant systems must be prioritized.
Practical verification steps (how to confirm a host is fixed)
Follow these concrete steps after you apply vendor updates or backports:- Verify the kernel package version and changelog: ensure the installed kernel package lists the stable commit or explicitly references CVE‑2025‑38217 in the vendor changelog.
- Reboot into the patched kernel and confirm the module list: if the driver is modular, check the module version and build timestamp (modinfo ftsteutates or appropriate module name). If it is built in, confirm uname -r and kernel build metadata correspond to the fixed release.
- Run sanitized, non‑production smoke tests that exercise hwmon reads and updates under controlled concurrency in a staging environment. Confirm no oops or kernel warnings appear. Never attempt timing‑attack tests on production hosts.
Closing analysis and final recommendations
CVE‑2025‑ve example of how tiny, idiomatic coding slips in low‑level drivers can translate to real availability risks in production infrastructure. The fix is minimal and safe: capturing a shared field into a local variable is a small coding change with outsized operational benefit. Nevertheless, the real work for administrators is not the patch itself but the artifact management required to ensure every kernel and image in your fleet receives that fix — especially in cloud, embedded, and long‑lifecycle environments.Actionable priorities for teams responsible for Linux estates:
- Immediately inventory images and kernels for the presence of the ftsteutates hwmon driver. Treat multi‑tenant and appliance hosts as high priority.
- Apply vendor kernel updates or validated livepatches that include the CVE fix. Validate the fix via changelog or kernel commit references.
- For environments that cannot be patched immediately, reduce the local attack surface, remove device access for untrusted workloads, and isolate vulnerable appliances until vendor updates arrive.
- In cloud or Microsoft‑distributed artifacts, treat vendor attestations (such as Azure Linux VEX/CSAF statements) as useful signals but verify other artifacts on an artifact‑by‑artifact basis rather than assuming global coverage.
Conclusion: prioritize remediation now for shared and embedded systems, verify vendor advisories and package changelogs, and treat hwmon‑related TOCTOU fixes as part of routine kernel hardening rather than isolated trivia.
Source: MSRC Security Update Guide - Microsoft Security Response Center