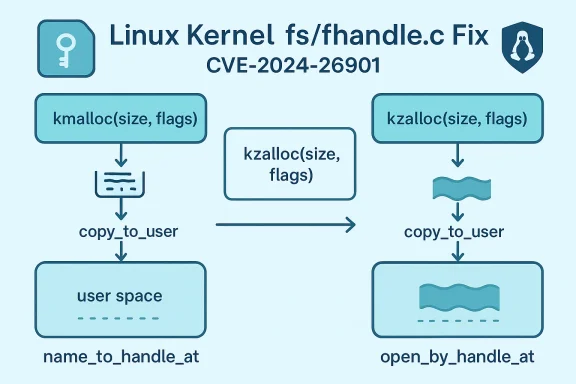
The Linux kernel received a small but important fix in April 2024 that replaces a non‑zeroed allocation with a zeroing allocator in the file‑handle path — closing an information‑leak uncovered by syzbot and flagged as CVE‑2024‑26901. The change is surgical (replace kmalloc() with kzalloc() in fs/fhandle.c), but its implications matter: an uninitialized 20‑byte buffer could be copied to userland by the name_to_handle_at/open_by_handle_at syscall path, potentially exposing kernel memory contents to local attackers.
name_to_handle_at() and open_by_handle_at() are the kernel syscalls that let userland convert a pathname into an opaque file handle and later open that file by the handle instead of by name. These interfaces are primarily used by userspace file‑server implementations, tooling that needs stable references to files across renames, and in some NFS/export workflows where file handles are used instead of pathnames. The manual pages and kernel configuration documentation explain the two‑step model: name_to_handle_at() returns a handle and a mount ID; open_by_handle_at() uses that handle and usually requires additional privileges.
The bug was discovered by syzbot (the kernel continuous fuzzing service) using KMSAN (Kernel Memory Sanitizer), which reports uninitialized memory reads. The KMSAN stacktrace recorded by the kernel team shows the uninitialized bytes being created by a kmalloc() and later copied to userland with copy_to_user(), causing the information disclosure alarm. The kernel CVE announcement lists the full KMSAN trace and states the simple remediation: allocate the buffer with kzalloc() so it’s zeroed before any fields are copied to userspace.
There is also a practical lesson for system operators: small kernel leaks are noisy to triage but can be exploited or used as reconnaissance if left unpatched. Even when the leak is only a few bytes, modern attack chains sometimes stitch multiple small weaknesses together. Therefore, the correct operational response is rapid but measured: verify vendor patches, apply them, and monitor for anomalies — not panic, but not complacency either.
Finally, the kzalloc() approach is not novel in the kernel; similar fixes have been applied in other subsystems where sanitizers reported uninitialized reads — changing kmalloc() to kzalloc() or otherwise ensuring deterministic initialization is a routine but crucial defensive step. That historical pattern is visible across multiple CVE writeups and internal kernel notes.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background / Overview
Background / Overview
name_to_handle_at() and open_by_handle_at() are the kernel syscalls that let userland convert a pathname into an opaque file handle and later open that file by the handle instead of by name. These interfaces are primarily used by userspace file‑server implementations, tooling that needs stable references to files across renames, and in some NFS/export workflows where file handles are used instead of pathnames. The manual pages and kernel configuration documentation explain the two‑step model: name_to_handle_at() returns a handle and a mount ID; open_by_handle_at() uses that handle and usually requires additional privileges.The bug was discovered by syzbot (the kernel continuous fuzzing service) using KMSAN (Kernel Memory Sanitizer), which reports uninitialized memory reads. The KMSAN stacktrace recorded by the kernel team shows the uninitialized bytes being created by a kmalloc() and later copied to userland with copy_to_user(), causing the information disclosure alarm. The kernel CVE announcement lists the full KMSAN trace and states the simple remediation: allocate the buffer with kzalloc() so it’s zeroed before any fields are copied to userspace.
What exactly went wrong (technical analysis)
The difference between kmalloc() and kzalloc()
- kmalloc(size, flags) allocates kernel memory but does not initialize it; the contents are whatever leftovers were in the slab object.
- kzalloc(size, flags) is effectively kmalloc() followed by memset(0), guaranteeing the returned region is zeroed.
The KMSAN trace and the leak
The public advisories reproduce the KMSAN trace: the sanitizer shows an uninitialized allocation chain ending in kmalloc() and reports that bytes 18–19 of a 20‑byte region were uninitialized when copied to userland. Because the file_handle structure used by name_to_handle_at() contains a variable‑length opaque handle buffer, the code path allocated and returned a buffer whose tail bytes were not explicitly set before being copied out. Replacing kmalloc() with kzalloc() stops that window of exposure by zeroing the whole buffer prior to copy_to_user().Code‑level scope
The vulnerable file is fs/fhandle.c. The kernel’s CVE announcement and vendor advisories point to a minimal change there (allocation call site switched to kzalloc()). The kernel team published commits for stable branches; vendors and distributions have backported the change into their kernels when appropriate. The fix is intentionally small, which is good from a maintenance perspective: fewer side effects, easier backporting, and predictable behavior across releases.Impact and exploitability
What the vulnerability permits
CVE‑2024‑26901 is an information‑disclosure bug — a kernel infoleak — not a direct code‑execution or privilege‑escalation flaw. The immediate impact is that a local process invoking the relevant syscall could obtain a small amount of kernel memory content. That content might, in rare circumstances, include sensitive material (for example, stack or heap contents that contain pointers, small secret fragments, or other residual data). The canonical exploit scenario is: local attacker calls name_to_handle_at() in a carefully crafted way and receives, alongside legitimate handle data, a couple of uninitialized bytes drawn from kernel memory.How easy is it to exploit?
- Access vector: local (AV:L in the CVSS vector recorded by NVD). An attacker needs to run code on the target machine (local user or low‑privilege process).
- Privileges required: name_to_handle_at() is callable from unprivileged processes in normal configurations; open_by_handle_at() typically requires CAP_DAC_READ_SEARCH to open arbitrary handles. Because the leak is in the name‑to‑handle path, an unprivileged caller may trigger it. Manpages and kernel docs confirm the syscall semantics.
- Leak size and practicality: the KMSAN trace shows a very small leak (a few bytes at the end of a buffer). Small leaks can be noisy and non‑deterministic; they are frequently useful only as telemetry or as a stepping stone in a broader attack chain (for example, to guess Kernel Address Space Layout or to collect entropy that aids other bugs), but they are less likely to directly yield credentials or long secret material. Still, security teams should treat any kernel memory disclosure as a serious risk because of the potential for chained exploitation.
CVSS and vendor scoring
NVD and multiple vendors classify the issue as Medium severity with a CVSS v3 score around 5.5 (vector: AV:L/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H or variations used by some vendors). The scoring reflects that exploitation requires local access and that the primary impact is information disclosure rather than remote code execution. Vendors that produce kernel packages (Red Hat, SUSE, Debian, Amazon) have issued updates and advisories referencing the same root cause and fix.Vendor response and patching status
The kernel team published the fix in the stable trees and included commit IDs for multiple stable branches; kernel maintainers advised users to upgrade to the latest stable kernels or apply the small patch into vendor kernels. Distributors and vendors subsequently issued advisories and backports:- Linux kernel CVE announcement (official): describes the issue, includes the KMSAN trace, and links to the stable commits to cherry‑pick for backporting.
- NVD entry: documents the issue and the sanitizer output, with CVSS summary.
- Amazon Linux (ALAS): listed the CVE and marked kernels in Amazon Linux 2/2023 as fixed in their ALAS advisories.
- Debian security tracker and DSA updates: grouped the kernel fixes (DSA‑5681‑1) and tracked distribution‑specific packages.
- Red Hat and related advisories: included the fix in kernel errata published to customers; LWN summaries of Red Hat kernel alerts include the CVE mention.
- SUSE, Oracle, Ubuntu and other vendors published corresponding CVE pages referencing the same KMSAN diagnosis and the kzalloc() remediation.
Detection and mitigation guidance for operators
Immediate operational steps (prioritized)
- Inventory: identify hosts that run Linux kernels built from upstream trees that include fs/fhandle.c and that expose ordinary userland access (virtually all desktops, servers, and containers). Use your asset management system to enumerate kernels and distributor package versions.
- Vendor check: consult the distro vendor advisory for your platform (ALAS, Debian DSA, Red Hat errata, SUSE advisories) to determine whether the kernel package installed on each host contains the backported fix; the vendor advisory is the authoritative source for whether a particular kernel package is patched.
- Patch and reboot: where unpatched kernels are present, schedule kernel package upgrades and reboots per your change control process. Because this is a kernel‑level fix, the change requires package replacement and a system reboot to take effect on a production host.
- Compensating controls: if immediate patching is impossible, mitigate exposure by restricting access to systems (network and local), isolating sensitive workloads, and enforcing least‑privilege for accounts that might call name_to_handle_at()—although this syscall is commonly available to unprivileged users so operational restrictions are blunt instruments.
Detecting exploitation attempts
- Audit rules: add an auditd / kernel auditing rule to log calls to name_to_handle_at() and open_by_handle_at(). On many systems you can add syscall auditing for events of interest and then analyze for abnormal frequency or unexpected callers. The syscall is part of the core ABI and therefore observable via syscall auditing facilities.
- Process tracking: observe processes that frequently invoke name‑to‑handle operations outside normal operational patterns (for example, processes that shouldn’t perform large numbers of filesystem metadata operations).
- Kernel logs: KMSAN traces (which exposed the issue) appear only in special sanitizer‑enabled kernel builds; production kernels typically run without KMSAN, so you will not see KMSAN findings in standard /var/log/messages. That means absence of KMSAN traces is not proof of safety.
Example audit rule (conceptual)
- Add an audit rule to watch the syscall (replace with your distro’s auditctl/augenrules syntax): audit events for name_to_handle_at/open_by_handle_at — log the PID, UID, executable path, and arguments. Analyze spikes or calls from unexpected services. (Note: tailor rules to your environment to avoid log overload.)
Why the fix is sensible — and what to watch for
Strengths of the remediation
- Minimal and correct: replacing kmalloc() with kzalloc() addresses the root cause — uninitialized allocation — directly, and it is a pattern with a long history in the kernel: zeroing allocations removes a common class of information disclosure bugs with the least invasive change.
- Backportable: because the change is localized to an allocation call, it is easy to cherry‑pick into stable branches; vendors can and have distributed backports to their kernels.
- Low regression risk: kzalloc() is a drop‑in replacement for kmalloc() in most contexts where initial zeroing does not change logic. The kernel community prefers small defensive fixes for exactly this reason.
Limitations and residual risks
- Small leaks can matter: even tiny, seemingly insignificant leaks can be valuable to attackers when chained with other bugs (e.g., to defeat ASLR, refine heap spraying techniques, or confirm memory layouts). Treat all kernel infoleaks as potential building blocks for larger exploit chains.
- Coverage depends on backports: while upstream stable trees received the patch, not every vendor or embedded device will have applied it. Some long‑lived or vendor‑frozen kernels (for appliances, IoT, or specialized platforms) may remain unpatched unless the vendor issues an explicit backport. Always verify the exact kernel package and patch level per vendor advisory.
- Sanitizer visibility vs real exploitability: KMSAN reports are invaluable for finding defects, but KMSAN is a debugging tool and not representative of the exact conditions on production kernels. The leak KMSAN found may be conditional or non‑deterministic in practice; however, the conservative operational posture is to patch because any actual information disclosure from kernel to userland is a clear security regression.
Practical remediation checklist
- Confirm whether your distribution or kernel vendor has released an update that includes the CVE fix. Use the vendor CVE pages (ALAS, Red Hat, Debian, SUSE, Oracle, Ubuntu) to match your installed kernel package to vendor patch notes.
- Apply vendor kernel updates and reboot the hosts in a controlled maintenance window. Verify the running kernel version corresponds to the updated package.
- For systems that cannot be patched immediately, restrict untrusted local code execution and look for anomalous name_to_handle_at() usage with syscall auditing.
- For high‑security environments, consider kernel hardening strahardened userland, capability restrictions) and a program of regular kernel updates and backport tracking.
- Retest any system‑specific custom kernel modules after upgrade to validate compatibility.
Wider context and takeaways
CVE‑2024‑26901 is a classic example of how small memory‑handling assumptions cause information leaks. The kernel community and continuous fuzzing infrastructure (syzbot plus sanitizers) are effective at catching these categories of defects early, and the remediation here — using kzalloc() — is the standard defensive hygiene: zero allocations that are at risk of being copied to userspace. The fix is a textbook safety improvement and the vendor responses followed the expected pattern: upstream commit, backport to stable branches, and distribution advisories and kernel package updates.There is also a practical lesson for system operators: small kernel leaks are noisy to triage but can be exploited or used as reconnaissance if left unpatched. Even when the leak is only a few bytes, modern attack chains sometimes stitch multiple small weaknesses together. Therefore, the correct operational response is rapid but measured: verify vendor patches, apply them, and monitor for anomalies — not panic, but not complacency either.
Finally, the kzalloc() approach is not novel in the kernel; similar fixes have been applied in other subsystems where sanitizers reported uninitialized reads — changing kmalloc() to kzalloc() or otherwise ensuring deterministic initialization is a routine but crucial defensive step. That historical pattern is visible across multiple CVE writeups and internal kernel notes.
Conclusion
CVE‑2024‑26901 is an information‑disclosure flaw in the Linux kernel’s file‑handle code, found by syzbot/KMSAN and fixed by switching to a zeroing allocator (kzalloc()) in fs/fhandle.c. The immediate code change is tiny and low‑risk, which helped vendors ship backports quickly; the operational impact is medium (local information disclosure), not a remote code‑execution or privilege‑escalation bug. Operators should verify vendor advisories, apply available kernel updates, reboot systems, and add audit/monitoring controls to detect unusual usage of name_to_handle_at/open_by_handle_at until patches are deployed. The kernel community’s handling of this case — fast, narrowly targeted, and backportable — is the right model for minimizing risk while keeping regressions low.Source: MSRC Security Update Guide - Microsoft Security Response Center